
好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解主要信息。 文章讲的是Drift Protocol遭受了黑客攻击,损失了约2.8亿美元。黑客是朝鲜的威胁行为者,他们利用了预先签名的交易和Nonce账户来延迟执行并精准攻击。攻击发生在4月1日,黑客获得了管理员权限,转移资金。Drift强调没有漏洞被利用,种子短语也没有被泄露。现在平台正在与安全公司和执法机构合作追回资金,并承诺发布详细报告。 接下来,我需要将这些关键点浓缩到100字以内。重点包括:攻击发生的时间、损失金额、黑客身份、攻击手法、平台回应措施。 然后组织语言,确保简洁明了。避免使用复杂的术语,让总结易于理解。 最后检查字数,确保不超过限制。 </think> Drift Protocol遭遇黑客攻击,损失约2.8亿美元。朝鲜威胁行为者利用预先签名交易和Nonce账户,在4月1日获取管理员权限并转移资金。攻击未利用平台漏洞或泄露种子短语。Drift正与安全公司和执法机构合作追回资金,并承诺发布详细报告。 2026-4-3 05:30:19 Author: www.bleepingcomputer.com(查看原文) 阅读量:17 收藏

Update: Revised story and title based on new information linking the attack with North Korean hackers.
The Drift Protocol lost at least $280 million after a threat actor took control of its Security Council administrative powers in a planned, sophisticated operation.
Blockchain intelligence firms Elliptic and TRM Labs linked the attacks to North Korean threat actors, based on multiple on-chain indicators consistent with DPRK tradecraft.
These include Tornado Cash usage, CarbonVote deployment timing (09:30 Pyongyang time), cross-chain bridging patterns, and rapid large-scale laundering, consistent with the Bybit hack.
The attacker leveraged durable nonce accounts and pre-signed transactions to delay execution and strike with accuracy at a chosen time, the platform explained.
Drift underlines that the hacker did not exploit any flaws in its programs or smart contracts, and no seed phrases have been compromised.
Drift Protocol is a DeFi trading platform built on the Solana blockchain that serves as a non-custodial exchange, giving users full control of their funds as they interact with on-chain markets.
As of late 2024, the platform claimed to have 200,000 traders, supporting total trading volumes of more than $55 billion and a daily peak of $13 million.
According to Drift's report, the heist was prepared between March 23 and 30, with the attacker setting up durable nonce accounts and obtaining 2/5 multisig approvals from Security Council members to meet the required threshold.
This enabled them to pre-sign malicious transactions that weren’t executed immediately.
On April 1st, the attacker performed a legitimate transaction and immediately executed the pre-signed malicious transactions, transferring admin control to themselves within minutes.
Having gained admin control, they introduced a malicious asset, removed withdrawal limits, and eventually drained funds.
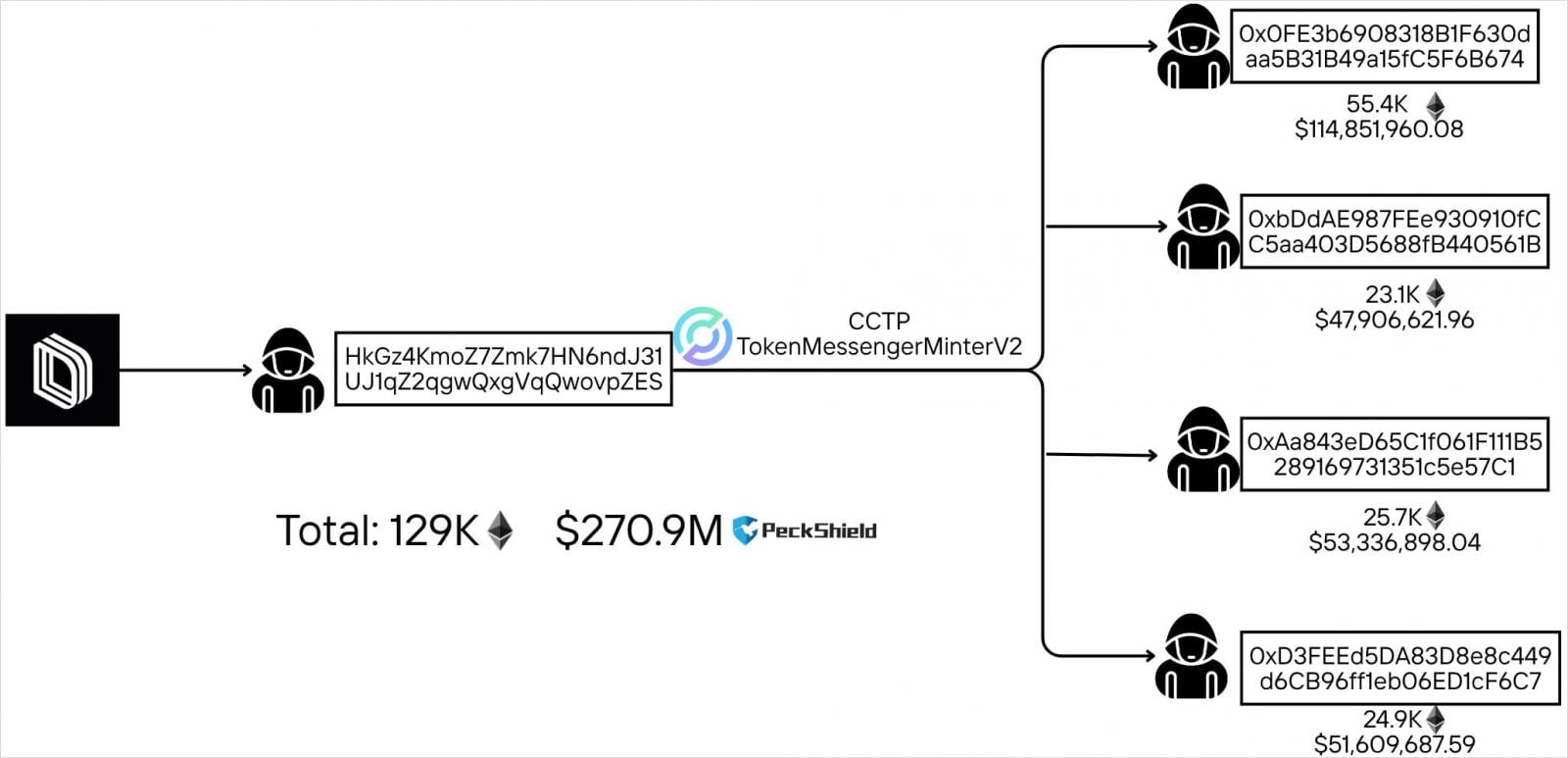
Drift Protocol estimates the losses at about $280 million, while blockchain tracking account PeckShieldAlert has calculated them at $285 million.
When unusual activity on the protocol was detected, Drift issued a public warning to users, stating that started an investigation and urging them not to deposit any funds until further notice.
As a result of the attack, borrow/lend deposits, vault deposits, and trading funds have been affected, and all protocol functions are now essentially frozen. Drift said DSOL is unaffected, and insurance fund assets are secured.
The platform is now working with security firms, cryptocurrency exchanges, and law enforcement authorities to trace and freeze the stolen funds.
Drift promised to publish a detailed post-mortem report in the coming days.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
.png)
