
嗯,用户让我帮忙总结一下这篇文章的内容,控制在一百个字以内,而且不需要用“文章内容总结”之类的开头。首先,我需要仔细阅读这篇文章,理解它的主要观点和关键信息。 文章主要讲的是安全运营中心(SOC)面临的问题,包括每天处理大量安全警报、分析师数量不足以及由此导致的倦怠问题。然后,文章介绍了自主 SOC 平台如何通过 AI 技术来解决这些问题,提升分析师的工作效率和角色定位。 接下来,我需要提取这些关键点,并用简洁的语言表达出来。确保在100字以内涵盖主要信息:问题、解决方案、AI的作用以及分析师角色的变化。 可能会遇到的难点是如何在有限的字数内准确传达所有重要信息。可能需要多次精简语言,确保每个要点都清晰明了。 最后,检查一下是否符合用户的要求:中文、直接描述内容、不使用特定开头。确保总结准确且简洁。 </think> 文章探讨了安全运营中心(SOC)面临的挑战:每天处理数千条警报、分析师数量不足及倦怠问题。通过引入自主化AI平台(如Morpheus),可自动处理警报,减少人工负担,并使分析师专注于战略任务如威胁狩猎和检测工程。这不仅提升了效率和安全性,还改善了团队士气和 retention 率。 2026-3-5 23:16:31 Author: securityboulevard.com(查看原文) 阅读量:7 收藏
How autonomous triage turns security analysts from ticket processors into strategic operators
The Security Operations Center has a math problem. The average enterprise SOC receives over 4,400 alerts per day. Analysts can’t investigate 67% of them. And the global cybersecurity workforce is short 4.8 million people. Something has to give, and the adversaries aren’t volunteering.
For over a decade, SOC analysts have been the frontline of enterprise defense: manually triaging thousands of alerts per shift, correlating data across dozens of disconnected tools, and fighting a war against alert volume they were never staffed to win. The result is an industry defined by burnout. 71% of analysts report exhaustion. 64% are considering leaving within the year. Up to 95% of analyst time goes to investigating alerts that turn out to be false positives.
Autonomous SOC platforms are designed to fix this at the structural level.
The numbers tell the story
| Metric | Figure |
|---|---|
| Avg. daily alerts per SOC | 4,484 |
| Alerts never investigated | 67% |
| Global workforce shortage | 4.8M |
The mean time to investigate a single alert is about 70 minutes. Fully working through one day’s alert queue would take more than 61 working days. Security teams spend 27% of their operational hours handling false positives alone. When analysts can’t keep up, they do the rational thing: suppress detection rules to manage the load. That creates the exact blind spots adversaries exploit.
Enter the autonomous SOC
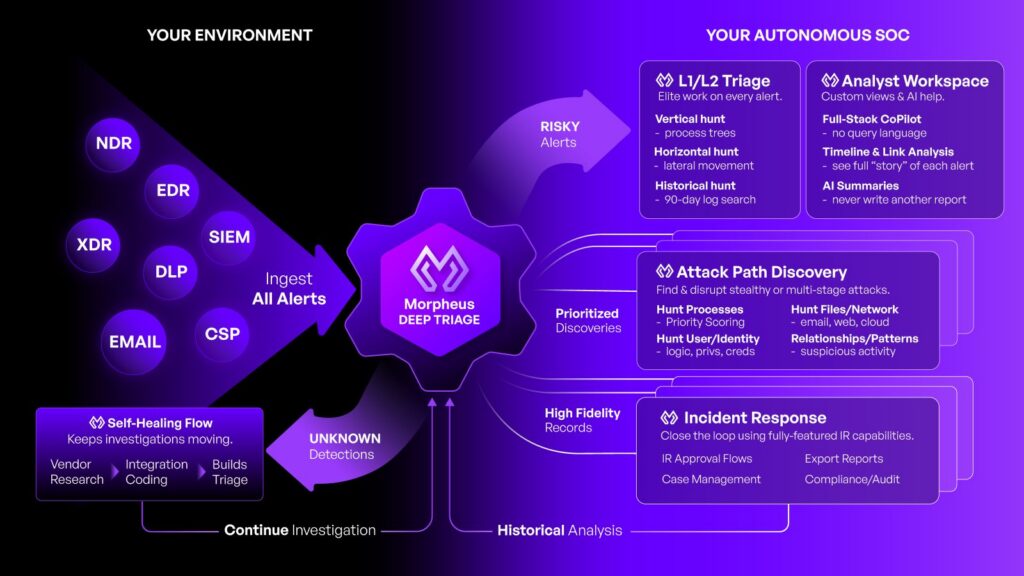
Autonomous triage platforms like Morpheus take a different approach. Rather than adding more analysts to an unscalable process, they use purpose-built AI to ingest, investigate, triage, and respond to security alerts at machine speed.
Morpheus was built by D3 Security over 24 months with a team of 60 specialists (red teamers, data scientists, AI engineers, experienced SOC analysts). The system is roughly 70–80% framework and guardrails, with only 20–30% comprising the LLM itself. That architecture prioritizes reliability and deterministic outcomes over raw generative capability. It is not a chatbot bolted onto a SOAR platform.
A large Master MSSP reported that after implementing Morpheus, their operation went from handling approximately 144,000 alerts to focusing on just 200 alerts per month requiring human analyst attention. Response times compressed from 30–60 minutes to 30 seconds–3 minutes.
Across deployments, organizations see an 80% improvement in Mean Time to Respond and a 99% reduction in time spent on false positives. The platform processes 100% of incoming alerts. No more silent dismissals. No more coverage gaps.
The analyst role is being elevated
The fear narrative around AI and jobs is familiar, but cross-industry research tells a more specific story. A 2025 SSRN analysis projects that while 85 million jobs globally will be displaced by AI automation, 97 million new roles will emerge. Those new roles require higher-order judgment, oversight, and domain expertise.
We see this playing out in other industries already. In manufacturing, autonomous inspection systems freed quality engineers for process optimization. In healthcare, AI diagnostics let physicians focus on complex cases and treatment planning. In financial services, automated fraud detection let analysts investigate sophisticated criminal networks rather than reviewing individual transactions.
The SOC is following the same trajectory. When Morpheus handles the triage, the analyst’s role changes in four concrete ways.
Analysts become AI auditors. They validate autonomous triage decisions, identify edge cases, and refine AI reasoning. This is a new competency that combines deep security knowledge with AI literacy.
Analysts become proactive threat hunters. With routine alerts handled autonomously, analysts dedicate sustained attention to hunting for indicators of compromise, analyzing adversary TTPs, and uncovering threats that automated detection might miss.
Analysts become detection engineers. They shift from following playbooks to writing them. They analyze patterns in AI-triaged data to author more precise detection logic, reduce false positive rates, and close coverage gaps.
Analysts become strategic advisors. Senior analysts contribute to security architecture, lead red team exercises, and translate technical risk into board-level language. These are activities that were perpetually deferred when every shift was consumed by queue management.
What you can do with 7,800 recovered hours
A ten-person SOC team where each analyst reclaims three hours per day from manual triage gets back 7,800 analyst-hours per year. That’s time redirected to work that actually reduces risk.
| Activity | Before | After autonomous SOC |
|---|---|---|
| Threat Hunting | Ad hoc, time permitting | Structured daily program |
| Detection Engineering | Reactive, post-incident | Continuous optimization |
| Red/Purple Team Exercises | Quarterly at best | Monthly or continuous |
| Architecture Review | Annual assessment | Ongoing advisory |
| Root Cause Analysis | Superficial due to backlog | Deep forensic investigation |
| AI Model Validation | Not applicable | Core analyst competency |
Each of these activities directly reduces organizational risk, which is something manual triage never delivered no matter how diligently it was performed.
Solving the talent crisis from both ends
The cybersecurity workforce gap isn’t closing. ISC2’s 2025 study reports that the global workforce must grow 87% to meet demand, yet it expanded by only 0.1% year-over-year. In the U.S. alone, 700,000 positions remain unfilled. Budget constraints have now surpassed talent scarcity as the leading cause of understaffing.
Autonomous triage addresses this crisis from two directions. First, as a force multiplier: it enables existing teams to achieve coverage levels that would otherwise require massive headcount expansion. Second, as a retention tool. When you eliminate the most fatiguing aspects of the analyst role and replace them with intellectually engaging, career-developing work, you directly address the root causes of the 71% burnout rate and the 18-month turnover cycles that hemorrhage institutional knowledge.
A 2025 empirical study from the Journal for Labour Market Research found that when AI handles routine tasks, workers experience greater job satisfaction, skill development, and professional agency. The SOC analyst who hunts threats and engineers detections is a different professional from the one drowning in a ticket queue, and far more likely to build a long-term career in security.
Better security posture, the real payoff
The real value of autonomous triage is security outcomes. When analysts shift from reactive firefighting to proactive defense, organizations see measurable improvements across every dimension of security posture.
Proactive threat hunting identifies adversary footholds before they mature into full compromises, dramatically reducing dwell time. Continuous detection engineering restores the visibility that gets lost when overwhelmed analysts suppress rules. Regular red team exercises validate defenses against real-world techniques. And security architecture advisory embeds defensive thinking into infrastructure decisions before vulnerabilities are created.
With IBM’s 2025 Cost of a Data Breach report recording an average breach cost of $4.44 million, the return on proactive security investment is significant, and it compounds as the SOC’s capabilities mature.
The shift to autonomous triage means the same analysts doing more valuable work that actually moves the needle on organizational risk.
The path forward
Getting to autonomous SOC operations takes more than a software rollout. It requires phased adoption, deliberate investment in analyst reskilling, clear governance frameworks for AI decision-making, and evolved metrics that measure security outcomes rather than ticket throughput.
Organizations that adopt autonomous triage while investing in analyst growth will pull ahead: better security posture, more resilient operations, and a team built for what’s coming next. Those that wait risk falling further behind adversaries and losing the people they need most.
The SOC analyst role is evolving. The question is whether your organization is evolving with it.
For a deeper look at how autonomous triage reshapes the SOC analyst’s career path, skill requirements, and day-to-day responsibilities, read the full whitepaper: The Evolving Role of the SOC Analyst in the Age of AI-Driven Autonomous Security Operations.
The post The SOC Analyst Role Is Going Up (And It Was Never Going Away) appeared first on D3 Security.
*** This is a Security Bloggers Network syndicated blog from D3 Security authored by Shriram Sharma. Read the original post at: https://d3security.com/blog/role-of-the-soc-analyst/
如有侵权请联系:admin#unsafe.sh