
好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是F5 Networks重新分类了一个漏洞,从DoS升级到RCE。这个漏洞影响BIG-IP APM系统,攻击者可以利用它植入webshell。F5已经发布了IOCs,并建议检查系统。CISA也警告联邦机构修复漏洞。 接下来,我需要把这些关键点浓缩成一句话。要包括F5 Networks、漏洞升级、影响的系统、攻击者的行为以及相关部门的警告。 可能的结构是:F5 Networks将BIG-IP APM的一个漏洞从DoS升级为RCE,攻击者可利用此漏洞植入webshell,F5和CISA已发布警告并建议修复。 这样应该在100字以内,并且涵盖了主要信息。 </think> F5 Networks将BIG-IP APM的DoS漏洞重新分类为RCE高危漏洞,攻击者可借此植入webshell。该漏洞影响配置访问策略的虚拟服务器,已被野利用。F5和CISA发布警告,敦促用户修复并检查系统。 2026-3-30 11:1:20 Author: www.bleepingcomputer.com(查看原文) 阅读量:17 收藏

Cybersecurity firm F5 Networks has reclassified a BIG-IP APM denial-of-service (DoS) vulnerability as a critical-severity remote code execution (RCE) flaw, warning that attackers are exploiting it to deploy webshells on unpatched devices.
BIG-IP APM (short for Access Policy Manager) is a centralized access management proxy solution that enables admins to secure and manage user access to their organizations' networks, cloud, applications, and application programming interfaces (APIs).
Tracked CVE-2025-53521, this security flaw can be exploited by attackers without privileges to perform remote code execution when targeting BIG-IP APM systems with access policies configured on a virtual server.
In addition to flagging the vulnerability as being exploited in the wild, F5 published indicators of compromise (IOCs) and advised defenders to check their BIG-IP systems' disks, logs, and terminal history for signs of malicious activity.
"This known vulnerability was previously categorized and remediated as a Denial-of-Service (DoS) vulnerability. Due to new information obtained in March 2026, the original vulnerability is being re-categorized to an RCE. The original CVE remediation has been validated to address the RCE in the fixed versions. We have learned that this vulnerability has been exploited in the vulnerable BIG-IP versions," F5 warned in an advisory update published this Sunday.
"F5 strongly recommends that you consult your corporate security policy for guidelines about incident handling procedures including but not limited to forensic best practices, that are specific to your organization. More specifically, review the policies to ensure that they comply with evidence collection and forensics procedures for a security incident before you attempt to recover the system," the company added.
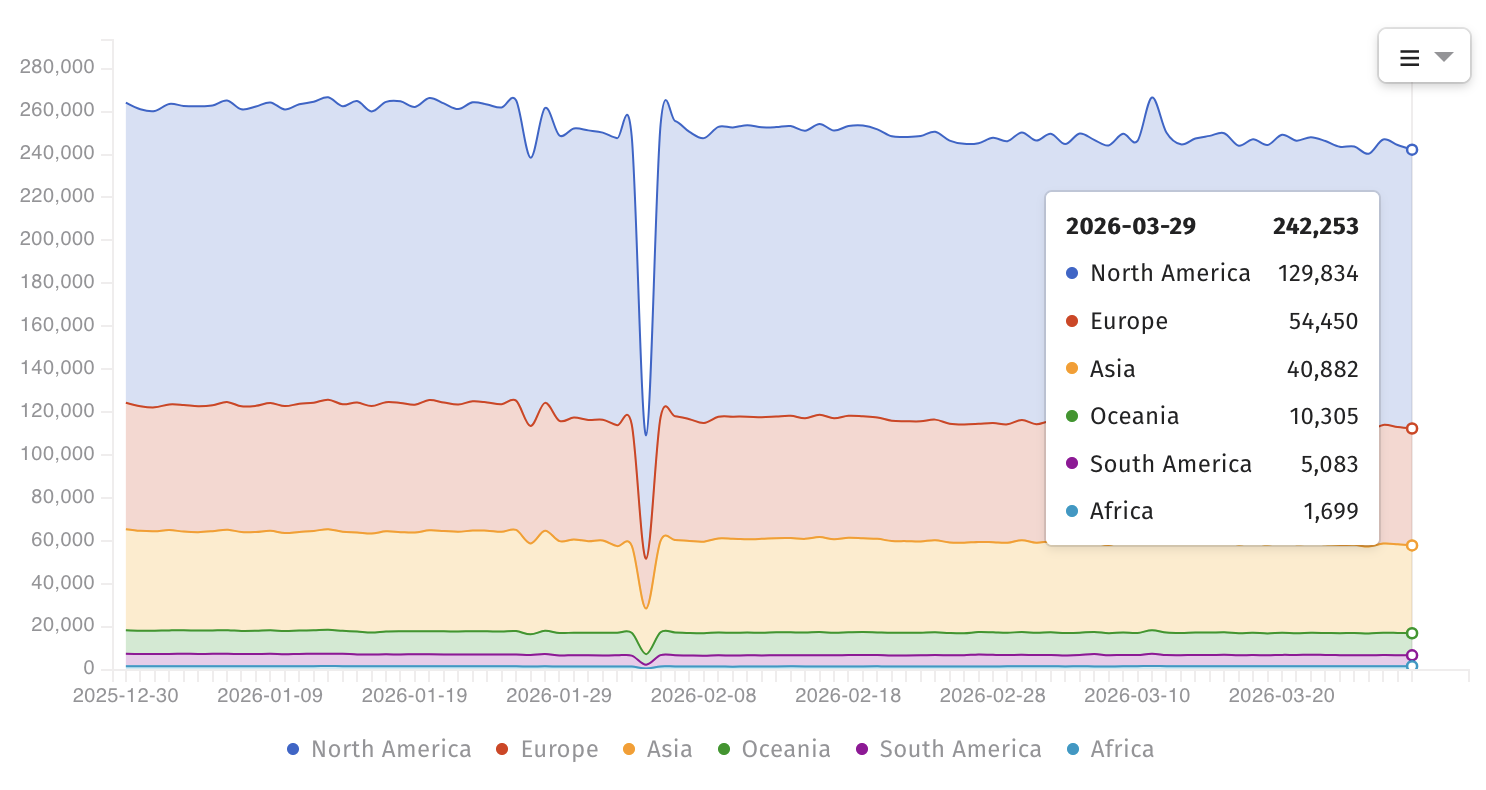
Internet threat-monitoring non-profit organization Shadowserver now tracks over 240,000 BIG-IP instances exposed online; however, there is no information on how many have a vulnerable configuration or have already been secured against CVE-2025-53521 attacks.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) also added the vulnerability to its list of actively exploited flaws on Friday and ordered federal agencies to secure their BIG-IP APM systems by midnight on Monday, March 30.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," it warned.
"Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable."
In recent years, BIG-IP vulnerabilities have been exploited by nation-state and cybercrime threat groups to breach corporate networks, map internal servers, deploy data-wiping malware, hijack devices, and steal sensitive documents from victims' networks.
F5 is a Fortune 500 technology giant that provides cybersecurity, application delivery networking (ADN), and various other services to more than 23,000 customers worldwide, including 48 of the Fortune 50 companies.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
