February brought another round of major detection improvements across ANY.RUN’s threat intelligence and sandbox coverage. Alongside new Threat Intelligence reports, our analysts expanded behavioral visibility across dozens of malware families, strengthened detection logic for modern phishing and data-stealing campaigns, and added thousands of new network detection rules.
Let’s take a closer look at the updates delivered this month.
Threat Intelligence Reports
In February, we published several new Threat Intelligence Reports covering malware families and attack techniques currently observed in the wild. All reports are available to TI Lookup Premium users, along with related IOCs, detection guidance, and TI Lookup pivot queries.
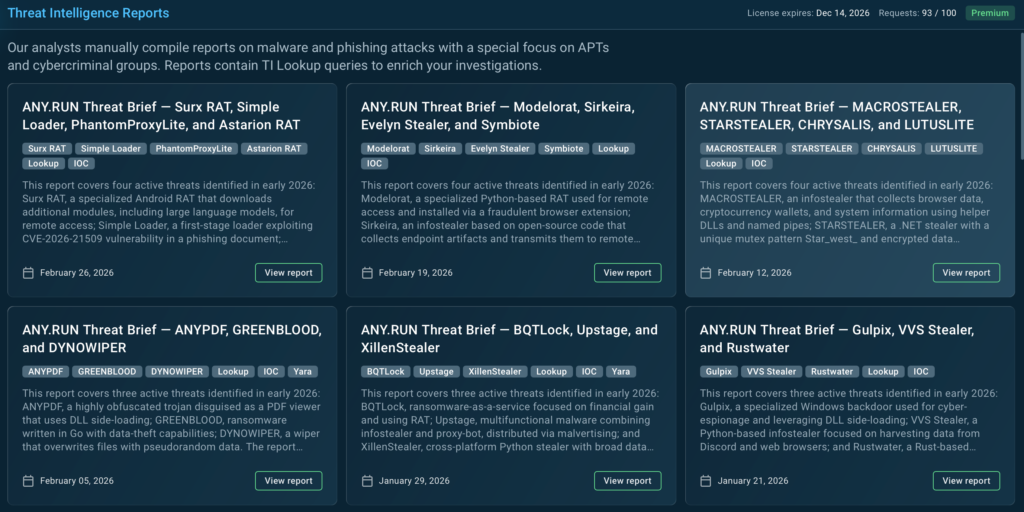
The reports cover the following threats:
- Anypdf, Greenblood, Dynowiper: A credential-stealing trojan disguised as a PDF viewer, a Go-based ransomware with data-theft capabilities, and a destructive wiper designed to overwrite files and make recovery impossible.
- Macrostealer, Starstealer, Chrysalis, Lutuslite: Credential-stealing malware targeting browsers and cloud services, alongside stealthy backdoors used in targeted intrusions and supply-chain attacks.
- Modelorat, Sirkeira, Evelyn Stealer, Symbiote: RAT and infostealer activity leveraging browser extensions, developer environments, and system persistence techniques to maintain access and exfiltrate sensitive data.
- Surx Rat, Simple Loader, Phantomproxylite, Astarion Rat: Malware used across different stages of attacks, from Android remote access and phishing-delivered loaders to tunneling tools and RAT implants enabling long-term control of compromised systems.
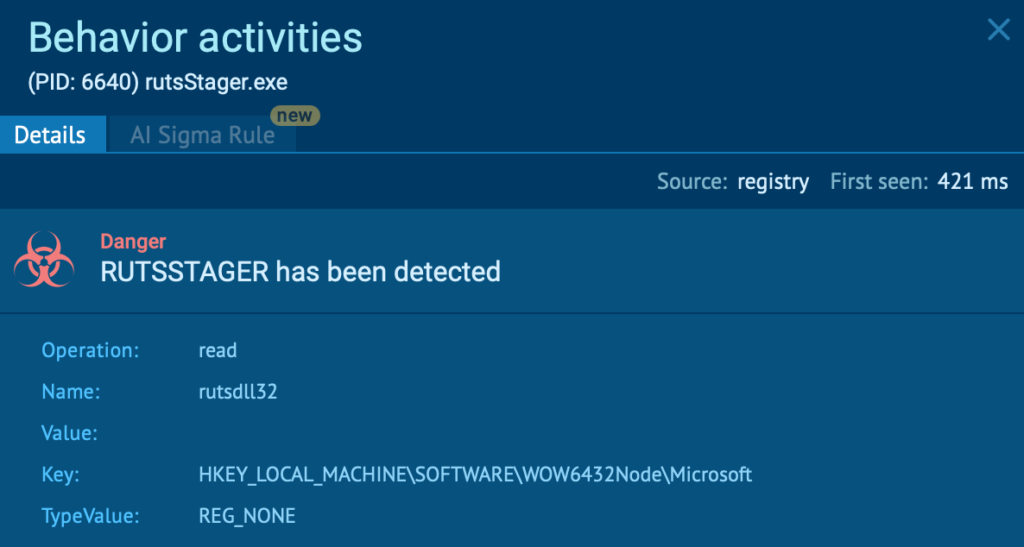
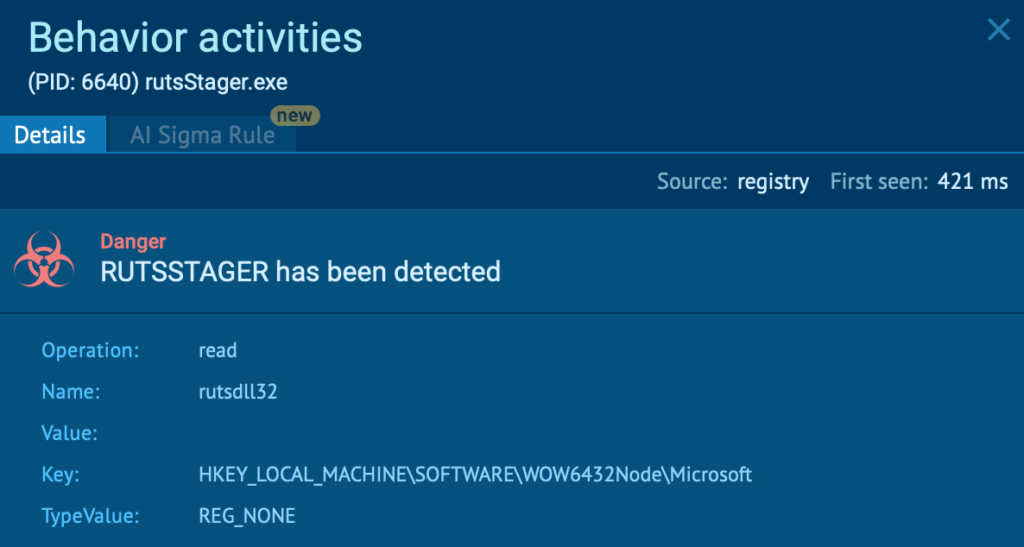
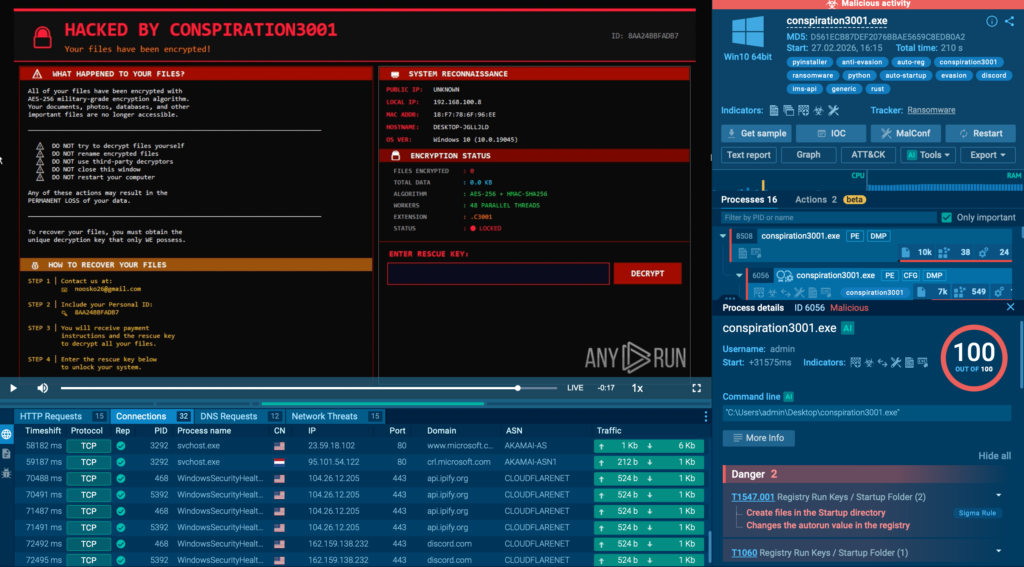
Behavior Signatures
In February, we expanded the malicious behavior coverage of ANY.RUN’s Interactive Sandbox with 150 new behavior signatures. These updates help teams surface malicious activity faster during analysis sessions and reduce investigation time by highlighting key indicators automatically.
The new signatures cover a wide range of malware families, including loaders, stealers, ransomware strains, and remote access tools commonly used in modern intrusion campaigns.
Among the threats now detected in the sandbox:
Evasion and discovery techniques:
- Vm-related process checks
- Vm-related registry checks
- Net.exe host discovery
- Deno runtime abuse
- Delegate execute modification
Loaders and droppers:
Remote access and control:

Stealers and credential-focused threats:
Malware families and tools observed in sessions:
YARA Rules
To improve early-stage detection during static inspection, we added 2 new YARA rules targeting destructive malware and RAT activity.
The new rules detect:
- DynoWiper: A destructive wiper capable of damaging systems and disrupting operations
- KarstoRAT: A remote access trojan capable of maintaining persistence and executing commands on infected machines
These rules allow analysts to quickly flag suspicious samples before full execution, accelerating triage and investigation workflows.
Suricata Rules
In February, we significantly expanded network-level detection with 2,314 new Suricata rules.
These additions strengthen monitoring capabilities for stealer activity, phishing infrastructure, and modern command-and-control communication patterns.
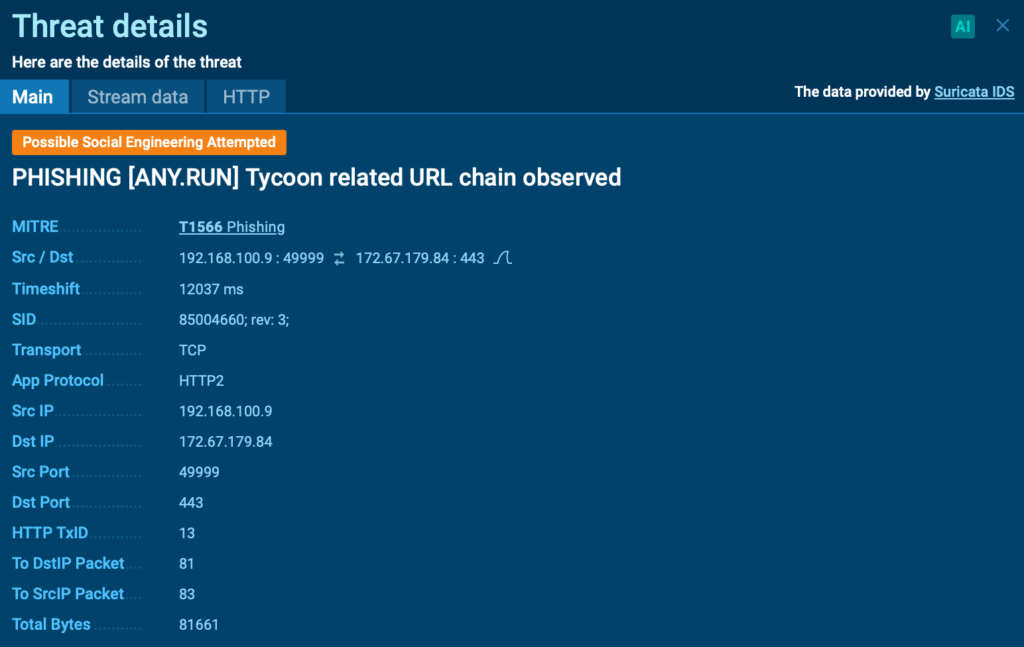
Key examples include:
- Tycoon2FA URL pattern observed (sid: 85005825): Detects HTTP requests with specific URL patterns associated with Tycoon PhaaS
- PureLogs TCP C2 connection (sid: 85006096): Identifies PureLogs Stealer attempts to establish connection with its C2 host
- Snake Keylogger exfil via Telegram (sid: 85006206): Tracks malware stolen data exfiltration via Telegram Bot API
These new rules help SOC teams identify malicious network activity earlier and gain deeper visibility into attacker infrastructure and data exfiltration channels.
About ANY.RUN
ANY.RUN, a leading provider of interactive malware analysis and threat intelligence solutions, integrates into modern SOC operations and supports investigations from the first alert through containment and detection improvement.
Security teams use ANY.RUN’s Interactive Sandbox to execute suspicious files and URLs safely, observe real behavior in a controlled environment, extract actionable indicators, and enrich findings instantly with Threat Intelligence Lookup and Threat Intelligence Feeds. This approach reduces uncertainty, improves validation accuracy, and keeps response consistent across the organization.
Today, more than 600,000 security professionals across 15,000+ organizations rely on ANY.RUN to accelerate investigations, strengthen detection coverage, and stay ahead of evolving phishing and malware campaigns.
Integrate ANY.RUN’s solution for Tier 1/2/3 in your organization →