好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得通读全文,抓住主要信息。 文章讲的是荷兰情报机构披露俄罗斯政府黑客针对Signal和WhatsApp用户的攻击行动。目标包括政府、军方官员和记者。攻击手段主要是钓鱼和社会工程学,而非恶意软件。比如,伪装成客服发送警告信息,诱骗用户提供验证码和PIN码,从而接管账户。 在Signal中,用户可能重新注册后恢复聊天记录,但可能被锁定。而WhatsApp则利用“关联设备”功能,可能读取旧消息。两家公司都建议用户不要分享验证信息。 接下来,我需要把这些要点浓缩成一段话,不超过100字。要确保涵盖攻击者、目标、手段以及后果。 最后检查一下字数和流畅度,确保信息准确且简洁。 </think> 荷兰情报机构披露俄罗斯政府黑客针对Signal和WhatsApp用户的全球性攻击行动,目标包括政府、军方官员及记者。黑客通过钓鱼和社会工程学手段获取验证码及PIN码以接管账户,并利用关联设备功能读取旧消息。两家公司均建议用户勿分享验证信息。 2026-3-9 16:33:32 Author: techcrunch.com(查看原文) 阅读量:13 收藏
Russian government hackers are targeting Signal and WhatsApp users, particularly government and military officials, as well as journalists all over the world, Dutch intelligence said on Monday.
The Netherlands’ Defence Intelligence and Security Service (MIVD) and the General Intelligence and Security Service (AIVD) published details about a “large-scale global” hacking campaign against Signal and WhatsApp users. The two agencies accused “Russian state actors” of using phishing and social engineering techniques — rather than malware — to take over accounts on the two messaging apps.
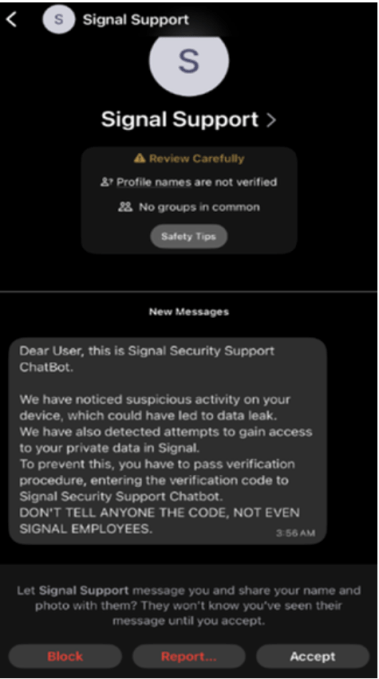
In the case of Signal, the hackers are masquerading as the app’s support team and messaging targets directly with warnings of suspicious activity, “a possible data leak,” or of attempts to access the target’s private data. If the target falls for it, the hackers ask for a verification code sent via SMS — the hackers themselves request this code from Signal — as well as the targets’ PIN code.
Contact Us
Do you have more information about this hacking campaign, or other campaigns targeting Signal and WhatsApp? From a non-work device, you can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, or via Telegram and Keybase @lorenzofb, or email.
The hackers then use the verification and PIN codes to register a new device with a new phone number, impersonate the target, and potentially access their contacts, according to the report. Also, the target gets locked out of their account, but can re-register their number.
“Because Signal stores the chat history locally on the phone, a victim can regain access to that history after re‑registering. As a result, the victim may assume that nothing is wrong. The Dutch services want to stress that this assumption could be incorrect,” the report reads.
Signal does not provide support directly through the app. And it’s important to note that, generally speaking, when a user adds a new device to their Signal account, the new device does not have access to previous messages.
Signal did not respond to a request for comment, but posted a thread on social media sharing advice for users on how to protect themselves, including advising against ever sharing the SMS verification code and PIN.

Hackers are also trying to trick targets on both apps into scanning malicious QR codes or clicking on malicious links. “For example, an actor may send a QR code or link to a victim to add them to a chat group, but this QR code or link actually links the actor’s device to the victim’s account,” the report explained.
In the case of WhatsApp, the hackers are abusing the “Linked devices” function, which allows users to access WhatsApp from a secondary device such as a laptop or a tablet. If the hackers successfully trick their targets, — unlike with Signal — they can potentially read past messages. And sometimes, the victim may not realize that they have granted access to the hackers’ given that they don’t get logged out of their account.
Meta’s spokesperson Zade Alsawah said that WhatsApp suggests users to never share their six-digit code with anyone, and pointed to a Help Center page to help users recognize suspicious messages, and a page about the Linked Devices feature.
The Dutch Ministry of Interior and Ministry of Defense did not respond to a request for more information about the hacking campaign.
The Russian embassy in Washington D.C. did not respond to a request for comment.
Some of the techniques highlighted by the Dutch intelligence services in this report have been known to be used by Russian government hackers in the context of the war against Ukraine.
Lorenzo Franceschi-Bicchierai is a Senior Writer at TechCrunch, where he covers hacking, cybersecurity, surveillance, and privacy.
You can contact or verify outreach from Lorenzo by emailing [email protected], via encrypted message at +1 917 257 1382 on Signal, and @lorenzofb on Keybase/Telegram.
如有侵权请联系:admin#unsafe.sh