
好的,我现在需要帮用户总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读文章内容,抓住主要信息。 文章讲的是苹果公司为仍在使用iOS 18的iPhone设备提供了安全更新,以防御DarkSword漏洞套件。DarkSword是在2025年被发现的,影响了多个iOS版本。苹果在2026年4月1日发布了iOS 18.7.7更新,修复了相关漏洞,并扩大了支持设备范围,包括iPhone XR、XS、XS Max等多款设备。此外,DarkSword被多个威胁组织用于攻击,包括土耳其的PARS Defense和疑似俄罗斯的情报集团。 接下来,我需要将这些信息浓缩到100字以内。重点包括苹果发布更新、修复DarkSword漏洞、扩大支持范围以及漏洞的影响。 可能会遗漏一些细节,比如具体的CVE编号或攻击中使用的恶意软件家族名称。但为了简洁明了,这些可以省略。 最后,确保语言流畅自然,不使用任何格式标记。 </think> 苹果发布iOS 18.7.7更新修复DarkSword漏洞套件相关问题,并扩大支持设备范围。该漏洞套件于2025年被发现影响多个iOS版本,并被多个威胁组织用于攻击。 2026-4-1 22:0:21 Author: www.bleepingcomputer.com(查看原文) 阅读量:18 收藏

Apple has now made it possible for more iPhones still running iOS 18 to receive security updates that protect against the actively exploited DarkSword exploit kit.
"We enabled the availability of iOS 18.7.7 for more devices on April 1, 2026, so users with Automatic Updates turned on can automatically receive important security protections from web attacks called DarkSword," reads a note in today's iOS 18.7.7 security update changelog.
"The fixes associated with the DarkSword exploit first shipped in 2025."
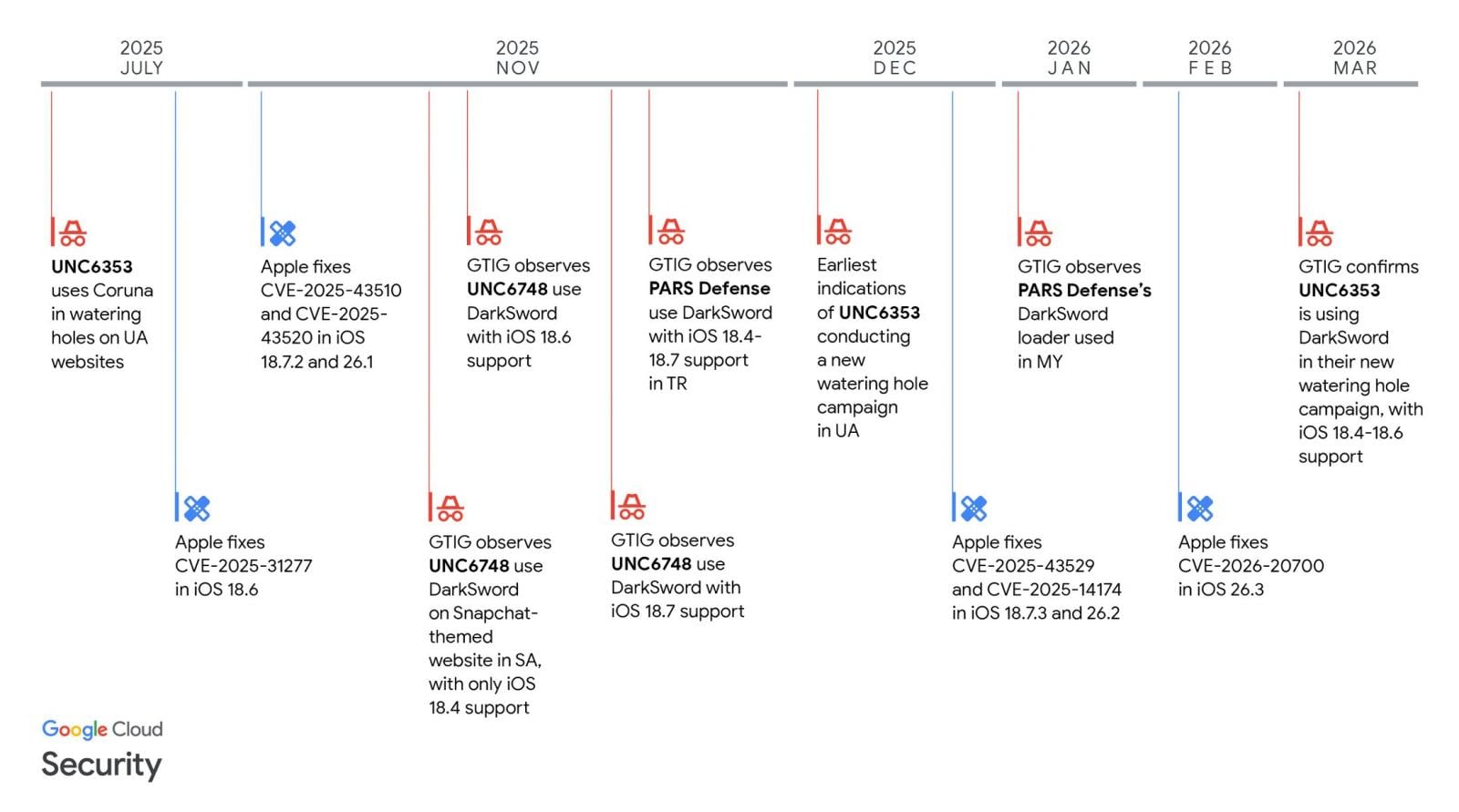
In March, researchers at Lookout, iVerify, and Google Threat Intelligence revealed a new "DarkSword" exploit kit that targeted iPhones running iOS 18.4 through 18.7.
The six vulnerabilities used by the DarkSword exploit kit are tracked as CVE-2025-31277, CVE-2025-43529, CVE-2026-20700, CVE-2025-14174, CVE-2025-43510, and CVE-2025-43520.
While iOS exploits have typically been used in highly targeted spyware campaigns, this iOS exploit kit was used much more widely, including by Turkish commercial surveillance vendor PARS Defense, a threat actor tracked as UNC6748, and a suspected Russian espionage group tracked as UNC6353.
In these attacks, GTIG observed three separate information-stealing malware families deployed on victims' devices: a highly aggressive JavaScript infostealer named GhostBlade, the GhostKnife backdoor, and the GhostSaber JavaScript malware, which can execute code and steal data.
Since July 2025, with the release of iOS 18.6, Apple has been steadily fixing the flaws as they are disclosed in security updates pushed out to compatible devices.
Source: GTIG
However, by late 2025, Apple stopped offering iOS 18 updates to newer devices capable of running the newer iOS 26.
For those who decided not to upgrade and stay on iOS 18, availability to the security updates became limited, with newer devices no longer receiving patches for DarkSword vulnerabilities released in 2026.
Since then, only a small number of devices remained able to receive iOS 18 updates, and the last 18.7.6 update was offered only to iPhone XS, iPhone XS Max, and iPhone XR devices.
To make matters worse, a researcher released the DarkSword exploit kit on GitHub last month, making it accessible to other threat actors who wanted to target older iPhones.
Today, Apple has released iOS 18.7.7 to make it available to more devices that want to stay on the older operating system while remaining protected from the latest threats.
Devices eligible to receive the new update now include iPhone XR, iPhone XS, iPhone XS Max, iPhone 11 (all models), iPhone SE (2nd generation), iPhone 12 (all models), iPhone 13 (all models), iPhone SE (3rd generation), iPhone 14 (all models), iPhone 15 (all models), iPhone 16 (all models), iPhone 16e, iPad mini (5th generation - A17 Pro), iPad (7th generation - A16), iPad Air (3rd - 5th generation), iPad Air 11-inch (M2 - M3), iPad Air 13-inch (M2 - M3), iPad Pro 11-inch (1st generation - M4), iPad Pro 12.9-inch (3rd - 6th generation), and iPad Pro 13-inch (M4).
iPhone users still running iOS 18 with Automatic Updates enabled will now receive the latest version and protections against the DarkSword exploit kit.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
