好的,我现在需要帮用户总结一篇文章,控制在100字以内。首先,我得仔细阅读文章内容,抓住主要信息。 文章讲的是一个中型大学的安全项目,他们通过钓鱼测试来评估安全风险。最初,84个凭证被钓鱼,导致了严重的内部漏洞,比如权限过高和数据泄露。后来他们采取了NodeZero平台进行深入分析和修复,结果在后续测试中只发现了2个凭证被利用,漏洞大幅减少。 我需要把这些关键点浓缩成一句话。重点包括:钓鱼测试揭示内部漏洞、修复后的显著改善、以及安全措施的有效性。 现在组织语言,确保不超过100字。可能的结构是:钓鱼测试显示内部问题,修复后风险降低。 最终总结应该是:大学通过钓鱼测试发现内部漏洞,随后采取措施显著降低风险。 </think> 大学通过钓鱼测试发现内部身份权限问题和数据暴露风险,并采取针对性措施显著降低安全威胁。 2026-3-11 15:21:36 Author: horizon3.ai(查看原文) 阅读量:12 收藏
A Pentest Wednesday® Story
Security programs rarely fail because teams ignore phishing risks. They fail because phishing is measured by click rate, not by consequence.
At a mid-sized university, phishing awareness training had improved year over year. Click rates were low. On paper, the organization appeared disciplined.
But awareness metrics do not reveal what happens after a credential is submitted.
Inside the environment, identity sprawl had grown quietly over time. Permissions accumulated. Legacy systems remained in place. Access patterns expanded with operational needs. Like many institutions balancing modernization with budget constraints, complexity increased faster than security visibility.
Phishing simulations were active. Patch cycles were consistent. Security conversations were happening. What was missing was proof of impact.
The university’s security program is led by a single practitioner.
“I’m the security department. I’m the SOC analyst. I’m the incident handler. I do it all.”
When you are a team of one, you cannot chase everything. You have to focus on what actually reduces risk. As the security lead explained:
“We had a well-accepted belief that, oh well, that’s internal, it’s not going to be a problem.”
That belief held until it was tested.
Outcomes at a Glance
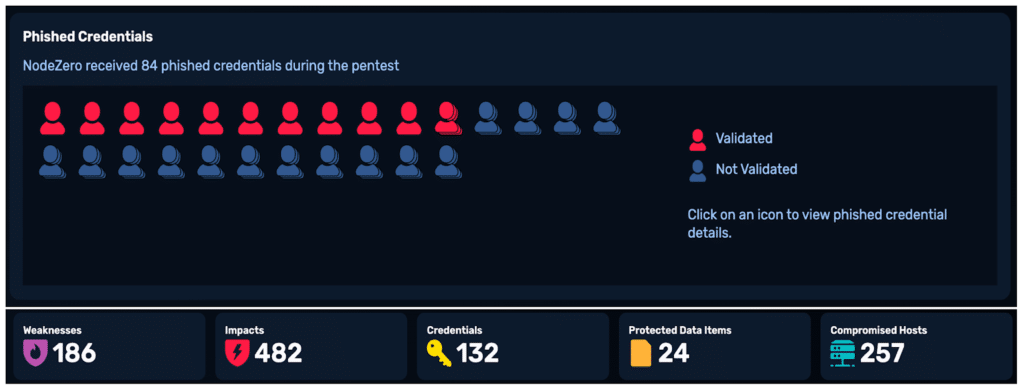
Early 2025 – Phishing Impact Test
- 84 phished credentials
- 132 credentials leveraged during the pentest
- 186 weaknesses identified
- 482 verified impacts
- 257 compromised hosts
- 24 PCI-classified data items discovered
- Domain compromise achieved
Late 2025 – Follow-Up Phishing Impact Test
- 2 phished credentials
- 3 remaining potentially exploitable weaknesses
- No cascading domain-wide compromise
- Dramatically reduced ransomware exposure
Same institution. Same security lead. Fundamentally different risk posture.
Impact
In early 2025, 84 users entered their credentials during a phishing simulation. Rather than treating this as a training metric, the university used those real credentials to emulate an active breach using Phishing Impact Testing within the NodeZero® platform.
This wasn’t about who clicked. It was about what happened next.
Authenticating as compromised users, the platform mapped permissions, escalated privileges, and chained exploitable weaknesses together, just as an attacker would.
Nineteen minutes later, it had established a path to domain control.
Over the next 28 hours, NodeZero mapped the complete blast radius tied to those 84 compromised credentials.
- 482 verified impact paths
- 257 compromised hosts
- Domain compromise
- Ransomware exposure across critical systems
- 24 PCI-classified data items identified
Those 24 PCI-classified data items were not abstract findings. In a university environment, PCI classification typically aligns to student payment systems, tuition transactions, and financial account data. When combined with domain-level compromise, that exposure shifts from technical risk to institutional risk.

Figure 1. Phishing impact test summary showing 84 phished credentials, 482 impacts, and 257 compromised hosts.
As the security lead at the university explained:
“When we ran a pentest where somebody clicked on a phishing link and within 30 some odd minutes a domain controller had been compromised and they owned us, that was proof we had to pay attention to the internal side as well.”
The attack path visualization showed exactly how those phished credentials were chained into privilege escalation and infrastructure compromise.

Figure 2. Attack path visualization demonstrating domain user compromise, critical infrastructure compromise, domain compromise, and host compromise.
The pentest also revealed considerable data at risk. One compromised credential had access to 7,587 data resources across 862 assets. Another had access to 297,676 data resources across 302 assets. A third exposed more than 3.7 million data resources and was linked to 319 distinct attack paths.
Following these findings, the university upgraded to NodeZero Elite to expand reporting and data analysis capabilities. That upgrade includes Advanced Data Pilfering, which enables deeper inspection of exposed data resources to better understand the sensitivity of what is at risk.

Figure 3. Attack path visualization demonstrating domain user compromise leading to ransomware exposure and sensitive data exposure.
“It will try and exploit it and it will tell me that yeah, it owns me… not a great thing to see, but now at least I know what reality is.”
That visibility removed ambiguity. It turned assumption into measurement.
Background
The university’s security function is led by a single practitioner responsible for everything from vulnerability prioritization to executive reporting.
With limited resources, manually analyzing thousands of vulnerabilities is not sustainable. For a department of one, understanding how weaknesses connect and which credentials create the most leverage matters more than sheer vulnerability volume.
The first phishing impact test provided that clarity. It was not simply a list of findings. It demonstrated how identity misconfigurations, excessive permissions, and legacy weaknesses could be chained together into meaningful compromise and where remediation would have the greatest effect.
More importantly, it revealed where risk was concentrated.
One credential alone represented 66 percent of critical impact paths. Another accounted for 18 percent. Remediating those high-leverage accounts collapsed the majority of the attack paths.
“I needed to move from reacting to alerts to understanding what actually matters.”
That shift was strategic. It was about reducing exploitability, not just reducing counts.
Mitigation
The security lead focused on collapsing the attack paths that had been proven exploitable. Rather than attempting to eliminate all 186 weaknesses at once, the next few months were spent prioritizing:
- Reducing excessive write permissions
- Tightening domain user privileges
- Addressing credential hygiene gaps
- Removing lateral movement pathways
- Retesting with NodeZero to confirm attack path elimination
The approach was deliberate and effective.
“It’s allowed me to be a lot more efficient. It saves me a bunch of time. I’m all about time saving.”

Figure 4. 1-Click Verify Summary proving closure of issues previously discovered was underway.
Remediation
In late 2025, the security lead needed to know if their efforts were paying off and repeated the phishing simulation exercise. This time, only two users submitted credentials, demonstrating measurable improvement in phishing awareness. Those credentials were again passed to NodeZero, which executed the same adversary-driven validation process as before.
This time, the difference in outcomes was measurable.
- 2 phished credentials
- 3 remaining potentially exploitable weaknesses
- No cascading domain compromise
- No widespread ransomware exposure
The weaknesses that previously enabled rapid escalation no longer enabled large-scale lateral movement.
The blast radius had collapsed.
“The follow-up test showed us that the remediation work mattered. It wasn’t just cleaner reports. There were fewer paths an attacker could actually use.”
“I’ve moved past the ‘putting out the fires’ kind of thing to actually starting to do more strategic planning and looking ahead.”

Figure 5. Phishing impact test summary showing two phished credentials and three remaining exploitable weaknesses.
Conclusion
Phishing awareness reduced click rates. Targeted remediation reduced blast radius.
In early 2025, a phishing simulation exposed a domain-wide blast radius. By late 2025, the same controlled exercise demonstrated that escalation paths were collapsed and exposure contained.
That delta represents measurable, validated risk reduction.
For leadership, this is the difference between assuming controls work and proving they do. It shifts security from activity-based reporting to outcome-based governance.
“It’s the security assistant that I never had, the one that never gets tired and never complains.”
The move from Patch Tuesday to Pentest Wednesday® is not only about running more tests. It is about continuously validating exposure, prioritizing what is exploitable, and demonstrating that remediation materially reduces institutional risk.
For a security team of one, that creates leverage.
For leadership, it creates confidence backed by proof.
如有侵权请联系:admin#unsafe.sh