嗯,用户让我帮忙总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我需要仔细阅读文章内容,抓住主要观点。 文章主要讲的是“左移安全”(Shift Left Security),这是一种在软件开发的早期阶段就集成安全措施的方法。传统的做法是在开发后期才处理安全问题,这样成本高且效率低。左移安全通过在开发初期就进行安全测试和自动化工具的使用,可以更早地发现和修复漏洞,降低成本并提高效率。 接下来,我需要提取关键点:左移安全的定义、重要性、实施原则以及案例。然后把这些信息浓缩到100字以内,确保涵盖主要概念。 可能会提到Gartner的预测,云 computing的重要性,以及左移安全如何帮助组织提升安全性、降低成本和促进团队协作。同时,案例如Capital One和Netflix的成功经验也是重点。 最后,确保语言简洁明了,不使用复杂的术语,让用户容易理解。 </think> Gartner预测到2028年云计算将成为核心业务需求。左移安全(Shift Left Security)是一种在软件开发生命周期早期集成安全的方法,通过自动化工具和团队协作提前发现漏洞,降低成本并提高安全性。该方法强调开发者主动参与安全实践,并与DevOps结合以实现更快、更高效的软件交付。 2026-3-28 07:28:14 Author: securityboulevard.com(查看原文) 阅读量:5 收藏
Gartner predicts that by 2028, cloud computing will be a core business necessity, with global spending expected to surpass $1 trillion. As organizations continue to adopt cloud-native development to build and deliver innovative solutions, the demand for stronger application security (AppSec) practices is also on the rise. Traditionally, security has been addressed in the later stages of the software development lifecycle (SDLC). This makes fixing vulnerabilities, misconfigurations, and other issues more complex, time-consuming, and costly. This reactive approach drives costs, delays, missed threats, and team friction. This is where Shift Left Security comes into play, a transformative approach that integrates security from the very beginning of the SDLC. Embedding security early reduces time, cost, and risk by stopping vulnerabilities before production.
In this guide, we’ll explore Shift Left Security in detail, covering what it is, why it’s critical, and how organizations can successfully implement it.
Shift Left Security: A Quick Insight
Shift Left Security is a cloud security approach centered on integrating security into the software development process. The word comes from the SDLC, where development starts early (left), and security was traditionally added later (right). Shifting left embeds security early in the SDLC, not as an afterthought. This approach also places greater responsibility on developers to actively contribute to application security.
The concept of Shift Left Security has gained momentum alongside the rise of DevOps, which emphasizes faster and more efficient software delivery through automation. As release cycles became shorter, organizations recognized the importance of integrating security directly into the development process.
Importance of Shift Left Security
Shift Left Security enables organizations to detect and address threats early in the SDLC, lowering remediation costs, strengthening security awareness, and improving team collaboration. In cloud environments, Shift Left Security integrates security and compliance early in development, ensuring applications are secure by design and enabling a proactive approach.
- Improved Application Security
The shift left approach identifies potential vulnerabilities and cloud security risks early in the development process by analyzing application code at initial stages. Detecting and resolving issues before deployment in cloud environments significantly lowers the risk of cyberattacks and data breaches.
- Cost-Efficient Remediation
Addressing security issues after deployment can result in increased technical debt and higher remediation costs. By adopting a shift left approach, vulnerabilities are identified and resolved early, making remediation more efficient and cost-effective.
- Enhanced Developer Awareness
Engaging developers in security from the early stages helps them build essential security skills and gain a deeper understanding of common vulnerabilities and threats. This results in improved coding practices and more secure applications.
Shift left helps organizations establish an application security program that integrates seamlessly into modern development workflows.
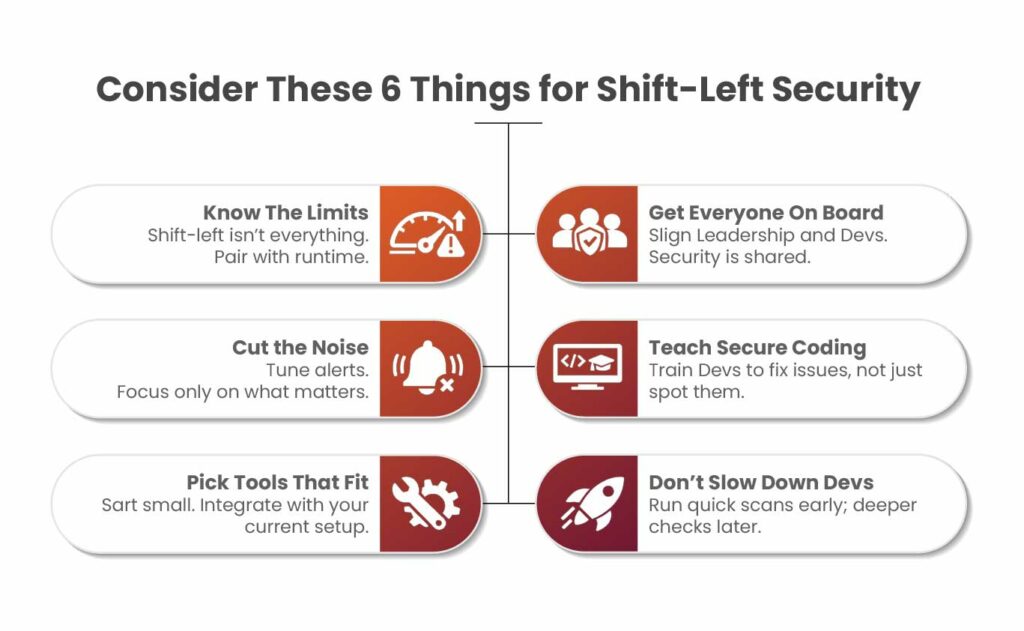
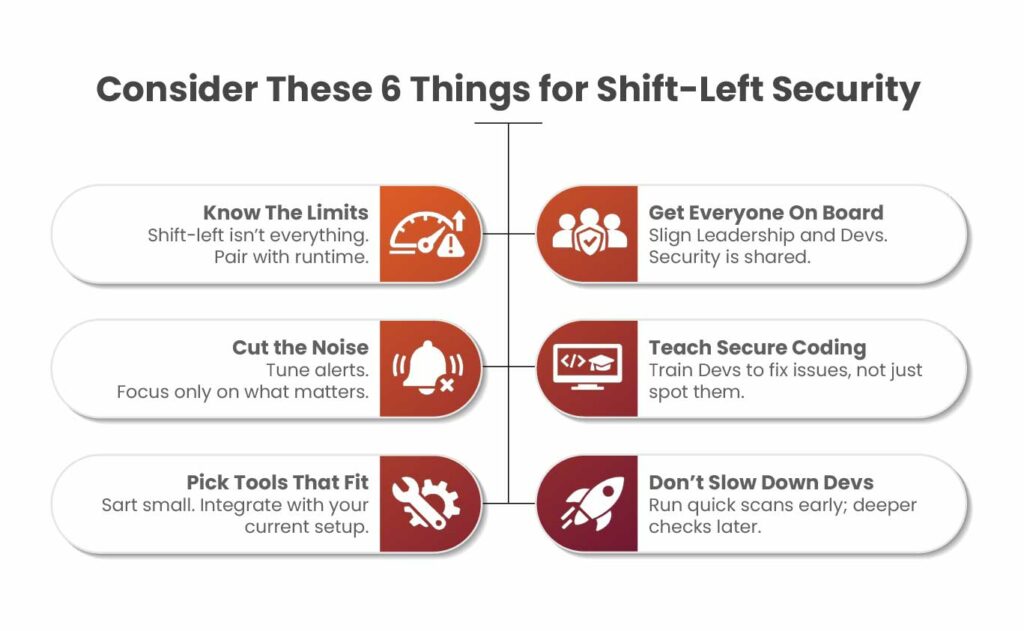
Principles of Shift Left Security
Integrating cloud-native security practices across every stage of application development and deployment, from design to runtime, ensures secure operations.
Integration:
Shift left integrates security checks into CI/CD pipelines, code reviews, and testing stages. To achieve multi-cloud security, organizations must consistently apply and embed security practices across the entire development lifecycle, ensuring protection for applications running on diverse cloud platforms.
Automation:
Using automated tools for continuous vulnerability assessment enables early detection of security issues during development. Solutions like Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) can be integrated into the SDLC to deliver real-time security insights.
Collaboration:
Close collaboration between development, QA, and security teams fosters a shared responsibility for application security. Eliminating silos encourages open communication, enables collaborative problem-solving, and accelerates the resolution of security issues.
Industry Case Studies and Insights
Many organizations have successfully adopted Shift Left Security, integrating security early in the development process, to strengthen their overall security posture.
Capital One
After experiencing a major data breach in 2019, Capital One strengthened its security posture by integrating automated security checks into its CI/CD pipeline. This proactive strategy enabled early detection and remediation of vulnerabilities during development, reducing risks and avoiding expensive rework. Their focus on embedding security into development has since become a benchmark in the financial sector.
Netflix
Netflix follows a “paved road” approach to software development by embedding security testing and monitoring directly into its workflows. By enabling engineers to take ownership of security from the start, the company leverages Software Composition Analysis (SCA) tools to identify vulnerable open-source dependencies early. This proactive strategy has significantly reduced security risks associated with third-party libraries, highlighting the value of early, automated security practices.
Strategies for Effective Implementation of Shift Left Security
Building a cloud security architecture requires consistent protection across all cloud environments, and adopting a shift left approach is a crucial step in that direction.
A successful shift left strategy starts with aligning security policies with existing development workflows. Clear and well-defined security requirements should guide secure coding practices, vulnerability management, and collaboration across teams.
Equipping developers with the right knowledge is equally important. Regular training on secure coding, common vulnerabilities, and effective use of security tools helps foster a security-first mindset and encourages continuous improvement.
Finally, integrating automated security testing such as SAST and DAST into CI/CD pipelines enables early vulnerability detection. This allows developers to identify and remediate issues quickly without disrupting workflows or delaying release cycles.
Conclusion
Shift Left Security is no longer a forward-thinking concept; it has become a critical requirement for organizations building and deploying applications in cloud-native environments. As development cycles accelerate and threat landscapes evolve, embedding security early in the SDLC is essential to staying resilient and competitive. Proactively identifying and addressing vulnerabilities early in development reduces risks, lowers remediation costs, and eliminates the inefficiencies of reactive security practices. More importantly, Shift Left Security fosters a culture of shared responsibility, where developers, security, and operations teams collaborate to build secure applications from the ground up.
FAQs
- What is the shift left approach?
Shift Left focuses on identifying and preventing defects early in the software development lifecycle. It emphasizes improving quality by moving security and testing activities to the earliest possible stages. In practice, Shift Left testing means conducting testing much earlier in the development process.
- What is the concept of shift left?
Shift-left involves introducing testing, quality checks, and feedback loops early in the SDLC. Rather than uncovering issues during final testing, when fixes are costly and time-consuming.
- What are the four types of shift-left testing?
These are commonly categorized as traditional, incremental, Agile/DevOps, and model-based shift-left testing approaches.
The post What is Shift Left Security? appeared first on Kratikal Blogs.
*** This is a Security Bloggers Network syndicated blog from Kratikal Blogs authored by Shikha Dhingra. Read the original post at: https://kratikal.com/blog/what-is-shift-left-security/
如有侵权请联系:admin#unsafe.sh