嗯,用户让我帮忙总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读文章内容,抓住主要信息。 文章讲的是一个叫做EvilTokens的恶意工具包,它结合了设备代码钓鱼功能,用于劫持微软账户,并支持业务电邮欺诈攻击。这个工具包通过Telegram销售,并且还在持续开发中,计划扩展支持Gmail和Okta的钓鱼页面。 设备代码钓鱼利用OAuth 2.0的设备授权流程,诱骗受害者授权恶意设备。EvilTokens攻击通过发送带有钓鱼链接或二维码的邮件进行,模仿合法业务内容,针对特定职位的员工。 攻击流程中,受害者会被引导到微软的登录页面,输入验证码后,攻击者获得访问令牌和刷新令牌,从而控制账户。受影响国家包括美国、加拿大、法国等。 总结时需要涵盖EvilTokens的功能、传播方式、攻击方法以及影响范围。要简洁明了,不超过100字。 </think> EvilTokens是一种恶意工具包,结合设备代码钓鱼功能,用于劫持Microsoft账户并支持业务电邮欺诈攻击。该工具包通过Telegram销售,并计划扩展支持Gmail和Okta钓鱼页面。攻击者利用OAuth 2.0设备授权流程诱骗用户授权恶意设备,并获取访问令牌和刷新令牌以控制账户。受攻击国家包括美国、加拿大、法国等。 2026-4-1 19:45:15 Author: www.bleepingcomputer.com(查看原文) 阅读量:22 收藏

A new malicious kit called EvilTokens integrates device code phishing capabilities, allowing attackers to hijack Microsoft accounts and provide advanced features for business email compromise attacks.
The kit is sold to cybercriminals over Telegram and is under continuous development, its author stating that they plan to extend support for Gmail and Okta phishing pages.
Device code phishing attacks abuse the OAuth 2.0 device authorization flow, in which attackers gain access to a victim account by tricking the owner into authorizing a malicious device.
The technique is well-documented and has been used by various threat actors, including Russian groups tracked as Storm-237, UTA032, UTA0355, UNK_AcademicFlare, and TA2723 [1, 2, 3], and the ShinyHunters data extortion group.
EvilTokens attacks
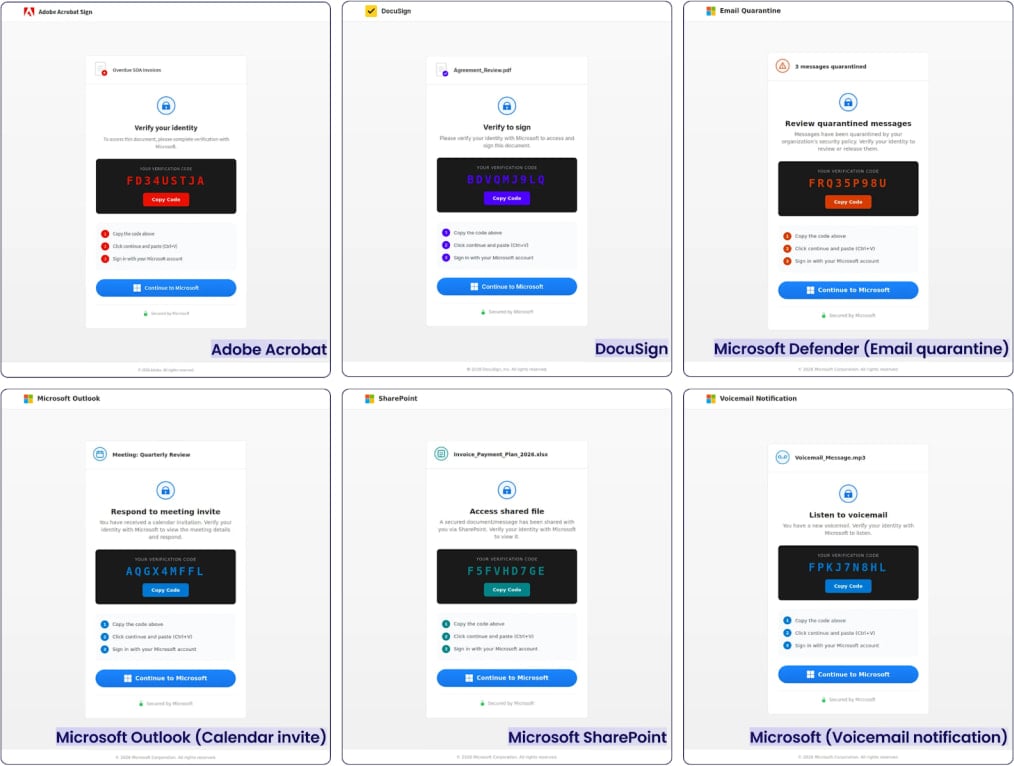
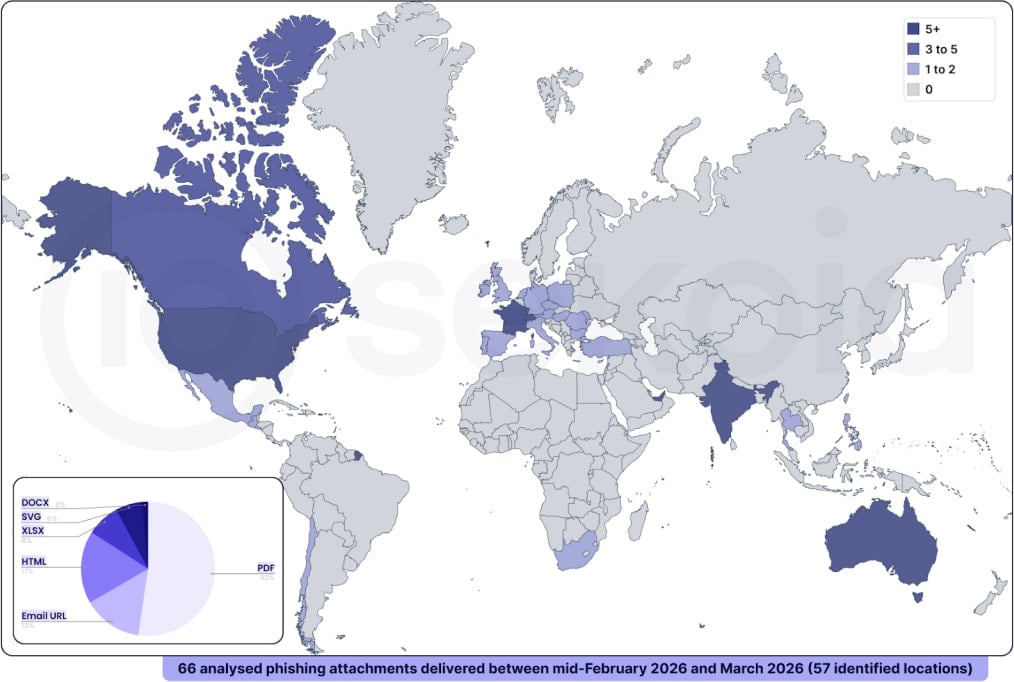
Researchers at threat detection and response company Sekoia observed EvilTokens attacks where the victims received emails with documents (PDF, HTML, DOCX, XLSX, or SVG) that contained either a QR code or a hyperlink to an EvilTokens phishing template.
These lures impersonate legitimate business content such as financial documents, meeting invitations, logistics or purchase orders, payroll notices, or shared documents via services like DocuSign or SharePoint, and are often tailored to employees in finance, HR, logistics, or sales roles.
Source: Sekoia
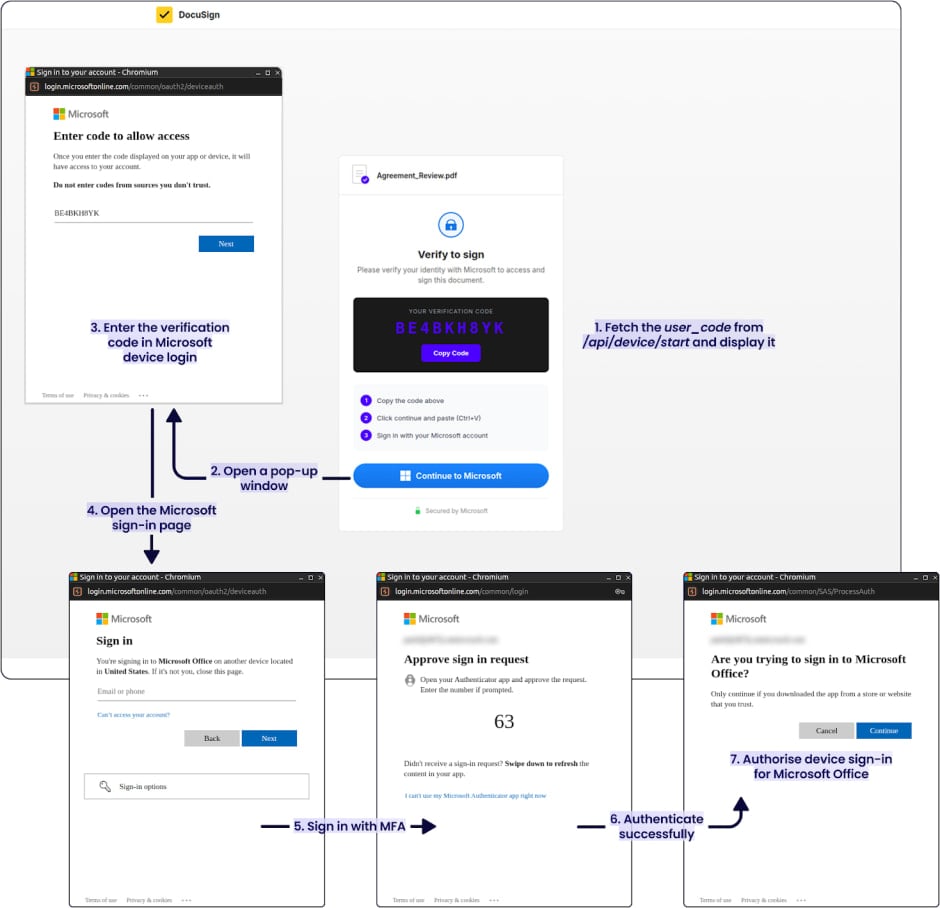
When the victim opens the link, they are presented with a phishing page that impersonates a trusted service (e.g., Adobe Acrobat or DocuSign), which displays a verification code and instructions to complete identity verification.
The page prompts the user to click a “Continue to Microsoft” button, redirecting them to the legitimate Microsoft device login page.
At this step, the attacker uses a legitimate client (any Microsoft application) to request a device code. Then, they trick the victim into authenticating to the legitimate Microsoft URL from the threat actor.
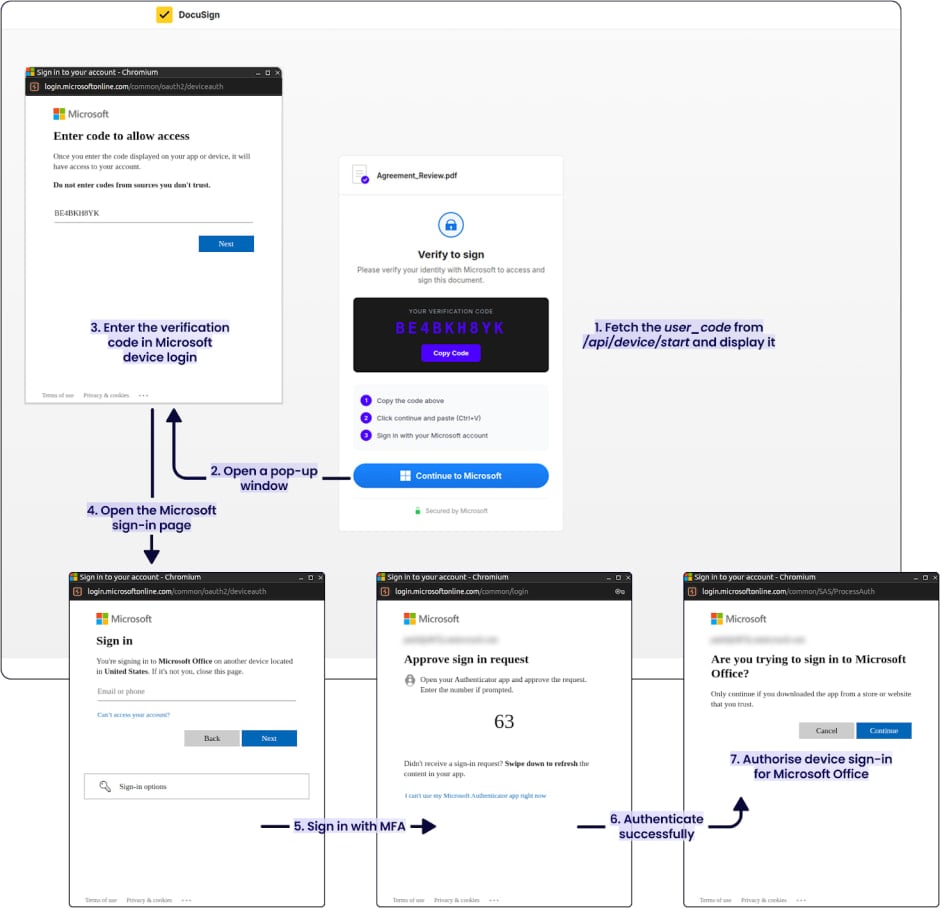
Source: Sekoia
This way, the attacker receives both a short-lived access token and a refresh token for persistent access.
These tokens give the attacker immediate access to the services associated with the victim account, including email, files, Teams data, and the capability to perform SSO impersonation across Microsoft services.
Sekoia researchers examined EvilTokens' infrastructure and uncovered campaigns with a global reach, the most affected countries being the United States, Canada, France, Australia, India, Switzerland, and the UAE.
Source: Sekoia
Apart from advanced phishing, Sekoia researchers say that the EvilTokens phishing-as-a-service (PhaaS) operation also provides "advanced features to conduct BEC [business email compromise] attacks" through automation.
The variety of the campaigns suggests that EvilTokens is already being used at scale by threat actors involved in phishing and business email compromise (BEC) activities.
Sekoia provides indicators of compromise (IoC), technical details, and YARA rules to help defenders block attacks leveraging the EvilTokens PhaaS kit.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
