好的,我现在需要帮用户总结一篇文章,控制在100字以内,而且不需要用“文章内容总结”这样的开头。首先,我得仔细阅读文章,理解其主要内容。 文章主要讨论开放重定向(open redirect)被威胁行为者滥用的情况。虽然这种漏洞本身不算高风险,但作者指出它常被用于钓鱼攻击。链接指向合法域名,容易骗过受害者和简单的检测机制。作者还提到尽管OWASP不再列出它为顶级漏洞,但攻击者从未停止利用它。 接下来,作者分析了2026年第一季度的钓鱼邮件数据,发现有超过21%的邮件使用了重定向。这些重定向机制多种多样,包括半开放、完全开放以及广告或跟踪系统中的重定向。特别是像Google这样的半开放重定向机制,虽然需要特定令牌,但这些令牌通常可重复使用且有效期长,容易被滥用。 最后,作者建议开发者确保自己的应用不暴露易被滥用的重定向端点,并在必要时监控和限制使用。 现在我需要将这些要点浓缩到100字以内。重点包括:开放重定向被滥用、用于钓鱼、合法域名欺骗、检测困难、攻击者持续利用、数据统计结果、机制多样性以及防范建议。 可能的结构:开放重定向被威胁行为者滥用用于钓鱼攻击;链接指向合法域名欺骗受害者;攻击者持续利用;统计数据显示其常见性;机制多样;建议开发者防范。 现在试着组织语言: “文章探讨了开放重定向被威胁行为者滥用的情况。虽然这种漏洞本身不算高风险,但常用于钓鱼攻击。链接指向合法域名欺骗受害者和检测机制。尽管OWASP不再列为顶级漏洞,攻击者仍持续利用。数据显示2026年第一季度有超过21%的钓鱼邮件使用了此类机制。建议开发者确保应用不暴露易被滥用的端点。” 检查字数:大约100字左右。 </think> 文章探讨了开放重定向被威胁行为者滥用的情况。虽然这种漏洞本身不算高风险,但常用于钓鱼攻击。链接指向合法域名欺骗受害者和检测机制。尽管OWASP不再列为顶级漏洞,攻击者仍持续利用。数据显示2026年第一季度有超过21%的钓鱼邮件使用了此类机制。建议开发者确保应用不暴露易被滥用的端点。 2026-4-6 08:50:27 Author: isc.sans.edu(查看原文) 阅读量:14 收藏
In one of his recent diaries, Johannes discussed how open redirects are actively being sought out by threat actors[1], which made me wonder about how commonly these mechanisms are actually misused…
Although open redirect is not generally considered a high-impact vulnerability on its own, it can have multiple negative implications. Johannes already covered one in connection with OAuth flows, but another important (mis)use case for them is phishing.
The reason is quite straightforward – links pointing to legitimate domains (such as google.com) included in phishing messages may appear benign to recipients and can also evade simpler e-mail scanners and other detection mechanisms.
Even though open redirect has not been listed in OWASP Top 10 for quite some time, it is clear that attackers have never stopped looking for it or using it. If I look at traffic on almost any one of my own domains, hardly a month goes by when I don’t see attempts to identify potentially vulnerable endpoints, such as:
/out.php?link=https://domain.tld/While these attempts are not particularly frequent, they are generally consistent.
We also continue to see open redirect used in phishing campaigns. Last year, I wrote about a campaign using a “half-open” (i.e., easily abusable) redirect mechanism on Google [2], and similar cases still seem to appear regularly.
But how regular are they, actually?
To find out, I reviewed phishing e-mails collected through my own filters and spam traps, as well as samples sent to us here at the ISC (either by our professional colleagues, or by threat actors themselves), over the first quarter of this year. Although the total sample only consisted of slightly more than 350 individual messages (and is therefore far from statistically representative), it still provided quite interesting results.
Redirect-based phishing accounted for a little over 21 % of all analyzed messages sent out over the first 3 months of 2026 – specifically for 32 % in January, 18 % in February and 16.5 % in March.
It should be noted that if a message contained multiple malicious links and at least one of them used a redirect, the entire message was counted exclusively as a redirect sample, and that not all redirect cases were classic "open redirects". In fact, the abused redirect mechanisms varied widely.
Some behaved similarly to the aforementioned Google-style “half-open” redirects (see details below), while others were fully open. In some cases, the redirectors were part of tracking or advertising systems, while in others, they were implemented as logout endpoints or similar mechanisms. It should be noted that URL shorteners were also counted as redirectors (although these were not particularly common).
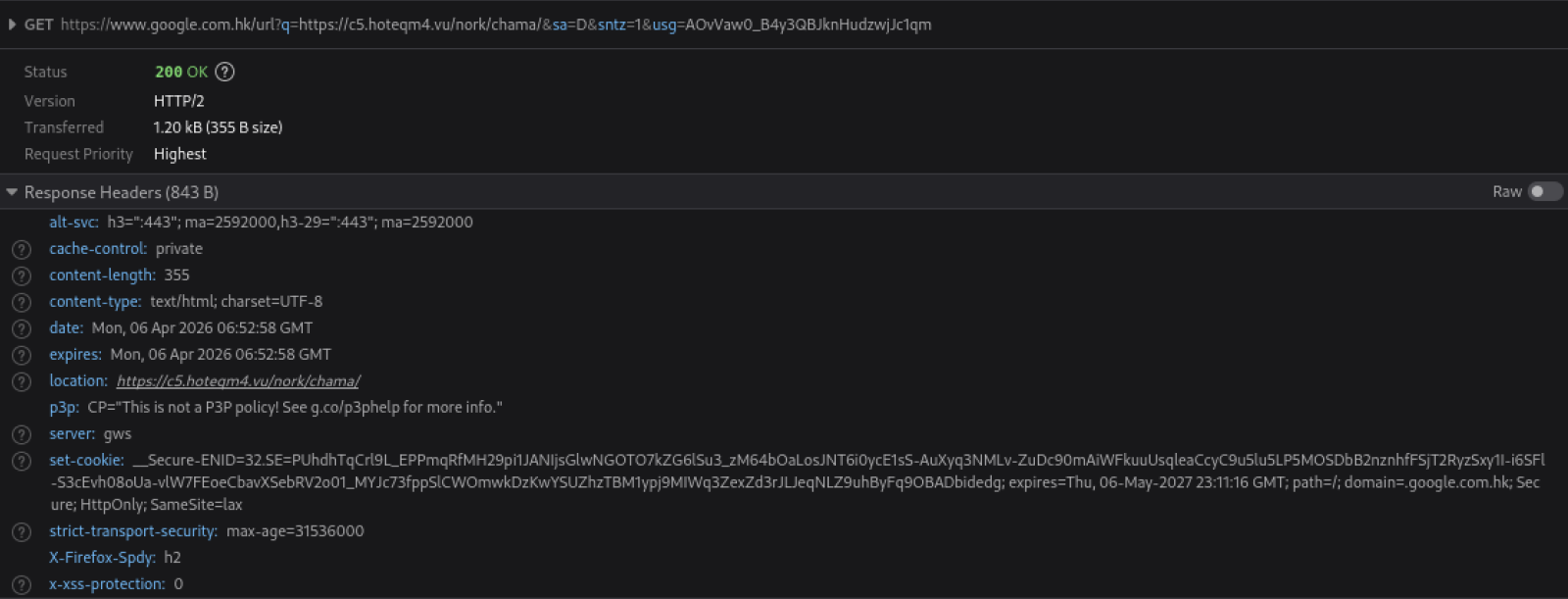
As we mentioned, the Google-style redirects are not fully open. They do require a specific valid token to work, however, since these tokens are typically reusable, have a very long lifetime, and are not tied to any specific context (such as IP address or session), they can be – and are – readily reused in phishing campaigns.
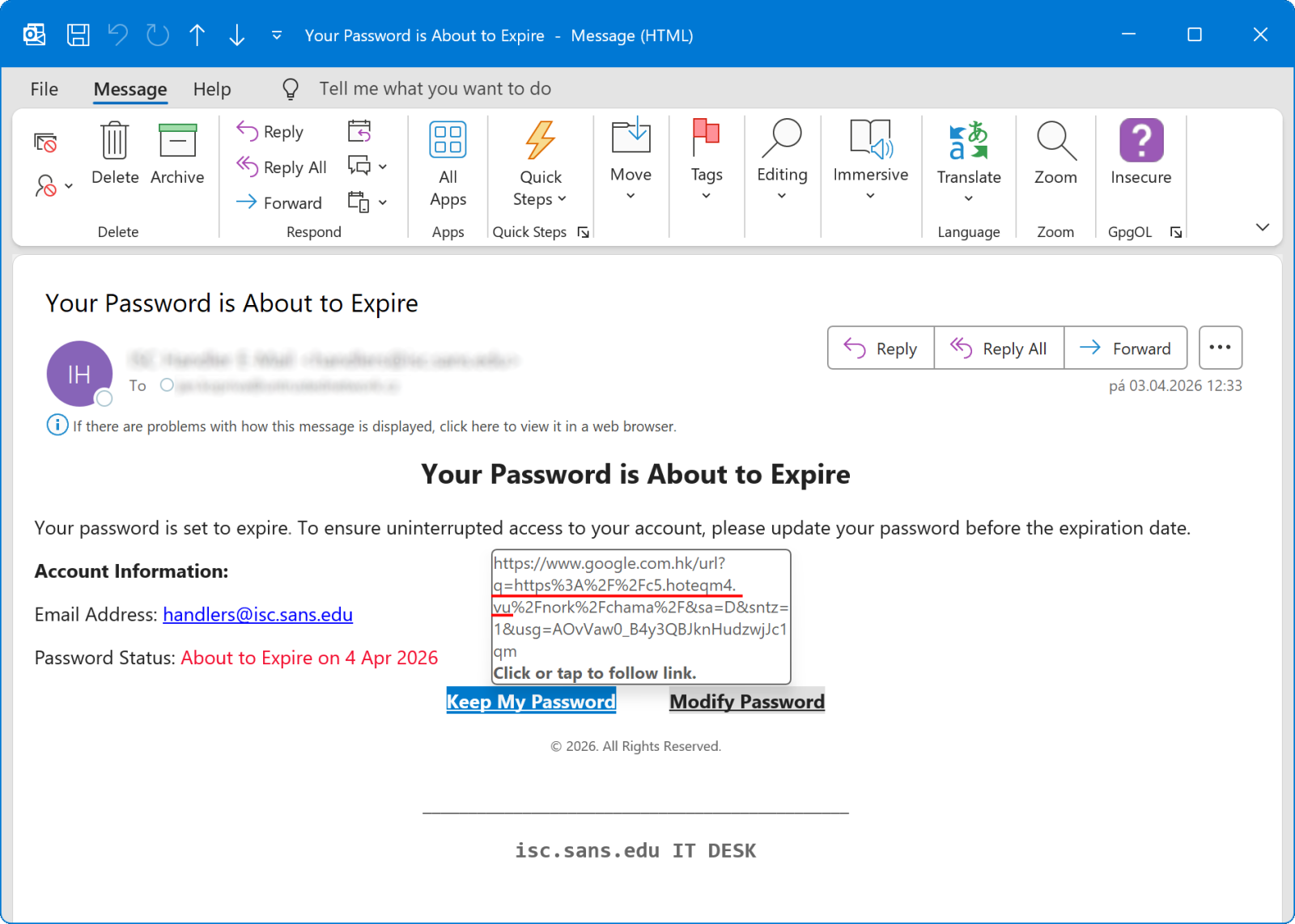
An example of such a phishing message and subsequent redirection can be seen in the following images. Though, to avoid focusing solely on Google, it should be mentioned that similar redirect mechanisms on other platforms (e.g., Bing) are also being abused in the same way.
As we can see, although open redirect is commonly considered more of a nuisance issue than an actual high-risk vulnerability these days, it doesn’t keep malicious actors from misusing it quite heavily… Which means we shouldn’t just ignore it.
At the very least, it is worth ensuring that our own applications do not expose endpoints that can be misused in this way. And where any redirection functionality is strictly required, it should be monitored for abuse and restricted as necessary.
[1] https://isc.sans.edu/diary/Open+Redirects+A+Forgotten+Vulnerability/32742
[2] https://isc.sans.edu/diary/Another+day+another+phishing+campaign+abusing+googlecom+open+redirects/31950
-----------
Jan Kopriva
LinkedIn
Nettles Consulting
如有侵权请联系:admin#unsafe.sh