
嗯,用户让我帮忙总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头,直接写描述。首先,我需要仔细阅读这篇文章,理解其主要内容。 文章讲的是欧盟的网络安全服务CERT-EU将欧洲委员会云系统的入侵事件归咎于TeamPCP威胁集团。入侵导致至少29个欧盟实体的数据泄露。事件发生在3月10日,TeamPCP利用被窃取的亚马逊网络服务API密钥进入系统,之后他们使用TruffleHog工具搜索更多秘密,并创建新的访问密钥以逃避检测。随后,他们在暗网上泄露了数据,包括个人姓名、电子邮件地址和内容。CERT-EU分析确认了数据泄露的情况,并指出没有网站被关闭或篡改。 接下来,我需要将这些信息浓缩到100字以内。重点包括:CERT-EU归咎于TeamPCP,入侵导致29个实体的数据泄露,使用API密钥和工具进行攻击,数据在暗网上泄露,包含个人信息和邮件内容。 可能的结构是:欧盟网络安全机构将云入侵归咎于TeamPCP集团,导致29个实体数据泄露。入侵者利用API密钥和工具窃取信息,并在暗网上发布包含个人数据的90GB档案。 检查一下字数是否合适。确保不超过100字,并且信息准确全面。 </think> 欧盟网络安全机构将欧洲委员会云系统入侵归咎于TeamPCP威胁集团,导致至少29个欧盟实体的数据泄露。入侵者利用被窃取的亚马逊网络服务API密钥进入系统,并使用TruffleHog工具搜索更多秘密。随后他们在暗网上泄露了包含个人姓名、电子邮件地址和内容的90GB数据档案。 2026-4-3 06:45:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:44 收藏

The European Union's Cybersecurity Service (CERT-EU) has attributed the European Commission cloud hack to the TeamPCP threat group, saying the resulting breach exposed the data of at least 29 other Union entities.
The European Commission publicly disclosed the incident on March 27 after BleepingComputer reached out for confirmation that the Amazon cloud environment of the European Union's main executive body had been breached.
Two days earlier, the Commission notified CERT-EU of the hack, saying that its Cybersecurity Operations Center was not alerted to API misuse, potential account compromise, or any abnormal network traffic until March 24, five days after the initial intrusion.
On March 10, TeamPCP used a compromised Amazon Web Services API key with management rights over other European Commission AWS accounts (stolen in the Trivy supply-chain attack) to breach the Commission's Amazon cloud environment.
In the next stage of the attack, they used TruffleHog (a tool for scanning and validating cloud credentials) to search for additional secrets, then attached a newly created access key to an existing user to evade detection before conducting further reconnaissance and stealing data.
TeamPCP has been linked to supply-chain attacks targeting multiple other developer code platforms, such as GitHub, PyPi, NPM, and Docker.
The cybercrime gang has also compromised the LiteLLM PyPI package in an attack that impacted tens of thousands of devices using its "TeamPCP Cloud Stealer" information-stealing malware.
Data leaked on the dark web by ShinyHunters
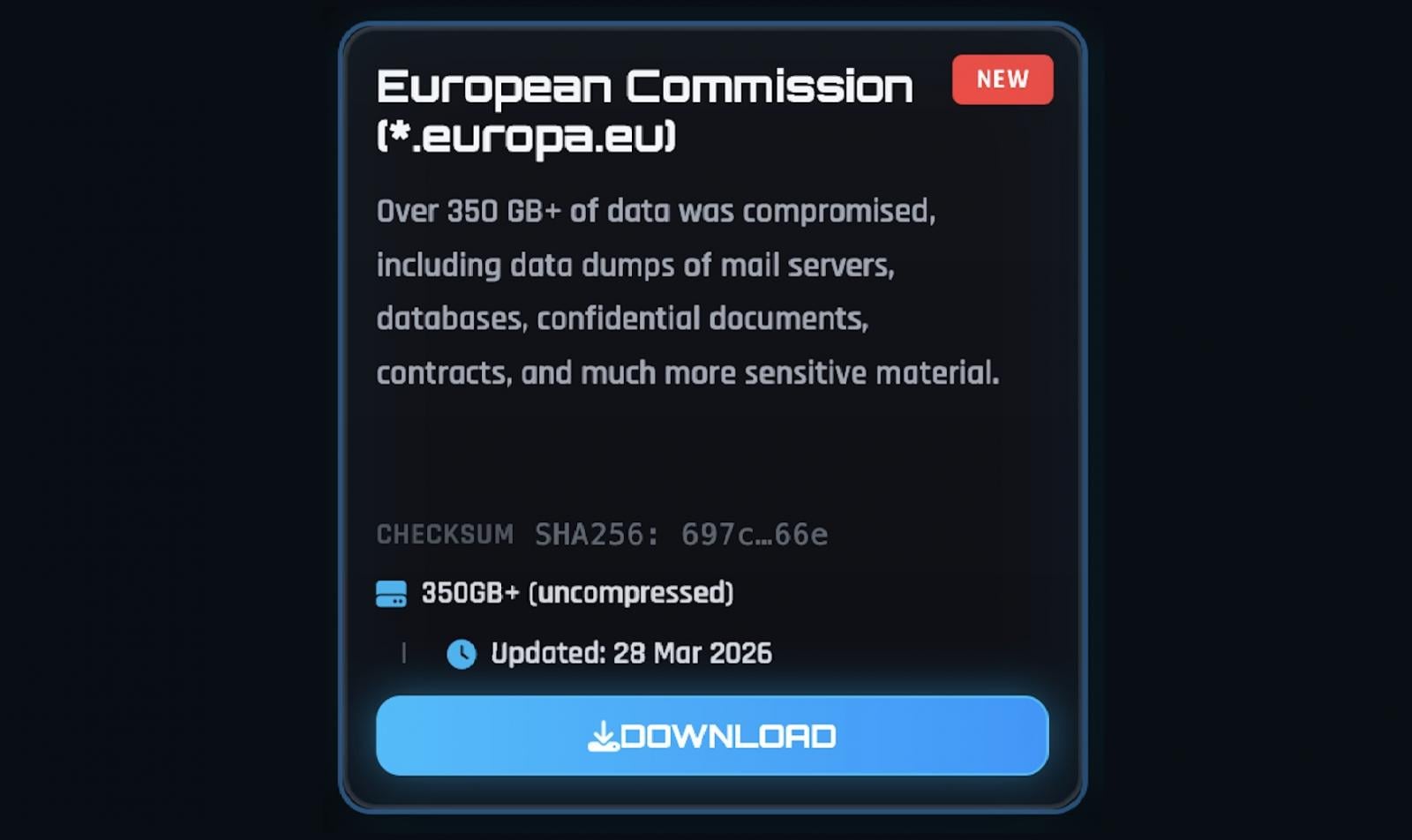
On March 28, data extortion group ShinyHunters published the stolen dataset on their dark web leak site as a 90GB archive of documents (approximately 340GB uncompressed), containing names, email addresses, and email content.
CERT-EU's analysis confirmed that the threat actors have stolen tens of thousands of files containing personal information, usernames, email addresses, and email content, and that the resulting data breach potentially affects 42 internal European Commission clients and at least 29 other Union entities using the europa.eu web hosting service.
"The threat actor used the compromised AWS secret to exfiltrate data from the affected cloud environment. The exfiltrated data relates to websites hosted for up to 71 clients of the Europa web hosting service: 42 internal clients of the European Commission, and at least 29 other Union entities," CERT-EU said on Thursday.
"Analysis of the published dataset has so far confirmed the presence of personal data, including lists of names, last names, usernames, and email addresses, predominantly from the European Commission’s websites but potentially pertaining to users across multiple Union entities," it added.
"The dataset also contains at least 51,992 files related to outbound email communications, totalling 2.22 GB. The majority of these are automated notifications with little to no content. However, 'bounce-back' notifications, which are responses to incoming messages from users, may contain the original user-submitted content, posing a risk of personal data exposure."
CERT-EU added that no websites were taken offline as a result of this incident or tampered with, and no lateral movement to other Commission AWS accounts has been detected.
While the analysis of exfiltrated databases and files is ongoing and will likely require "a considerable amount of time," the Commission has notified relevant data protection authorities and is in direct communication with affected entities.
In February, the European Commission disclosed another data breach after discovering that a mobile device management platform used to manage staff's devices had been hacked.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
