嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要仔细阅读文章内容,抓住关键点。 文章讲的是Fortinet的FortiClient EMS存在一个不正确的访问控制漏洞,允许未经身份验证的攻击者执行未经授权的代码或命令。这个漏洞已经被野外利用了。影响版本是7.4.5到7.4.6,CVSS评分很高,9.1和9.8。修复建议是立即打补丁或限制访问。 接下来,我需要把这些信息浓缩到100字以内。要包括漏洞名称、影响版本、CVSS评分、攻击后果、修复建议等关键点。 可能的结构:FortiClient EMS存在高危漏洞,允许未认证攻击者执行代码,CVSS 9.8,影响7.4.5-7.4.6版本,建议立即修复或限制访问。 检查一下字数是否合适,确保信息准确且简洁。 </think> FortiClient EMS 存在高危漏洞(CVE-2026-35616),允许未认证攻击者通过精心构造的请求执行未经授权的代码或命令。该漏洞影响 FortiClient EMS 7.4.5 至 7.4.6 版本,CVSS v3 评分为 9.8。建议立即安装补丁或限制访问以缓解风险。 2026-4-6 20:4:19 Author: horizon3.ai(查看原文) 阅读量:19 收藏
Fortinet FortiClient EMS Improper Access Control Vulnerability | Active Exploitation
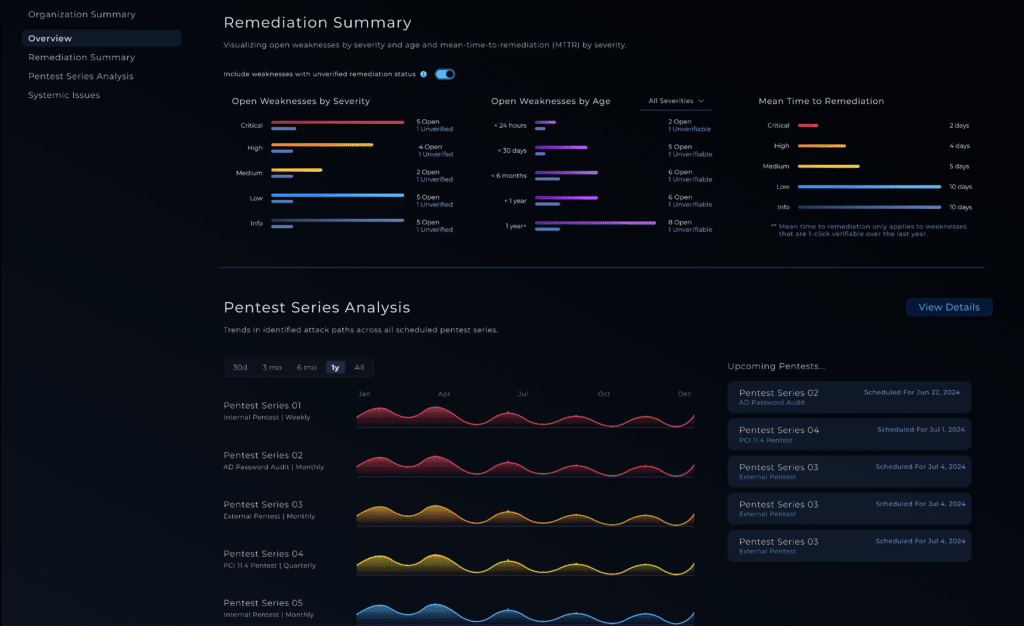
Fortinet FortiClient Enterprise Management Server (EMS), contains an improper access control vulnerability that can allow an unauthenticated attacker to execute unauthorized code or commands through crafted requests. Fortinet says the flaw has been exploited in the wild. Affected versions are FortiClient EMS 7.4.5 through 7.4.6. Fortinet’s advisory lists the issue as critical and notes a CVSS v3 score of 9.1, while the CVSS score shown by NVD is 9.8. A NodeZero® Proactive Security Platform Rapid Response test is available to help customers verify exposure and confirm remediation.
Technical Details
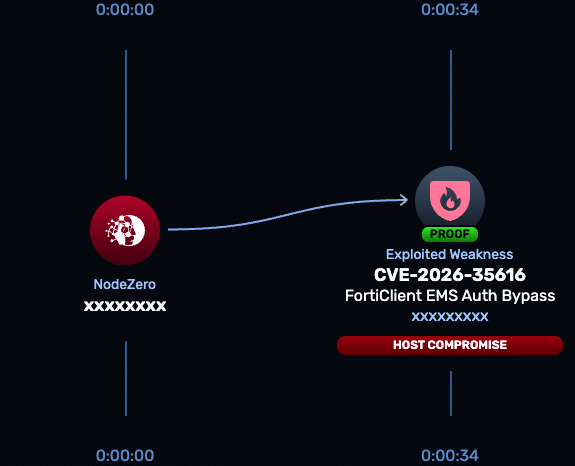
CVE-2026-35616 is an improper access control issue in the FortiClient EMS API. Fortinet says an unauthenticated attacker can send crafted requests that lead to unauthorized code or command execution. Public reporting has described the issue as a pre-authentication API access bypass that can sidestep authentication and authorization protections. Fortinet also states it has observed exploitation in the wild.
This matters because EMS is the management plane for FortiClient deployments. If an attacker compromises EMS, they are not just landing on a standalone server. They are compromising the system used to manage endpoint security policy across connected devices. That makes this a high-priority exposure for any organization running a vulnerable EMS instance, especially if it is internet accessible.
NodeZero® Proactive Security Platform — Rapid Response
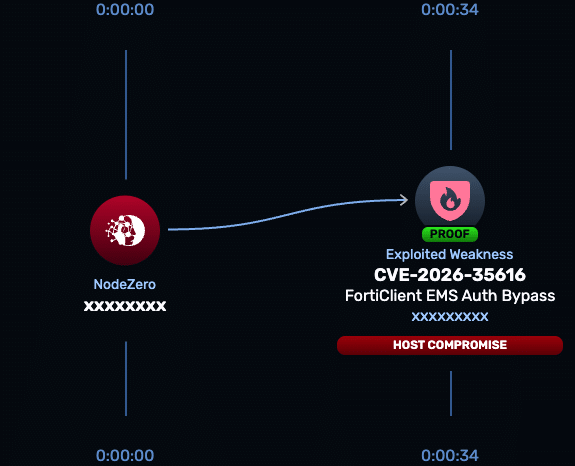
A NodeZero Rapid Response test is available now to help organizations quickly determine whether a FortiClient EMS deployment is exposed to CVE-2026-35616 and to validate that remediation removed exploitability.
- Run the Rapid Response test — Horizon3.ai customers can launch the test from the customer portal to verify whether FortiClient EMS is vulnerable to CVE-2026-35616.
- Patch immediately — Fortinet says FortiClient EMS 7.4.5 and 7.4.6 are affected and directs customers to install the vendor hotfixes immediately. Fortinet also says the issue will be fixed in FortiClient EMS 7.4.7. If patching cannot be completed immediately, restrict access to EMS management and agent-facing services to trusted hosts only.
- Re-run the Rapid Response test — confirm the hotfix or upgrade removed exploitability and that the exposed attack path is closed.
Indicators of Compromise
At the time of writing, the public sources tied to this issue confirm active exploitation but do not provide a detailed list of attacker IPs, hashes, filenames, or specific post-exploitation commands. Public reporting does, however, indicate that internet-facing EMS instances have been observed at scale and that exploitation was seen in the wild before broad public disclosure.
| Indicator | Type | Description |
| Crafted requests to vulnerable EMS API endpoints | Activity | Public descriptions characterize the flaw as a pre-authentication API access bypass leading to unauthorized code or command execution. |
| Internet-exposed FortiClient EMS instances | Exposure condition | Shadowserver tracking cited in public reporting found roughly 2,000 exposed EMS instances online, increasing risk for externally reachable systems. |
| Unexplained command execution or system changes on EMS | Behavioral signal | Consistent with Fortinet’s statement that the flaw can enable unauthorized code or command execution. |
Affected versions & patch
- Affected: FortiClient EMS 7.4.5 through 7.4.6. Fortinet states FortiClient EMS 7.2 is not affected.
- Patch: Install the vendor hotfix for 7.4.5 or 7.4.6 immediately, following Fortinet’s release-note instructions. Fortinet says FortiClient EMS 7.4.7 will include a permanent fix.
Timeline
- March 31, 2026 — Public reporting says exploitation attempts were first recorded against honeypots, and Defused Cyber said it observed zero-day exploitation earlier that week.
- April 4, 2026 — Fortinet published advisory FG-IR-26-099 for CVE-2026-35616.
- April 5, 2026 — Media reporting highlighted active exploitation and emergency hotfix guidance.
- April 6, 2026 — Public reporting said CISA added CVE-2026-35616 to the KEV catalog and set an April 9 remediation deadline for FCEB agencies.
References
Read about other CVEs
NodeZero® Platform
Implement a continuous find, fix, and verify loop with NodeZero
The NodeZero® platform empowers your organization to reduce your security risks by autonomously finding exploitable weaknesses in your network, giving you detailed guidance around how to priortize and fix them, and having you immediately verify that your fixes are effective.
Recognized By
如有侵权请联系:admin#unsafe.sh