Welcome to this week's edition of the Threat Source newsletter.
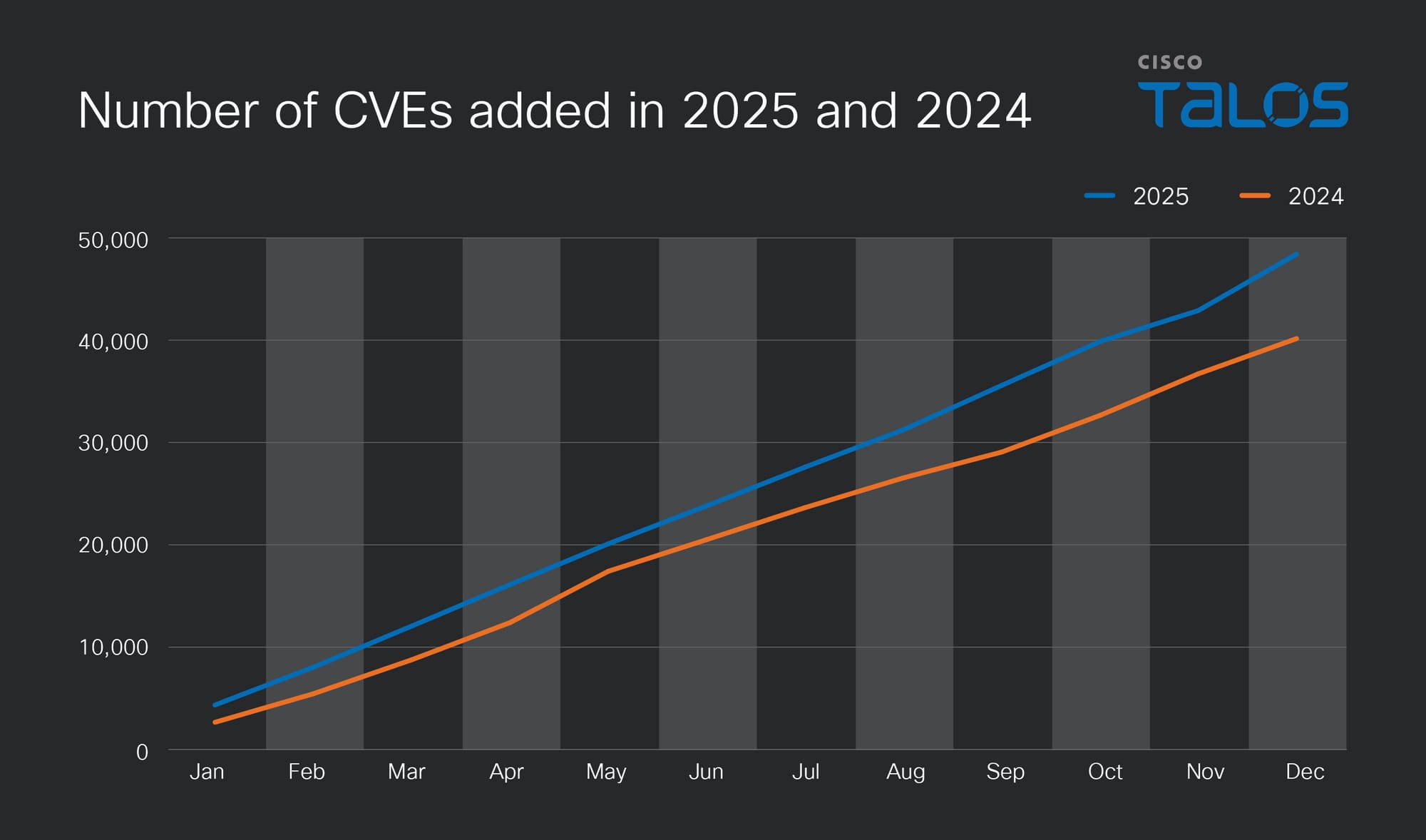
It's time to look back at a year that pushed the vulnerability landscape to new heights. I'll admit this retrospective is arriving a bit later than planned. With 48,196 CVEs in 2025 (a stunning 132 vulnerabilities per day), the analysis takes time — especially when you're operating one-handed after an encounter with black ice breaks your dominant arm. But better thorough than rushed, right?

What concerns me more than the sheer volume is what's inside these CVEs. XSS, SQL injection, and deserialization vulnerabilities continue to dominate, accounting for roughly 10,000 CVEs. Despite decades of awareness, these fundamental software security weaknesses persist.
The Known Exploited Vulnerabilities (KEV) Catalog tells an even more sobering story. With 241 KEVs in 2025 compared to 186 in 2024, we saw a 30% increase in confirmed active exploitation.

94 KEVs (39%) added in 2025 originated from CVE-2024 and earlier. We saw actively exploited vulnerabilities from as far back as 2007 — yes, vulnerabilities old enough to vote in some countries are still causing problems today. Patch management must address legacy systems. It starts with visibility: maintaining accurate asset inventories and understanding what's actually running in your environment. For those systems that truly can't be patched, whether due to operational constraints or vendor abandonment, compensating controls become essential. Microsegmentation, network isolation, and enhanced monitoring can reduce the radius of damage when (not if) something goes wrong.

With 54 KEVs targeting firewalls, VPNs, and other network appliances, we saw network infrastructure take a disproportionate hit. And the vendor landscape in KEVs expanded to 99 vendors in 2025, up from 79 when I last checked in October. Connect that with supply chain complexity and the patch management visibility challenges I mentioned earlier, and you'll quickly realize why security teams are spending more time — not less — on vulnerability management. Every additional vendor in your environment is another patch cycle to track, another advisory to monitor, another potential weak link in the chain.
This is the first time I've attempted to systematically track AI-related vulnerabilities in the CVE data, and the methodology is still evolving. Defining what constitutes an "AI vulnerability" isn'tstraightforward. For this initial pass, I searched for CVEs containing specific keywords across several categories:
AutoGPT, Open WebUI, Ollama, vLLM, llama.cpp, LLaMA-Factory, MaxKB, Dify, LangChain | |
PyTorch, TensorFlow, scikit-learn, XGBoost, Hugging Face, MLflow | |
ChatGPT, GPT-3, GPT-4, OpenAI, Anthropic, Claude Code | |
prompt injection, large language model, Model Context Protocol |
Using this approach, AI-related CVEs nearly doubled year-over-year, jumping from 168 to 330. Notably, “Model Context Protocol (MCP)” and “Claude” didn't appear in 2024 data at all.
A word of caution: While CVE data provides valuable insight into disclosed vulnerabilities in AI tools and frameworks, it doesn't capture emergent risks such as jailbreaking, hallucination-based misinformation, training data extraction, or model inversion attacks. See https://genai.owasp.org/llm-top-10/ and https://atlas.mitre.org/ if you want to learn more.
Keep tracking, keep patching, and stay tuned for the 2025 Year in Review for more trend analysis.
The one big thing
Cisco Talos continues to monitor the ongoing conflict in the Middle East. At this time we have not seen any significant cyber impacts, with some small incidents such as web defacements and small-scale distributed-denial-of-service (DDoS) attacks occurring. As with any highly fluid or dynamic situation, we are focused on providing our customers with highly accurate and timely intelligence and information. We will remain vigilant looking to identify any cyber related activity relevant to the region.
Why do I care?
Currently there does not appear to be any significant increase in cyber activity associated with state-sponsored or state-affiliated groups. However, cyber criminals are likely to take advantage of the war to try and increase their scope of infections through the use of lures and other social engineering avenues.
So now what?
Recommendations for organizations are currently focused on security hygiene, to include having multi-factor authentication (MFA) enabled, being diligent around any links or documents that are circulating, and ensuring you have proper monitoring in place to ensure you are prepared for any collateral impacts as they arise. Additional inspection or controls may be warranted to insulate potential larger impacts to the wider organization. Warn employees against clicking on unsolicited links related to the Middle East conflict, whether news or humanitarian. As always, ensure all software has been updated to the latest versions to minimize the attack surface and ensure you have a robust patching process.
If and/or when more relevant information becomes available, we will update this blog accordingly.
Top security headlines of the week
Hackers steal medical details of 15 million in France
France's health ministry has confirmed a data breach involving the exposure of administrative information for 15.8 million patients and sensitive doctors' notes for approximately 165,000 individuals. (France 24)
Google addresses actively exploited Qualcomm zero-day
The memory-corruption vulnerability (CVE-2026-21385) which Google’s Androidsecurity team reported to Qualcomm Dec. 18, affects 234 chipsets, Qualcomm said in a security bulletin. (CyberScoop)
Quantum decryption of RSA may be much closer than expected
The Advanced Quantum Technologies Institute announced that the JVG algorithm requires thousand-fold less quantum computer resources, and “research extrapolations suggest it will require less than 5,000 qubits to break encryption methods used in RSA and ECC.” (SecurityWeek)
Indian APT “Sloppy Lemming” targets defense, critical infrastructure
The group has evolved from using off-the-shelf red teaming tools like Cobalt Strike and Havoc C2 to developing its own custom tooling written in Rust, while expanding its C2 infrastructure (DarkReading)
Can’t get enough Talos?
UAT-9244 targets South American telecommunication providers
Since 2024, UAT-9244 has targeted critical telecommunications infrastructure, including Windows and Linux-based endpoints and edge devices in South America, proliferating access via three malware implants.
New Dohdoor malware campaign targets education and health care
Dohdoor utilizes the DNS-over-HTTPS (DoH) technique for command-and-control (C2) communications and has the ability to download and execute other payload binaries reflectively.
Upcoming events where you can find Talos
- DEVCORE 2026 (March 14) Taipei, Taiwan
- Botconf 2026 (April 15 – 17) Reims, France
Most prevalent malware files from Talos telemetry over the past week
SHA256: 96fa6a7714670823c83099ea01d24d6d3ae8fef027f01a4ddac14f123b1c9974
MD5: aac3165ece2959f39ff98334618d10d9
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=96fa6a7714670823c83099ea01d24d6d3ae8fef027f01a4ddac14f123b1c9974
Example Filename: d4aa3e7010220ad1b458fac17039c274_63_Exe.exe
Detection Name: W32.Injector:Gen.21ie.1201
SHA256: 90b1456cdbe6bc2779ea0b4736ed9a998a71ae37390331b6ba87e389a49d3d59
MD5: c2efb2dcacba6d3ccc175b6ce1b7ed0a
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=90b1456cdbe6bc2779ea0b4736ed9a998a71ae37390331b6ba87e389a49d3d59
Example Filename: d4aa3e7010220ad1b458fac17039c274_64_Dll.dll
Detection Name: Auto.90B145.282358.in02
SHA256: 9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
MD5: 2915b3f8b703eb744fc54c81f4a9c67f
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=9f1f11a708d393e0a4109ae189bc64f1f3e312653dcf317a2bd406f18ffcc507
Example Filename: https_2915b3f8b703eb744fc54c81f4a9c67f.exe
Detection Name: Win.Worm.Coinminer::1201
SHA256: 38d053135ddceaef0abb8296f3b0bf6114b25e10e6fa1bb8050aeecec4ba8f55
MD5: 41444d7018601b599beac0c60ed1bf83
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=38d053135ddceaef0abb8296f3b0bf6114b25e10e6fa1bb8050aeecec4ba8f55
Example Filename: content.js
Detection Name: W32.38D053135D-95.SBX.TG
SHA256: 5bb86c1cd08fe5e1516cba35c85fc03e503bd1b5469113ffa1f1b9e10897f811
MD5: f3e82419a43220a7a222fc01b7607adc
Talos Rep: https://talosintelligence.com/talos_file_reputation?s=5bb86c1cd08fe5e1516cba35c85fc03e503bd1b5469113ffa1f1b9e10897f811
Example Filename: Accounts Final-2024 .exe
Detection Name: Win.Dropper.Suloc::1201