
嗯,用户让我总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头。首先,我需要通读整篇文章,抓住主要信息。 文章主要讲的是一个叫Storm-1175的网络犯罪团伙,他们使用Medusa勒索软件进行攻击。他们利用零日漏洞和N日漏洞,快速入侵目标网络,并在几天甚至24小时内完成数据外泄和勒索软件部署。最近影响了医疗、教育、金融等多个行业的机构。 接下来,我需要把这些信息浓缩到100字以内。要突出关键点:团伙名称、攻击手法、速度、影响的行业等。同时,避免使用复杂的术语,让总结简洁明了。 可能会这样组织句子:Storm-1175团伙利用零日和N日漏洞快速攻击目标网络,在几天内完成数据外泄和勒索软件部署,影响了医疗、教育、金融等多个行业的机构。 检查一下字数是否符合要求,大约是80字左右,符合用户的要求。同时确保没有使用任何开头模板,直接描述内容。 </think> Storm-1175团伙利用零日和N日漏洞快速攻击目标网络,在几天内完成数据外泄和勒索软件部署,影响了医疗、教育、金融等多个行业的机构。 2026-4-6 17:0:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:13 收藏

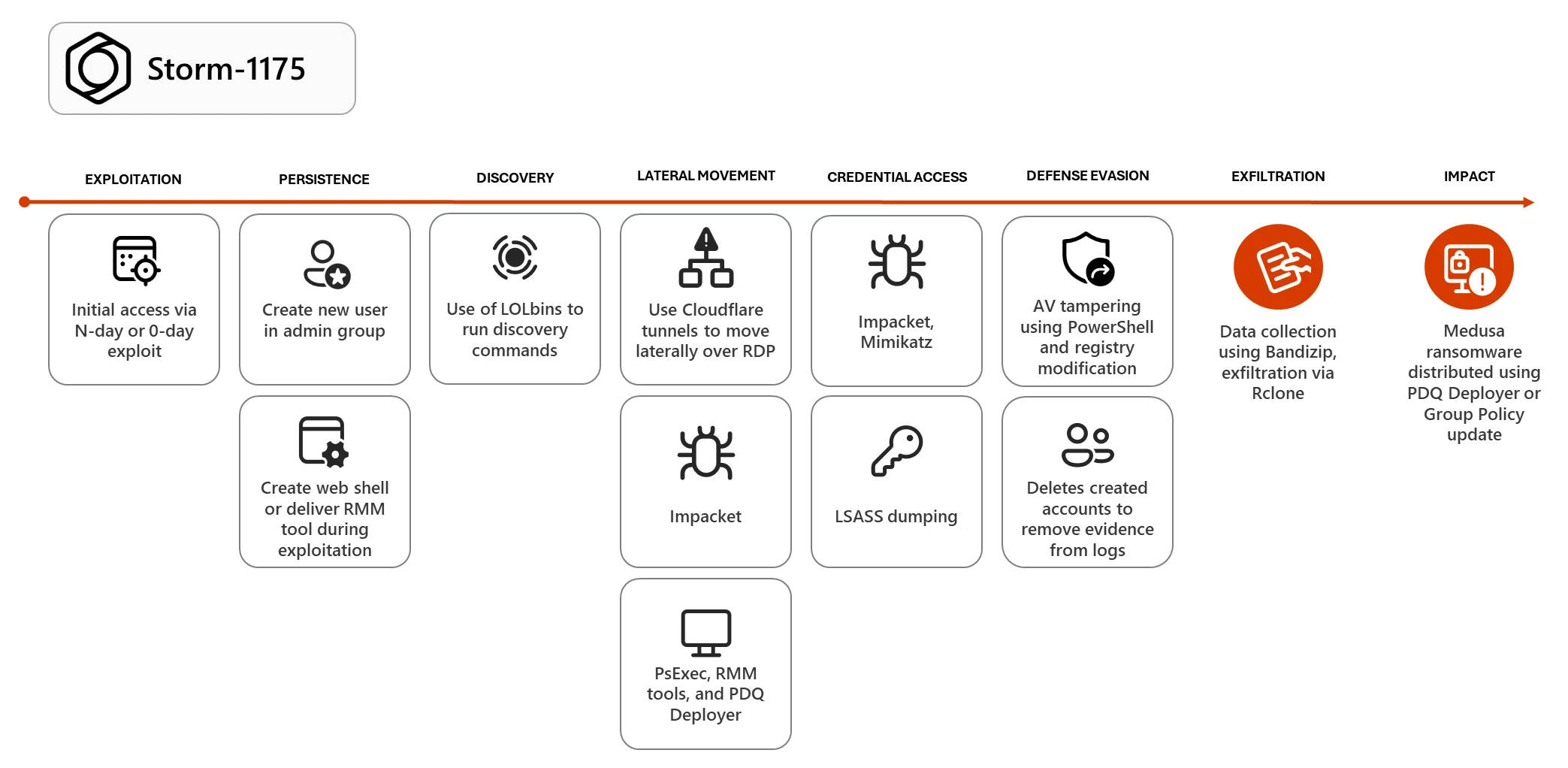
Microsoft says that Storm-1175, a China-based financially motivated cybercriminal group known for deploying Medusa ransomware payloads, has been deploying n-day and zero-day exploits in high-velocity attacks.
This cybercrime gang quickly shifts to targeting new security vulnerabilities to gain access to its victims' networks, weaponizing some of them within a day and, in some cases, exploiting them a week before patches are released.
"Storm-1175 rapidly moves from initial access to data exfiltration and deployment of Medusa ransomware, often within a few days and, in some cases, within 24 hours," Microsoft said.
"The threat actor's high operational tempo and proficiency in identifying exposed perimeter assets have proven successful, with recent intrusions heavily impacting healthcare organizations, as well as those in the education, professional services, and finance sectors in Australia, United Kingdom, and United States."
Microsoft has also observed Storm-1175 operators chaining multiple exploits to gain persistence on compromised systems by creating new user accounts, deploying remote monitoring and management software, stealing credentials, and disabling security software before dropping ransomware payloads.
In October, Microsoft reported that Storm-1175 had been exploiting a maximum-severity GoAnywhere MFT vulnerability (CVE-2025-10035) in Medusa ransomware attacks for over one week before it was patched.
Another vulnerability Storm-1175 exploited as a zero-day was CVE-2026-23760, an authentication bypass in SmarterTools' SmarterMail email server and collaboration tool.
"While these more recent attacks demonstrate an evolved development capability or new access to resources like exploit brokers for Storm-1175, it is worth noting that GoAnywhere MFT has previously been targeted by ransomware attackers, and that the SmarterMail vulnerability was reportedly similar to a previously disclosed flaw," Microsoft added.
"These factors may have helped to facilitate subsequent zero-day exploitation activity by Storm-1175, who still primarily leverages N-day vulnerabilities."
In recent campaigns, Storm-1175 has exploited more than 16 vulnerabilities across 10 software products, including Microsoft Exchange (CVE-2023-21529), Papercut (CVE-2023-27351 and CVE-2023-27350), Ivanti Connect Secure and Policy Secure (CVE-2023-46805 and CVE-2024-21887), and ConnectWise ScreenConnect (CVE-2024-1709 and CVE-2024-1708).
Microsoft has also seen them exploit vulnerabilities in JetBrains TeamCity (CVE-2024-27198 and CVE-2024-27199), SimpleHelp (CVE-2024-57726, CVE-2024-57727, and CVE-2024-57728), CrushFTP (CVE‑2025‑31161), SmarterMail (CVE-2025-52691), and BeyondTrust (CVE-2026-1731).
CISA issued a joint advisory with the FBI and the Multi-State Information Sharing and Analysis Center (MS-ISAC) in March 2025, warning that the Medusa ransomware gang's attacks had impacted over 300 critical infrastructure organizations across the United States.
In July 2024, Microsoft also linked the Storm-1175 threat group, along with three other cybercrime gangs, to Black Basta and Akira ransomware attacks that exploited a VMware ESXi authentication-bypass flaw.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh

