
好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内,并且不需要特定的开头。首先,我得仔细阅读文章内容,抓住主要信息。 文章讲的是Progress ShareFile这个企业级安全文件传输解决方案中发现了两个漏洞。这两个漏洞可以被利用来进行未认证的文件窃取。研究人员发现了一个认证绕过和一个远程代码执行漏洞,分别给了CVE编号。这些漏洞存在于5.x分支的Storage Zones Controller组件中。 攻击者可以利用第一个漏洞进入管理界面,然后修改存储区配置,甚至上传恶意代码到服务器。文章提到大约有3万多个这样的控制器暴露在互联网上,虽然目前还没有看到实际攻击,但建议尽快升级到修复后的版本。 接下来,我需要把这些关键点浓缩到100字以内。重点包括:两个漏洞、未认证文件窃取、CVE编号、受影响版本、潜在风险和建议措施。 可能的结构是:先说明问题,然后漏洞细节,接着影响范围和建议。这样既简洁又全面。 </think> Progress ShareFile 存在两个漏洞(CVE-2026-2699 和 CVE-2026-2701),可被链式利用实现未认证文件窃取。研究人员通过认证绕过进入管理界面并利用远程代码执行上传恶意代码。约 3 万个暴露实例存在风险,建议升级至 5.12.4 版本以修复问题。 2026-4-2 13:45:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:30 收藏

Two vulnerabilities in Progress ShareFile, an enterprise-grade secure file transfer solution, can be chained to enable unauthenticated file exfiltration from affected environments.
Progress ShareFile is a document sharing and collaboration product typically used by large and mid-sized companies.
Such solutions are an attractive target for ransomware actors, as previously seen in Clop data-theft attacks exploiting bugs in Accellion FTA, SolarWinds Serv-U, Gladinet CentreStack, GoAnywhere MFT, MOVEit Transfer, and Cleo.
Researchers at offensive security company watchTowr discovered an authentication bypass (CVE-2026-2699) and a remote code execution (CVE-2026-2701) in the Storage Zones Controller (SZC) component present in branch 5.x of Progress ShareFile.
SZC gives customers more control over their data by allowing them to store it on their infrastructure (either on-prem or in a third-party cloud provider) or on the Progress systems.
Following watchTowr's responsible disclosure, the problems have been addressed in Progress ShareFile 5.12.4, released on March 10.
How the attack works
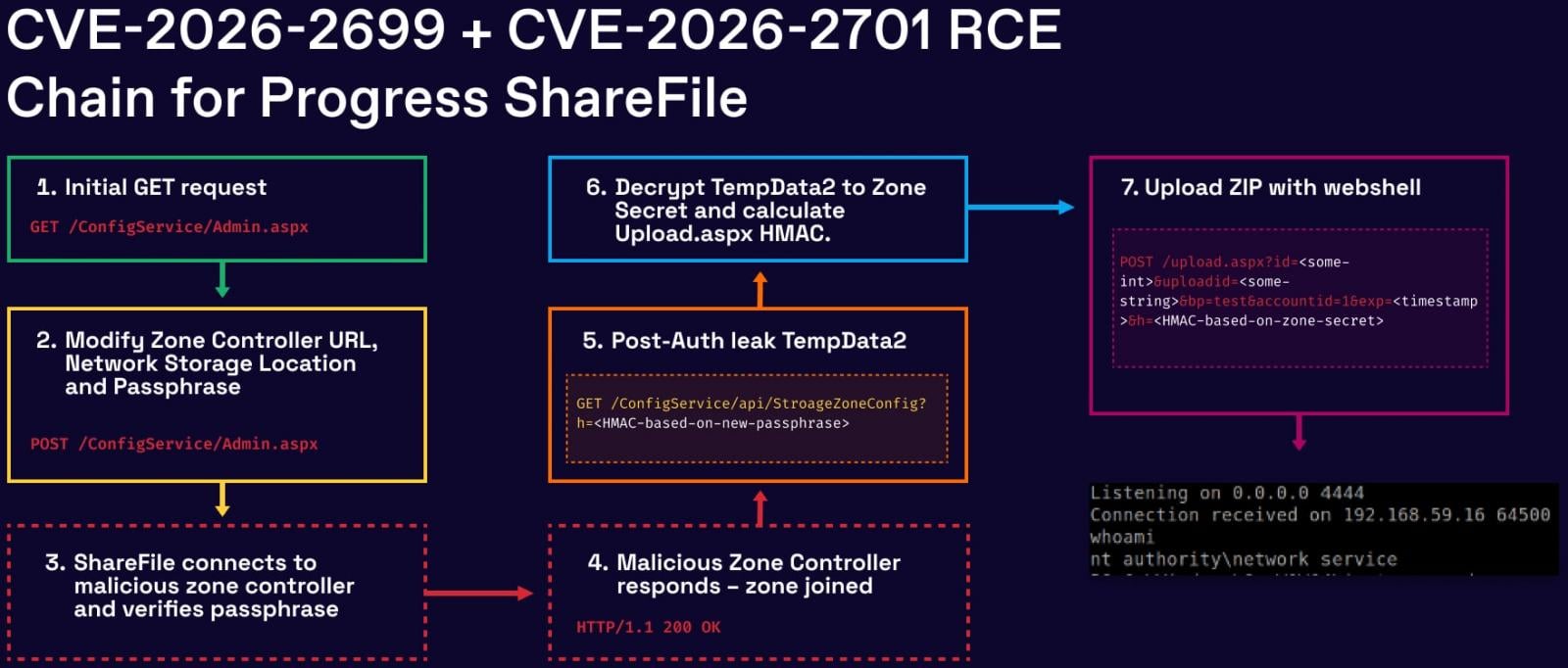
In a report today, watchTowr researchers explain that the attack begins by exploiting the authentication bypass issue, CVE-2026-2699, which gives access to the ShareFile admin interface due to improper handling of HTTP redirects.
Once inside, an attacker can modify Storage Zone configuration settings, including file storage paths and security-sensitive parameters such as the zone passphrase and related secrets.
By exploiting the second flaw, CVE-2026-2701, attackers can obtain remote code execution on the server by abusing file upload and extraction functionality to place malicious ASPX webshells in the application’s webroot.
The researchers note that, for the exploit to work, attackers must generate valid HMAC signatures and extract and decrypt internal secrets. However, these are achievable after exploiting CVE-2026-2699 due to the ability to set or control passphrase-related values.
Source: WatchTowr
Impact and exposure
By watchTowr's scans, there are about 30,000 Storage Zone Controller instances exposed on the public internet.
The ShadowServer Foundation currently observes 700 internet-exposed instances of Progress ShareFile, most of which are located in the United States and Europe.
watchTowr discovered the two flaws and reported them to Progress between February 6 and 13, and the full exploit chain was confirmed on February 18 for Progress ShareFile 5.12.4. The vendor released security updates in version 5.12.4, released on March 10.
Although no active exploitation in the wild has been observed as of writing, systems running vulnerable versions of ShareFile Storage Zone Controller should be patched immediately, as the public disclosure of the chain is likely to entice threat actors.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
