嗯,用户让我用中文总结一篇文章,控制在100字以内,而且不需要特定的开头。首先,我得仔细阅读这篇文章,找出关键信息。 文章主要讲的是CVE-2025-64155这个漏洞,属于Fortinet FortiSIEM设备的命令注入漏洞,CVSS评分9.4,非常严重。已经发布了利用代码,增加了被攻击的可能性。Fortinet设备一直是攻击者的目标,之前有23个CVE在CISA的列表里。文章还提到了修复版本和一些缓解措施。 接下来,我需要把这些信息浓缩到100字以内。要包括漏洞名称、影响范围、CVSS评分、已发布的利用代码、历史背景以及修复建议。同时,语言要简洁明了。 可能会遇到的问题是如何在有限的字数内涵盖所有关键点而不遗漏重要信息。可能需要删减一些细节,比如具体的受影响版本或缓解措施的具体步骤。 最后,确保总结直接描述文章内容,没有使用“这篇文章总结了...”这样的开头。 </think> Fortinet FortiSIEM设备存在严重命令注入漏洞CVE-2025-64155(CVSSv3评分9.4),允许远程未认证攻击者通过特制请求执行任意代码。该漏洞已发布公开利用代码,增加了被攻击风险。Fortinet设备历来是网络攻击目标,已有23个Fortinet CVE被列入CISA KEV列表。建议用户升级至修复版本以缓解风险。 2026-1-14 20:15:26 Author: www.tenable.com(查看原文) 阅读量:3 收藏
January 14, 2026
4 Min Read
Exploit code has been published for CVE-2025-64155, a critical command injection vulnerability affecting Fortinet FortiSIEM devices.
Key takeaways:
- CVE-2025-64155 is a critical operating system (OS) command injection vulnerability affecting Fortinet FortiSIEM.
- Fortinet vulnerabilities have historically been common targets for cyber attackers, with 23 Fortinet CVEs currently on the CISA KEV list.
- Public exploit code has been released, increasing the likelihood that CVE-2025-64155 could be exploited by attackers.
Background
On January 13, Fortinet published a security advisory (FG-IR-25-772) for CVE-2025-64155, a critical command injection vulnerability affecting Fortinet FortiSIEM.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2025-64155 | Fortinet FortiSIEM Command Injection Vulnerability | 9.4 |
Analysis
CVE-2025-64155 is a critical operating system (OS) command injection vulnerability affecting Fortinet FortiSIEM. A remote, unauthenticated attacker can exploit this flaw to execute arbitrary code using specially crafted requests.
Historical Exploitation of Fortinet Devices
Fortinet vulnerabilities have historically been common targets for cyber attackers, with 23 Fortinet CVEs currently on the Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) list. At the time this blog was published on January 14, CVE-2025-64155 had not been added to the KEV, however we anticipate that it is likely to be added in the near future.
As Fortinet devices have been popular targets for attackers, the Tenable Research Special Operations Team (RSO) has authored several blogs about vulnerabilities affecting these devices. The following table outlines some of the most impactful Fortinet vulnerabilities in recent years.
Proof of concept
On January 13, in coordination with the release of the advisory by Fortinet, researchers at Horizon3.ai published a technical writeup as well as a proof of concept for CVE-2025-64155. While there has been no reports of in-the-wild exploitation, we anticipate that attackers will quickly incorporate this exploit into their attacks.
Solution
The following table details the affected and fixed versions of Fortinet FortiSIEM devices for CVE-2025-64155:
| Product Version | Affected Range | Fixed Version |
|---|---|---|
| FortiSIEM 6.7 | 6.7.0 through 6.7.10 | Migrate to a fixed release |
| FortiSIEM 7.0 | 7.0.0 through 7.0.4 | Migrate to a fixed release |
| FortiSIEM 7.1 | 7.1.0 through 7.1.8 | 7.1.9 or above |
| FortiSIEM 7.2 | 7.2.0 through 7.2.6 | 7.2.7 or above |
| FortiSIEM 7.3 | 7.3.0 through 7.3.4 | 7.3.5 or above |
| FortiSIEM 7.4 | 7.4.0 | 7.4.1 or above |
| FortiSIEM 7.5 | Not affected | - |
| FortiSIEM Cloud | Not affected | - |
Fortinet’s security advisory advises if immediate patching is not able to be performed, they recommend limiting access to the phMonitor port of 7900. We strongly recommend reviewing the advisory for updates as well as the latest on mitigation recommendations.
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2025-64155 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
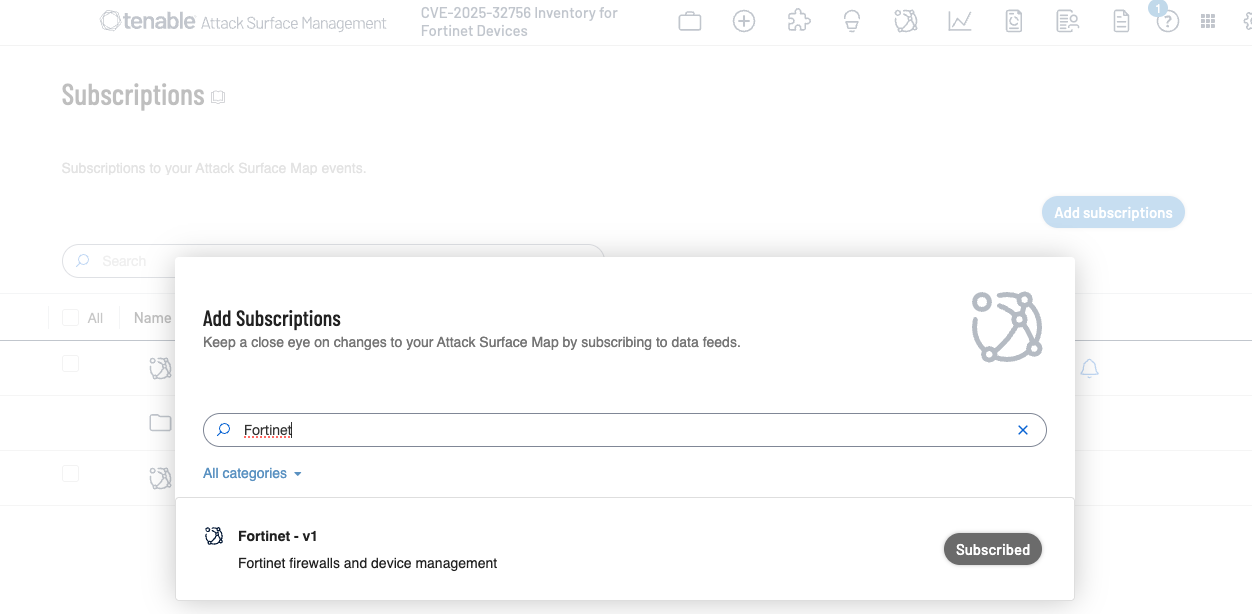
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Fortinet devices by using the following subscription:

Get more information
Join Tenable's Research Special Operations (RSO) Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.

Scott Caveza
Senior Staff Research Engineer, Research Special Operations
Scott joined Tenable in 2012 as a Research Engineer on the Nessus Plugins team. Over the years, he has written hundreds of plugins for Nessus, and reviewed code for even more from his time being a team lead and manager of the Plugins team. Previously leading the Security Response team and the Zero Day Research team, Scott is currently a member of the Research Special Operations team, helping the research organization respond to the latest threats. He has over a decade of experience in the industry with previous work in the Security Operations Center (SOC) for a major domain registrar and web hosting provider. Scott is a current CISSP and actively maintains his GIAC GWAPT Web Application Penetration Tester certification.
Interests outside of work: Scott enjoys spending time with his family, camping, fishing and being outdoors. He also enjoys finding ways to break web applications and home renovation projects.
Cybersecurity news you can use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
如有侵权请联系:admin#unsafe.sh