
嗯,用户让我总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头。好的,我先快速浏览一下文章。 文章主要讲的是Citrix的NetScaler ADC和Gateway设备存在一个严重漏洞,CVE-2026-3055。黑客正在利用这个漏洞获取敏感数据。Citrix在3月23日发布了安全公告,提到了这个高危漏洞和其他问题。漏洞影响的是配置为SAML身份提供者的设备,需要管理员采取行动。 然后,多家网络安全公司指出这个漏洞风险很高,和之前的CitrixBleed类似。watchTowr公司观察到针对易受攻击实例的侦察活动,并警告野外利用即将开始。到了3月27日,研究人员确认威胁行为者已经开始利用这个漏洞提取认证管理会话ID,可能导致设备被完全接管。 watchTowr分析发现这个漏洞实际上涉及两个内存读取错误,分别影响SAML和WS-Federation认证端点。他们还提到Citrix的安全公告披露不完整,并提供了一个Python脚本来帮助检测易受攻击的主机。 目前Citrix还没有提到该漏洞被利用的情况,BleepingComputer联系了该公司但没有得到回应。另外,ShadowServer基金会发现有大量NetScaler和Gateway实例暴露在线上。 好的,现在我要把这些信息浓缩到100字以内。重点包括:漏洞名称、影响的产品、黑客利用情况、风险级别、watchTowr的发现、影响范围以及 Citrix 的回应情况。 可能的结构是:黑客利用Citrix设备的严重漏洞CVE-2026-3055获取敏感数据;该漏洞影响配置为SAML IDP的设备;网络安全公司警告风险高;watchTowr观察到攻击活动并确认已被利用;涉及两个内存读取错误;Citrix公告未提及被利用;大量设备暴露在线。 现在检查字数是否合适。 </think> 黑客正利用Citrix NetScaler ADC和Gateway设备中的严重漏洞CVE-2026-3055获取敏感数据。该漏洞影响配置为SAML身份提供者的设备。网络安全公司警告其风险极高,并与之前广泛利用的漏洞相似。研究人员发现该漏洞涉及两个内存读取错误,并已观察到针对未修补设备的攻击活动。 2026-3-30 18:30:18 Author: www.bleepingcomputer.com(查看原文) 阅读量:27 收藏

Hackers are exploiting a critical severity vulnerability, tracked as CVE-2026-3055, in Citrix NetScaler ADC and NetScaler Gateway appliances to obtain sensitive data.
Citrix initially disclosed CVE-2026-3055 in a security bulletin on March 23, alongside a high-severity race condition flaw tracked as CVE-2026-4368. The issue impacts versions of the two products before 14.1-60.58, versions older than 13.1-62.23, and those older than 13.1-37.262.
The vendor underlined that the flaw only affected appliances configured as a SAML identity provider (IDP) and noted that action is required only for administrators running on-premise appliances.
In response to the bulletin, multiple cybersecurity firms highlighted that CVE-2026-3055 has a significant risk, noting technical resemblance to the widely exploited ‘CitrixBleed’ and CitrixBleed2’ from 2023 and 2025, respectively.
watchTowr, a company that provides adversarial simulation and continuous testing services, said on Saturday that it observed reconnaissance activity targeting vulnerable instances and warned that in-the-wild exploitation was imminent.
The next day, the researchers confirmed that threat actors started leveraging the flaw since at least March 27.to extract authentication administration session IDs, potentially enabling a full takeover of NetScaler appliances.
“In-the-wild exploitation has begun, with evidence from our honeypot network showing exploitation from known threat actor source IPs as of March 27th,” reports watchTowr.
watchTowr’s analysis indicates that CVE-2026-3055 actually covers at least two distinct memory overread bugs, not one. The first affects the ‘/saml/login’ endpoint handling SAML authentication, while the second one affects the ‘/wsfed/passive’ endpoint used for WS-Federation passive authentication.
The researchers demonstrated that the security flaw can be leveraged to "sensitive information - including authenticated administrative session IDs."
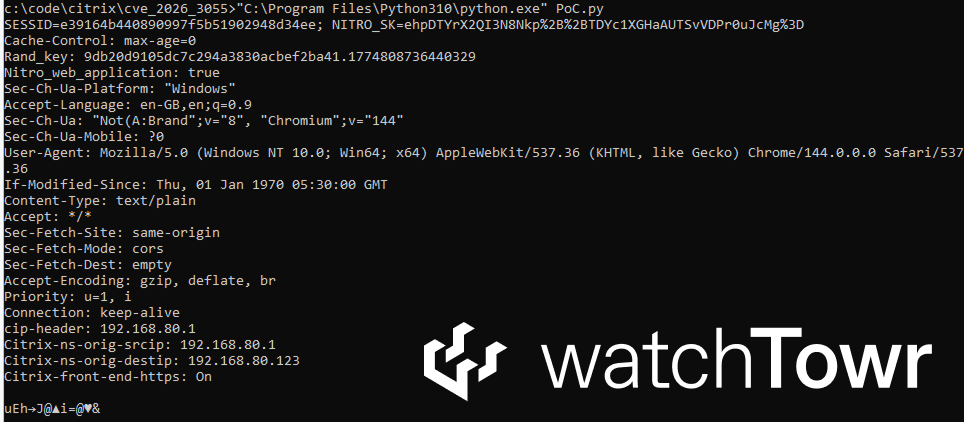
Source: watchTowr
The researchers call Citrix’s incomplete disclosure of the security issue in the security bulletin “disingenuous.” They also shared a Python script to help defenders identify vulnerable hosts in their environments.
As of publishing, Citrix's bulletin does not mention CVE-2026-3055 being exploited. BleepingComputer has contacted the company for a comment on the reported threat actor activity targeting unpatched appliances, but we have not received a response.
As of March 28, The ShadowServer Foundation sees 29,000 NetScaler and 2,250 Gateway instances exposed online, although it is unclear what percentage of those are vulnerable to CVE-2026-3055.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
