好的,我现在需要帮用户总结一篇文章,控制在100字以内。用户的要求是直接写文章描述,不需要开头的总结性语句。 首先,我得通读整篇文章,抓住主要内容。文章主要讲的是微软的Defender如何保护高价值资产,比如域控制器、Web服务器和身份基础设施。这些资产常被高级攻击目标。 接下来,文章提到Defender使用微软安全风险敞口管理来检测和阻止威胁,并通过实际案例展示了防御技术。比如域控制器的凭证盗窃、Webshell攻击等场景。 我需要把这些关键点浓缩到100字以内。要确保涵盖高价值资产、Defender的保护措施、具体防御技术和实际案例。 最后,组织语言,确保简洁明了。避免使用复杂的术语,让用户容易理解。 </think> 文章探讨了高价值资产(HVAs)如域控制器、Web服务器和身份基础设施在复杂攻击中的重要性,并介绍了微软 Defender 如何通过资产感知保护和微软安全风险敞口管理检测和阻止针对这些关键系统的威胁。文章还通过真实案例展示了防御技术的应用场景。 2026-3-27 19:53:53 Author: www.microsoft.com(查看原文) 阅读量:15 收藏
High-value assets including domain controllers, web servers, and identity infrastructure are frequent targets in sophisticated attacks. Microsoft Defender applies asset-aware protection using Microsoft Security Exposure Management to detect and block threats against these critical systems. This article explores real-world attack scenarios and defense techniques.
As cyberthreats continue to grow in scale, speed, and sophistication, organizations must pay close attention to the systems that form their backbone: High-Value Assets (HVAs). These assets include the servers, services, identities, and infrastructure essential for business operations and security. Examples include domain controllers that manage authentication and authorization across the network; web servers hosting business-critical applications such as Exchange or SharePoint; identity systems that enable secure access across on-premises and cloud environments; and other components such as certificate authorities and internet-facing services that provide access to corporate applications.
This reinforces a simple but important idea: not all assets carry the same risk, and protections should reflect their role and impact. To support this, we continue to expand differentiated protections for the assets that matter most. These efforts focus on helping organizations reduce risk, disrupt high-impact attack paths, and strengthen overall resilience. Microsoft Defender already provides enhanced protection for critical assets through capabilities such as automatic attack disruption. In this article, we explore how additional security layers further strengthen risk-based protection.
Using asset context to strengthen detection
In recent years, human-operated cyberattacks have evolved from sporadic, opportunistic intrusions into targeted campaigns designed to maximize impact. Analysis shows that in more than 78% of these attacks, threat actors successfully compromise a High-Value Asset, such as a domain controller, to gain deeper, elevated access within the organization.
Traditional endpoint detection methods rely on behavioral signals such as process execution, command-line activity, and file operations. While effective in many scenarios, these signals often lack context about the asset being targeted. Administrative tools, scripting frameworks, and system utilities can appear identical in both legitimate and malicious use.
This is where understanding a device’s role becomes essential. On high-value assets such as domain controllers or identity infrastructure, even small risks matter because the potential impact is significantly higher. Activities that may be routine on general-purpose servers or administrative workstations can indicate compromise when observed on Tier-0 systems.
Defender incorporates a critical asset framework to enrich detection with this context. This intelligence is powered by Microsoft Security Exposure Management, where critical assets, attack paths, and cross-workload relationships provide the context needed to distinguish normal administrative activity from high-risk behavior. This approach also enables automatic identification of critical assets in customer environments and applies deeper, context-aware detections based on each asset’s risk profile.
How high-value asset protection works
- Asset classification: Security Exposure Management asset intelligence builds a high‑confidence inventory and exposure graph of an organization’s assets across devices, identities, cloud resources, and external attack surfaces. By enriching asset data with contextual signals such as predefined classifications and criticality levels based on a system’s role and function, Security Exposure Management can automatically identify and tag High-Value Assets across on-premises, hybrid, and cloud environments, providing a consistent view of the systems that are most critical to the organization.
- Real Time Differentiated Intelligence from Cloud: HVA-aware anomaly detection extends cloud delivered protection by continuously learning what normal looks like for critical assets and highlighting activity that meaningfully deviates from those baselines. Instead of applying one size fits all thresholds, the system will evaluate behavior in the context of the asset role, sensitivity, and expected operational patterns.
- Endpoint Delivered Protections: Targeted protections that prioritize high-impact TTPs on High-Value Assets. By incorporating device role context and critical asset intelligence from Security Exposure Management, behaviors that may appear as weak signals in isolation can be elevated to high-confidence prevention when observed on Tier-0 systems, enabling more decisive protection where the potential blast radius is greatest.
Real-world high-value asset protection scenarios
Focused protection for domain controllers
Domain controllers are the backbone of on-premises environments, managing identity and access through Active Directory (AD). Because of their central role, threat actors frequently target domain controllers seeking elevated privileges. One common technique involves extracting credential data from NTDS.DIT, the Active Directory database that stores password hashes and account information for users across the domain, including highly privileged accounts such as domain administrators. On systems identified as domain controllers, Defender can apply stronger prevention powered by critical assets and attack paths, combining multiple behavioral signals that would otherwise appear benign in isolation.
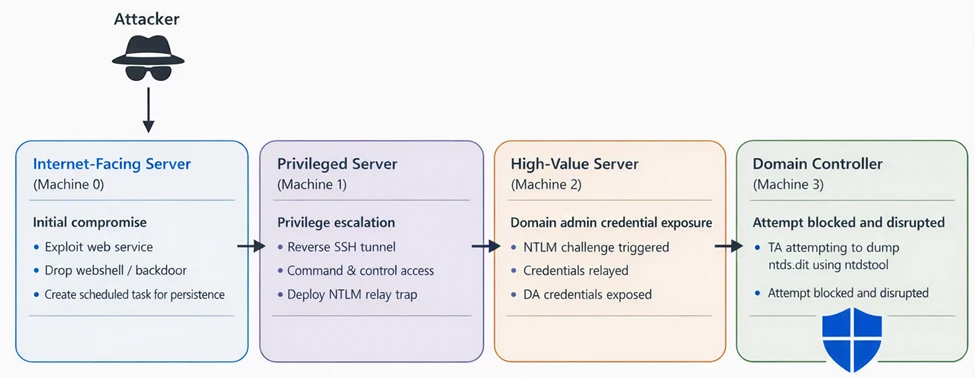
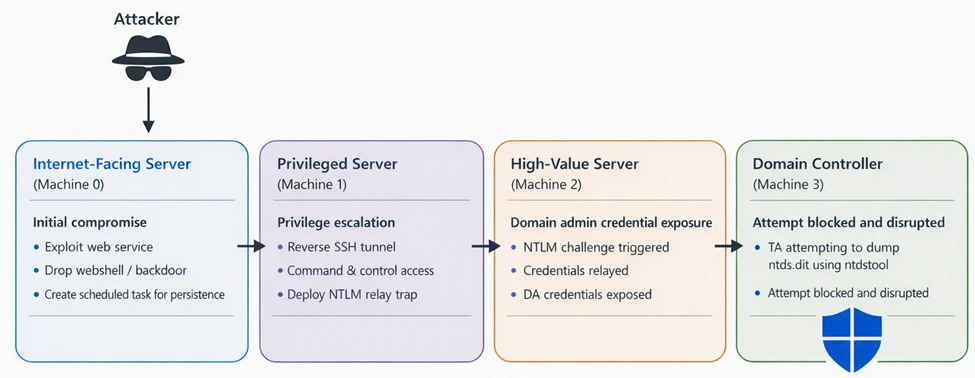
In one observed incident, the activity begins with the compromise of Machine 0, an internet-exposed server. The threat actor gained a foothold and established persistence to maintain access. This system served as the initial entry point into the environment, allowing the threat actor to begin reconnaissance and identify systems with broader access inside the network. The threat actor then laterally moved to Machine 1, a server with broader access within the network.
On this system, the actor established a reverse SSH tunnel to threat actor-controlled infrastructure while bypassing inbound firewall restrictions and setting up an NTLM relay trap. This positioned the machine to intercept or relay authentication attempts originating from other machines in the network. Subsequently, authentication activity originating from Machine 2, a high-value system with Domain Admin privileges, interacted with the relay setup. By leveraging the captured NTLM authentication exchange, the actor was able to authenticate with elevated privileges within the domain.
Using the leaked Domain Admin access, the threat actor then authenticated to Machine 3, a domain controller. With privileged access to the DC, the actor attempted to extract Active Directory credential data by using ntdsutil.exe to dump the NTDS.DIT database. Protections designed specifically for high‑value assets prevented the command‑line attempt, stopping execution before the database could be accessed. The activity also triggered automated disruption, resulting in the Domain Admin account being disabled, effectively stopping the threat actor from proceeding further with credential extraction and limiting the potential impact to the domain.
In this attack, the adversary remotely created a scheduled task on a domain controller that executed ntdsutil.exe to generate a backup containing the Active Directory database. The task was configured to run as SYSTEM and then deleted shortly afterward to reduce forensic visibility.
Individually, both behaviors, remote scheduled task creation and execution of ntdsutil.exe can occur in administrative scenarios across enterprise environments. However, by analyzing historical activity within the environment, these activities appear as outliers when combined, making it a high-confidence indicator of credential theft preparation on a domain controller. By incorporating asset role, attack path context, historical correlations, and the blast radius of the activity, Defender can deterministically block credential theft preparation on domain controllers.
Early detection of webshells and IIS compromise
When Defender identifies a high-value asset running the IIS role, it applies targeted inspection to locations that are commonly exposed and frequently abused during server compromise. This includes focused scanning of web-accessible directories and application paths for suspicious or unauthorized script files. In several investigations involving SharePoint and Exchange servers, this approach surfaced previously unknown and highly targeted webshells with poor detection coverage.
In many cases, the malicious logic was inserted directly into legitimate web application files, allowing threat actors to blend into normal application behavior and maintain stealthy access to the server.
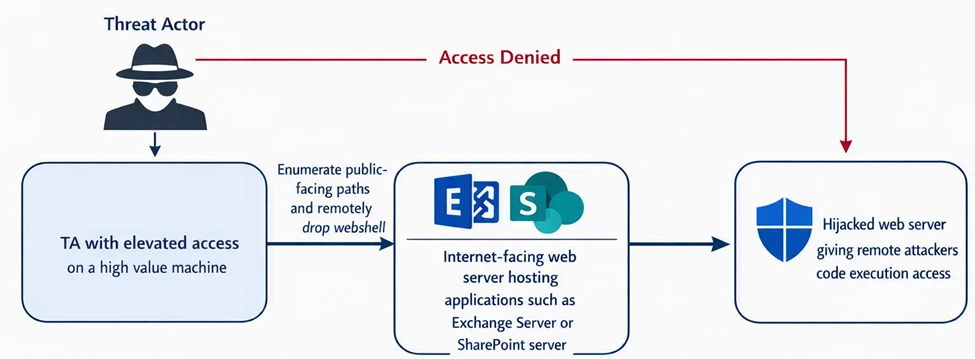
Protection tech like AMSI for Exchange and SharePoint helps block malicious code and incoming exploitation attempts. However, if an threat actor already has elevated access inside the organization, they can target these internet-facing High-Value Assets directly. In one scenario, the threat actor had already gained access inside the organization with elevated privileges. From another compromised system, the actor remotely drops a highly customized, previously unseen webshell into EWS directory of Exchange Server.
The webshell has file upload, download and in-memory code execution capabilities. Because the device was identified as an Exchange server hosting internet-facing content, the risk profile was significantly higher. Leveraging this role context, Defender immediately remediated the file upon creation, preventing the threat actor from establishing control over the Exchange workload.
Expanded protection from remote credential dumping
High‑Value Assets (HVAs) hold the most sensitive credentials in an organization, making them a primary target for adversaries once initial access is achieved. Threat actors often attempt to access credential stores remotely using administrative protocols, directory replication methods, or interactions with identity synchronization systems such as Microsoft Entra Connect.
These activities can involve the movement or staging of sensitive artifacts, including Active Directory database files, registry hives, or identity synchronization data. Suspicious patterns such as creation of credential-related files in non-standard locations or unexpected transfers between systems may indicate attempts to compromise credentials. Incorporating device role context enables stronger protections on the systems where credential exposure poses the highest risk, such as domain controllers and identity infrastructure servers. By considering the process chains and access patterns involved, Defender can more effectively prevent exfiltration of sensitive credential data.
Protecting your HVAs
While Microsoft’s Security Exposure Management continues to improve automatic identification and classification of high‑value assets (HVAs) in customer environments, customers can take several concrete steps today to strengthen protection outcomes.
1. Ensure coverage across all critical assets
Review environments to confirm that all truly high‑value assets are identified, including assets that may not be obvious by type alone (for example, servers running privileged services or machines holding sensitive credentials). Gaps in classification can lead to gaps in protection prioritization.
2. Prioritize security posture improvements and alert response for HVAs
Customers should focus first on implementing security posture recommendations that apply to high-value assets, as these systems represent the greatest potential impact if compromised. Addressing gaps on HVAs delivers disproportionately higher risk reduction compared to non-critical assets.
In addition, organizations should prioritize monitoring and rapid response for alerts originating from HVAs. Accelerating investigation and remediation for these alerts helps mitigate threats in a timely manner and significantly limits potential blast radius.
3. Triage vulnerabilities with HVA context
When reviewing vulnerabilities, prioritize remediation on HVAs before lower‑impact assets. A moderate vulnerability on a high‑value asset might present greater risk than a high‑severity issue on a non‑critical endpoint.
Learn more
Explore these resources to stay updated on the latest updates
- To learn more about our security products, see Microsoft Defender products and services. Microsoft Defender products and services – Microsoft Defender | Microsoft Learn
- To learn more about how attack disruption safeguards your domain controllers, check out this video video.
- To learn more about Security Exposure Management, see Microsoft Security Exposure Management. Microsoft Security Exposure Management | Microsoft Security
- To learn more about AMSI, see AMSI for SharePoint server (Configure AMSI integration with SharePoint Server – SharePoint Server | Microsoft Learn) or AMSI for Exchange server (AMSI integration with Exchange Server | Microsoft Learn)
To get notified about new publications and to join discussions on social media, follow us on LinkedIn, X (formerly Twitter), and Bluesky.
To hear stories and insights from the Microsoft Threat Intelligence community about the ever-evolving threat landscape, listen to the Microsoft Threat Intelligence podcast.
如有侵权请联系:admin#unsafe.sh