
好的,我现在需要帮用户总结一篇文章的内容,控制在一百个字以内。首先,我得仔细阅读文章,理解主要内容。 文章讲的是黑客利用TrueConf会议服务器的一个零日漏洞(CVE-2026-3502)进行攻击。这个漏洞源于软件更新机制中缺少完整性检查,导致恶意文件被伪装成合法更新分发给所有连接的客户端。 TrueConf是一个视频会议平台,支持自托管和云部署,常用于封闭的线下环境。疫情期间,超过10万个组织使用它,包括政府、军队等敏感机构。 CheckPoint的研究人员发现了一个名为TrueChaos的活动,从年初开始利用这个漏洞攻击东南亚政府机构。攻击者通过控制内部服务器替换更新包,导致恶意文件被执行。 漏洞影响了TrueConf的8.1.0到8.5.2版本,在报告后已在8.5.3版本中修复。CheckPoint认为攻击者可能与中国有关,并使用了Havoc框架。 总结时要涵盖:零日漏洞、攻击目标、漏洞影响、修复情况以及攻击者背景。控制在100字以内,直接描述内容。 </think> 黑客利用TrueConf会议服务器的零日漏洞(CVE-2026-3502),通过恶意更新分发文件,影响政府等敏感机构。该漏洞源于软件更新机制缺少完整性检查,已修复于8.5.3版本。 2026-4-1 21:45:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:16 收藏

Hackers have targeted TrueConf conference servers in attacks that exploit a zero-day vulnerability, allowing them to execute arbitrary files on all connected endpoints.
The flaw is tracked as CVE-2026-3502 and received a medium severity score. It stems from a missing integrity check in the software’s update mechanism, which can be used to replace the legitimate update with a malicious variant.
TrueConf is a video conferencing platform that can run as a self-hosted server. Although it also supports cloud deployments, it is generally designed for closed, offline environments.
According to the vendor, more than 100,000 organizations transitioned to TrueConf during the COVID-19 pandemic for remote online business activities. Among TrueConf users are military forces, government agencies, oil and gas corporations, and air traffic management companies.
CheckPoint researchers have been tracking a campaign they track as TrueChaos that, since the beginning of the year, has exploited CVE-2026-3502 in zero-day attacks targeting government entities in Southeast Asia.
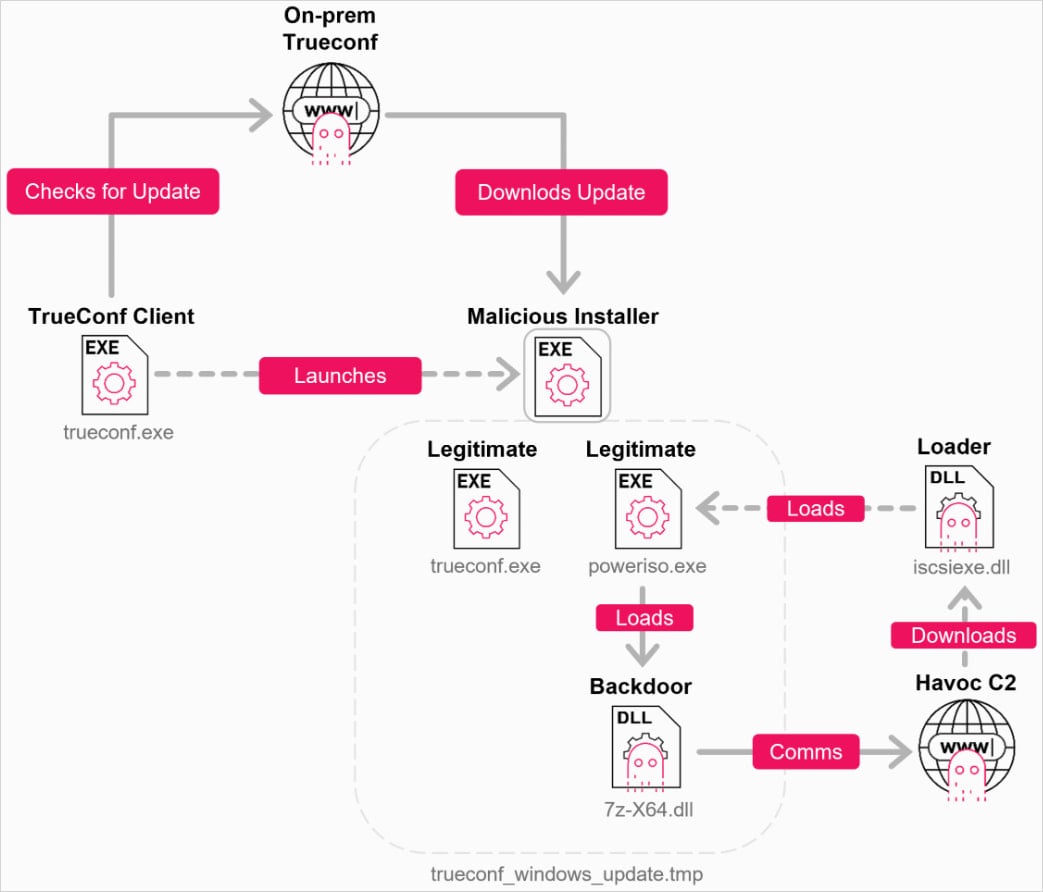
“An attacker who gains control of the on-premises TrueConf server can replace the expected update package with an arbitrary executable, presented as the current application version, and distribute it to all connected clients,” CheckPoint says.
“Because the client trusts the server-provided update without proper validation, the malicious file can be delivered and executed under the guise of a legitimate TrueConf update.”
The flaw affects TrueConf versions 8.1.0 through 8.5.2, and following CheckPoint’s report to the vendor, a fix was released in version 8.5.3 in March 2026.
“TrueChaos” operation
CheckPoint has moderate confidence in attributing the TrueChaos activity to a Chinese-nexus threat actor, based on tactics, techniques, and procedures (TTPs), the use of Alibaba Cloud and Tencent for hosting the command and control (C2) infrastructure, and victimology.
The attacks spread through a centrally managed government TrueConf server, impacting multiple agencies, pushing malicious files via fake updates to all connected TrueConf clients.
Source: Check Point
The infection chain includes DLL sideloading and the deployment of reconnaissance tools (tasklist, tracert), privilege escalation (UAC bypass via iscicpl.exe), and the establishment of persistence.
The researchers were unable to recover the final payload, but noted that network traffic pointed to Havoc C2 infrastructure, making it highly likely that the Havoc implant was used.
Source: Check Point
Havoc is an open-source C2 framework capable of executing commands, managing processes, manipulating Windows tokens, executing shellcode, and deploying additional payloads on compromised systems.
It has previously been used by the Chinese threat cluster ‘Amaranth Dragon’ in attacks with a similar targeting scope.
CheckPoint's report shares indicators of compromise (IoCs) as well as multiple infection signals. Strong signs of a breach include the presence of poweriso.exe or 7z-x64.dll, and suspicious artifacts like %AppData%\Roaming\Adobe\update.7z or iscsiexe.dll.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
