嗯,用户让我帮忙总结一下这篇文章,控制在一百个字以内,而且不需要特定的开头。好的,我先看看文章内容。 这篇文章主要讲的是AI在安全运营中心(SOC)中的应用,特别是自主AI SOC的分类能力。看起来作者指出,虽然这些AI系统能够分类和处理警报,但它们在深入调查方面存在局限性。文章提到了L1和L2的区别,L1是初步分类,而L2则是更深入的调查。 接下来,作者讨论了当前市场上的AI SOC平台大多只能做到L1级别的处理,无法进行更深入的分析和响应。这导致了他们所谓的“L1自动化天花板”。然后,文章介绍了D3 Morpheus这个解决方案,它能够进行更深入的攻击路径发现和全面的平台整合。 用户的需求是用中文总结这篇文章的内容,并且控制在一百字以内。所以我要抓住关键点:AI SOC的分类能力、L1天花板、深入调查的重要性以及D3 Morpheus的优势。 现在开始组织语言:首先说明AI SOC在分类警报方面的现状,然后指出它们无法进行深入调查的问题,接着提到D3 Morpheus如何突破这个限制,并整合了完整的平台功能。 确保不超过一百字,并且直接描述内容,不需要特定开头。检查一下是否涵盖了所有关键点:分类、调查、天花板、解决方案、整合功能。 最后调整用词,使句子简洁流畅。 </think> 文章探讨了当前AI SOC平台在安全运营中的局限性。尽管这些平台能够快速分类和处理警报(L1级别),但它们无法进行深入的攻击路径分析和响应(L2级别)。作者指出这是由于现有平台依赖通用大型语言模型,缺乏对网络攻击传播机制的理解。文章介绍了D3 Morpheus解决方案,通过专为网络安全设计的语言模型实现多维度攻击路径发现,并整合了SOAR和案例管理功能,突破了传统AI SOC的局限性。 2026-4-1 21:50:22 Author: securityboulevard.com(查看原文) 阅读量:8 收藏
Your “autonomous AI SOC” classifies alerts, but it stops short of investigating them. Here’s why that distinction will define the next generation of security operations.
The AI SOC Gold Rush
The AI SOC market is in a gold rush. Venture-funded startups have collectively raised hundreds of millions of dollars on a compelling promise: autonomous AI agents that replace Tier 1 analysts, eliminate alert fatigue, and revolutionize security operations.
The demos are polished. The speed metrics are impressive. And after years of drowning in alerts, security leaders are understandably eager to believe that AI will finally solve the SOC staffing crisis.
But there’s a problem that nobody in the AI SOC market wants to talk about: almost every platform on the market stops at L1 triage.
They classify alerts. They enrich them with threat intelligence. They tell you whether something is a true positive or a false positive. And then they hand the real work back to your team.
The L1 Ceiling Is Structural
L1 triage (alert classification, enrichment, and prioritization) is genuinely valuable work. Automating it addresses a real pain point. But it’s only the front door of the investigation.
Once an alert is classified as a true positive, the substantive investigation begins: tracing the attack path across multiple tools and telemetry sources. Correlating identity events with endpoint activity. Mapping lateral movement. Assessing blast radius. Determining containment and remediation actions. This is Level 2 work, and it’s precisely where today’s AI SOC platforms hit their ceiling.
We call this the L1 Automation Ceiling, and it’s a structural consequence of building on general-purpose large language models that lack a foundational understanding of how cyber attacks propagate across tools and time.
What’s Below the Marketing
Beneath the marketing language of “autonomous investigation” and “AI SOC analyst,” a consistent pattern emerges across the competitive landscape:
- Generic AI foundations. Most platforms wrap general-purpose LLMs in cybersecurity prompts. They’re fast classifiers, and they lack the depth of trained investigators.
- No attack path discovery. They classify alerts individually. They can’t trace lateral movement across your EDR, SIEM, identity systems, cloud logs, and network telemetry to build a unified threat narrative.
- Agent maintenance overhead. Several require your team to build, configure, and maintain AI agents, trading the “SOAR architect” problem for an “agent architect” problem.
- No SOAR or case management. They’re triage layers that stop short of full platforms. You still need a separate SOAR product for response orchestration and a separate case management system for incident tracking.
- Silent integration failures. When vendor APIs change, their integrations break, and nobody knows until alerts start queuing.
- Usage-based pricing. Many charge per alert, per investigation, or per AI credit. Scale your coverage and your costs scale with it.
What It Actually Takes to Go Beyond L1
Going beyond L1 triage requires a fundamentally different architecture: a purpose-built cybersecurity intelligence engine that understands how attacks move through enterprise environments.
That’s what we built with D3 Morpheus.
Morpheus is powered by a cybersecurity LLM that we developed over 24 months with a team of 60 specialists: red teamers, data scientists, AI engineers, and SOC analysts. On every incoming alert, it performs multi-dimensional attack path discovery: vertical deep inspection into the origin tool’s telemetry, and horizontal correlation across the full security stack. The result is an L2-level investigation report with step-by-step reasoning, delivered in under two minutes.
L1 triage solutions tell your analyst the alert is real. Morpheus tells your analyst what happened, how far it spread, what systems are affected, and what to do about it.
The Complete SOC Platform
But investigation depth is only part of the story. The AI SOC market’s other blind spot is platform completeness.
Morpheus consolidates three products into one: AI-driven autonomous triage with attack path discovery, a full traditional SOAR engine for deterministic playbook automation, and integrated case management for incident lifecycle tracking. Organizations can start with traditional SOAR playbooks for compliance-sensitive workflows and adopt AI-driven triage progressively, running both from the same platform, migrating at their own pace.
And critically: no usage fees. No per-alert charges. No investigation quotas. No overage surprises. Your SOC can scale to 100% alert coverage without watching a meter tick.
The Question Every Security Leader Should Ask
Before you sign your next AI SOC contract, ask one question: “What happens after the alert is classified as a true positive?”
If the answer is “a human analyst picks it up from there,” you’re buying an L1 bot. A sophisticated, fast, well-funded L1 bot, but an L1 bot nonetheless.
If you want a platform that investigates, orchestrates, and manages the full incident lifecycle from a single vendor with predictable pricing, the architecture exists. It’s called Morpheus.
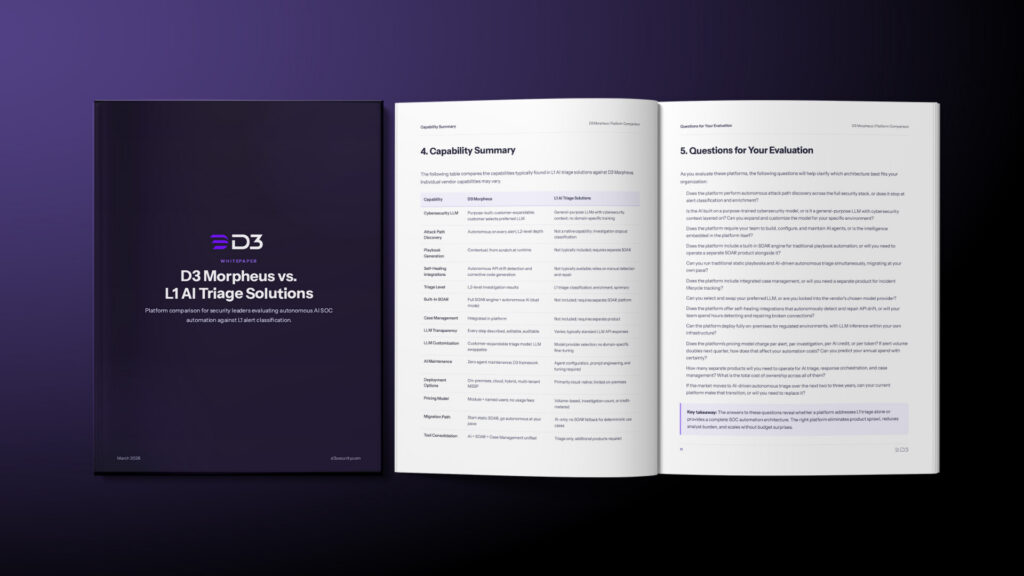
For a deeper read, check out our new whitepaper D3 Morpheus vs. L1 AI Triage Solutions.
Ready to see the difference? Request a personalized demo at d3security.com
The post The AI SOC’s L1 Automation Ceiling: Why Classification Is Not Investigation appeared first on D3 Security.
*** This is a Security Bloggers Network syndicated blog from D3 Security authored by Shriram Sharma. Read the original post at: https://d3security.com/blog/l1-ceiling-ai-soc-vendor/
如有侵权请联系:admin#unsafe.sh