好的,我现在需要帮用户总结这篇文章的内容,控制在100字以内。首先,我得仔细阅读文章,理解其主要内容和关键点。 文章主要讲的是一个新的WhatsApp骗局,称为GhostPairing攻击。骗子通过发送一条看似正常的“我找到了你的照片”的消息,诱导用户点击链接。链接看起来像Facebook页面,要求用户进行验证。实际上,这个页面会引导用户完成WhatsApp的设备连接过程,使得攻击者的设备被连接到用户的账户中。 攻击者不需要窃取密码或进行SIM卡交换,而是利用WhatsApp的正常功能来获取访问权限。一旦设备连接成功,攻击者可以查看消息、照片、视频,并发送信息,甚至冒充用户联系他人。这种攻击方式隐蔽性强,用户通常不会察觉。 文章还提到这种骗局传播迅速的原因是攻击者利用被入侵的账户继续发送诈骗信息给受害者的朋友和联系人。此外,作者建议用户检查已连接的设备、对代码和QR请求保持警惕、启用双重验证以及提高警惕意识。 总结起来,我需要在100字以内涵盖这些要点:新的WhatsApp骗局、通过伪装验证步骤获取访问权限、攻击者可以做什么、传播方式以及防范措施。 接下来,我需要组织语言,确保简洁明了。可能的结构是:描述骗局如何运作(通过伪装消息和页面),说明攻击者如何获得访问权限(利用设备连接功能),指出潜在危害(读取和发送信息),提到传播方式(利用受害者联系人),最后给出防范建议(检查设备、启用双重验证等)。 现在开始写: “一种新的WhatsApp骗局通过伪装成正常的验证步骤获取访问权限。骗子发送看似可信的消息并引导用户点击链接,该链接伪装成Facebook页面要求验证。实际上,这会引导用户完成WhatsApp的设备连接过程,使攻击者的设备与用户的账户相连。一旦连接成功,攻击者可以读取和发送信息,并进一步传播骗局。建议用户定期检查已连接设备、启用双重验证并提高警惕。” 这样大约在100字左右,并且涵盖了主要要点。 </think> 一种新的WhatsApp骗局通过伪装成正常的验证步骤获取访问权限。骗子发送看似可信的消息并引导用户点击链接,该链接伪装成Facebook页面要求验证。实际上,这会引导用户完成WhatsApp的设备连接过程,使攻击者的设备与用户的账户相连。一旦连接成功,攻击者可以读取和发送信息,并进一步传播骗局。建议用户定期检查已连接设备、启用双重验证并提高警惕。 2025-12-15 23:8:10 Author: blog.avast.com(查看原文) 阅读量:1 收藏
How a simple “I found your photo” message can quietly take over your account
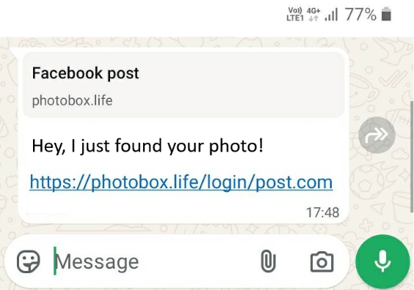
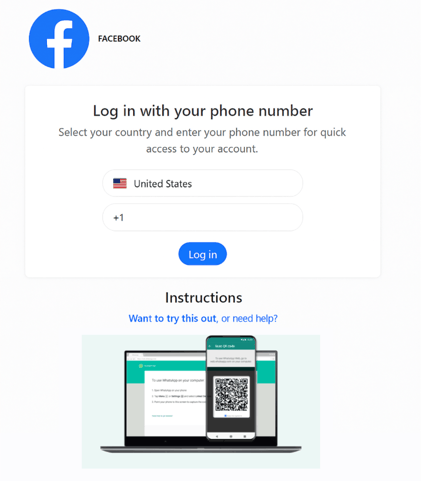
How a simple “I found your photo” message can quietly take over your account A new WhatsApp scam is spreading that doesn’t look like hacking at all. There’s no password theft. No SIM swap. No obvious warning signs. Instead, people are being tricked into giving attackers access themselves, simply by following what looks like a normal verification step. Security researchers call this a GhostPairing attack. Here’s how it works, why it’s dangerous, and what you can do to stay safe. It starts with a message from someone you trust The scam usually begins with a short, casual message from someone you know on WhatsApp. It often looks like this: “Hey, I just found your photo!” Lure message received by the victim There’s nothing obviously suspicious. No strange phone number. No long explanation. Just a familiar contact and a link. When you tap the link, it opens a page that looks like Facebook. Same colors. Same logo. Same general layout. The page tells you that you need to “verify” before you can view the photo. Many people click through without thinking twice. That’s the trap. The fake Facebook page isn’t about Facebook at all The page you see is not connected to Facebook. It’s a look-alike site designed to feel familiar and safe. Its real purpose is something very different. Instead of stealing your Facebook login, the page secretly walks you through WhatsApp’s own device-linking process, the same feature people use to connect WhatsApp Web or a desktop computer. Fake Facebook page showed after clicking on the WhatsApp received link By the end of the process, the attacker’s device is quietly added as a linked device on your WhatsApp account. From WhatsApp’s perspective, everything looks legitimate. You approved it. How attackers get into your WhatsApp without a password WhatsApp allows users to link new devices in two main ways: This scam mainly uses the numeric code option, because it works entirely on one phone and feels like a normal security step. Here’s what happens behind the scenes: No passwords are stolen. No security systems are broken. You’ve unknowingly invited them in. What scammers can see and do once they’re inside Once an attacker links their device, they get almost the same access you would on WhatsApp Web: The scariest part is that your phone keeps working normally. Many victims have no idea another device is connected in the background. The attacker can sit quietly, reading conversations and watching how people talk, for days or weeks. How the scam spreads so fast After taking over one account, attackers use it to message that person’s contacts. Family groups. Work chats. Sports teams. Friends. Because the message comes from someone people know, it feels safe. Some people click. Some don’t. Those who do become the next victims. This creates a snowball effect, allowing the scam to spread quickly without cold spam or random messages. Why this scam is especially concerning This attack stands out for a few reasons: In other words, it’s quiet, persistent, and easy to miss. And once attackers have access to conversations, they can use that information for more targeted scams, impersonation, or even extortion later on. How to protect yourself right now The good news is that protecting yourself against WhatsApp scams is straightforward. A bigger lesson beyond WhatsApp This attack isn’t just about one app. Many services today rely on QR codes, approval prompts, or “enter this code on your phone” flows to link devices quickly. When those steps are too easy and too invisible, they can be abused. GhostPairing is a reminder that convenience can become a vulnerability if users aren’t clearly warned what they’re approving. The bottom line This WhatsApp scam doesn’t break encryption or steal passwords. It does something simpler and more effective. It convinces people to approve access themselves. By hiding behind familiar designs and normal-looking verification steps, attackers can quietly create a “ghost device” that lives inside your account. A few small habits, checking linked devices, questioning unexpected verification requests, and sharing awareness, go a long way toward shutting this down. Staying safe doesn’t require technical expertise. It just requires knowing what to watch for. To read the original research, visit our Gen blog.
如有侵权请联系:admin#unsafe.sh