好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得通读全文,抓住主要信息。 文章讲的是APT28组织,也叫Fancy Bear,他们从2024年4月开始用BEARDSHELL和COVENANT这两个恶意软件来长期监视乌克兰军方人员。这两个工具都是定制的,能长期保持访问权限并收集敏感信息。BEARDSHELL用Icedrive API传输数据,而COVENANT则利用云服务进行控制。此外,这些工具的代码和十年前的工具有很强的相似性,说明该组织一直在沿用和改进他们的工具。 接下来,我需要把这些要点浓缩到100字以内。要包括APT28、目标、时间、使用的恶意软件、功能以及代码的延续性。 可能的结构是:APT28使用BEARDSHELL和COVENANT从2024年4月开始长期监视乌克兰军方人员,这些工具利用云服务进行控制,并且代码与早期工具有延续性。 现在检查字数是否在限制内,并确保没有遗漏关键信息。 </think> APT28(Fancy Bear)自2024年4月起利用BEARDSHELL和COVENANT恶意软件对乌克兰军方实施长期监视。这些定制工具通过云服务实现持久访问和信息收集,并与该组织十年前的恶意软件代码相似。 2026-3-10 15:14:13 Author: securityaffairs.com(查看原文) 阅读量:1 收藏
APT28 conducts long-term espionage on Ukrainian forces using custom malware

APT28 used BEARDSHELL and COVENANT malware to spy on Ukrainian military personnel, enabling long-term surveillance since April 2024.
The Russia-linked group APT28 (aka UAC-0001, aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) has used BEARDSHELL and COVENANT malware to conduct long-term surveillance of Ukrainian military personnel. According to ESET, the campaign began in April 2024 and relies on custom implants designed to maintain persistent access and collect sensitive information from targeted systems.
“Since April 2024, Sednit’s advanced development team has reemerged with a modern toolkit centered on two paired implants, BeardShell and Covenant, each using a different cloud provider for resilience.” reads the report published by ESET. “This dual‑implant approach enabled long‑term surveillance of Ukrainian military personnel. Interestingly, these current toolsets show a direct code lineage to the group’s 2010‑era implants.”
The APT28 group has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. The group was involved also in the string of attacks that targeted 2016 Presidential election.
The group operates out of military unity 26165 of the Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS).
BEARDSHELL and SLIMAGENT are two advanced malware tools written in C++. BEARDSHELL downloads, decrypts (using ChaCha20-Poly1305), and runs PowerShell scripts, sending results via the Icedrive API. It creates a unique folder on each infected machine based on system identifiers. SLIMAGENT captures screenshots using Windows APIs, encrypts them with AES and RSA, and stores them locally with timestamped filenames. Both tools are stealthy, use strong encryption, and exploit legitimate cloud services to avoid detection, highlighting modern APT tactics.
“SlimAgent includes several features that were absent from the 2018 samples, such as encryption of the collected logs. Nevertheless, it is remarkable that samples deployed six years apart exhibit such strong code similarities.” continues the report. “We therefore assess with high confidence that both the 2018 samples and the 2024 SlimAgent sample were built from the same codebase.”

In May 2025, ESET researchers reported unauthorized access to an email account in the Ukrainian government’s gov.ua domain. CERT-UA, in collaboration with the Cybersecurity Center of Military Unit A0334, responded to the incident.
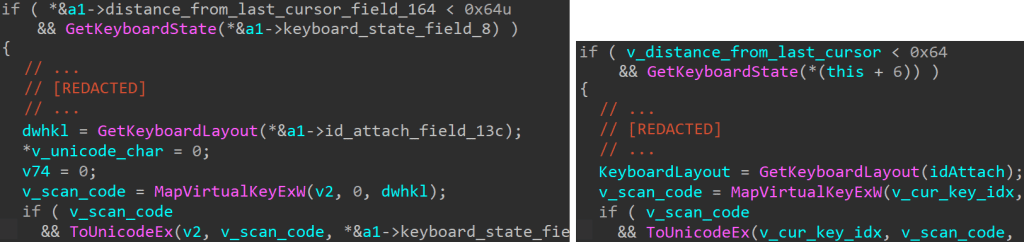
Analysis shows that SLIMAGENT likely evolved from the XAgent keylogger long used by APT28. Researchers found strong code similarities, including identical keylogging logic and HTML-based logging with the same color scheme for captured data. Evidence suggests SLIMAGENT has been deployed as a standalone espionage tool since at least 2018. Despite XAgent’s well-known codebase, the group continues reusing and adapting it, alongside newer malware like BEARDSHELL, in recent espionage campaigns.
During forensic analysis, the researchers discovered malware linked to the COVENANT framework and the BEARDSHELL backdoor. The experts were not able to determine the initial infection vector.
ESET noted that BEARDSHELL uses a rare obfuscation method called opaque predicate, previously seen in XTunnel, a tool used by APT28 during the Democratic National Committee hack. This link strongly suggests BEARDSHELL belongs to the group’s toolkit. Another tool, COVENANT, has been heavily modified to support long-term espionage and uses cloud services like Filen for command-and-control communications.
The cybersecurity firm reports that developers behind APT28 have developed strong expertise in the Covenant framework, despite its official development ending in 2021. The group has successfully adapted and reused the tool for several years, particularly in espionage operations targeting Ukrainian organizations.
“we have shown that Sednit’s advanced development team is active once again, operating an arsenal centered on two implants – BeardShell and Covenant – deployed in tandem and each leveraging a different cloud provider.” concludes the report. “The sophistication of BeardShell and the extensive modifications made to Covenant demonstrate that Sednit’s developers remain fully capable of producing advanced custom implants. Furthermore, the shared code and techniques linking these tools to their 2010-era predecessors strongly suggest continuity within the development team.”
Recently, ClearSky researchers reported a phishing campaign linked to Russia that targets Ukrainian organizations using two new malware families, BadPaw and MeowMeow. The attack chain begins with a phishing email carrying a link to a ZIP archive. When opened, an HTA file displays a Ukrainian-language lure about border crossing appeals while secretly launching the infection chain.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Russia)
如有侵权请联系:admin#unsafe.sh