嗯,用户让我总结一下这篇文章的内容,控制在100字以内,而且不需要用“文章内容总结”之类的开头。首先,我需要通读全文,抓住主要信息。 文章讲的是威胁行为者如何利用Binance Smart Chain(BSC)作为恶意软件的C2基础设施。VMRay和Iknaio合作分析了一个案例,追踪了加密货币流动,发现了线索。他们通过动态分析和跨链追踪,揭示了资金流向交易所,为执法提供了线索。 接下来,我需要把这些要点浓缩到100字以内。重点包括:滥用BSC作为C2、VMRay和Iknaio的合作、跨链追踪、资金流向交易所、执法线索。 然后组织语言,确保流畅且信息完整。可能的结构是:威胁行为者利用BSC作为C2基础设施,VMRay和Iknaio合作分析案例,追踪资金流向交易所,为执法提供线索。 检查字数是否符合要求,并确保没有使用不需要的开头词。最终总结应该简洁明了。 </think> 威胁行为者利用Binance Smart Chain(BSC)作为恶意软件的Command-and-Control(C2)基础设施。VMRay与Iknaio合作分析案例,追踪加密货币流动并揭示资金流向交易所,为执法提供线索。 2026-3-24 15:50:6 Author: www.vmray.com(查看原文) 阅读量:13 收藏
Threat actors are constantly evolving their tactics. One increasingly observed technique involves abusing public blockchains, specifically the Binance Smart Chain (BSC), as Command-and-Control (C2) infrastructure for malware operations. By hosting malicious code on-chain, attackers can circumvent traditional blocking mechanisms: smart contracts cannot simply be taken down like a conventional web server.
In a recent joint investigation, VMRay and Iknaio Cryptoasset Analytics collaborated to analyze a specific malware sample leveraging this technique, sometimes referred to as *EtherHiding*. They traced the associated cryptocurrency flows across multiple blockchain networks, uncovering leads that could help law enforcement identify the perpetrators.
How VMRay discovered the malware
VMRay’s lab team continuously analyzes new malware samples to identify emerging techniques. During routine analysis, they identified a sample from [URLhaus](https://urlhaus.abuse.ch/url/3581740/) that was distributed via a URL hosted on infrastructure belonging to a UK-based company (since taken down). What made this sample stand out: it used a public blockchain as its C2 channel, a technique that is difficult to disrupt because blockchain data is immutable and globally accessible.
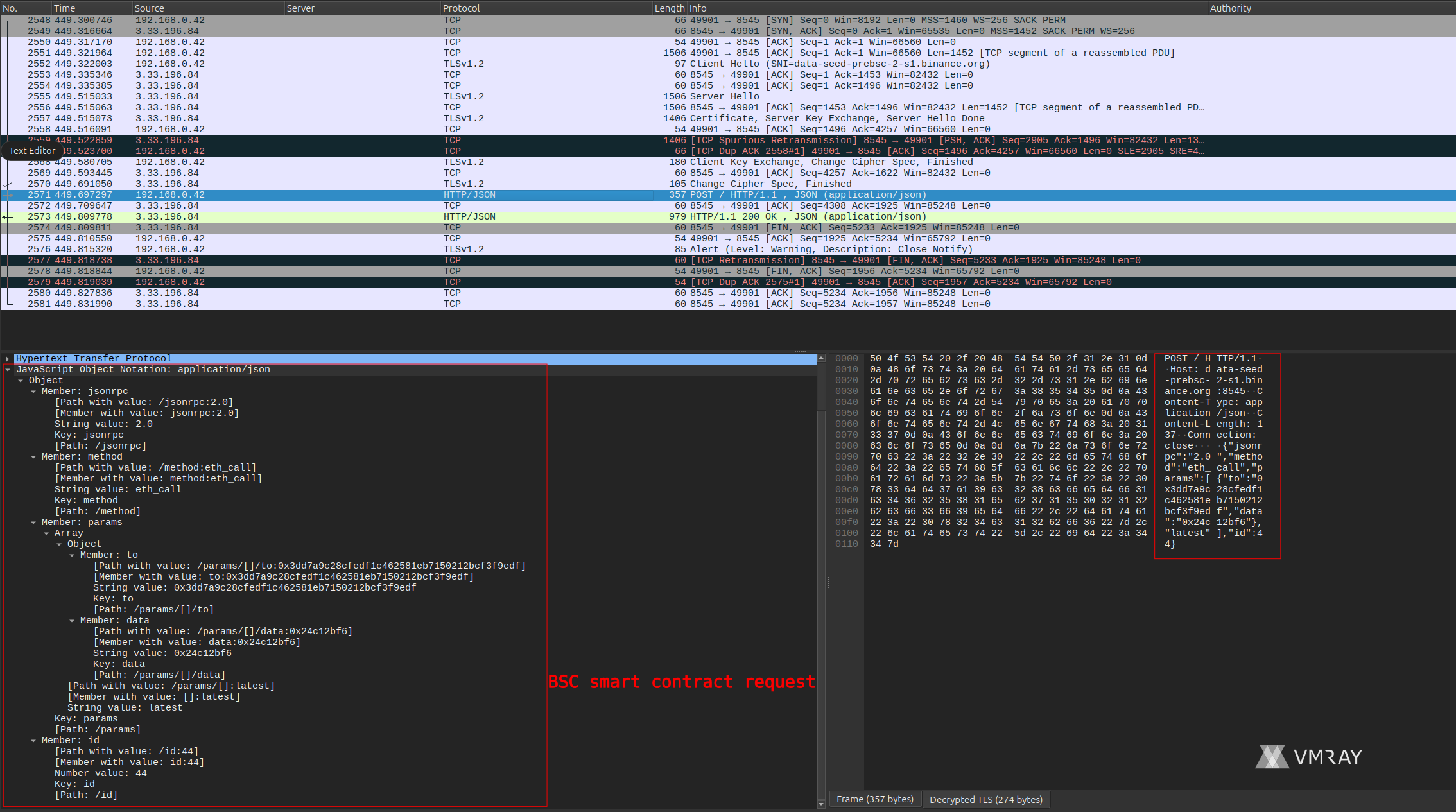
VMRay’s dynamic analysis revealed the malware’s behavior in detail: upon execution, it reached out to a smart contract deployed on the BSC network to retrieve C2 instructions. The sandbox captured the exact contract interaction, including the ABI function call the malware used to fetch its command payload. This level of visibility that static analysis alone would not provide.
The threat actor deployed this contract and periodically invoked its `update` function to push new encoded command sequences. Notably, the contract was deployed on the BSC Testnet, a testing environment where gas fees are paid with freely available testnet BNB rather than real tokens. This means that on the BSC side, there is no direct financial trail from gas payments. However, the operational infrastructure behind the contract still required real funding elsewhere, and that is where the money trail begins.
Note: Specific on-chain addresses and indicators of compromise have been shared with relevant authorities and are available to law enforcement upon request.
From BSC to Ethereum: a cross-chain investigation
This is where Iknaio’s blockchain analytics expertise came in. VMRay reached out to Iknaio to help trace who was behind the blockchain transactions funding this operation.
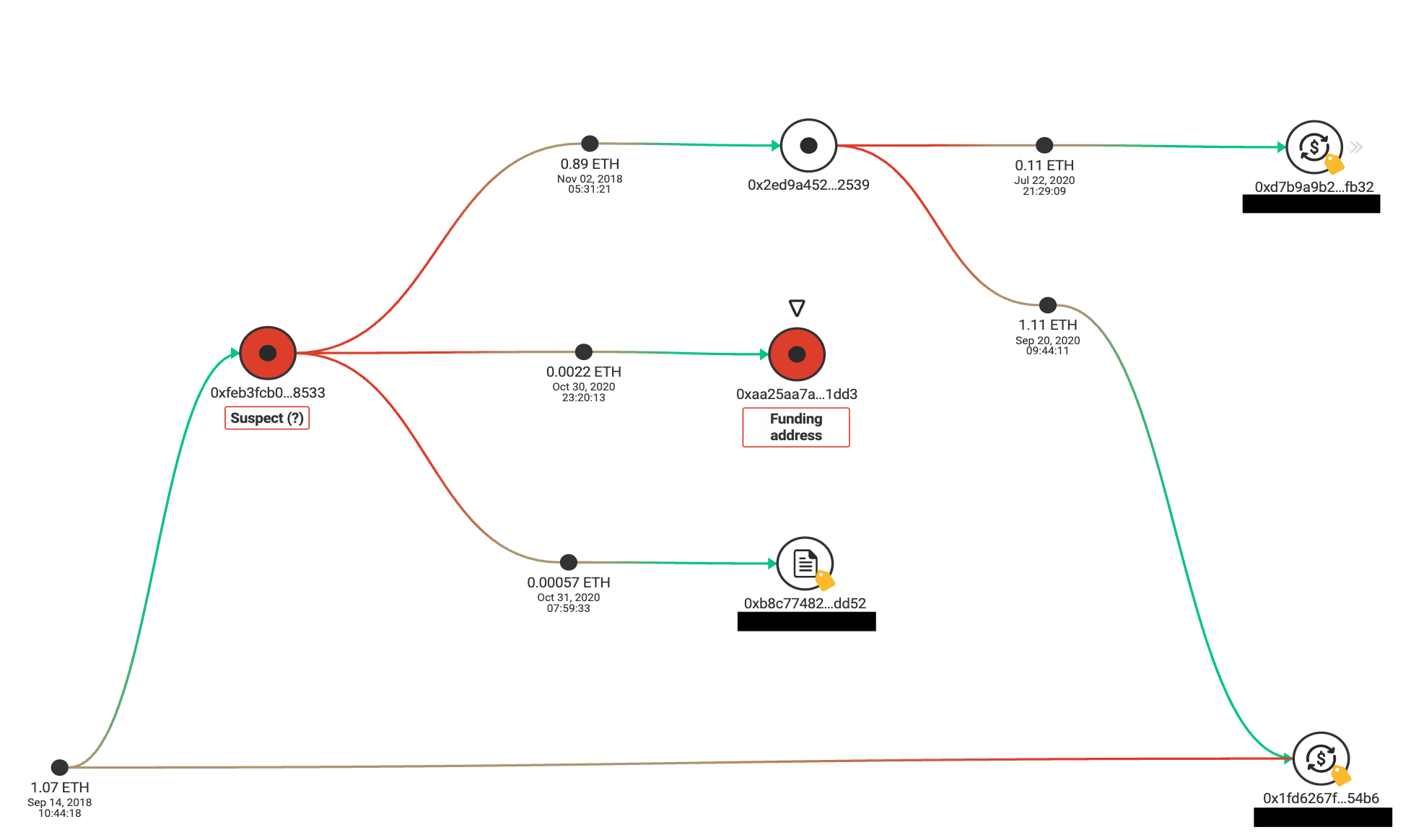
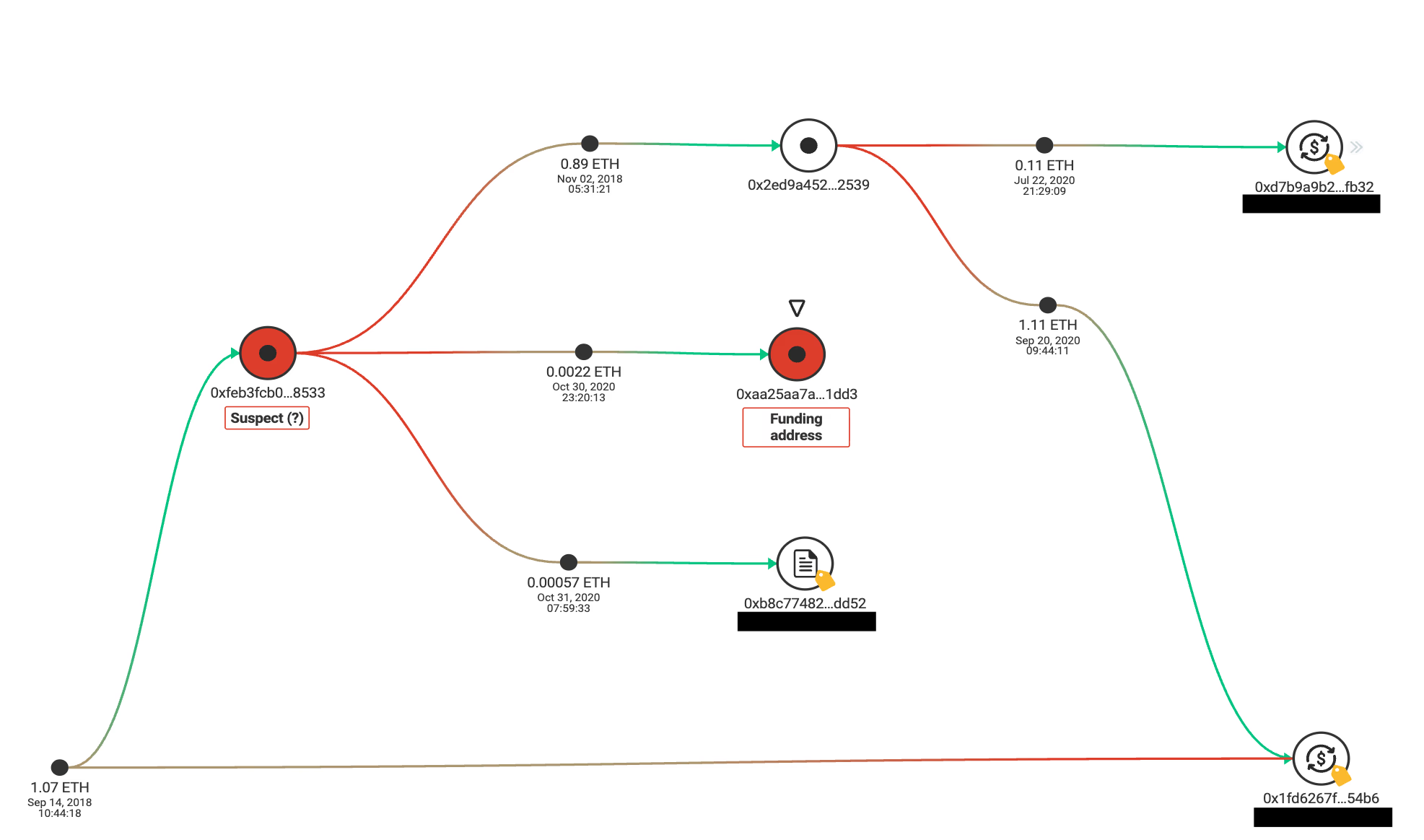
Starting from the smart contract address VMRay identified, Iknaio worked backwards through the on-chain transaction history. Using GraphSense, Iknaio’s open-source cryptoasset analytics platform, the team applied address clustering heuristics and cross-chain resolution techniques that go well beyond what a manual block explorer lookup can achieve. This automated analysis traced the contract creator, identified the address that funded the deployment, and detected that the same cryptographic key pair had been used on another blockchain network.
By pivoting the investigation to the Ethereum mainnet, Iknaio uncovered a trail of real-value transactions connected to the same entity. These were transactions that the BSC Testnet alone would never have revealed.
Following the money on Ethereum
On the Ethereum chain, Iknaio’s analysis revealed that the funding address had received funds from another address with direct connections to a well-known cryptocurrency exchange. The investigation showed that this address both received funds from and sent funds to exchange-controlled addresses. Additional on-chain activity suggested the purchase of BNB tokens, likely used to fund the C2 operations on BSC.
Regulated exchanges operating under Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations are required to collect personally identifiable information on their users. These exchange connections therefore represent potential investigative leads. It is worth noting, however, that KYC processes are not infallible: accounts may have been opened with stolen or fabricated identity documents, and the level of verification varies between exchanges and jurisdictions. Obtaining actual user data also requires formal legal process, which can involve cross-border cooperation and significant lead times. Nonetheless, the identified exchange interactions provide law enforcement with a concrete starting point for further investigation.
Why this matters
This case illustrates several important trends in the threat landscape:
– Blockchain as C2 infrastructure is a growing technique. As documented in recent reports by [Microsoft](https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/msc/documents/presentations/CSR/Microsoft-Digital-Defense-Report-2025.pdf), [Guardio Labs](https://guard.io/labs/etherhiding-hiding-web2-malicious-code-in-web3-smart-contracts), and [Google Cloud Threat Intelligence](https://cloud.google.com/blog/topics/threat-intelligence/unc5142-etherhiding-distribute-malware), threat actors are increasingly hiding malicious payloads in smart contracts.
– Cross-chain analysis is essential. Investigators who limit their scope to a single blockchain risk missing critical connections. Address reuse across chains with compatible address schemes (Ethereum, BSC, Polygon, Arbitrum, and others) is common and exploitable for forensic purposes.
– Collaboration between malware analysts and blockchain investigators closes the gap. VMRay’s sandbox captured the live interaction between the malware and the smart contract, revealing the exact contract address, function calls, and encoded payloads that a static analysis would miss. Iknaio then took that on-chain footprint and applied cross-chain clustering and tracing techniques to follow the money to exchange-linked addresses on another chain. Neither could have achieved this result alone: without VMRay’s dynamic analysis, the blockchain entry point would remain unknown; without Iknaio’s cross-chain analytics, the on-chain evidence would lead to a dead end on a testnet.
Conclusion
The convergence of malware operations and blockchain technology creates new challenges for defenders, but also new opportunities. When threat actors interact with public blockchains, they leave permanent, transparent records of their financial activity. By combining malware analysis with cross-chain blockchain forensics, investigators can turn the attackers’ own infrastructure against them.
This joint investigation by VMRay and Iknaio demonstrates how the combination of dynamic malware analysis and cryptoasset tracing can produce leads that bring law enforcement closer to identifying the individuals behind sophisticated cyber threats.
This investigation was conducted jointly by [VMRay](https://www.vmray.com/) and [Iknaio Cryptoasset Analytics](https://www.iknaio.com/).
如有侵权请联系:admin#unsafe.sh