
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。用户的要求是直接写文章描述,不需要以“文章内容总结”或“这篇文章”开头。 首先,我阅读了用户提供的文章。文章主要讲的是美国网络安全和基础设施安全局(CISA)下令联邦机构在周五之前修复FortiClient EMS服务器的一个被积极利用的漏洞。这个漏洞被追踪为CVE-2026-35616,允许攻击者绕过身份验证和授权控制。Fortinet已经发布了紧急补丁,并警告威胁行为者正在利用这个漏洞进行零日攻击。Shadowserver报告称有近2000个FortiClient EMS实例暴露在线上。 接下来,我需要将这些信息浓缩到100字以内。关键点包括:CISA下令修复漏洞、漏洞允许攻击者绕过控制、Fortinet发布补丁、Shadowserver报告暴露实例数量。 然后,我要确保语言简洁明了,不使用复杂的术语,同时涵盖所有重要信息。避免重复,确保每个句子都传达一个主要信息点。 最后,检查字数是否在限制内,并确保内容准确无误。 </think> 美国网络安全机构CISA要求联邦机构修复FortiClient EMS服务器的高危漏洞CVE-2026-35616,该漏洞可被攻击者绕过身份验证。Fortinet已发布紧急补丁警告零日攻击风险。Shadowserver报告称近2000个EMS实例暴露在线上。 2026-4-6 16:15:16 Author: www.bleepingcomputer.com(查看原文) 阅读量:12 收藏

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) ordered federal agencies to secure FortiClient Enterprise Management Server (EMS) instances against an actively exploited vulnerability by Friday.
Tracked as CVE-2026-35616, this security flaw was discovered by cybersecurity firm Defused, which described it as a pre-authentication API access bypass that can allow attackers to bypass authentication and authorization controls entirely.
Fortinet released emergency hotfixes over the weekend to address the vulnerability and said the security issue stems from an improper access control weakness that unauthenticated attackers can exploit to execute code or commands via specially crafted requests.
The company also warned that threat actors had been exploiting it in zero-day attacks and warned IT administrators to secure their EMS instances as soon as possible by applying the hotfixes or upgrading to FortiClient EMS version 7.4.7 when it becomes available.
"Fortinet has observed this to be exploited in the wild and urges vulnerable customers to install the hotfix for FortiClient EMS 7.4.5 and 7.4.6," the company said.
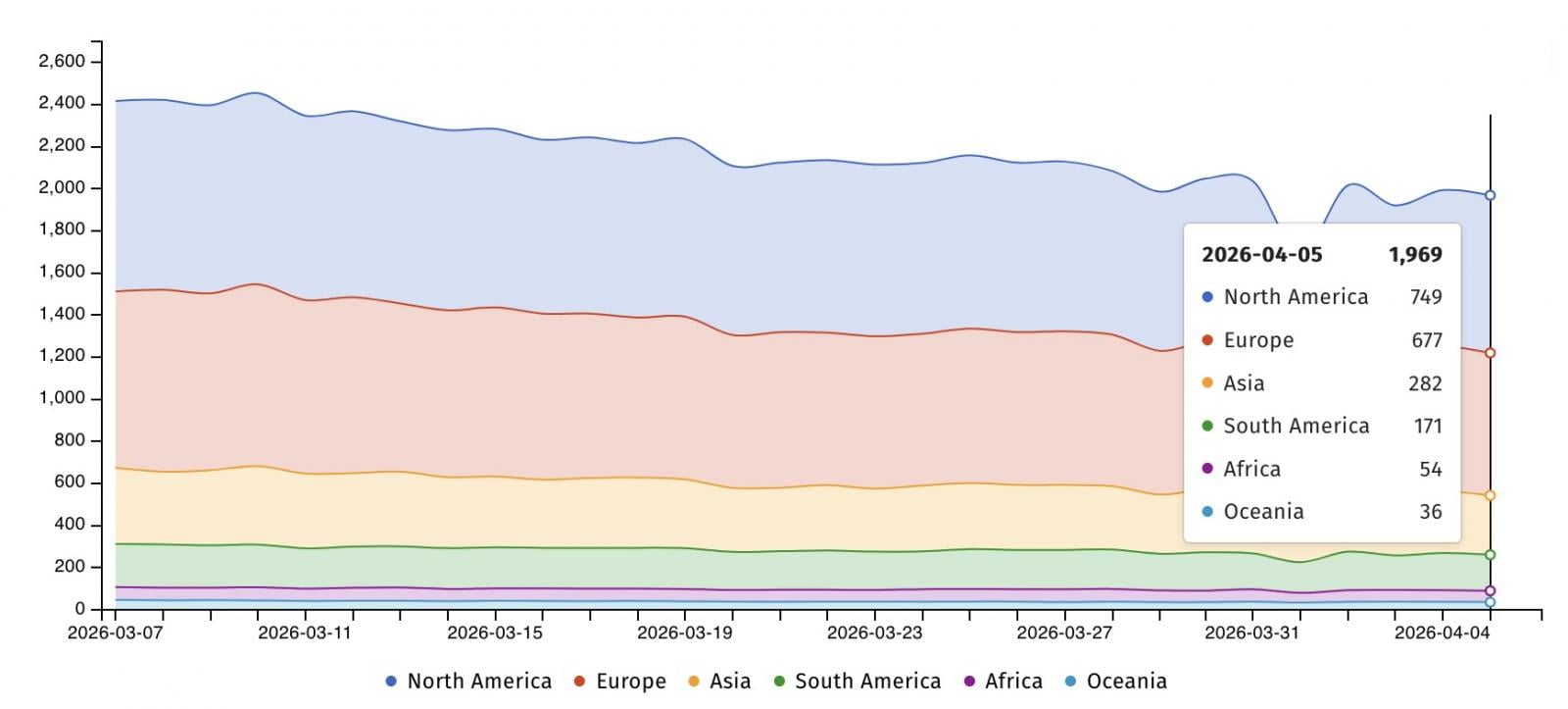
Internet security watchdog group Shadowserver currently tracks nearly 2,000 FortiClient EMS instances exposed online, with more than 1,400 IPs in the United States and in Europe. However, there are no details on how many have already been patched or have vulnerable configurations.
On Monday, CISA added CVE-2026-35616 to its Known Exploited Vulnerabilities (KEV) Catalog and ordered Federal Civilian Executive Branch (FCEB) agencies to patch FortiClient EMS instances by Thursday midnight, April 9, as mandated by Binding Operational Directive (BOD) 22-01.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," the cybersecurity agency warned.
"Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable."
Even though BOD 22-01 applies only to U.S. federal agencies, CISA urged all defenders (including those in the private sector) to prioritize patching for CVE-2026-35616 and secure their organizations' networks as soon as possible.
Fortinet patched another critical FortiClient EMS flaw (CVE-2026-21643) in February, which was also flagged less than two weeks ago as exploited in attacks.
Fortinet vulnerabilities are often exploited in cyber espionage campaigns and ransomware attacks (often as zero-day bugs) to breach corporate networks. Most recently, Fortinet blocked FortiCloud SSO connections from devices running vulnerable firmware versions to mitigate CVE-2026-24858 zero-day attacks.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
