
好的,我现在需要帮用户总结一篇文章,控制在100字以内。首先,我得仔细阅读文章内容,抓住关键信息。 文章讲的是Handala黑客组织,他们与伊朗有关联,入侵了FBI局长Kash Patel的个人邮箱,并发布了照片和文件。FBI确认了这一事件,但表示被盗数据不包括政府信息。黑客声称这是对FBI先前行动的报复。 接下来,我需要提取主要元素:谁(Handala黑客)、做了什么(入侵邮箱)、结果(发布数据)、以及FBI的回应。同时要注意字数限制,确保简洁明了。 可能的结构是:Handala黑客入侵FBI局长邮箱,发布数据;FBI确认但称无政府数据;黑客报复先前行动。这样大概在100字左右。 最后检查是否有遗漏的重要信息,比如黑客组织的背景或影响,但为了简洁可能不需要详细说明。 </think> 伊朗关联的Handala黑客入侵FBI局长Kash Patel的个人邮箱并发布数据;FBI确认事件但称无政府信息泄露;黑客声称报复先前行动。 2026-3-29 21:15:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:24 收藏
The Handala hackers associated with Iran have breached the personal email account of FBI Director Kash Patel and published photos and documents.
The FBI has confirmed the compromise, saying that the stolen data was not recent and did not include any government data.
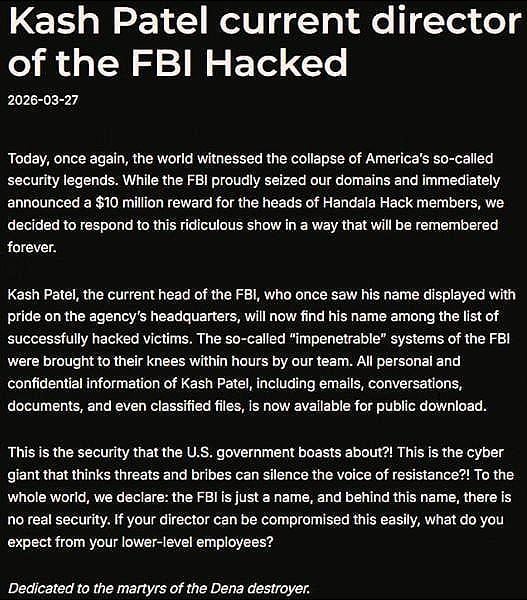
On Friday, the Handala threat actor announced on one of their websites that Patel has been added to the list of their victims, alleging that they compromised “the so-called ‘impenetrable’ systems of the FBI” in just a few hours.
The hackers said that their action was in response to the FBI seizing Handala domains and the U.S. government offering a reward of up to $10 million for information on the threat group’s members.
However, the hackers had breached the FBI Director’s personal Gmail inbox.
“All personal and confidential information of Kash Patel, including emails, conversations, documents, and even classified files, is now available for public download,” the Handala hackers said before publishing proof of the breach.
source: BleepingComputer
Shortly after the announcement, the threat actor published a set of watermarked personal photos and documents extracted from Patel’s inbox, along with email correspondence from before becoming FBI director.
In a statement for BleepingComputer, the FBI said that it was aware of hackers “targeting Director Patel’s personal email information.”
The agency further notes that it has taken every necessary precaution to reduce any negative impact that may result from this activity.
“The FBI is aware of malicious actors targeting Director Patel’s personal email information, and we have taken all necessary steps to mitigate potential risks associated with this activity. The information in question is historical in nature and involves no government information,” - the Federal Bureau of Investigation
The Handala hacktivist group has previously breached the Microsoft environment of medical technology giant Stryker and wiped nearly 80,000 devices.
Also known as Handala Hack, Hatef, and Hamsa, the actor emerged in December 2023 and is a hacktivist persona carrying out cyber activities for Iran's Ministry of Intelligence and Security (MOIS).
In the statement on the compromise of Director Patel’s personal email account, the FBI reiterated the $10 million reward from the Department of State's Rewards for Justice “for information leading to the identification of the Handala Hack Team out of Iran.”
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
