好的,我现在需要帮用户总结一篇关于意大利恶意垃圾邮件活动的文章,控制在100字以内。首先,我得通读整篇文章,抓住主要信息。 文章提到TG Soft CRAM在2026年3月2日至8日的报告,全球和意大利的恶意垃圾邮件活动都有所减少。主要恶意软件家族包括AgentTesla、FormBook、Remcos和VIPKeylogger。总共监测到59次活动,其中8次使用意大利语。峰值出现在3月3日全球和4日意大利。 接下来,我需要将这些信息浓缩成一句话,不超过100字。要确保包含时间范围、活动变化、恶意软件家族、监测数据和峰值情况。 可能会这样组织:TG Soft CRAM报告称,在2026年3月2日至8日期间,全球和意大利的恶意垃圾邮件活动有所减少。监测到59次活动,其中8次使用意大利语,峰值分别在3月3日和4日出现。 检查一下字数是否符合要求,并确保信息准确无误。 </think> TG Soft CRAM报告称,在2026年3月2日至8日期间,全球和意大利的恶意垃圾邮件活动有所减少。监测到59次活动,其中8次使用意大利语,峰值分别在3月3日和4日出现。 2026-3-2 10:18:52 Author: www.tgsoft.it(查看原文) 阅读量:10 收藏
Weekly report by the TG Soft CRAM, concerning Italian malspam campaigns.
Below are the details of the campaigns released during the week from 02 March 2026 to 08 March 2026.
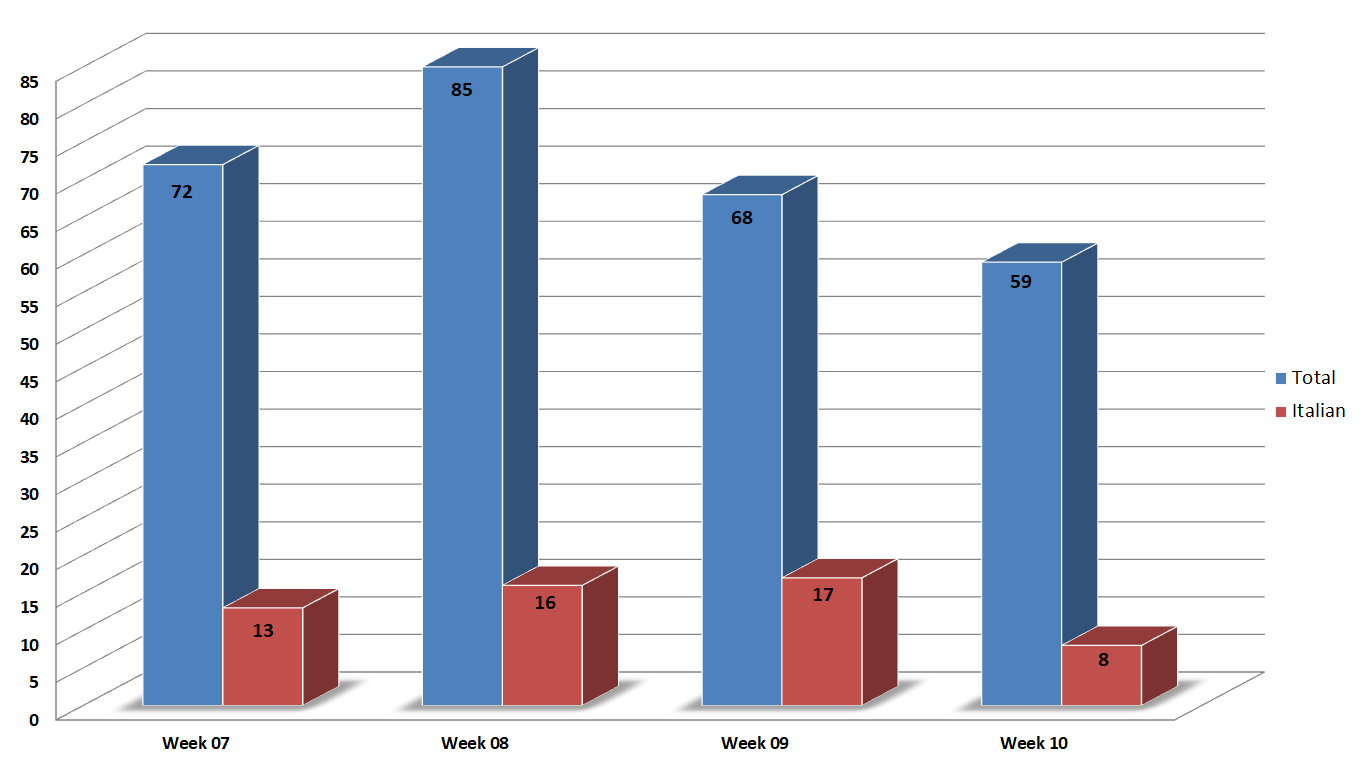
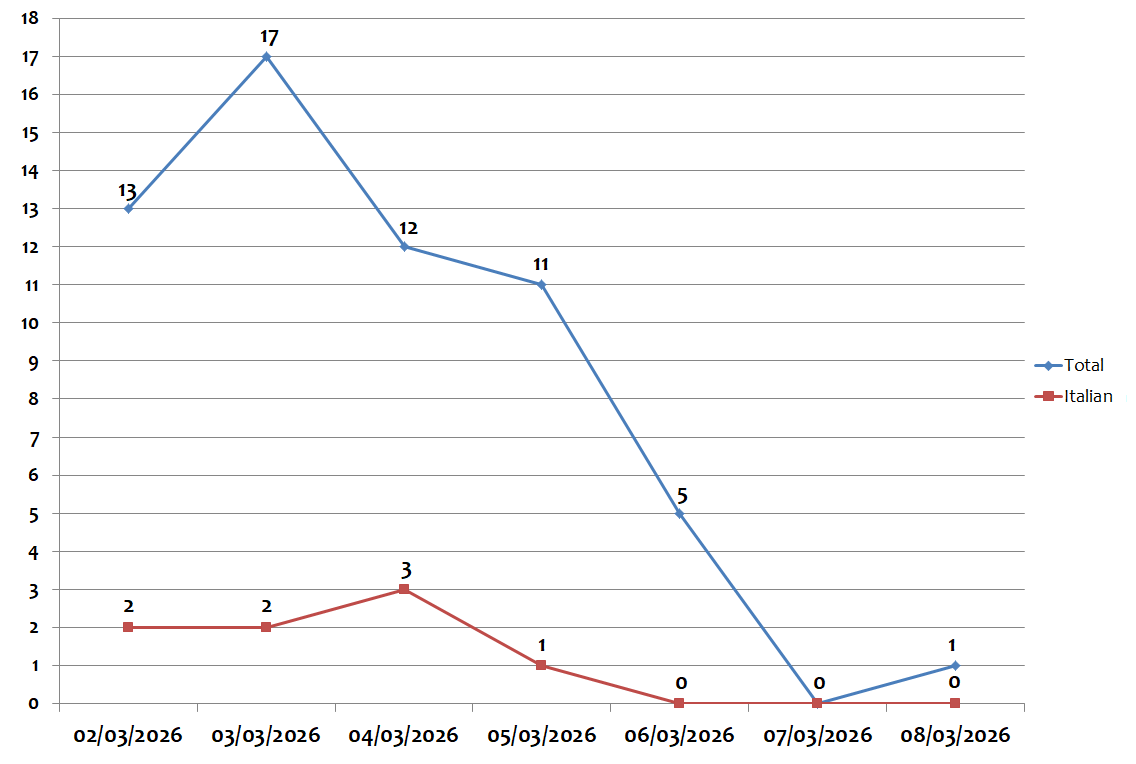
During the week monitored, global campaigns decreased compared to the previous week, campaigns in Italian also decreased.
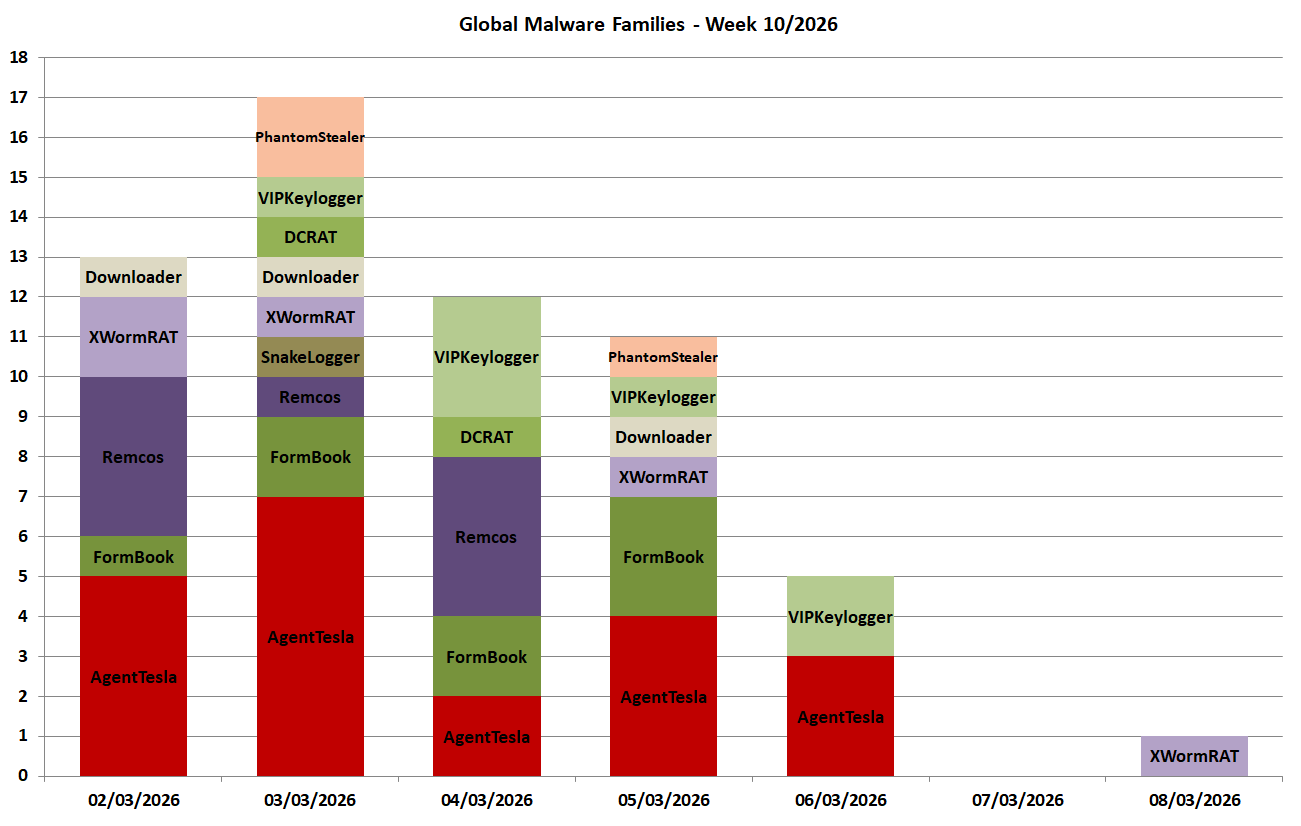
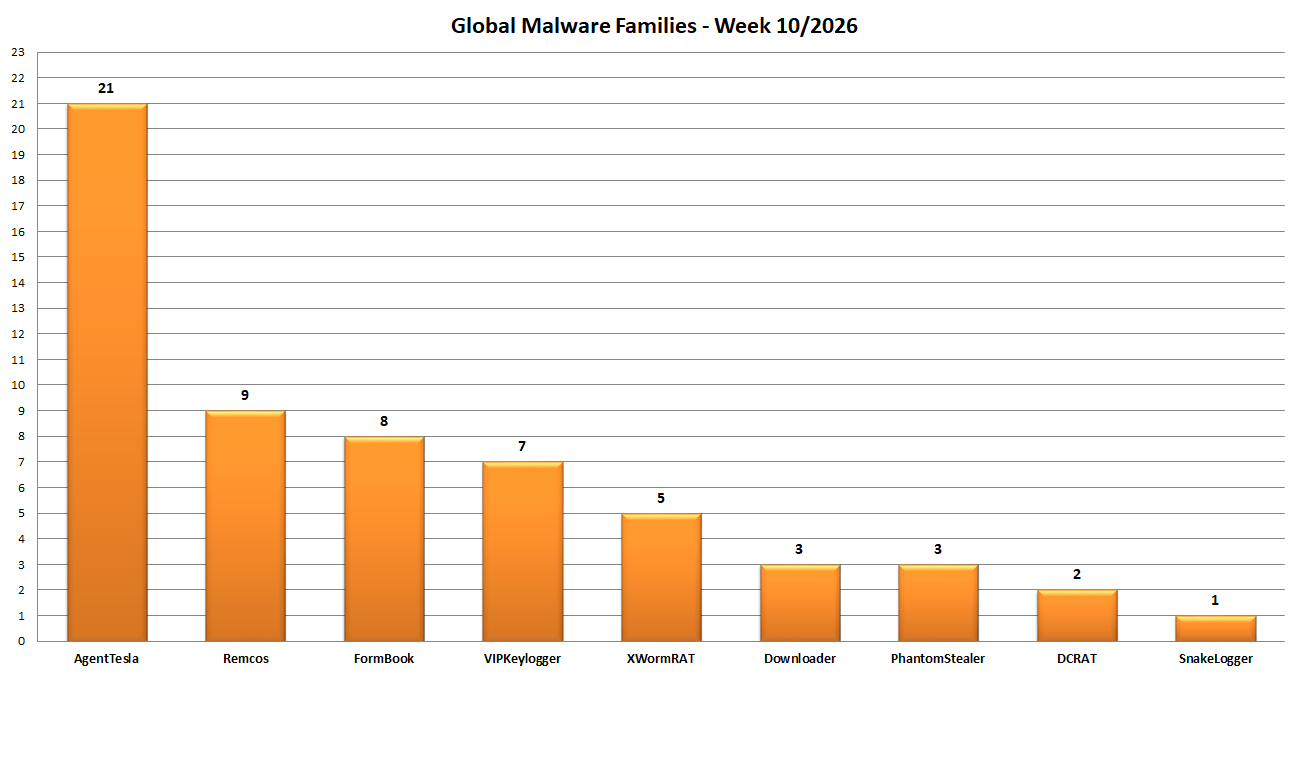
The week was characterized by Password Stealer of the Families: AgentTesla, FormBook, Remcos e VIPKeylogger.
The blue bar shows the total number of campaigns monitored in Italy in each week, while the red bar concerns campaigns in Italian (and targeting Italy).
We monitored 59 campaigns during the week, 8 of which used Italian as their language.
In order to understand how the various weeks are divided, below is a small table showing the breakdown of the considered period:
| Week | from | to |
| Week_07 | 09/02 | 15/02 |
| Week_08 | 16/02 | 22/02 |
| Week_09 | 23/02 | 01/03 |
| Week_10 | 02/03 | 08/03 |
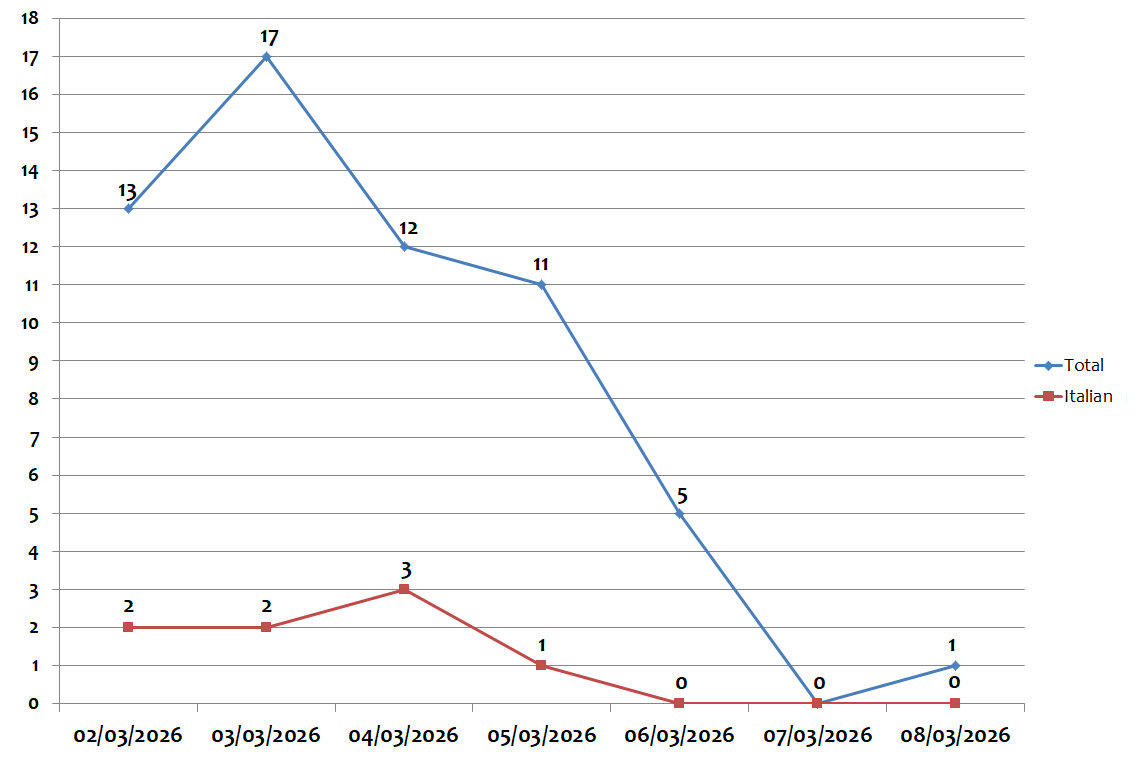
During the week, the peak in global campaigns was recorded on Tuesday 03 March, with 17 different campaigns per day. The peak in campaigns in Italian was recorded on Wednesday 04 March, with 3 different campaigns per day, as shown in the graph below:
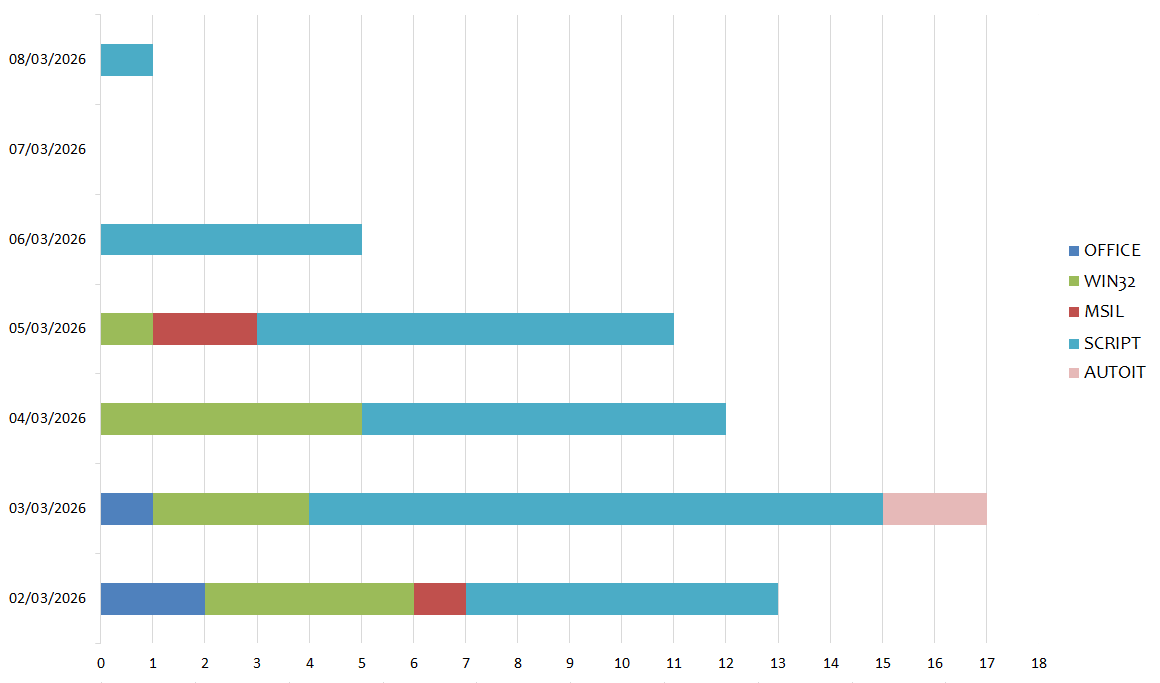
In the following chart we see the malware families spread globally for each day of the week:
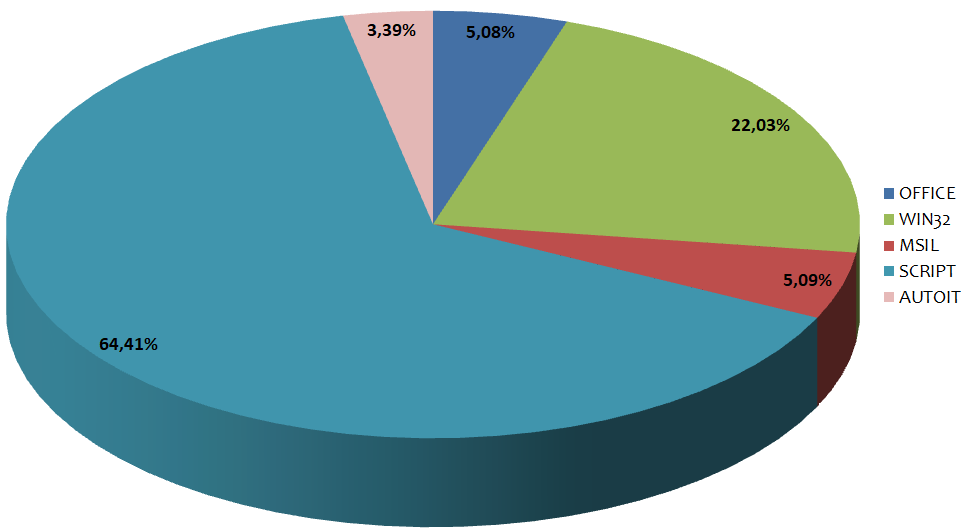
Instead in this graph we see the distribution based on malware family. In the past week 9 different families were detected:
The top-ranking samples this week are Script files accounting for 64,41%.
WIN32 executable files files follow in second place with 22,03%.
As for third place, we find MSIL files with 5,09%.
In the chart below we can see the various types of language used to develop malware:
In the following graph we see the distribution of the various types of languages divided by day:
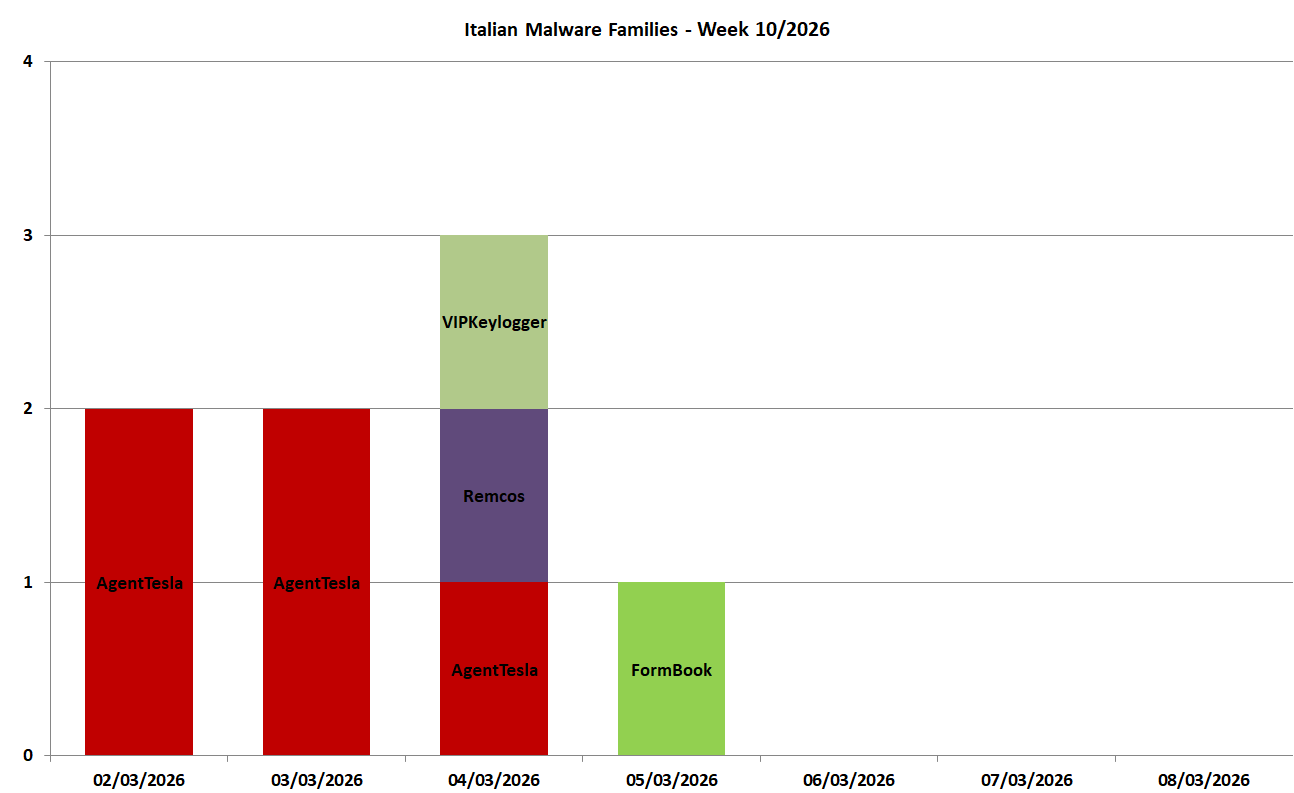
In this graph we can see the malware families spread during the week with target Italy (in Italian) and composed of 4 families:
The campaigns in Italian analyzed by the TG Soft C.R.A.M. were grouped according to macro categories, obtained from the subject of the email message used for malware distribution (malspam). Below we see the subjects used in the various campaigns divided by day and type of malware.
02/03/2026
AgentTesla - spread through two campaigns themed "Orders".
03/02/2026
AgentTesla - spread through two campaigns themed "Orders" and "Requests".
04/02/2026
AgentTesla - spread through a campaign themed "Bank Transfers".
Remcos - spread through a campaign themed "Bank Transfers".
VIPKeylogger - spread through a campaign themed "Others".
05/02/2026
FormBook - spread through a campaign themed "Payments".
Check out the Febraury/March campaigns
We invite you to check out the Febraury and March 2026 reports, to stay up-to-date on the malspam campaigns circulating in Italy:
Any information published on our site may be used and published on other websites, blogs, forums, facebook and/or in any other form both in paper and electronic form as long as the source is always and in any case cited explicitly “Source: CRAM by TG Soft www.tgsoft.it” with a clickable link to the original information and / or web page from which textual content, ideas and / or images have been extrapolated.
It will be appreciated in case of use of the information of C.R.A.M. by TG Soft www.tgsoft.it in the report of summary articles the following acknowledgment/thanks “Thanks to Anti-Malware Research Center C.R.A.M. by TG Soft of which we point out the direct link to the original information: [direct clickable link]”
如有侵权请联系:admin#unsafe.sh