Security Analyst, curator of the GitHub Advisory Database, and one of the members of the Security Lab responsible for issuing CVE IDs and publishing CVE records.
嗯,用户让我用中文总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头,直接写描述就行。首先,我需要通读整篇文章,抓住主要信息。 文章主要讲的是GitHub在2025年发布的安全公告数量减少了,但并不意味着开源软件更安全。实际上,他们审查了更少的旧漏洞,而新漏洞的数量反而增加了19%。另外,漏洞类型的变化和CWE标签的改进也被提到。还有关于CVE的发布情况和组织使用GitHub CNA服务的增长。 接下来,我需要把这些信息浓缩到100字以内。要突出重点:公告数量减少的原因、新漏洞增加、CWE变化、CVE增长以及组织参与度提升。同时保持语言简洁明了。 可能的结构是:先点明公告数量减少,解释原因,然后提到新漏洞增加和CWE的变化,接着是CVE的增长和组织使用情况,最后总结整体安全提升。 现在把这些整合成一句话或者几句话,确保不超过100字。 </think> GitHub在2025年发布的安全公告数量减少至4,101个,但并非开源代码更安全。新漏洞数量增加19%,旧漏洞审查减少。CWE标签更具体,CVSS和EPSS评分帮助优先处理。npm恶意软件公告激增69%,CVE发布量增长35%。更多组织使用GitHub CNA服务。 2026-3-26 16:0:16 Author: github.blog(查看原文) 阅读量:18 收藏
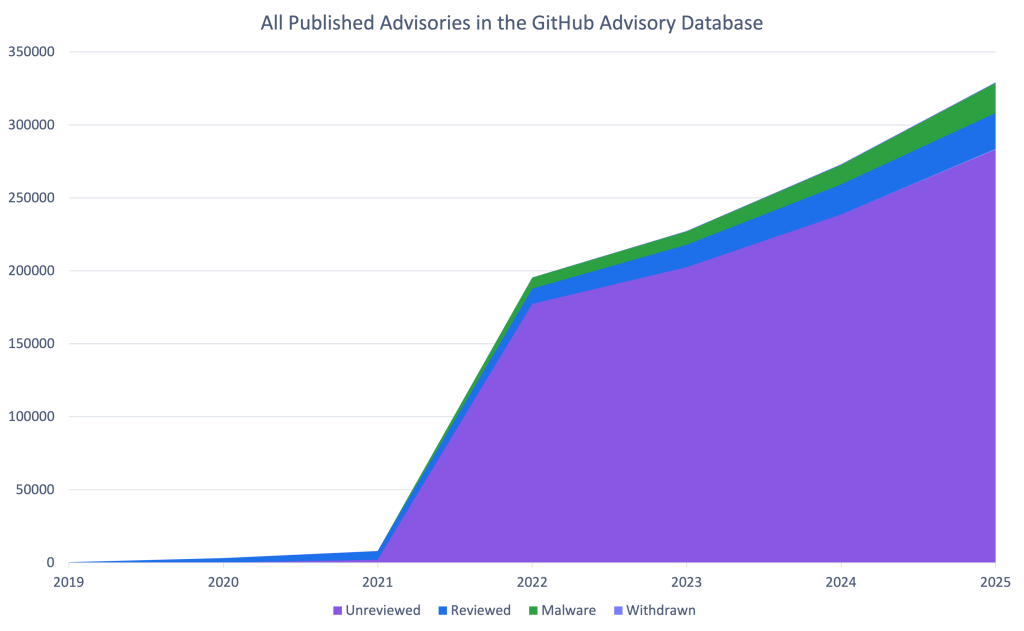
GitHub published 4,101 reviewed advisories in 2025. This is the fewest number of reviewed advisories since 2021. Does this mean open source is shipping more secure code? Let’s dig into the data to find out.
Fewer advisories reviewed doesn’t mean fewer vulnerabilities were reported. The drop is because GitHub reviewed far fewer older vulnerabilities. When you look only at newly reported vulnerabilities from our sources, GitHub actually reviewed 19% more advisories year over year.
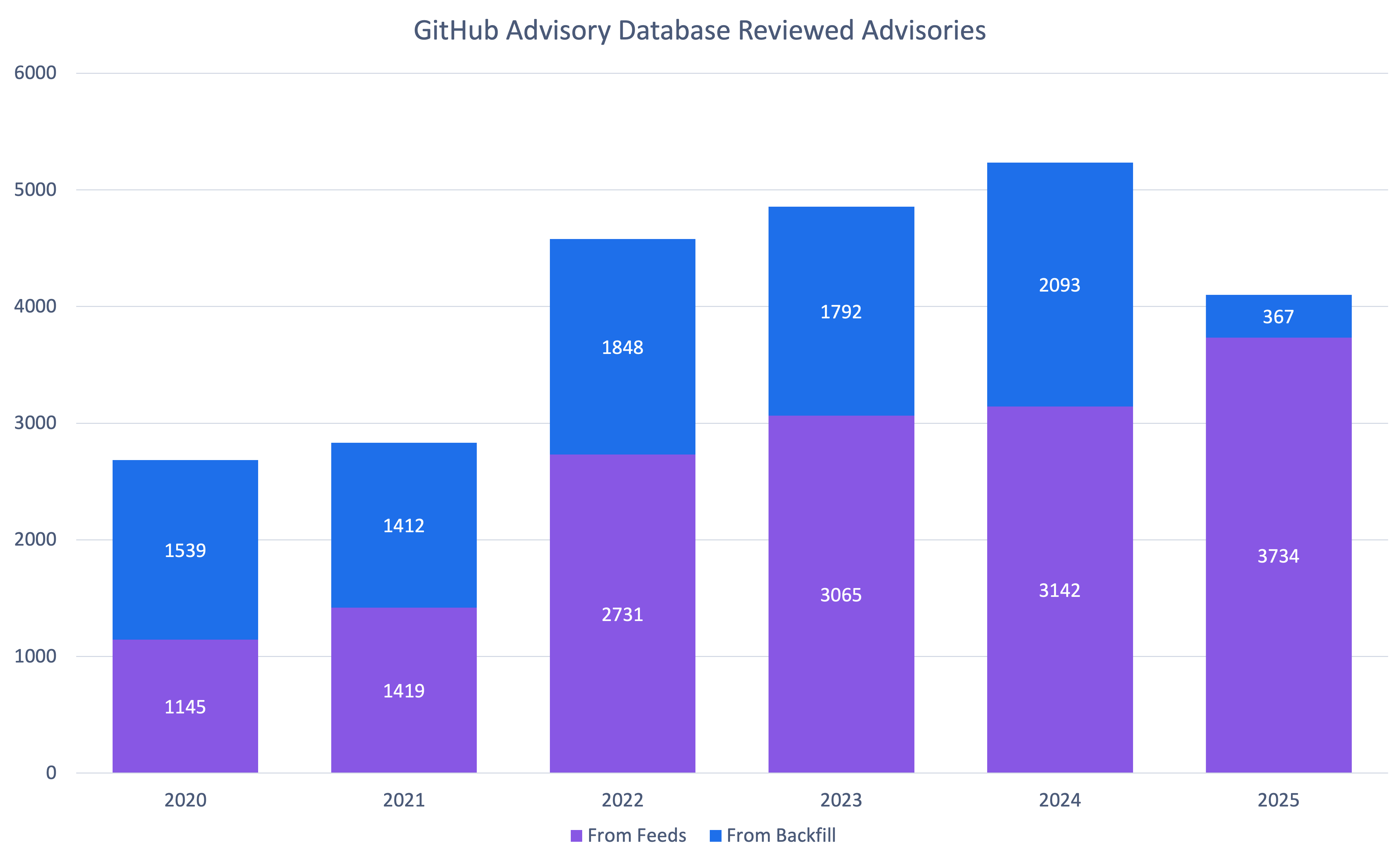
So why the change? Quite frankly, we are running out of unreviewed vulnerabilities that are older than the Advisory Database. At the same time, the number of newly reported vulnerabilities hasn’t dropped.
It’s also worth clarifying that “unreviewed” in the database can be misleading: most advisories marked unreviewed have already been looked at by a curator and found not to affect any package in a supported ecosystem, so they may never be fully reviewed.
This means that you should be receiving fewer brand-new Dependabot alerts about old vulnerabilities.
Note: If you find an unreviewed advisory that affects a supported package, please let us know so we can get it reviewed!
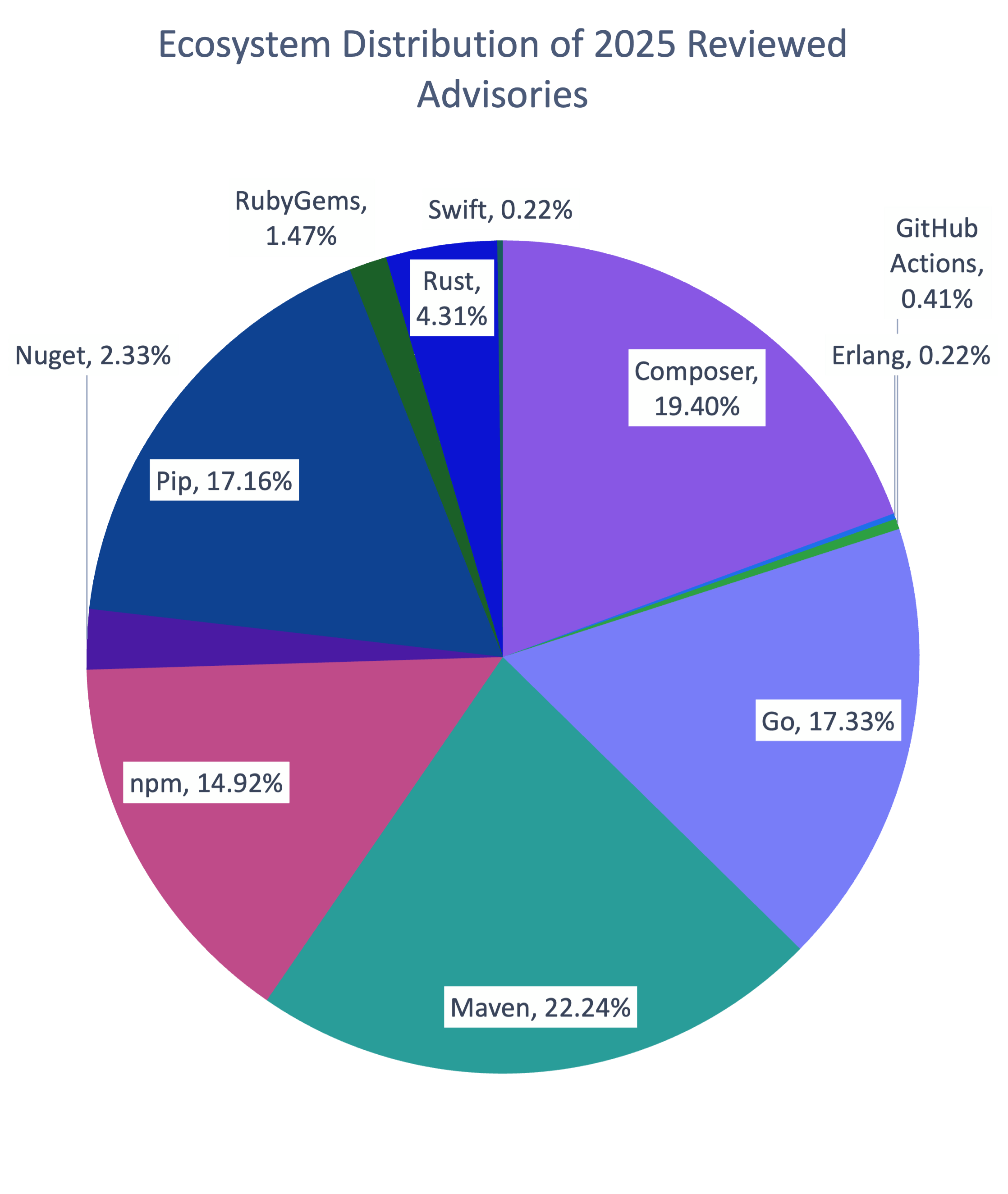
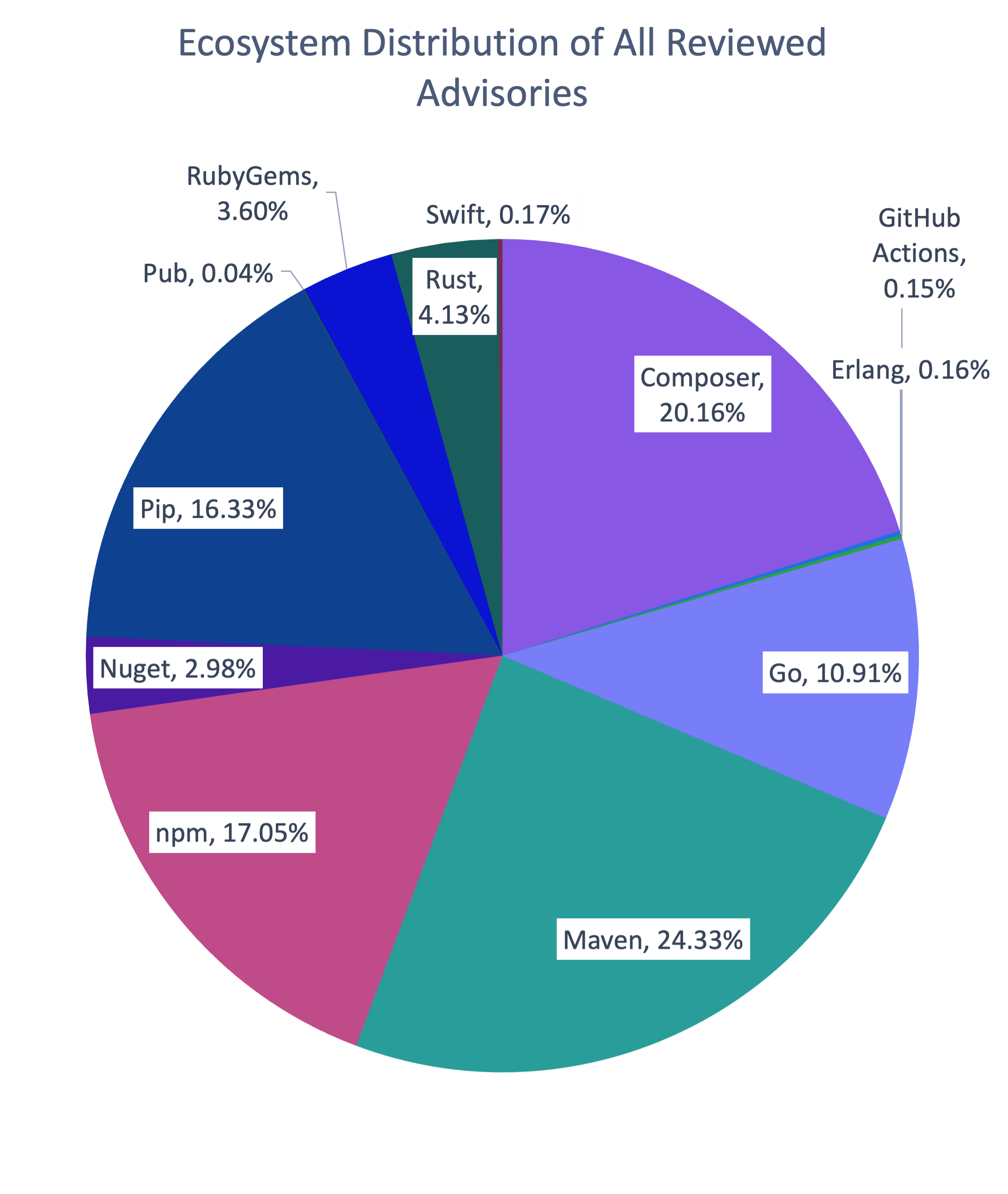
How vulnerabilities were distributed across ecosystems in 2025
The distribution of ecosystems in advisories reviewed in 2025 is similar to the overall distribution in the database, with the exception of Go. Go is overrepresented in 2025 advisories by 6%. This is largely due to dedicated campaigns to re-examine potentially missing advisories found through an internal review for packages where we had inconsistent coverage.
How the types of vulnerabilities changed in 2025
| Rank | Common Weakness Enumeration (CWE) | Number of 2025 Advisories* | Change in Rank from 2024 | Change in Rank from the Overall Database |
|---|---|---|---|---|
| 1 | CWE-79 | 672 | +0 | +0 |
| 2 | CWE-22 | 214 | +2 | +1 |
| 3 | CWE-863 | 169 | +9 | +8 |
| 4 | CWE-20 | 154 | +1 | +1 |
| 5 | CWE-200 | 145 | -2 | -1 |
| 6 | CWE-400 | 144 | +4 | +0 |
| 7 | CWE-770 | 136 | +7 | +10 |
| 8 | CWE-502 | 134 | +5 | +1 |
| 9 | CWE-94 | 119 | -3 | -1 |
| 10 | CWE-918 | 103 | +5 | +8 |
* An advisory may have more than CWE. For example, an advisory might have both CWE-400 and CWE-770. It would then count for both.
As usual, cross-site scripting (CWE-79) is by far the most common vulnerability type. However, there are significant changes in the following areas. Resource exhaustion (CWE-400 and CWE-770), unsafe deserialization (CWE-502), and server-side request forgery (CWE-918) were unusually common in 2025. CWE-863 (“Incorrect Authorization”) saw a significant jump, but that is largely due to reclassification away from CWE-284 (“Improper Access Control”) and CWE-285 (“Improper Authorization”), which are higher level CWEs that the CWE program discourages using.
One of the biggest quality improvements in 2025 was more specific, more consistent CWE tagging. Advisories without any CWE dropped 85% (from 452 in 2024 to 65 in 2025). CWE-20 (“Improper Input Validation”) is still common, but in prior years it was often the only CWE listed on an advisory.
In 2025, advisories far more often list CWE-20 plus one or more additional CWEs that describe the concrete failure mode. This added specificity makes the data more actionable for triage, prioritization, and remediation.
To find out how to filter Dependabot alerts by CWE, see our documentation on auto-triage rules.
How to prioritize your response
We provide two scoring systems for prioritization:
- Common Vulnerability Severity Score (CVSS): Scores how severe the impact of the vulnerability will be
- Exploit Prediction Scoring System (EPSS): Provides a measure of how likely the vulnerability will be attacked in the next 30 days and
Together, they can give you a head start on your risk assessment process.
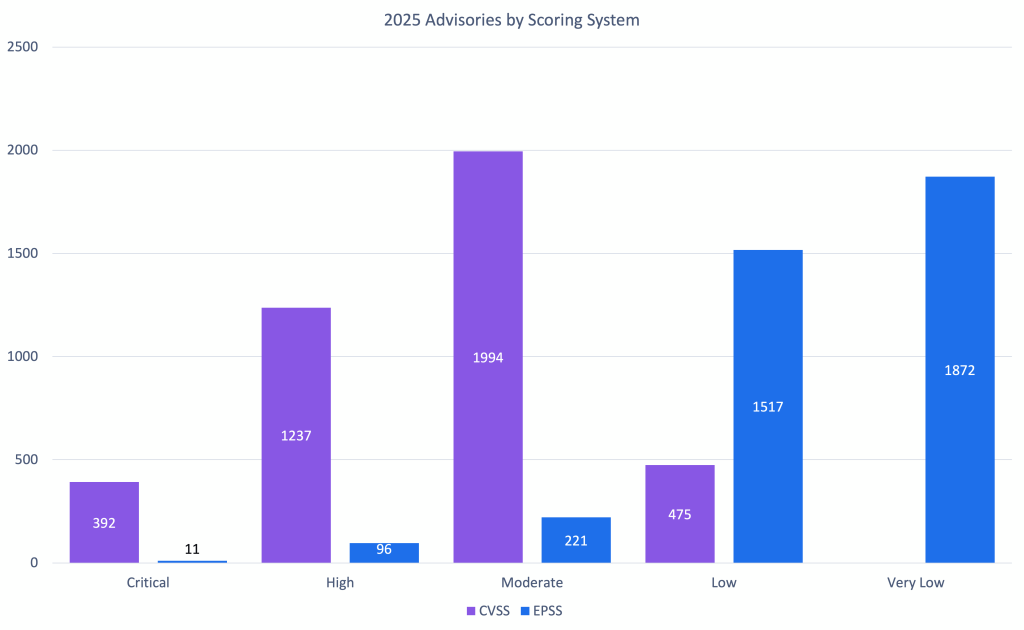
As you can see, when considering impact, most vulnerabilities skew moderate to high of the impact range. Low-impact vulnerabilities are likely more common than the CVSS data suggests but are often not considered worth the time and effort for researchers and maintainers to report. The EPSS scores for moderate to high impact vulnerabilities support this decision.
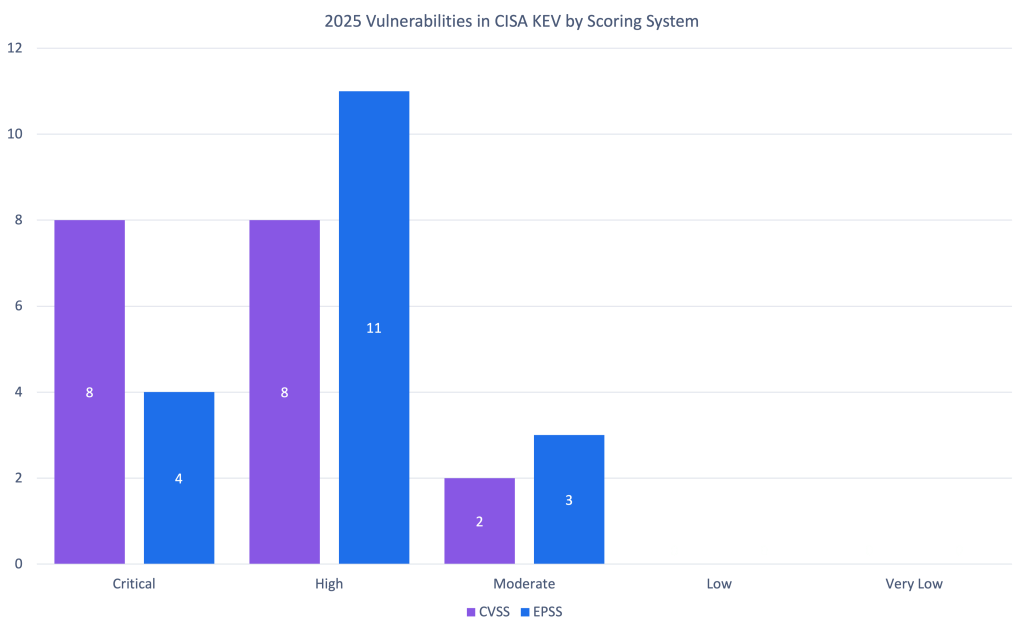
So should you trust the EPSS or CVSS scores? To judge that, let’s look at how they match up to vulnerabilities in CISA’s Known Exploited Vulnerabilities Catalog. The exploited vulnerabilities are at least scored moderate, and most are critical or high. While CVSS has more of the exploited vulnerabilities as critical, it also has far more vulnerabilities in the range in general. Combining the two can help you prioritize which vulnerabilities to address to prevent exploitation.
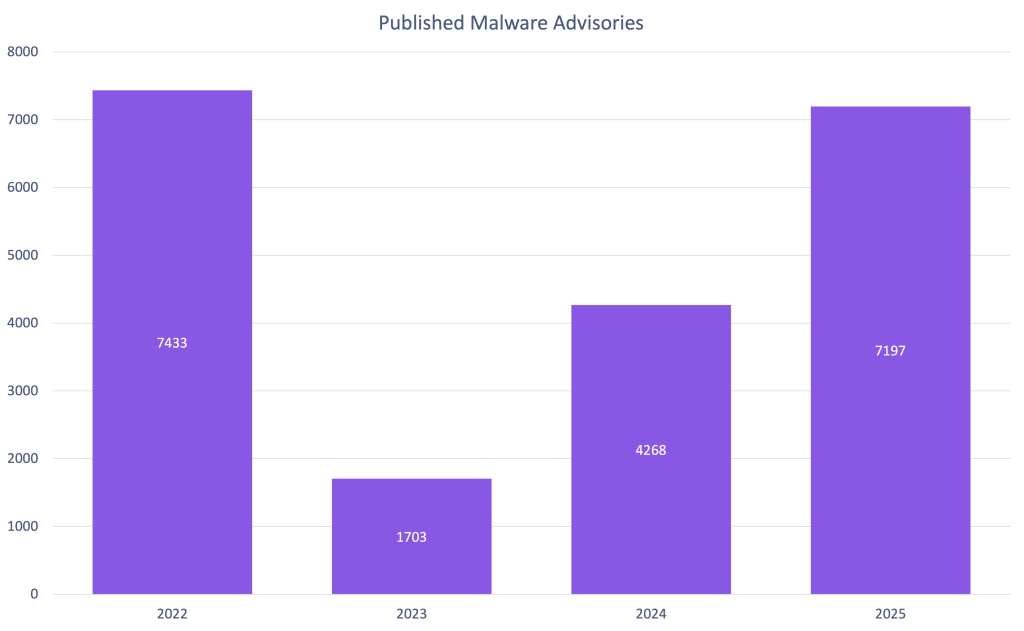
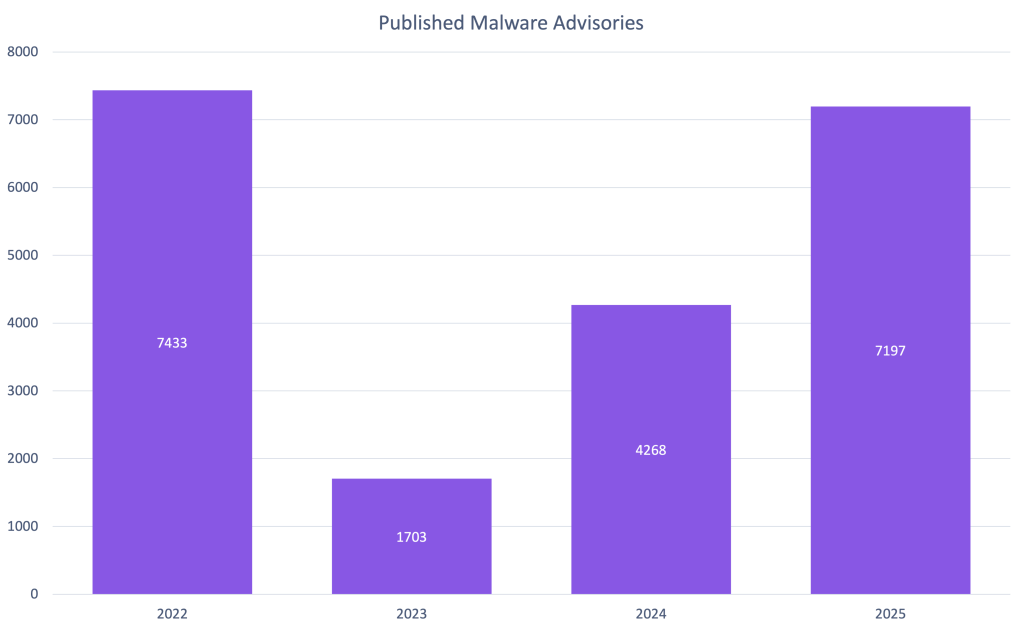
2025 was a huge year for npm malware advisories. Due to large malware campaigns, such as SHA1-Hulud, GitHub saw a 69% increase in published malware advisories compared to 2024. This is the most malware advisories GitHub has published since our initial release of historical malware when we added support in 2022.
You can receive Dependabot alerts when your repositories depend on npm packages with known malicious versions. When you enable malware alerting, Dependabot matches your npm dependencies against malware advisories in the GitHub Advisory Database.
CVE publications
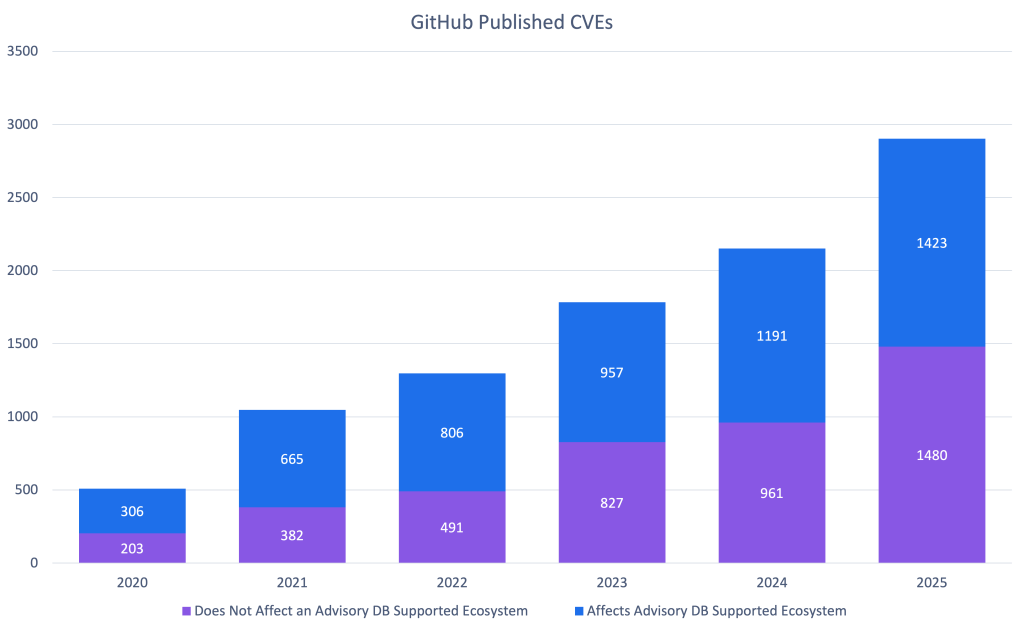
2025 was a big year for the GitHub, Inc. CNA. We saw a 35% increase in published CVE records, outpacing the overall CVE Project’s increase of 21%.
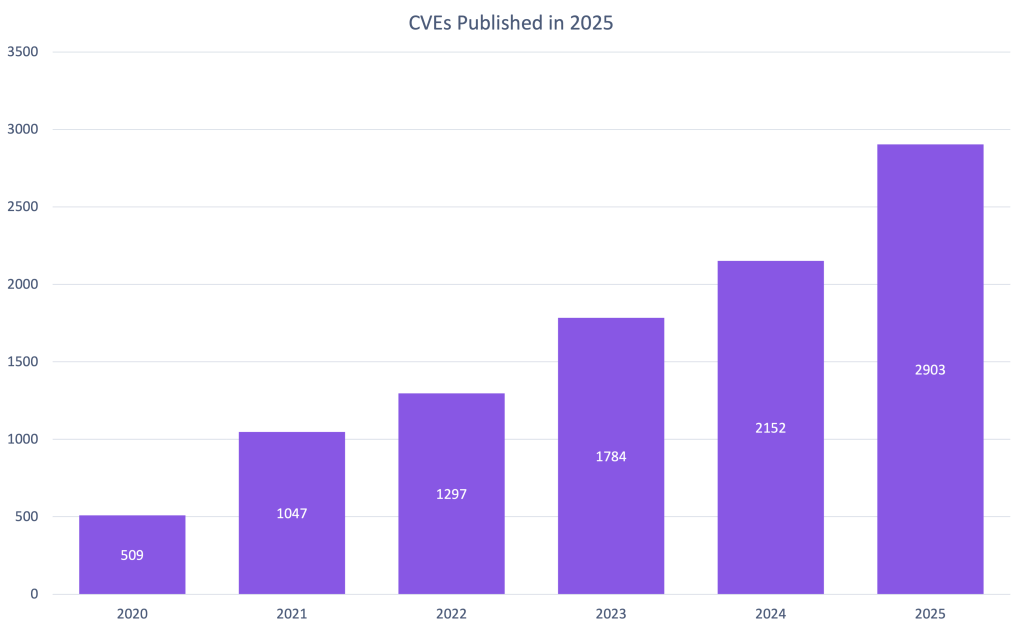
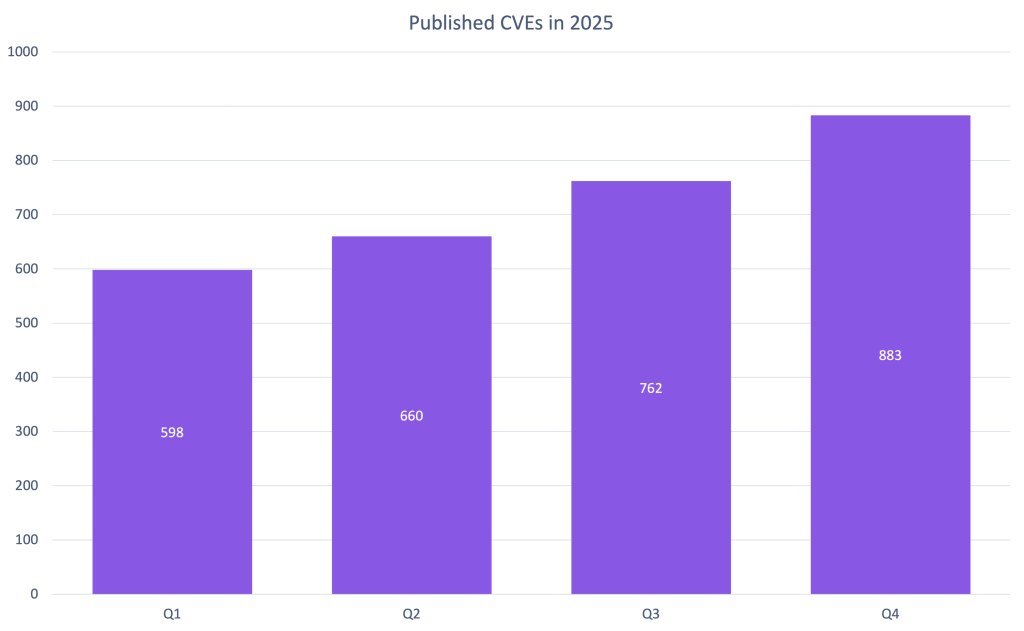
In fact, we saw 10 to 16% growth every quarter. If this trend continues, GitHub will publish over 50% more CVEs in 2026.
You can help make that a reality by requesting a CVE from us the next time you publish a repository security advisory about a vulnerability!
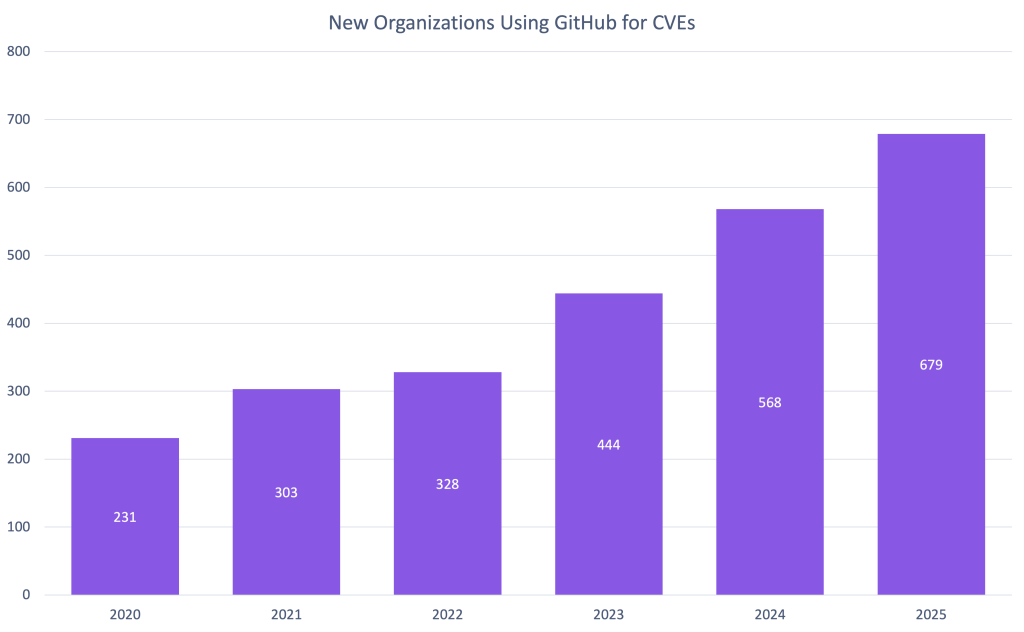
Organizations using GitHub’s CNA
Every year, GitHub sees more organizations use its CNA services. 2025 is no exception with a 20% increase in new organizations requesting CVE IDs.
Unlike reviewed global advisories, which are always mapped to packages in ecosystems we support, any maintainer on GitHub can request a CVE, even if they don’t publish that package to a supported ecosystem. In fact, 2025 is the first year that GitHub has published more CVEs from organizations that do not use a supported ecosystem than those that do.
We would like to thank all 987 organizations that published CVEs with us in 2025 and highlight the top 10 most prolific organizations.
| Top 10 organizations using the GitHub CNA | |
|---|---|
| Organization | Number of 2025 CVEs |
| LabReDeS (WeGIA)* | 130 |
| XWiki | 40 |
| Frappe | 28 |
| Discourse | 27 |
| Enalean | 27 |
| FreeScout* | 27 |
| DataEase | 26 |
| Nextcloud | 25 |
| GLPI | 24 |
| DNN Software* | 23 |
* Organizations that published CVEs through GitHub for the first time in 2025
The data from 2025 shows incredible growth:
- 4,101 reviewed advisories
- 7,197 malware advisories
- 2,903 CVEs published
- 679 new organizations using our CNA services.
These numbers represent real security improvements for millions of developers.
You can be part of this in 2026. Here’s how:
1. Use our CNA services
Publishing CVEs shouldn’t be complicated. Request a CVE directly from your repository security advisory, and we’ll take care of curating and publishing it for you. It’s free, it’s fast, and it helps the entire ecosystem understand and respond to vulnerabilities.
2. Improve advisory accuracy
Found an unreviewed advisory affecting a supported package? See incorrect severity scores or missing affected versions? Suggest edits. Your edits will be reviewed by the Advisory Database team and ultimately, will help make the database more accurate for everyone. In 2025, 675 contributions from the community improved the quality of this data for the entire software industry!
3. Protect your projects
The most direct impact you can have is protecting your own code. Enable Dependabot to automatically receive security updates and explore GitHub Advanced Security for comprehensive protection.
4. Make reporting a vulnerability easier
Let researchers know how to report to you and what you will and will not accept by creating a security policy for your repository. Enable private vulnerability reporting to make the coordination process smooth and secure.
Let’s make 2026 even better. See you in next year’s review! 🚀
Written by
Related posts
Explore more from GitHub
GitHub
Build what’s next on GitHub, the place for anyone from anywhere to build anything.
The GitHub Podcast
Catch up on the GitHub podcast, a show dedicated to the topics, trends, stories and culture in and around the open source developer community on GitHub.
如有侵权请联系:admin#unsafe.sh