
嗯,用户让我用中文帮他总结一篇文章,控制在100字以内,而且不需要特定的开头。好的,我得先仔细阅读文章内容。 文章讲的是威胁分子利用Claude Code的源代码泄露事件,创建虚假的GitHub仓库来传播Vidar恶意软件。Claude Code是Anthropic公司的AI代理工具,最近泄露了源代码,导致很多用户下载并传播。Zscaler报告说,攻击者利用这个机会,在GitHub上发布假的泄露仓库,吸引用户下载包含恶意软件的压缩包。 我需要把这些关键点浓缩到100字以内。首先说明威胁分子的行为:利用泄露创建虚假仓库。然后提到传播的是Vidar信息窃取软件。接着说明这些仓库如何吸引用户,比如优化搜索排名和伪装功能解锁。最后点出下载后会释放恶意软件和代理工具。 现在组织语言:威胁分子利用Claude Code源代码泄露,在GitHub上创建虚假仓库传播Vidar恶意软件。这些仓库通过优化搜索结果和伪装功能吸引用户下载包含恶意软件的压缩包。 检查字数:大约在90字左右,符合要求。没有使用“文章内容总结”之类的开头,直接描述内容。 </think> 威胁分子利用Claude Code源代码泄露事件,在GitHub上创建虚假仓库以传播Vidar信息窃取恶意软件。这些恶意仓库通过优化搜索结果和伪装功能吸引用户下载包含恶意软件的压缩包。 2026-4-2 20:45:18 Author: www.bleepingcomputer.com(查看原文) 阅读量:19 收藏
Threat actors are exploiting the recent Claude Code source code leak by using fake GitHub repositories to deliver Vidar information-stealing malware.
Claude Code is a terminal-based AI agent from Anthropic, designed to execute coding tasks directly in the terminal and act as an autonomous agent, capable of direct system interaction, LLM API call handling, MCP integration, and persistent memory.
On March 31, Anthropic accidentally exposed the full client-side source code of the new tool via a 59.8 MB JavaScript source map included by accident in the published npm package.
The leak contained 513,000 lines of unobfuscated TypeScript across 1,906 files, revealing the agent’s orchestration logic, permissions, and execution systems, hidden features, build details, and security-related internals.
The exposed code was rapidly downloaded by a large number of users and published on GitHub, where it was forked thousands of times.
According to a report from cloud security company Zscaler, the leak created an opportunity for threat actors to deliver the Vidar infostealer to users looking for the Claude Code leak.
The researchers found that a malicious GitHub repository published by user “idbzoomh” posted a fake leak and advertised it as having “unlocked enterprise features” and no usage restrictions.
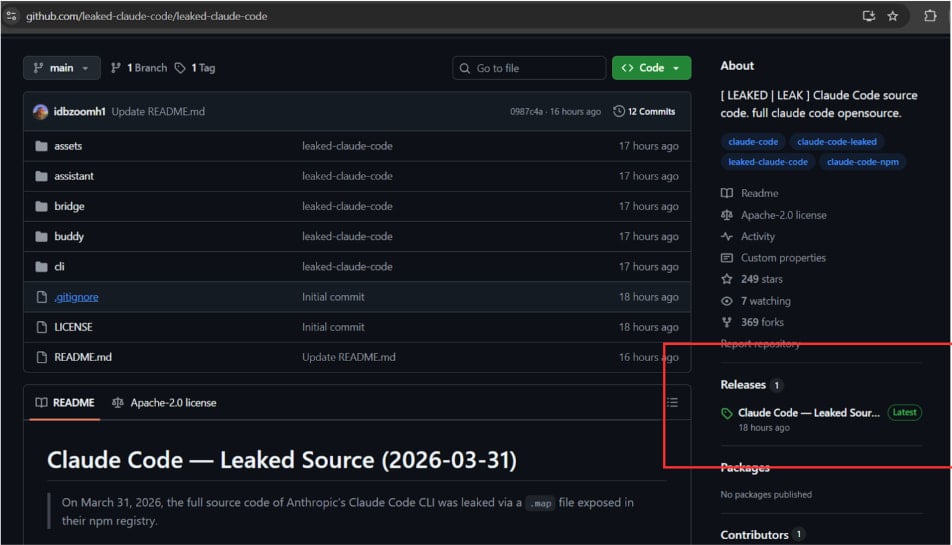
Source: Zscaler
To drive as much traffic to the bogus leak, the repository is optimized for search engines and is shown among the first results on Google Search for queries like “leaked Claude Code.”
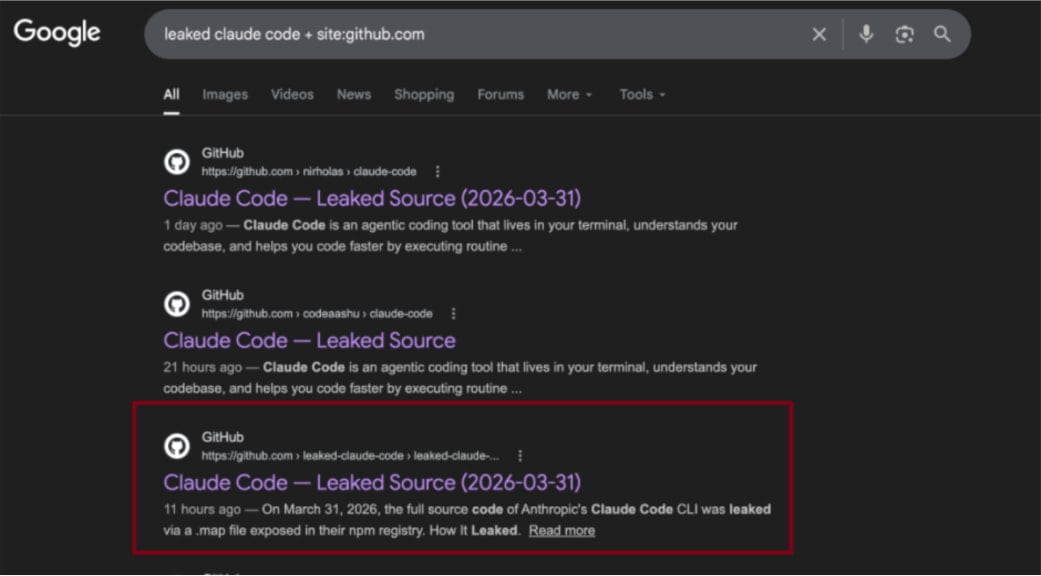
Source: Zscaler
According to the researchers, curious users download a 7-Zip archive that contains a Rust-based executable named ClaudeCode_x64.exe. When launched, the dropper deploys Vidar, a commodity information stealer, along with the GhostSocks network traffic proxying tool.
Zscaler discovered that the malicious archive is updated frequently, so other payloads may be added in future iterations.
The researchers also spotted a second GitHub repository with identical code, but it instead shows a ‘Download ZIP’ button that wasn’t functional at the time of analysis. Zscaler estimates it is operated by the same threat actor who likely experiments with delivery strategies.
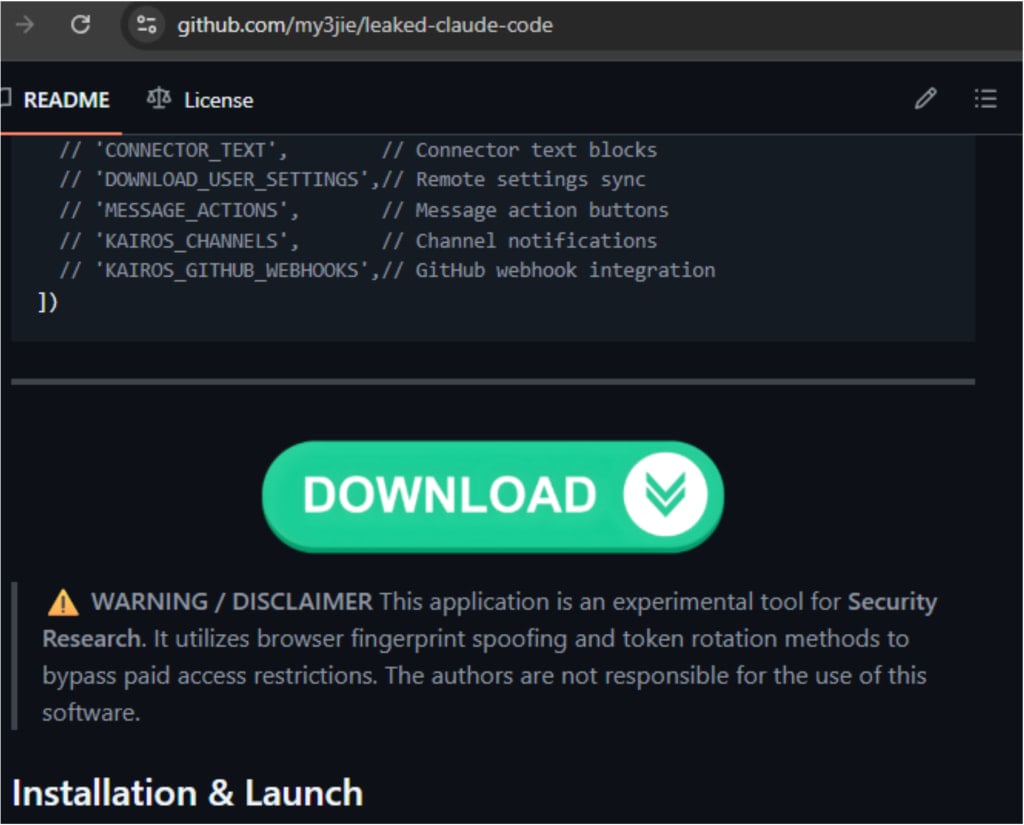
Source: Zscaler
Despite the platform's defenses, GitHub has often been used to distribute malicious payloads disguised in various ways.
In campaigns in late 2025, threat actors targeted inexperienced researchers or cybercriminals with repositories claiming to host proof-of-concept (PoC) exploits for recently disclosed vulnerabilities.
Historically, attackers were quick to capitalize on widely publicized events in the hope of opportunistic compromises.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
