好的,我现在需要帮用户总结一篇关于安全摄像头和物联网设备被攻击的文章,控制在100字以内。首先,我得通读整篇文章,抓住主要观点。 文章主要讲的是安全摄像头、物联网和运营技术设备容易被攻击者利用,成为攻击工具。比如国家黑客利用这些设备进行侦察、间谍活动、勒索软件攻击和僵尸网络构建。问题在于这些设备存在结构上的弱点,比如默认密码、补丁不及时、直接暴露在互联网上等。 然后,文章提到零信任网络连接(ZTc)作为解决方案,它在网络层实施零信任原则,阻止未经授权的连接,不需要端点代理,支持去中心化部署。 接下来,我需要将这些要点浓缩成100字以内的总结。要注意不要使用“文章内容总结”之类的开头词,直接描述内容。 可能的结构是:首先指出设备易受攻击的问题,然后列举攻击用途的例子,接着说明结构性弱点带来的风险,最后提出ZTc的解决方案。 确保语言简洁明了,涵盖关键点:易受攻击、用途多样、结构性弱点、ZTc的优势。 </think> 安全摄像头、物联网和OT设备因默认凭证、补丁不足及互联网暴露等弱点易受攻击。这些设备被用于侦察、间谍活动、勒索软件和僵尸网络等攻击。零信任网络连接(ZTc)通过在网络层实施零信任原则提供解决方案,阻止未经授权的连接并支持去中心化部署。 2026-4-2 22:5:29 Author: securityboulevard.com(查看原文) 阅读量:3 收藏
TL;DR
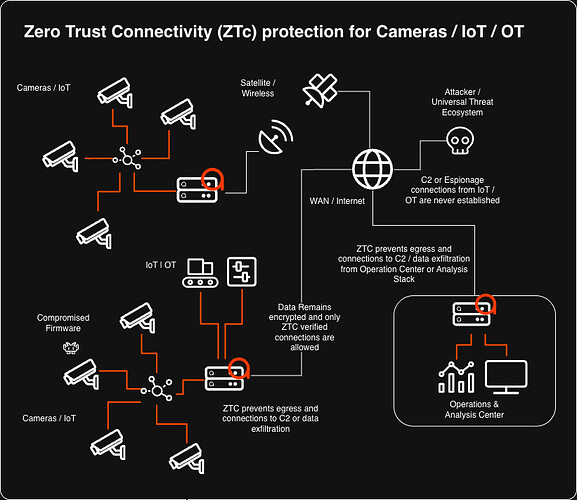
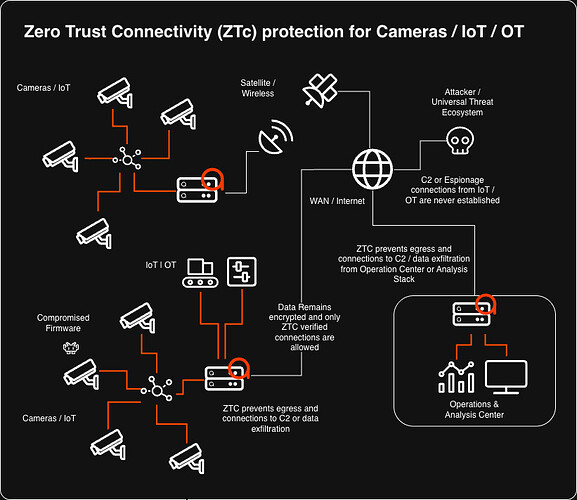
Security cameras, IoT, and OT devices that are meant to protect us, are easily compromised and turned against defenders, enabling nation-state reconnaissance (Iranian hacks on Hikvision/Dahua cameras during strikes, Russian webcam abuse in Ukraine), espionage via exposed live feeds, ransomware pivots (Akira group bypassing EDR), massive botnets (Mirai/Eleven11bot), and physical disruption. Structural weaknesses like default credentials, poor patching, internet exposure, supply-chain risks and espionage by design makes them ideal attacker tools, especially since they can’t receive endpoint security agents. Zero Trust Connectivity (ZTc) solves this by enforcing network-level Zero Trust: it blocks unauthorized connections before they form, requires no endpoint agents, prevents lateral movement, and supports decentralized deployment with sovereign data custody — giving defenders a powerful way to secure all devices without traditional detection or centralized decryption. In short, the watcher must be properly isolated at the network layer. In cybersecurity, the watcher must be watched most closely of all.
Turning Defense Technology Against the Defenders
We live in an era where security cameras, smart sensors, industrial controllers, other Internet of Things (IoT) and Operational Technology (OT) devices are deployed everywhere—from traffic poles, corporate boardrooms and factory floors to homes and critical infrastructure. They are meant to watch, alert, and protect. Yet when attackers gain control, these very devices become potent weapons in their hands: silent observers feeding real-time intelligence, hidden pivots into protected networks, launchpads for massive distributed denial-of-service (DDoS) attacks, or even tools for physical disruption and espionage.
The problem is structural. Many IoT and OT devices ship with default credentials, receive infrequent (or no) firmware updates, lack proper network segmentation, and are exposed directly to the internet. Even in well managed deployments of IoT and OT, the supply chain threat is an additional attack vector. In cases where defenders patch devices to the latest firmware update, attackers could still be turning their equipment against them by pushing compromised firmware to the devices.
Once breached they grant attackers low-effort footholds. From there, the devices can be repurposed for reconnaissance, lateral movement, data exfiltration, or amplification of larger campaigns. In OT environments, where these devices increasingly converge with IT networks, a single compromised camera or sensor can open the door to industrial control systems (ICS) that manage physical processes. Cyber as a warfare domain could be the area where underfunded or outgunned adversaries can cause the most damage.
Security researchers and government agencies have repeatedly warned against these risks but the threat is no longer theoretical. Adding to the complexity is the problem that no endpoint agent can be deployed on these devices and a single device compromised could be the only potential connection point the attackers need to advance their attack.
In the light of defending against abuse of security cameras, the following are important aspects to consider:
State Actors Weaponize Cameras for Battlefield Intelligence
In March 2026, researchers at Check Point documented hundreds of hacking attempts by Iranian-linked threat actors targeting internet-connected Hikvision and Dahua IP cameras across Israel, Bahrain, Cyprus, Kuwait, Lebanon, Qatar, and the UAE. The attempts were timed to coincide with Iranian missile and drone strikes, suggesting the cameras were being hijacked for real-time reconnaissance—spotting targets, assessing damage, or guiding follow-on kinetic operations. The attackers exploited known vulnerabilities in the cameras’ firmware and used commercial VPNs and VPS infrastructure to scan and compromise devices.
This mirrors earlier Russian tactics. In January 2024, Russian operatives compromised residential webcams in Kyiv, Ukraine, to monitor air-defense systems and critical infrastructure ahead of missile strikes; some feeds were even streamed publicly on YouTube. A May 2025 joint advisory from more than 20 international agencies (including the U.S., UK, Australia, and others) warned of an ongoing Russian GRU campaign that systematically targeted RTSP servers hosting IP cameras at Western logistics and technology firms, primarily to harvest live imagery and metadata from Ukrainian networks.
Exposed Cameras as Everyday Espionage Tools
In June 2025, cybersecurity firm Bitsight identified more than 40,000 security cameras worldwide with live feeds accessible via nothing more than a web browser and an IP address. Many were located in homes, offices, factories, and public spaces; attackers could view interiors, employee movements, or manufacturing processes in real time. Dark-web forums openly discussed tools to locate and abuse these exposures.
Nation State Espionage Interest
Nation States with an interest in espionage are funnelling data in huge quantity to be processed and harvested for information. Especially concerning China, a myriad of reports show concrete evidence of automatic “phoning home” behavior, persistent data exfiltration even when cloud features are disabled, and specific incidents of communication with China-based servers. This aligns with broader concerns under China’s National Intelligence Law, which requires companies to assist state intelligence efforts.
IoT Cameras as Ransomware Springboards
In early 2025, the Akira ransomware group demonstrated a particularly creative pivot. After endpoint detection and response (EDR) tools blocked their Windows-based encryptor, attackers gained remote shell access to an unsecured Linux-based IP webcam on the victim’s network. From the camera they mounted network shares, exfiltrated data, and launched the ransomware payload—bypassing traditional defenses entirely.
Botnet Armies Built from Hijacked Cameras
Compromised IP cameras and network video recorders (NVRs) remain favorite building blocks for massive botnets. In June 2025, the Eleven11bot malware infected roughly 30,000 devices—mostly outdated IP cameras and NVRs—turning them into a coordinated attack infrastructure. Variants of the decade-old Mirai malware continue to evolve, exploiting unpatched flaws such as those in AVTECH cameras as late as 2024–2025.
Critical Infrastructure at Risk
Unpatched vulnerabilities in AVTECH IP cameras—widely used in finance, healthcare, transportation, and other critical sectors—were actively leveraged to spread Mirai-based malware, prompting advisories from the U.S. Cybersecurity and Infrastructure Security Agency (CISA).
Physical disruption is easily achieved. In July 2025, a cyberattack on the Netherlands’ Public Prosecution Service rendered dozens of speed cameras permanently offline (or at least kept them from being reactivated), demonstrating how compromised camera infrastructure can directly impair law-enforcement capabilities.
These incidents show a clear pattern: attackers no longer need sophisticated zero-days to cause harm. They simply locate the weakest link in the expanding IoT/OT attack surface—often a camera —and repurpose it. The consequences range from privacy violations and espionage to physical-world kinetic support in Cyber War and large-scale service outages.
The good news is that advances in technology does not only provide more leverage to attackers – Defenders also have access to new tools: Enter Zero Trust Connectivity – a new expression of Zero Trust that is implemented on the network level, can disrupt attacks before they could establish a connection. This requires no endpoint agent and does not rely on detecting an attack before the attack could be disrupted. Deployment is decentralized which aids in resilience and facilitates sovereign data custody – meaning there is no centralized data flow or decryption required that has traditionally hindered IoT devices that contain confidential data from being protected by 3rd party security systems.
Defenders must treat every camera, sensor, and OT endpoint with the same rigor as traditional IT assets: enforce strong, unique credentials; implement network segmentation (never expose OT/IoT devices directly to the internet); apply verified patches promptly; monitor for anomalous behavior; and adopt zero-trust principles even for “dumb” devices. The vulnerability protection of ZeroTrust Connectivity without the need to detect intrusions & asset inventory are no longer optional—they are table stakes.
The uncomfortable truth is that the eyes we install to watch over us can just as easily watch for our adversaries. In cybersecurity, the watcher must be watched most closely of all.
Additional Reading:
Purdue 2.0? : Rising to the Challenge to secure OT with Zero Trust Connectivity – The ADAM Blog – ADAMnetworks – Explains the role of Zero Trust Connectivity applied to the protection of OT and Critical Infrastructure
“Wartime Usage of Compromised IP Cameras Highlight Their Danger” – Discusses Iranian, Russian, and other actors exploiting cameras for real-time intelligence in conflicts.
“When Smart Cameras Turn Blind: The Growing Cyber Threat to IoT Security Systems” – Covers vulnerabilities in smart camera infrastructure and attacks like the Netherlands speed camera incident.
“The Hidden Security Crisis: Why Your IoT Devices Are Handing Attackers the Keys to Your Network” – Details the Akira ransomware case using a compromised IP webcam as a pivot.
Healing a Broken Philosophy that Keeps Hurting Healthcare – Explores the vulnerability of IoT technologies and how Zero Trust Connectivity provides a solution for protecting technology debt in IoT-rich environments.
1 post – 1 participant
*** This is a Security Bloggers Network syndicated blog from The ADAM Blog - ADAMnetworks authored by Francois_Driessen. Read the original post at: https://support.adamnet.works/t/when-your-own-eyes-turn-against-you-how-compromised-security-cameras-and-iot-ot-devices-become-tools-for-your-attackers/1532
如有侵权请联系:admin#unsafe.sh