
嗯,用户让我总结一下这篇文章的内容,控制在一百个字以内。首先,我需要通读文章,抓住主要观点。 文章主要讲的是供应链攻击变得越来越频繁,攻击者利用这些攻击获取开发者的高权限凭证,形成了一个“开发者凭证经济”。传统的EDR工具在检测和响应执行层的威胁方面有效,但对供应链攻击中的凭证盗窃无能为力,因为它们无法监控CI/CD环境。 接下来,文章提出了CTEM(持续威胁暴露管理)作为解决方案,强调预先识别和消除风险条件的重要性。这包括硬ening措施、限制身份权限以及进行反侦察。 所以,总结时需要涵盖供应链攻击的新趋势、EDR的局限性以及CTEM的必要性。控制在100字以内,语言要简洁明了。 </think> 供应链攻击正通过窃取高权限开发者凭证形成“开发者凭证经济”,传统EDR工具无法有效应对此类威胁。需采用持续威胁暴露管理(CTEM)策略,在攻击发生前识别并消除风险条件。 2026-4-3 18:50:57 Author: www.tenable.com(查看原文) 阅读量:6 收藏

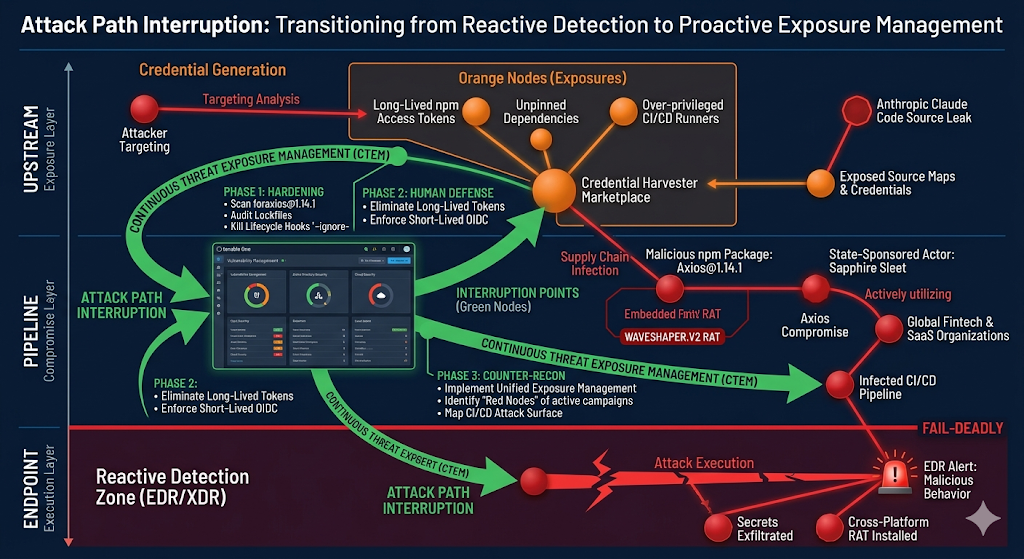
Recent supply chain attacks have highlighted an urgent need for organizations to shift from a reactive security posture to a preemptive exposure management strategy. Learn why endpoint detection and response tools don’t have you covered when highly privileged developer credentials get exposed.
Key takeaways:
- Recent supply chain attacks are emblematic of an insidious new trend in cybercrime: Threat actors are increasingly using supply chain attacks to harvest highly privileged developer credentials and create a “Developer Credential Economy,” a lucrative black market for API keys, secrets, and cloud access tokens.
- Relying on execution-layer detection, such as EDR, is insufficient against supply chain threats because these tools lack visibility into the ephemeral CI/CD environments where credential theft and weaponization actually occur.
- Neutralizing the systemic infrastructure risk created by the Developer Credential Economy requires a continuous threat exposure management (CTEM) approach to proactively identify and eliminate exposure conditions, such as long-lived access tokens, before an attacker can exploit them.
Background
The convergence of the Anthropic Claude Code source leak and the Sapphire Sleet (UNC1069) Axios compromise has collapsed the boundary between traditional malware and systemic infrastructure risk. Our analysis of the exposure intelligence data reveals that the cluster of supply chain attacks observed in March 2026 should not be viewed as disparate incidents; rather, they signify the new operational reality of a high-velocity “Developer Credential Economy,” a black market for highly privileged developer credentials.
In this new reality, attackers are no longer just hacking software supply chains; they’re systematically using supply chain attacks to harvest the very keys to the kingdom from the tools security teams trust most.
The myth of the EDR singularity
Microsoft and Google have independently attributed the recent Axios compromise to a North Korean state actor. Industry narratives have framed the compromise, which backdoored an npm-managed JavaScript library package with 100 million weekly downloads, as a victory for endpoint detection and response (EDR). The logic seems simple: EDR caught and stopped the payload at execution, therefore EDR is the solution.
This is a dangerous miscalculation. The concept of an EDR singularity, where Endpoint Detection and Response (EDR) solutions become so comprehensive, intelligent, and autonomous that they negate the need for virtually all other security tools and human intervention at the endpoint is a powerful and seductive myth dominating the current security landscape. This narrative suggests that, through advancements in machine learning, behavioral analytics, and automated response capabilities, a single, all-encompassing EDR platform will eventually unify and solve the bulk of security challenges.
Relying on EDR to stop a supply chain attack is like relying on a smoke detector while storing open canisters of gasoline in your kitchen. Our analysis shows that by the time an EDR agent fires on the WAVESHAPER.V2 RAT, the true damage — the exposure — has already occurred. This demonstrates the urgent need for organizations to shift from a reactive to a preemptive cybersecurity posture.
- EDR is reactive: It monitors execution, not the conditions that allow it. It cannot see the misconfigured GitHub Action or the over-privileged npm token that enabled the compromise in the first place.
- The coverage gap: EDR has zero visibility into the ephemeral CI/CD runners and build environments where these credentials are stolen. In the Developer Credential Economy, the theft happens where the agents aren't.
- The fail-deadly speed: In the Axios campaign, the malware was designed to exfiltrate secrets and self-destruct within seconds; typically faster than an EDR alert can be triaged by a human analyst.
- EDR evasion is not theoretical: EDR evasion is an active, industrialized capability. Threat actors routinely bypass kernel-level EDR through bring your own vulnerable driver (BYOVD) attacks, where adversaries load legitimately signed but vulnerable kernel drivers to disable or blind EDR agents.
Targeting analysis: Mapping the credential generation layer
Adversaries are increasingly compromising and weaponizing critical chokepoint tools used by developers and security teams, like the Axios npm package and the KICS IaC scanner. This trend, which involves moving upstream in the development lifecycle, reveals a distinct division of labor within this emerging threat economy.
| Actor / Group | Operational focus | Primary target | Vertical Impact |
|---|---|---|---|
| TeamPCP | Generation layer: Bulk credential harvesting via tool exploitation | Trivy, LiteLLM, KICS (Security/Dev tools) | Global SaaS & AI infrastructure |
| Sapphire Sleet | Weaponization layer: State-sponsored exfiltration and revenue generation | Axios, npm ecosystem | Fintech, Crypto, Government |
| GlassWorm | Opportunistic layer: High-volume automated theft | VSCode extensions, OpenVSX | Blockchain & Web3 |
Actors are successfully exploiting exposures, such as long-lived tokens, overprivileged CI/CD runners, and unpinned dependencies, to force organizations into a reactive posture.
Exposure intelligence: The shift to CTEM
To escape this pattern, defenders must shift from merely reacting to malware to adopting continuous threat exposure management (CTEM) as a preemptive strategy.
While AI companies market their frontier models as security tools, the recent leak of 512,000 lines of Claude source code demonstrates that AI is just another asset with its own massive exposure profile.
A mature CTEM program, powered by exposure intelligence, focuses on the preemptive actions that actually reduce risk:
- Phase 1: Hardening (The Kill Switch): Organizations must audit lockfiles and kill lifecycle hooks (--ignore-scripts) immediately. This eliminates the postinstall vector that Sapphire Sleet used to deploy WAVESHAPER.V2.
- Phase 2: Human/Identity defense: We must eliminate long-lived tokens. The Axios compromise succeeded because a single stolen token bypassed every security control. Transitioning to short-lived, OIDC-based automation is an exposure management requirement, not a nice-to-have.
- Phase 3: Counter-recon: Use Tenable One to map your full attack surface, including the CI/CD pipelines and cloud-native build stages that EDR cannot reach.
The bottom line
The Axios and Anthropic events are a wake-up call for the C-suite. Theoretical severity and reactive detection (EDR) are insufficient against an adversary that has industrialized the theft of developer identities.
Exposure management should be your first and primary line of defense. By identifying and remediating the exposure conditions that supply chain attacks depend on, we can stop the payload before it ever reaches the endpoint.
Get more information
- Read the Tenable Research Special Operations Advisory on the Axios npm Compromise
- Accelerate your preemptive security with Tenable’s agentic engine, Hexa AI
- Explore Tenable One for Exposure Management
Join Tenable's Research Special Operations (RSO) Team on Tenable Connect for further discussions on the latest cyber threats.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.

Research Special Operations
The Research Special Operations (RSO) team serves as Tenable’s Forward Logistics Element in the threat landscape, providing customers with the analyses and contextualized exposure intelligence required to manage risks to critical business assets. With over 150 years of collective expertise, this hand-picked group of world-class security researchers is united with one mission: to cut through the noise and deliver critical intelligence about the most dangerous cyber threats emerging right now. Uniting the missions of the Tenable Security Response, Zero-Day Research, and Decision Science Operations teams, RSO disseminates timely, accurate, and actionable information about the latest threats and exposures.
- Exposure Management
- Vulnerability Management
Cybersecurity news you can use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
如有侵权请联系:admin#unsafe.sh