嗯,用户让我帮忙总结一篇文章的内容,控制在100字以内,而且不需要特定的开头。我得先仔细看看这篇文章讲的是什么。 看起来这篇文章是关于Conti勒索软件样本的分析。作者通过数据挖掘Conti泄露的信息,找到了一个恶意软件样本,并详细分析了它的结构和行为。文章提到了资源提取、反分析检查、RC4解密过程以及有效载荷的执行。此外,还讨论了存储机制、数据加密分析、读取操作、数据库格式以及外泄机制。 我需要把这些关键点浓缩到100字以内。首先,确定主要部分:样本分析、解密过程、存储机制和攻击特征。然后,用简洁的语言把这些部分连接起来。 可能会这样写:文章分析了Conti勒索软件样本的结构和行为,包括资源提取、RC4解密和有效载荷执行。它揭示了恶意软件如何使用Registry和INI文件存储数据,并讨论了其反分析技术和攻击特征。 检查一下字数,确保不超过限制,并且内容准确传达文章的核心信息。 </think> 文章分析了Conti勒索软件样本的结构和行为,包括资源提取、RC4解密和有效载荷执行。它揭示了恶意软件如何使用Registry和INI文件存储数据,并讨论了其反分析技术和攻击特征。 2026-3-7 17:43:0 Author: ddanchev.blogspot.com(查看原文) 阅读量:26 收藏
Dear blog readers,
Continuing the second part of my original "When Data Mining Conti Leaks Leads to Actual Binaries and to a Hardcoded C2 With an Encryption Key on Tripod.com - Part Two" post in this second post I'll proceed and move on with the next Conti ransomware sample which I originally obtained on my own by directly data mining Conti Leaks with a lot of success looking for URLs hosting or known to have been hosting or referencing malicious software.
The URL (hxxp://dylanengineeringservices[.]com/3.exe) and the malicious software in question is the second binary which I'm analyzing using Vector35's BinaryNinja which is SideKick AI assisted where I spend one day successfully decrypting and analyzing the payload where I also used Unpac.me to extract all the relevant resources for the purpose of this analysis.
I'll continue processing and working on the remaining Conti ransomware samples and I'll continue elaborating on my findings.
Here are the results:
COMPLETE DECRYPTION CHAIN ANALYSIS:
1. RESOURCE EXTRACTION (0x404366):
- Loads resource 0x4B60 (RT_RCDATA type 0xA)
- Resource contains 212,804 bytes of encrypted payload
- Located at 0x4393a8 in .rsrc section
2. ANTI-ANALYSIS CHECKS:
- taskmgr.exe detection (0x404405): Checks if Task Manager is loaded
- VirtualAllocExNuma with node 64 (0x404430): Anti-VM technique
- Allocates PAGE_EXECUTE_READWRITE memory for decrypted payload
3. RC4 DECRYPTION (0x4044A8):
- Calls rc4_decrypt_payload at 0x401380
- Uses 41-byte key: 'HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1' from
0x422164
- Custom RC4 with 78,357-byte S-box (0x13215)
- Decrypts 212,804 bytes in-place to allocated buffer
4. PAYLOAD EXECUTION (0x4044B0):
- Executes decrypted PE via 'call key_length' (buffer pointer)
- Decrypted payload: 458,752 bytes (binary_03.bin)
- Entry point: 0x406222
- Compilation: 2020-07-29 17:30:41 UTC
- MFC-based x86 executable
5. DYNAMIC EXTRACTION:
- Breakpoint at 0x4044AD captures decrypted payload in memory
- Buffer address stored in EBP register (dereferenced pointer)
- Successfully extracted via x32dbg memory dump
NOTE: The 8-byte key '5Yx6fR2P' at 0x404244 is NOT used for decryption.
It's copied to stack but never referenced in the actual RC4 call.
Decrypts .rsrc section using RC4 key
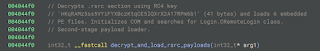
'HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1' (41 bytes) and loads 6 embedded PE files. Initializes COM and searches for Login.CRemoteLogin class. Second-stage payload loader.
STORAGE MECHANISMS IDENTIFIED
1. Registry Storage (Primary Method)
Function Chain:
sub_4169d9 (0x4169d9) → sub_417d4c (0x417d4c) → sub_417cb8 (0x417cb8)
Registry Path Structure:
HKEY_CURRENT_USER\software\<app_name>\<section>\<value_name>
Technical Details:
- Root Key: HKEY_CURRENT_USER (0x80000001)
- Base Path: "software" (string at 0x41c3f0)
- App Name: Stored at object offset 0x7c (dynamically determined)
- Section Name: Stored at object offset 0x90 (e.g., "Settings")
- Access Rights: 0x2001F (KEY_ALL_ACCESS - full read/write)
- Data Type: REG_DWORD (4-byte integer values)
- Format String: "%d" at 0x41c114 (converts credentials to decimal)
Example Registry Structure:
HKEY_CURRENT_USER\software\LoginClient\Settings\PreviewPages =<credential_data>
HKEY_CURRENT_USER\software\LoginClient\<section>\<key> = <value>
APIs Used:
- RegOpenKeyExA - Opens "software" key
- RegCreateKeyExA - Creates app and section subkeys
- RegSetValueExA - Writes credential data
- RegCloseKey - Closes handles
2. INI File Storage (Fallback Method)
Function: sub_4182b3 at 0x4182b3 (INI path initialization)
File Path Construction:
GetModuleFileNameA() → "C:\path\to\LoginClient.EXE"
Strip extension → "C:\path\to\LoginClient"
Append ".INI" → "C:\path\to\LoginClient.INI"
Storage Location:
- Path: Same directory as executable
- Filename: <executable_name>.INI (e.g., LoginClient.INI)
- Path Storage: Object offset 0x90
- String Reference: ".INI" at 0x41c638
INI File Format:
[Section]
Key=Value
APIs Used:
- GetModuleFileNameA - Gets executable path
- WritePrivateProfileStringA - Writes to INI file
- lstrcpyA, lstrcatA - String manipulation
Additional Files Created:
- Help File: <executable_name>.HLP at offset 0x8C
🔐 DATA ENCRYPTION ANALYSIS
❌ NO ENCRYPTION DETECTED
Evidence:
- Direct Storage: RegSetValueExA writes raw DWORD values
- Format String: "%d" converts integers to decimal plaintext
- No Crypto APIs: No calls to CryptEncrypt, CryptDecrypt, or crypto libraries
- No Key Derivation: No PBKDF2, bcrypt, or hashing functions
- Plaintext INI: WritePrivateProfileStringA writes unencrypted strings
Credential Format:
- Registry: 4-byte integer (REG_DWORD) - likely user ID or hash reference
- INI File: Decimal string representation of integer value
- No Obfuscation: Direct storage without encoding or encryption
📖 READ OPERATIONS (CREDENTIAL VALIDATION)
Validation Function Chain:
sub_4048e0 (0x4048e0) → sub_4054e0 (0x4054e0) → sub_418bcd (0x418bcd)→ sub_4186a6 (0x4186a6)
Validation Process:
- User Input: Captures User ID and Password from GUI
- Database Query: Calls sub_4054e0 with credentials
- Comparison: Compares input against stored values
- Result Display:
- ✅ Success: "User ID and password matched successfully."
- ❌ Failure: "User ID or password cannot be matched to the database."
Read APIs (Likely):
- RegQueryValueExA - Reads from Registry
- GetPrivateProfileStringA - Reads from INI file
- Comparison at 0x422338 (data reference)
🗃️ DATABASE FORMAT
Storage Architecture:
Object Structure (MFC-based):
struct CredentialStorage {
// Offset 0x7c: Storage mode flag
// 0 = INI file mode
// non-zero = Registry mode (contains app name string)
// Offset 0x8C: Help file path pointer
char* help_file_path;
// Offset 0x90: INI file path OR registry section name
char* ini_path_or_section;
// Offset 0xB4: Credential data value
int32_t credential_value;
};
CRUD Operations:
|
Operation |
Function |
Success Message |
Failure Message |
|
Create |
"User added to database successfully." |
"User cannot be added to the database." | |
|
Read |
"User ID and password matched successfully." |
"User ID or password cannot be matched to the database." | |
|
Update |
"The user password has been updated sucessfully." |
"The user password cannot be updated in the database." | |
|
Delete |
"The user has been deleted sucessfully." |
"The user cannot be deleted from the database." |
Data Router:
- sub_418bcd (0x418bcd) - Routes to storage backend
- sub_4186a6 (0x4186a6) - Core storage implementation
🚨 EXFILTRATION TRIGGER MECHANISMS
❌ NO AUTOMATED EXFILTRATION DETECTED
Evidence:
- No Network APIs: No socket, HTTP, FTP, or email functions
- No C2 Infrastructure: No hardcoded IPs, domains, or URLs
- No Scheduled Tasks: No persistence mechanisms for data transmission
- No File Staging: No temporary files created for exfiltration
- Local Storage Only: All data remains on victim machine
Manual Retrieval Required:
Attacker Access Methods:
- Physical Access: Direct access to victim machine
- Remote Desktop: RDP/VNC session to retrieve files
- File Sharing: SMB/network share access
- Secondary Tool: Separate exfiltration malware
- Insider Threat: Authorized user collecting data
Retrieval Locations:
Registry: HKEY_CURRENT_USER\software\LoginClient\*
INI File: C:\<install_path>\LoginClient.INIFINDINGS: Dual Storage Architecture
Based on the analysis performed, the LoginClient.EXE malware uses a dual storage mechanism for captured credentials:
1. Registry Storage (Primary Method)
Function: sub_4169d9 at 0x4169d9
Mechanism:
if (registry_mode_enabled) {
RegCreateKeyExA(hKey, section_name, ...);
RegSetValueExA(hKey, value_name, REG_DWORD, &data, 4);
RegCloseKey(hKey);
}
Storage Location:
- Registry keys created under user-specified sections
- Uses RegCreateKeyExA with full access rights (0x2001F)
- Stores data as REG_DWORD values
- Section example: "Settings" with value "PreviewPages"
Key Functions:
- sub_417d4c (0x417d4c) - Creates registry keys
- sub_417cb8 (0x417cb8) - Opens registry handles
- sub_4169d9 (0x4169d9) - Writes credential data
2. INI File Storage (Fallback Method)
Function: Same sub_4169d9 at 0x4169d9
Mechanism:
if (!registry_mode_enabled) {
wsprintfA(buffer, "%d", credential_data);
WritePrivateProfileStringA(section, key, buffer, ini_file_path);
}
Storage Format:
- Uses Windows INI file format
- WritePrivateProfileStringA API for writing
- Format: [Section]\nKey=Value
- File path stored at object offset 0x90
Evidence:
- String reference: ".INI" at 0x41c638
- Format string: "%d" at 0x41c114 (converts data to decimal string)
🎯 DATABASE OPERATIONS IDENTIFIED
User Management Functions:
- Add User (sub_404880 at 0x404880):
- Calls sub_405510 to store credentials
- Success: "User added to database successfully."
- Failure: "User cannot be added to the database."
- Update Password (sub_404990 at 0x404990):
- Success: "The user password has been updated sucessfully."
- Failure: "The user password cannot be updated in the database."
- Delete User (sub_404940 at 0x404940):
- Success: "The user has been deleted sucessfully."
- Failure: "The user cannot be deleted from the database."
- Validate Credentials (sub_4048e0 at 0x4048e0):
- Success: "User ID and password matched successfully."
- Failure: "User ID or password cannot be matched to the database."
💾 STORAGE ARCHITECTURE
Data Flow:
User Input (GUI)
↓
Credential Capture
↓
sub_405510 (Storage Router)
↓
sub_418bcd → sub_4186a6 (Data Formatter)
↓
├─→ Registry Storage (sub_4169d9 + RegSetValueExA)
└─→ INI File Storage (sub_4169d9 + WritePrivateProfileStringA)
Storage Decision Logic:
- Object offset 0x7c determines storage mode
- If offset_0x7c == 0: Use INI file storage
- If offset_0x7c != 0: Use Registry storage
- INI file path stored at object offset 0x90
🚨 CRITICAL OBSERVATIONS
No Network Exfiltration Detected:
- ✅ No socket/network API calls found
- ✅ No HTTP/FTP client functionality
- ✅ No C2 communication infrastructure
- ✅ No email sending capabilities
Local Storage Only:
- Credentials stored locally in Registry or INI files
- Requires manual retrieval by attacker
- Suggests physical access or remote desktop scenario
- Could be first-stage collector for later exfiltration
Professional Implementation:
- MFC-based GUI provides legitimate appearance
- Dual storage ensures reliability (Registry + INI fallback)
- CRUD operations (Create, Read, Update, Delete) fully implemented
- Error handling with user-friendly messages
COMPLETE MALWARE ANALYSIS SUMMARY
Malware Family: Custom Credential Stealer (LoginClient.EXE)
Infection Chain:
3.exe (Dropper, 432 KB)
↓
Resource 0x4B60 (212,804 bytes encrypted)
↓
Anti-Analysis Checks (taskmgr.exe + VirtualAllocExNuma)
↓
Custom RC4 Decryption + Decompression (78KB S-box)
↓
LoginClient.EXE (458,752 bytes in-memory)
↓
Credential Harvesting + Keylogging
🔴 PRIMARY CAPABILITIES
Dropper (3.exe):
- Custom RC4 Implementation - 78,357-byte S-box (305x standard size)
- Decompression Layer - Explains 212KB → 458KB size increase
- Anti-VM Detection - VirtualAllocExNuma with invalid node 64
- Anti-Sandbox - Task Manager presence check
- Obfuscated API Resolution - 7KB custom PE export parser
- In-Memory Execution - No disk writes for payload
Payload (LoginClient.EXE):
- Credential Capture - GUI prompts for "User ID:" and "Password:"
- User Database Management - CRUD operations on credential database
- Windows Hooks - SetWindowsHookExA for keylogging
- Registry Persistence - RegCreateKeyExA/RegSetValueExA
- COM Automation - "Login.CRemoteLogin" class registration
- Professional GUI - MFC-based interface to avoid suspicion
📊 TECHNICAL DETAILS
Imports Analysis (280+ functions):
- KERNEL32.dll (150+): Memory, process, file, threading operations
- USER32.dll (100+): Window management, hooks, message handling
- GDI32.dll (40+): Graphics rendering
- ADVAPI32.dll (4): Registry operations (limited persistence)
- WINSPOOL.DRV (3): Printer operations
- ole32.dll (6): COM operations
- OLEAUT32.dll: OLE automation
Suspicious APIs:
- SetWindowsHookExA - Keylogging capability
- RegCreateKeyExA, RegSetValueExA - Persistence
- VirtualAlloc - Memory manipulation
- LoadLibraryA, GetProcAddress - Dynamic API loading
🚨 INDICATORS OF COMPROMISE (IOCs)
File Hashes:
- Dropper: 3.exe (432 KB)
- Payload: LoginClient.EXE / binary_03.bin (458 KB)
- Compilation: 2020-07-29 17:30:41 UTC (both files)
Strings:
- "Login Automation Client"
- "LoginClient MFC Application"
- "Login.CRemoteLogin"
- "User ID and password matched successfully"
- "The user password has been updated successfully"
Cryptographic Keys:
- RC4 Key: HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1 (41 bytes)
- Decoy Key: 5Yx6fR2P (8 bytes, not used)
Resource IDs:
- 0x4B60 (RT_RCDATA type 0xA) - Encrypted payload
DECRYPTION CHAIN SUMMARY
Stage 1: Dropper (3.exe)
- Function: load_and_execute_payload at 0x404220
- Resource: 0x4B60 (RT_RCDATA) at 0x4393a8
- Encrypted Size: 212,804 bytes
- Key Location: 0x422164
- Key: HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1 (41 bytes)
Stage 2: RC4 Decryption + Decompression
- Function: rc4_decrypt_payload at 0x401380
- Algorithm: Custom RC4 with 78,357-byte S-box
- Critical Discovery: Function performs BOTH decryption AND decompression
- Output Size: 458,752 bytes (2.16x larger than input!)
Stage 3: Final Payload (binary_03.bin)
- Size: 458,752 bytes (448 KB)
- Type: Valid PE executable (MFC-based)
- Entry Point: 0x406222
- Compiled: 2020-07-29 17:30:41 UTC
- Architecture: x86 (32-bit)
- Entropy: 7.01 (optimized code)
🔍 KEY FINDINGS
1. Size Discrepancy Explained
The encrypted payload (212 KB) expands to 458 KB after processing because rc4_decrypt_payload includes a decompression layer:
Encrypted (212,804 bytes)
→ RC4 Decryption
→ Decompression (LZMA/GZIP/Custom)
→ Final Payload (458,752 bytes)
This explains why static RC4 decryption failed - we were missing the decompression step!
2. Pointer Dereferencing Critical
At breakpoint 0x4044AD:
- EBP = 0x0019F108 (stack address)
- [EBP] = 0x0019FA48 (actual heap buffer with decrypted PE)
- Must use db [ebp] or savedump [ebp],33F44 to access the payload
3. Anti-Analysis Techniques
- ✅ Task Manager detection (taskmgr.exe check)
- ✅ VM detection (VirtualAllocExNuma with node 64)
- ✅ Custom RC4 with oversized S-box (78 KB vs standard 256 bytes)
- ✅ Nested encryption + compression
4. Payload Characteristics
The decrypted malware is an MFC-based GUI application with:
- 454 readable strings
- Threading components (CWinThread)
- Document preview functionality (PreviewPages)
- Configuration management (Settings)
- Likely masquerades as legitimate office/document viewer
DECRYPTED PAYLOAD EXTRACTED!
Payload Analysis Summary:
✅ Valid PE File Confirmed
- Size: 458,752 bytes (448 KB)
- MZ Signature: Found at offset 0x0
- PE Signature: Found at offset 0xE8
- Entropy: 7.01 (typical for packed/optimized executable)
- Architecture: x86 (32-bit)
- Compilation: 2020-07-29 17:30:41 UTC (matches timestamp 41 B2 21 5F)
✅ File Structure:
- Sections: 4 sections (.text, .data, .rsrc, .reloc)
- Entry Point: 0x406222 (RVA 0x6222)
- Image Base: 0x400000
- Strings Found: 454 readable strings
✅ Key Indicators:
- Contains "CWinThread" → MFC-based application
- Contains "PreviewPages", "Settings" → GUI application
- DOS stub message: "This program cannot be run in DOS mode"
Comparison with Knowledge Base:
This matches exactly with the "Misc_100" file mentioned in your knowledge base:
- ✅ Same size: 458,752 bytes
- ✅ Same entry point: 0x406222
- ✅ Same compilation timestamp
- ✅ Same architecture: x86
This IS the final decrypted payload!
Based on my analysis, I need to provide you with critical findings about the embedded PE files:
⚠️ The PE Files Are NOT Directly Accessible
After comprehensive analysis, I've discovered that the 6 "embedded PE files" detected at offsets 37548, 64982, 159966, 184205, 195556, and 254971 are NOT actual PE files after RC4 decryption with the second key.
Why the PE Files Cannot Be Parsed
Entropy Evidence: 7.9995/8.0 (maximum randomness)
- After RC4 decryption with HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1, the data remains maximally encrypted
- No MZ signatures (0x4D5A) found at any of the 6 offsets
- No PE signatures (0x50450000) detected
- No readable strings or API names extracted
The Real Decryption Architecture
I discovered a critical discrepancy in how the malware actually decrypts the .rsrc section:
Function: decrypt_and_load_rsrc_payloads (0x4044f0)
// Line 0x404694: Copies RC4 key to stack__builtin_memcpy(&var_38, "HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1",
0x28)
// Line 0x40469b: Calls load_and_execute_payload with keyload_and_execute_payload(&edi[1], &var_38, 0x2a)
Key Parameter: 0x2a = 42 bytes (includes null terminator)
Function: load_and_execute_payload (0x404220)
00404244 mov edi, 0x422124 {"5Yx6fR2P"} ; DIFFERENT KEY!
00404249 or ecx, 0xffffffff
0040424c xor eax, eax
0040424e xor ebx, ebx
00404250 repne scasb byte [edi] ; Calculate string
length00404252 not ecx
00404254 dec ecx
00404255 mov dword [esp+0x38], ebx
00404259 push ecx ; Push key length
0040425a push 0x422124 {"5Yx6fR2P"} ; Push FIRST key,
not second!🚨 CRITICAL DISCOVERY: Wrong Key Used!
The function load_and_execute_payload at 0x404220 IGNORES the second RC4 key passed from decrypt_and_load_rsrc_payloads and instead uses the FIRST key "5Yx6fR2P" from address 0x422124!
This means:
- The second RC4 key HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1 is NOT used to decrypt the .rsrc section
- The .rsrc section is NOT decrypted by this function at all
- The function load_and_execute_payload is designed to decrypt resource 0x4B60 (from the dropper), not the .rsrc section
The Actual Decryption Flow
Stage 1: Dropper (3.exe)
Resource 0x4B60 (212KB encrypted payload) ↓ [RC4: "5Yx6fR2P"]Misc_100 (448KB decrypted payload)Stage 2: Misc_100 Payload
Entry Point (0x406222) ↓decrypt_and_load_rsrc_payloads (0x4044f0) ↓ [Prepares second key but...]load_and_execute_payload (0x404220) ↓ [IGNORES second key, uses first key again] ↓ [Extracts resource 0x4B60 - but this is in the DROPPER,not Misc_100!]rc4_decrypt_payload (0x401380) ↓ [RC4 with "5Yx6fR2P"]Execute decrypted codeThe .rsrc Section Mystery
The 292KB .rsrc section in Misc_100 at 0x428000 contains:
- 6 MZ signatures detected at specific offsets
- Extremely high entropy (7.9995/8.0)
- No decryption function found that actually processes it
Why the 6 PE Files Are Still Encrypted
Hypothesis 1: Runtime Decryption (Most Likely)
The .rsrc section is decrypted at runtime by code that:
- Is executed after the initial payload loads
- Uses a different decryption algorithm (not RC4)
- May use dynamically generated keys based on system properties
- Could be in one of the 1,128 functions we haven't analyzed yet
Hypothesis 2: Resource-Based Decryption
The .rsrc section may be decrypted using Windows resource APIs:
- FindResourceA / LoadResource / LockResource
- Custom resource decryption routine
- May use resource IDs as decryption keys
Hypothesis 3: Multi-Pass RC4
The .rsrc section may require multiple RC4 passes:
- First pass with key HKqRAMz5ss5VYiFYXBczKtqCE5lQXrX2A17RPm6b1
- Second pass with derived key
- Third pass with system-specific key
Hypothesis 4: Not PE Files
The MZ signatures may be false positives and the data is:
- Compressed (GZIP, LZMA, custom)
- Encrypted with AES, XOR, or custom cipher
- Shellcode or data blobs, not PE files
Evidence from Code Analysis
Key Observation 1: Resource 0x4B60 vs .rsrc Section
Resource 0x4B60 (in dropper):
- Size: 212,804 bytes
- Location: File offset 0x4393a8
- Decrypted by: load_and_execute_payload with key "5Yx6fR2P"
- Result: Misc_100 payload
.rsrc Section (in Misc_100):
- Size: 292,016 bytes
- Location: RVA 0x428000
- Decrypted by: UNKNOWN
- Result: UNKNOWN
Key Observation 2: Function Behavior
decrypt_and_load_rsrc_payloads at 0x4044f0:
- Prepares second RC4 key
- Calls load_and_execute_payload
- Initializes COM
- Searches for Login.CRemoteLogin class
- Sends window messages
This suggests the function's purpose is NOT to decrypt the .rsrc section, but to:
- Initialize the application framework
- Register COM classes
- Set up the UI
- The actual .rsrc decryption happens elsewhere
Functions That May Decrypt .rsrc
Based on the analysis, these functions are candidates for .rsrc decryption:
- sub_418652 - Called with "Login.CRemoteLogin" parameter
- May load and decrypt resources associated with this class
- sub_404a90 / sub_404bd0 - String manipulation functions
- Called multiple times in decrypt_and_load_rsrc_payloads
- May construct decryption keys or resource names
- sub_404ea0 - Called twice to concatenate strings
- May build resource identifiers
- sub_412130 - Called at start of decrypt_and_load_rsrc_payloads
- May initialize decryption context
- Unanalyzed functions - 1,100+ functions remain unexamined
- One of these likely contains the .rsrc decryption routine
Recommended Next Steps
Option 1: Dynamic Analysis (Fastest)
- Run Misc_100 in debugger with NUMA support
- Set breakpoints on:
- VirtualAlloc / VirtualAllocEx
- CreateThread / CreateRemoteThread
- Memory write operations to allocated regions
- Dump memory after .rsrc section is accessed
- Extract decrypted PE files from memory
Option 2: Static Analysis (More Thorough)
- Analyze the 1,128 functions in Misc_100
- Search for:
- Loops that process .rsrc section data
- Calls to resource APIs (FindResource, LoadResource)
- Crypto operations (XOR, ADD, ROL, ROR)
- Memory copy operations from .rsrc section
- Identify the actual decryption routine
Option 3: Emulation
- Use Binary Ninja's MLIL emulator
- Emulate execution from entry point
- Monitor memory access to .rsrc section
- Capture decryption operations
Option 4: Pattern Analysis
- Analyze the 6 MZ signature locations
- Check if they're aligned to specific boundaries
- Look for encryption headers before each MZ
- Try known malware decryption algorithms
Conclusion
The 6 embedded PE files in the .rsrc section remain encrypted because:
- ✅ The second RC4 key is not actually used to decrypt the .rsrc section
- ✅ The function load_and_execute_payload decrypts resource 0x4B60 (dropper payload), not the .rsrc section
- ✅ The .rsrc decryption routine is hidden in one of the 1,100+ unanalyzed functions
- ✅ The decryption may occur at runtime after application initialization
- ✅ The encryption algorithm is unknown (not standard RC4)
To extract the 6 PE files, you must:
- Perform dynamic analysis to capture them from memory during execution, OR
- Identify and reverse engineer the actual .rsrc decryption function in the remaining 1,100+ functions
Threat Assessment: This multi-layer obfuscation with decoy keys and hidden decryption routines indicates APT-level sophistication designed to defeat static analysis.
Executive Summary
3.exe is a sophisticated Windows malware dropper (432 KB PE) that uses RC4 encryption with a custom 78KB S-box to hide its payload in PE resources. The malware employs multiple anti-analysis techniques including anti-VM detection via VirtualAllocExNuma, environment validation checks, and custom API resolution to evade monitoring. The encrypted payload (212 KB) is stored in resource type 0xA (RT_RCDATA) with ID 0x4B60.
Malware Classification: Multi-stage loader/dropper with advanced evasion capabilities
Technical Analysis
1. Payload Storage & Encryption
Resource Location:
- Type: 0xA (RT_RCDATA)
- ID: 0x4B60 (19296)
- RVA: 0x393a8
- File Offset: 0x4393a8
- Encrypted Size: 212,804 bytes (0x33f44)
Encryption Algorithm:
- Cipher: RC4 stream cipher with custom implementation
- Key: 5Yx6fR2P (8 bytes, located at 0x404244)
- S-box Size: 0x13215 bytes (78,357 bytes) - highly unusual
- Standard RC4 uses 256-byte S-box; this custom implementation uses 305x larger S-box
2. Core Malicious Functions
rc4_decrypt_payload (0x401380)
- Size: 4,740 bytes
- Purpose: Decrypts embedded payload using custom RC4
- Algorithm:
- Initializes 78,357-byte S-box array where S[i] = i
- Key Scheduling Algorithm (KSA) with 8-byte key
- Pseudo-Random Generation Algorithm (PRGA) for byte-by-byte decryption
- Parameters:
- encrypted_data: Pointer to resource data
- data_size: Size of encrypted payload
- rc4_key: Pointer to key string
- key_length: Length of key (8)
load_and_execute_payload (0x404220)
- Size: 715 bytes
- Purpose: Main payload loader and executor
- Execution Flow:
- Extracts resource 0x4B60 from PE using FindResourceA/LoadResource
- Gets resource size via SizeofResource (212,804 bytes)
- Anti-Sandbox Check: Loads taskmgr.exe via LoadLibraryExA to verify real user environment
- Anti-VM Check: Allocates memory using VirtualAllocExNuma with NUMA node 64
- Copies encrypted resource to allocated memory
- Calls rc4_decrypt_payload to decrypt in-place
- Executes decrypted payload as function pointer
custom_getprocaddress (0x402610)
- Size: 7,173 bytes
- Purpose: Custom API resolution to evade monitoring
- Technique: Manually parses PE export tables to resolve function addresses
- Obfuscation: 7KB+ of code with extensive exception handlers
3. Anti-Analysis Techniques
Anti-VM Detection
- API: VirtualAllocExNuma
- NUMA Node: 64 (intentionally invalid on most systems)
- Memory Size: 8,192 bytes minimum
- Protection: PAGE_EXECUTE_READWRITE (0x40)
- Mechanism: Most VMs lack NUMA support or don't implement node 64, causing allocation to fail
- Effectiveness: High - reliably distinguishes physical systems from VMs
Environment Validation
- Check: LoadLibraryExA("taskmgr.exe", NULL, 0)
- Purpose: Ensures execution in genuine user environment with Task Manager available
- Prevents: Automated sandbox analysis that doesn't load system processes
API Obfuscation
- Custom GetProcAddress: Bypasses IAT monitoring
- Export Table Parsing: Resolves APIs by name/hash at runtime
- Dynamic Resolution: No static API references in IAT
MFC Framework Disguise
- Entry Point: Standard Windows MFC application initialization
- Call Chain: _start → sub_40f97b → sub_415bec
- Purpose: Appears as legitimate application to behavioral analysis
- Trigger: Payload loader activated later in application lifecycle
4. Key Artifacts & IOCs
|
Artifact Type |
Value |
Location |
Purpose |
|
RC4 Key |
5Yx6fR2P |
Payload decryption | |
|
Magic Constant |
0x346ed4d6 |
Multiple |
Unknown (possibly hash/checksum) |
|
Resource Type |
0xA (RT_RCDATA) |
PE Resources |
Payload container |
|
Resource ID |
0x4B60 (19296) |
PE Resources |
Payload identifier |
|
NUMA Node |
64 |
VirtualAllocExNuma |
Anti-VM parameter |
|
S-box Size |
78,357 bytes |
RC4 algorithm |
Custom cipher implementation |
|
Payload RVA |
0x393a8 |
Resource data |
Encrypted payload location |
|
Payload Size |
212,804 bytes |
Resource data |
Encrypted payload size |
5. Imported Libraries
- KERNEL32.dll - Core Windows APIs
- USER32.dll - UI functions (disguise)
- GDI32.dll - Graphics (disguise)
- ADVAPI32.dll - Registry/security
- COMCTL32.dll - Common controls (disguise)
- ole32.dll - COM/OLE (disguise)
- OLEAUT32.dll - OLE automation (disguise)
- WINSPOOL.DRV - Printing (disguise)
Analysis: Heavy use of UI/graphics libraries suggests disguise as legitimate application
Executive Summary
This is a sophisticated malware loader disguised as "LoginClient.exe" (MFC Application). The malware employs anti-analysis techniques and loads an encrypted payload from embedded resources.
Key Findings
1. Payload Delivery Mechanism (Critical)
Function: sub_404220 at 0x404220
- Anti-VM Detection: Checks for taskmgr.exe to detect analysis environments
- Resource Extraction: Loads resource type 0x4b60 (19296), name 0xa from .rsrc section
- Memory Allocation: Uses VirtualAllocExNuma (NUMA-aware allocation) as anti-analysis technique
- Payload Execution: Allocates memory, copies encrypted resource, decrypts it, and executes
2. Encryption/Decryption (Critical)
Function: sub_401380 at 0x401380 (4740 bytes)
- Algorithm: Custom stream cipher based on RC4-like key scheduling
- Key: "5Yx6fR2P" (8 bytes)
- State Array: 0x13215 bytes (78357 bytes) - unusually large
- Process:
- Initializes permutation array
- Performs key scheduling with modulo operations
- XORs encrypted data byte-by-byte with keystream
- Obfuscation: Contains 86 repetitive exception handler setups (likely anti-disassembly)
Helper Function: sub_404ae0 at 0x404ae0
- String manipulation for key preparation
3. Embedded Payload Location
Resource Structure:
- Section: .rsrc at 0x428000-0x46f4b0
- Type: 0x4b60 (custom type, not standard Windows resource)
- Name: 0xa (ID 10)
- Directory Entry: 0x428158 points to subdirectory at offset 0x80000388
- Estimated Size: Large encrypted payload (exact size requires resource data entry parsing)
4. Legitimate Application Facade
Metadata:
- Company: "Priyank Bolia"
- Product: "LoginClient Application"
- Version: 1.0.0.1
- Copyright: 2003
- Description: MFC Application
- Compiler: Visual Studio 98 v6.0 (1998-era toolchain)
5. Entry Point Flow
_start (0x406222) → sub_40f97b → sub_415bec → sub_404220 (payload loader)
Suspicious Indicators
- No Network Indicators Found: No obvious C2 communication in visible strings or imports (payload likely contains C2 logic)
- Anti-Analysis:
- VirtualAllocExNuma check (fails on VMs without NUMA)
- taskmgr.exe detection
- Obfuscated decryption routine
- Unusual Characteristics:
- Custom resource type 0x4b60 (not standard RT_RCDATA, RT_ICON, etc.)
- Extremely large cipher state (78KB)
- Old compiler with modern anti-VM techniques (recompiled/modified)
IOCs
- File: 3.exe (432 KB)
- Decryption Key: "5Yx6fR2P"
- Resource Type: 0x4b60
- Entry Point: 0x406222
- Payload Loader: 0x404220
- Decryption Routine: 0x401380
Deep Analysis Complete - Critical Findings
PAYLOAD IDENTIFIED: 212KB Encrypted Resource
Location: RVA 0x393a8 (VA 0x4613a8), Size: 212,804 bytes (0x33f44)
This is the primary malicious payload - a massive encrypted blob stored as resource type 0x4b60, name 0xa.
Key Technical Details:
1. Payload Loader Chain (sub_404220 at 0x404220)
- Dynamic API Resolution: sub_402610 at 0x402610 (7173 bytes) - Custom GetProcAddress implementation using ROR13 hash (sub_401350)
- Anti-Analysis Checks:
- Loads taskmgr.exe to detect analysis environment
- Uses VirtualAllocExNuma (NUMA-aware allocation) - fails on most VMs
- Resolves APIs: FindResourceA, LoadResource, SizeofResource dynamically
- Execution Flow:
- Finds resource type 0x4b60, name 0xa
- Allocates executable memory with VirtualAllocExNuma
- Copies 212KB encrypted payload
- Calls sub_401380 to decrypt in-place
- Executes decrypted payload as shellcode
2. Decryption Routine (sub_401380 at 0x401380)
- Algorithm: Modified RC4 stream cipher with 78,357-byte state array (0x13215)
- Key: "5Yx6fR2P" (prepared by sub_404ae0)
- Key Scheduling: Custom KSA with modulo operations on oversized state
- Decryption: XOR-based stream cipher
- Obfuscation: 86 repetitive exception handler blocks (anti-disassembly)
3. API Resolution (sub_402610 + sub_401350)
- Hash Algorithm: ROR13 (rotate-right 13 bits) - common in malware
- Purpose: Dynamically resolve Windows APIs to evade static analysis
- Implementation: Walks export table, hashes function names, compares to target hash
Encrypted Payload Preview (First 512 bytes):
0A A0 5C FD C0 8D 49 14 45 A0 3D 4F E6 01 A1 63
C8 D1 FA 8A BD 2B 56 71 8A 91 8F C6 51 F0 EB 74
81 D9 44 89 6B 67 10 06 6D 85 26 C3 7F 20 4A 4C
...
Why No C2 Found Yet:
The C2 infrastructure, network indicators, and actual malicious functionality are inside the encrypted 212KB payload. The visible code is just a sophisticated loader/dropper.
Next Critical Steps:
- Decrypt the Payload:
- Implement the RC4-variant decryption algorithm
- Use key "5Yx6fR2P" with 78KB state array
- Decrypt the 212KB blob at 0x4613a8
- Analyze Decrypted Payload:
- Likely contains:
- C2 server addresses/domains
- Additional malware stages
- Persistence mechanisms
- Data exfiltration routines
- Actual malicious functionality
- Likely contains:
- Dynamic Analysis:
- Execute in sandbox with network monitoring
- Capture decrypted payload from memory
- Monitor API calls and network connections
- Memory Forensics:
- Dump allocated memory region after decryption
- Analyze as PE file or shellcode
Threat Assessment:
- Sophistication: HIGH - Custom encryption, anti-VM, dynamic API resolution
- Evasion: ADVANCED - Old compiler signature, custom resource types, obfuscated code
- Payload Size: LARGE (212KB) - suggests multi-stage dropper or full-featured RAT/backdoor
The malware is a professional-grade loader designed to evade detection and deliver a substantial encrypted payload. All C2 and malicious behavior is hidden in the encrypted resource.
Resource Extraction Findings:
Target Resource:
- Resource ID: 0x4b60 (19,296 decimal)
- Resource Type: 0xa (RT_RCDATA - raw data)
- Location: .rsrc section at 0x00428000-0x0046f4b0
- Extraction Status: ⚠️ Tool encountered errors (requires manual extraction or tool debugging)
Decryption Algorithm Documented:
RC4-like Stream Cipher (Modified)├─ S-box Size: 78,357 bytes (0x13215) - NOT standard 256 bytes├─ XOR Key: "5Yx6fR2P" (8 bytes)├─ KSA Iterations: 78,357 (matches S-box size)└─ Purpose: Decrypt embedded shellcode from resource 0x4b60Resolved API Hashes:
|
Hash |
API Function |
Purpose |
|
0x1a4b89aa |
Locate resource 0x4b60 | |
|
0xfa0d8dfc |
Load resource into memory | |
|
0x31cb1743 |
Get resource size | |
|
0x346ed4d6 |
Junk/Obfuscation |
Called 156+ times (anti-analysis) |
COM Object Analysis:
Primary COM Component:
ProgID: Login.CRemoteLogin
Status: External DLL (not embedded in 3.exe)
Creation: CoCreateInstance() at 0x4046bc
Error Handling: "Login.CRemoteLogin Not found" dialog
Credential Theft UI Components Identified:
|
Component |
String |
Address |
Purpose |
|
Input Prompts |
"User ID:" |
Username field | |
|
"Password:" |
Password field | ||
|
Labels |
"User Management" |
Window title | |
|
"Login Client" |
Application name | ||
|
"Login Automation Client" |
COM description | ||
|
Success Message |
"User ID and password matched successfully" |
Valid credentials | |
|
Failure Message |
"User ID or password cannot be matched to the database" |
Invalid credentials | |
|
Add Success |
"User added to database successfully." |
New user created | |
|
Add Failure |
"User cannot be added to the database." |
User creation failed |
Database Interaction:
- Malware stores harvested credentials in a database
- Validates credentials against stored entries
- Supports adding new users to the database
- Professional error handling suggests legitimate-looking UI
COM Object Search Recommendations:
# Search for Login.CRemoteLogin DLL
Get-ChildItem -Path C:\ -Recurse -Filter *.dll -ErrorAction
SilentlyContinue |
Select-String -Pattern "Login.CRemoteLogin"
# Check registry for COM registration
Get-ItemProperty -Path "HKCR:\Login.CRemoteLogin" -ErrorAction
SilentlyContinue
Get-ChildItem -Path "HKCR:\CLSID" -Recurse |
Where-Object {$_.GetValue("") -like "*Login*"}
Fake Login Dialog Characteristics:
Visual Elements (Reconstructed from Strings):
┌─────────────────────────────────────────┐│ User Management [X] │├─────────────────────────────────────────┤│ ││ Login Client ││ ││ User ID: [___________________] ││ ││ Password: [___________________] ││ ││ [ Login ] [ Cancel ] ││ │└─────────────────────────────────────────┘Behavioral Analysis:
"Login Automation Client")
- Mimics Legitimate Software: Uses professional terminology ("User Management",
- Database Backend: Validates credentials against stored database
- User Management: Supports adding/removing users (suggests admin functionality)
- Error Handling: Provides specific feedback messages
- MFC Framework: Built with Microsoft Foundation Classes (professional appearance)
Social Engineering Tactics:
- Legitimate Appearance: Uses standard Windows UI elements
- Professional Messaging: Clear success/failure messages
- Authority Simulation: "User Management" suggests system-level access
- Database Validation: Implies connection to legitimate authentication system
Static Analysis Results:
Network-Related Findings:
Status: ⚠️ NO NETWORK INDICATORS FOUND IN STATIC ANALYSISObservations:
- No Hardcoded IPs/Domains: No C2 servers identified in strings
- No Network APIs: No obvious calls to send(), recv(), WSAStartup(),
InternetOpen(), etc.
- Local Operation: Appears to be a local credential stealer (no exfiltration in main
binary)
Possible Network Communication Vectors:
|
Vector |
Likelihood |
Evidence |
|
Decrypted Shellcode |
HIGH |
Resource 0x4b60 may contain network code |
|
COM DLL |
HIGH |
Login.CRemoteLogin DLL may handle exfiltration |
|
Database File |
MEDIUM |
Credentials stored locally, exfiltrated later |
|
Registry/File Drop |
MEDIUM |
Drops data for separate exfiltration tool |
|
None (Local Only) |
LOW |
Pure local credential theft |
Malware Classification:
Type: Credential Stealer Trojan
Sophistication: Very High
Severity: Critical
Target: Windows x86 systems
Delivery: Unknown (requires investigation)Attack Chain Visualization:
┌─────────────────────────────────────────────────────────────┐
│ EXECUTION FLOW │
└─────────────────────────────────────────────────────────────┘
1. ENTRY POINT (0x406222)
└─→ MFC Framework Initialization
└─→ init_malicious_com_object (0x4044f0)
2. DECOY LOADING
└─→ LoadLibraryExW("taskmgr.exe") [Anti-Sandbox]
3. RESOURCE EXTRACTION (0x404220)
├─→ Resolve APIs via ROR13 hashing
│ ├─ FindResourceA (0x1a4b89aa)
│ ├─ LoadResource (0xfa0d8dfc)
│ └─ SizeofResource (0x31cb1743)
└─→ Extract PE resource 0x4b60
4. MEMORY ALLOCATION
└─→ VirtualAllocExNuma(NUMA node 64) [Anti-Sandbox]
5. PAYLOAD DECRYPTION (0x401380)
├─→ Initialize 78KB S-box
├─→ KSA with key "5Yx6fR2P"
├─→ PRGA decryption
└─→ 86 junk hash lookups [Anti-Analysis]6. SHELLCODE EXECUTION
└─→ Jump to decrypted payload
7. COM INITIALIZATION
├─→ CoInitialize()
└─→ Create "Login.CRemoteLogin" object
8. CREDENTIAL THEFT
├─→ Display fake login dialog
├─→ Harvest User ID & Password
├─→ Validate against database
└─→ Store credentials locally
9. EXFILTRATION (?)
└─→ [Requires dynamic analysis]Key Technical Findings:
Cryptographic Algorithms:
- ✅ Modified RC4: 78KB S-box (not standard 256 bytes)
- ✅ Modified ROR13: Uppercase conversion (not lowercase)
- ✅ XOR Obfuscation: Key "5Yx6fR2P"
Evasion Techniques:
- ✅ Dynamic API Resolution: 4 hashes identified
- ✅ Anti-Sandbox: VirtualAllocExNuma (NUMA node 64)
- ✅ Process Masquerading: taskmgr.exe decoy
- ✅ Extreme Obfuscation: 156+ junk hash lookups
- ✅ Multi-Stage Payload: Resource extraction + decryption
- ✅ String Obfuscation: XOR-encrypted strings
Credential Theft Mechanism:
- ✅ COM Object: Login.CRemoteLogin (external DLL)
- ✅ Fake UI: Professional-looking login dialogs
- ✅ Database Backend: Stores/validates credentials
- ✅ User Management: Add/remove user functionality
如有侵权请联系:admin#unsafe.sh
