August 26, 2025
4 Min Read

Citrix has released patches to address a zero-day remote code execution vulnerability in NetScaler ADC and NetScaler Gateway that has been exploited. Organizations are urged to patch immediately.
Background
On August 26, Citrix published a security advisory for three vulnerabilities, including CVE-2025-7775, a zero-day vulnerability which has been exploited against its NetScaler Application Delivery Controller (ADC) and NetScaler Gateway appliances:
| CVE | Description | CVSSv4 |
|---|---|---|
| CVE-2025-7775 | Citrix NetScaler ADC and Gateway Unauthenticated Remote Code Execution (RCE) and Denial of Service (DoS) Vulnerability | 9.2 |
| CVE-2025-7776 | Citrix NetScaler ADC and Gateway DoS Vulnerability | 8.8 |
| CVE-2025-8424 | Citrix NetScaler ADC and Gateway Improper Access Control Vulnerability | 8.7 |
Analysis
CVE-2025-7775 is a RCE vulnerability affecting NetScaler ADC and Gateway appliances. An unauthenticated attacker could exploit this vulnerability to execute arbitrary code or cause a DoS condition on an affected device. According to the security advisory from Citrix, exploitation has been observed prior to the advisory and patches being made public.
While Citrix only confirmed exploitation of CVE-2025-7775, two additional vulnerabilities were patched as part of the same security advisory.
CVE-2025-7776 is a DoS vulnerability affecting NetScaler ADC and Gateway appliances. An authenticated attacker can trigger a memory overflow vulnerability in order to cause a DoS condition on an affected device. Devices that have been configured as a Gateway with a bounded PCoIP Profile are affected by this vulnerability.
CVE-2025-8424 is an improper access control vulnerability affecting NetScaler ADC and Gateway appliances. While no privileges are required to exploit this vulnerability, an attacker would need access to “NSIP, Cluster Management IP or local GSLB Site IP or SNIP with Management Access” in order to take advantage of this flaw.
ADC and Gateway Historically Targeted by Attackers
Citrix’s NetScaler ADC and Gateway appliances have been a valuable target for attackers over the last several years. Vulnerabilities including CVE-2022-27518 and CVE-2019-19781 have been favored by attackers. This includes attacks from Chinese state-sponsored threat actors, Iranian-based threat actors, Russian state-sponsored threat groups as well as ransomware groups. Additionally, CVE-2019-19781 was featured as one of the Top 5 vulnerabilities in our 2020 Threat Landscape Retrospective report.
More recently, Citrix NetScaler ADC and Gateway have been targeted by vulnerabilities known as CitrixBleed and CitrixBleed 2. CVE-2023-4966, known as CitrixBleed, was first disclosed in October 2023 after it was discovered as being exploited as a zero-day. Attacks continued to ramp up and the flaw was widely exploited by multiple ransomware groups and additional threat actors. CVE-2025-5777, known as CitrixBleed 2, was disclosed in June of this year. Multiple security researchers and outlets reported that CitrixBleed 2 was also exploited as a zero-day.
Due to the historical exploitation against NetScaler ADC and Gateway appliances, we strongly urge organizations to patch CVE-2025-7775 as soon as possible.
Proof of concept
At the time this blog post was published, no public proof-of-concept (PoC) had been identified for any of these vulnerabilities. However, given the historical exploitation of Citrix NetScaler ADC and Gateway and the reported usage of CVE-2025-7775 as a zero-day, we anticipate that exploit code may become available soon.
Solution
Citrix has released patches for these vulnerabilities as outlined in the table below:
| Affected Product | Affected Version | Fixed Version |
|---|---|---|
| NetScaler ADC and NetScaler Gateway | 13.1 before 13.1-59.22 | 13.1-59.22 and later releases of 13.1 |
| NetScaler ADC and NetScaler Gateway | 14.1 before 14.1-47.48 | 14.1-47.48 and later releases |
| NetScaler ADC | ADC 13.1-FIPS and NDcPP before 13.1-37.241-FIPS and NDcPP | 13.1-37.241-FIPS and NDcPP and later releases |
| NetScaler ADC | 12.1-FIPS and NDcPP before 12.1-55.330-FIPS and NDcPP | 12.1-55.330-FIPS and NDcPP and later releases |
Note: NetScaler ADC and NetScaler Gateway version 12.1 and 13.0 are End Of Life (EOL). Customers are recommended to upgrade their appliances to a supported version that addresses these vulnerabilities.
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE pages for CVE-2025-7775, CVE-2025-7776, and CVE-2025-8424 as they’re released. This link will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.
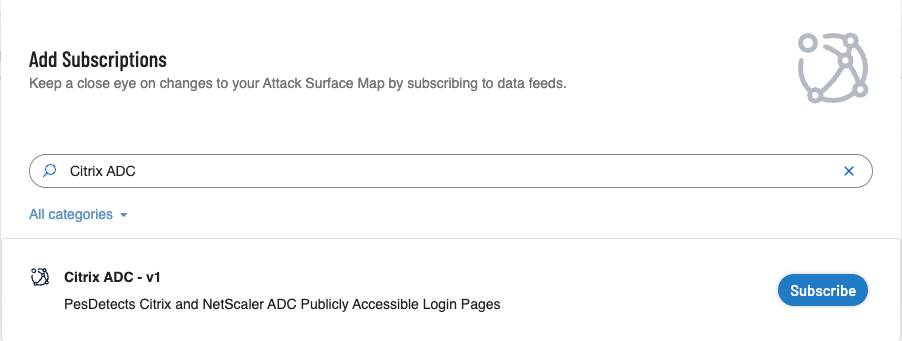
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing NetScaler ADC and Gateway assets by using the following subscription:
Get more information
- NetScaler ADC and NetScaler Gateway Security Bulletin for CVE-2025-7775, CVE-2025-7776 and CVE-2025-8424
- Tenable Blog: Frequently Asked Questions for CitrixBleed (CVE-2023-4966)
- Tenable Blog: CVE-2025-5777, CVE-2025-6543: Frequently Asked Questions About CitrixBleed 2 and Citrix NetScaler Exploitation
Join Tenable's Research Special Operations (RSO) Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.

Scott Caveza
Senior Staff Research Engineer, Security Response
Scott joined Tenable in 2012 as a Research Engineer on the Nessus Plugins team. Over the years, he has written hundreds of plugins for Nessus, and reviewed code for even more from his time being a team lead and manager of the Plugins team. Previously leading the Security Response team and the Zero Day Research team, Scott is currently a member of the Security Response team, helping the research organization respond to the latest threats. He has over a decade of experience in the industry with previous work in the Security Operations Center (SOC) for a major domain registrar and web hosting provider. Scott is a current CISSP and actively maintains his GIAC GWAPT Web Application Penetration Tester certification.
Interests outside of work: Scott enjoys spending time with his family, camping, fishing and being outdoors. He also enjoys finding ways to break web applications and home renovation projects.
- Exposure Management
- Tenable Vulnerability Management
Cybersecurity news you can use
Enter your email and never miss timely alerts and security guidance from the experts at Tenable.
