
嗯,用户让我总结这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头。直接写描述就行。 首先,我得通读一下文章。文章主要讲的是能源行业的勒索软件攻击情况,2025年发生了187起确认的攻击事件。影响很大,比如导致公司损失和居民生活不便。攻击者主要集中在几个团伙,如RansomHub、Akira等。 然后,文章分析了能源行业成为目标的原因:老旧的基础设施、IT和OT的融合、分布广泛的攻击面。还有漏洞利用的问题,很多是已知漏洞未修补。 最后,文章给出了防御建议:网络分段、监控黑市、快速补丁、准备应急响应等。 所以,总结的时候需要涵盖这些要点:勒索软件攻击现状、原因、影响以及防御措施。控制在100字左右。 可能的结构是:2025年能源行业遭受大量勒索软件攻击,原因包括老旧系统和漏洞利用,影响严重。建议加强安全措施以提高韧性。 这样应该能简洁明了地概括文章内容。 </think> 2025年全球能源行业遭遇187起勒索软件攻击,造成重大损失和影响。老旧基础设施、IT-OT融合及广泛分布的攻击面使能源行业成为主要目标。尽管难以完全消除风险,但通过网络分段、漏洞修复和应急响应等措施可提升韧性以应对威胁。 2026-3-26 07:15:42 Author: cyble.com(查看原文) 阅读量:33 收藏
The Energy Sector’s Ransomware Nightmare: Why Critical Infrastructure Can’t Catch a Break
Energy sector ransomware nightmare continued in 2025 but here’s lessons to learn for critical infrastructure protection in 2026.
Let’s talk about the sector that keeps our lights on, water running, and industries humming—and why it’s become ransomware’s favorite target.
In 2025, the global energy and utilities sector faced 187 confirmed ransomware attacks. Not attempts. Confirmed, successful intrusions where attackers locked systems, stole data, and demanded payment. And that’s just what we know about.
If you think that number sounds alarming, you’re paying attention.
When Ransomware Hits Where It Hurts
Here’s the thing about attacking energy infrastructure: the impact cascades. When ransomware paralyzed Halliburton’s operations in August 2025, the company disclosed a $35 million loss. When hackers using FrostyGoop malware hit a Ukrainian municipal energy company, residents in Lviv lost heating during sub-zero temperatures.
These aren’t abstract data breaches. They’re disruptions that affect millions of people who depend on essential services. And attackers know this—which makes energy companies prime targets for extortion.
The ransomware groups leading this assault? RansomHub tops the list with 24 incidents (12.8% of the total), followed closely by Akira with 20 attacks (10.7%) and Play with 18 (9.6%). Throw in Qilin and Hunters/Lynx, and you’ve got five crews responsible for nearly half of all ransomware incidents against energy targets worldwide.
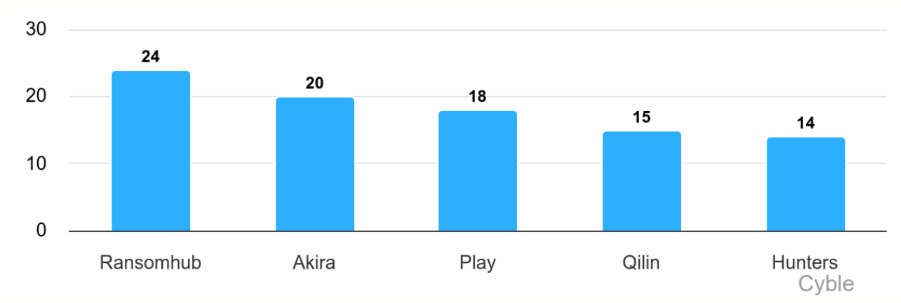
That’s not a diverse threat landscape—that’s concentrated, organized, industrial-scale cybercrime targeting critical infrastructure.
Why Energy? Follow the Vulnerability
Energy companies face a perfect storm of attack vectors that most sectors don’t deal with.
Legacy Infrastructure
Many power plants, refineries, and water treatment facilities run on operational technology (OT) systems that are decades old. We’re talking about industrial control systems running outdated protocols like Modbus and DNP3—designed in an era when “cybersecurity” wasn’t even a concept. These systems were built for reliability and uptime, not network defense.
IT-OT Convergence
As energy companies digitized operations for efficiency, they connected previously isolated industrial systems to corporate IT networks. That convergence created pathways for attackers to move from phishing an employee’s laptop to accessing SCADA systems controlling physical infrastructure.
Distributed Attack Surface
Unlike a bank with centralized data centers, energy infrastructure is geographically dispersed. Solar farms, wind installations, substations, pipeline monitoring stations—each represents a potential entry point. And managing security across hundreds or thousands of remote sites? That’s a nightmare.
The Numbers Tell a Grim Story
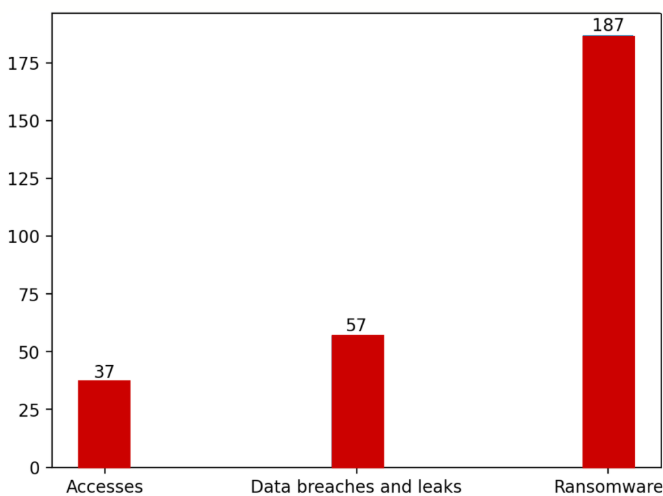
Between July 2024 and June 2025, the energy sector didn’t just face ransomware. It got hit from every angle:
- 37 incidents of compromised network access advertised for sale on criminal forums
- 57 data breach and leak events exposing sensitive operational data
- 187 ransomware attacks encrypting systems and exfiltrating files
- Over 39,000 hacktivist posts targeting energy infrastructure
To get the complete analysis on data breaches, ransomware attacks and attackers, hacktivists, and vulnerabilities plaguing the energy and utilities sector worldwide, download Cyble’s full report now!
North America bore the brunt of ransomware attacks, accounting for over one-third of incidents. But Asia and Europe weren’t far behind, each absorbing significant portions of compromised access sales and data breaches.
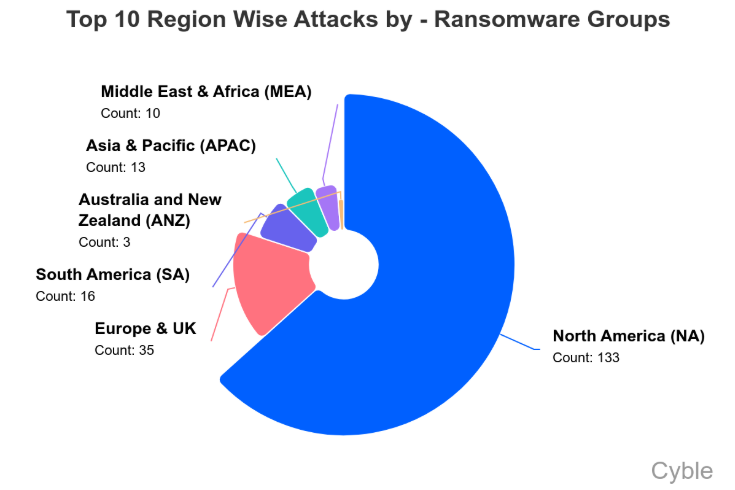
This geographic distribution tells us something important: attackers aren’t focused on one region. They’re systematically targeting energy infrastructure globally, exploiting whichever networks offer the easiest access.
The Broker Economy Feeding the Fire
Here’s a disturbing trend: initial access brokers are specializing in energy targets.
During the reporting period, Zerosevengroup, mommy, and miyako led sales of compromised energy sector credentials. Together, they posted about 27% of observed access offerings. That might not sound like much until you realize the remaining 73% was split among dozens of one-time sellers.
What this fragmentation means: barriers to entry for attacking energy infrastructure are low. You don’t need to be an elite hacker anymore. Just buy credentials from a broker for a few thousand dollars, and you’ve got a foothold in a power company’s network.
One particularly alarming listing? In March 2025, ZeroSevenGroup advertised admin-level access to a UAE water and power holding company, claiming reach over 5,000 network hosts. Another broker offered access to an Indonesian power plant operations subsidiary. A third claimed control-level access to a French wastewater treatment platform.
These aren’t theoretical vulnerabilities. They’re active criminal advertisements offering buyers the keys to critical infrastructure.
When Hacktivists Target the Grid
Geopolitical hacktivist groups added another dimension to the threat landscape in 2025—and some crossed lines that genuinely matter.
Pro-Russian groups like Sector 16 didn’t just deface websites or leak stolen documents. They claimed—and provided video evidence of—actual manipulation of operational technology at US oil and gas facilities. We’re talking about interfaces controlling shutdown systems, production monitoring, gas-lift controls, and valve actuation.
Whether they could have caused physical damage is debatable. That they had access to try? Undeniable.
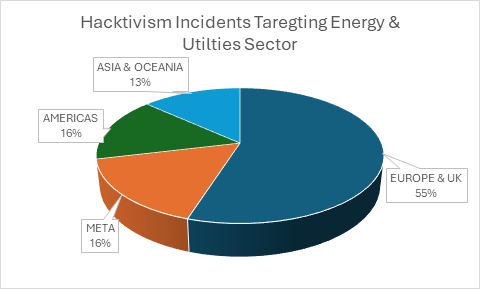
Similarly, the Golden Falcon Team claimed breach of a French wastewater monitoring platform with access to pH controls, temperature settings, and water distribution parameters. Again, the claimed level of access would allow manipulation of real-world physical processes.
Most hacktivist activity in 2025 consisted of low-level DDoS attacks and propaganda—more noise than genuine threat. But when groups start demonstrating OT access? That’s crossing from nuisance into dangerous territory.
The Colonial Pipeline Echo
Remember May 2021? The Colonial Pipeline ransomware attack that caused fuel shortages across the US East Coast?
That incident was supposed to be a wake-up call. Colonial supplies 45% of fuel for the East Coast. The attack forced them to pay $5 million in ransom just to resume operations. Panic buying. Gas station shortages. Economic disruption.
Four years later, we’re seeing similar attacks globally but with faster execution. The median time from breach to encryption has collapsed. Modern ransomware groups move through networks in hours, not weeks. They know exactly which systems to target for maximum leverage.
And here’s the kicker: many of these attacks succeed using known vulnerabilities that victims simply hadn’t patched.
Vulnerabilities: The Same Old Story
Throughout 2025, attackers exploited critical flaws in systems that energy companies depend on daily:
- ABB ASPECT systems used in substations
- Siemens SENTRON PAC3200 power meters
- Mass-deployed solar inverter platforms
- Schneider Electric Jira instances
- Various VMware, Ivanti, and Fortinet products
What’s frustrating is that patches existed for most of these. The median remediation time across energy enterprises exceeded 21 days—while attackers were weaponizing exploits within 72 hours of public disclosure.
That 18-day gap? That’s your exposure window. That’s when you’re vulnerable to attacks using publicly documented methods that everyone knows about.
What Defense Looks Like
So what actually works when you’re defending energy infrastructure against this onslaught?
Segment Everything
Your OT networks shouldn’t be reachable from corporate IT. Period. Air-gap where possible. When connection is necessary, lock it down with rigorous access controls, monitoring, and authentication. Every pathway between IT and OT is a potential attack vector.
Hunt the Broker Market
Continuous monitoring of criminal forums isn’t just for intelligence agencies anymore. Organizations need visibility into whether their credentials or network access is being advertised for sale. Finding out after an attack that your access was sold three months earlier? That’s too late.
Patch with Urgency
I know, I know—patching OT systems is complex. Downtime is expensive. Testing is slow. But you know what’s more expensive? Halliburton’s $35 million ransomware loss. Or NovaScotia Power dealing with 280,000 customers’ exposed data.
Create aggressive patch timelines. Test in parallel. Prioritize internet-facing systems and known exploited vulnerabilities. Move fast.
Prepare for the Worst
Every energy company should have tested incident response playbooks that assume successful breach. Can you isolate compromised systems? Do you have offline backups they can’t encrypt? Can you switch to manual operations if SCADA goes down? Have you drilled these scenarios?
Because when ransomware locks your systems at 3 AM on a Sunday, you won’t have time to figure it out.
The Honest Truth
Here’s what nobody wants to say out loud: perfect security for energy infrastructure is impossible.
The attack surface is too large. The systems are too old. The connectivity requirements are too complex. The attacker economics favor offense.
But perfect security isn’t the goal. Resilience is.
Resilient organizations detect breaches quickly. They respond effectively. They recover without paying ransoms. They learn from incidents and improve their defenses.
The energy sector can’t eliminate ransomware risk. But it can reduce the window of exposure, limit the blast radius, and ensure continuity of critical operations even under attack.
Because the next attack isn’t coming someday. It’s probably happening right now, somewhere in the supply chain, and the question is whether defenses will catch it before ransomware deploys.
For energy and utilities operators navigating the 2026 threat landscape, the challenge is clear: defend infrastructure designed for a pre-internet era against adversaries armed with industrialized attack tools. Resilience isn’t optional anymore—it’s survival.
如有侵权请联系:admin#unsafe.sh
