文章揭示了Proton66 ASN及其关联公司Chang Way Technologies涉及的恶意网络活动,包括漏洞扫描、攻击尝试、钓鱼活动及勒索软件传播。研究发现其利用最新漏洞针对科技、金融等行业发起攻击,并通过地下托管服务进行隐蔽运营。 2025-4-14 13:56:38 Author: www.trustwave.com(查看原文) 阅读量:15 收藏
4 Minute Read
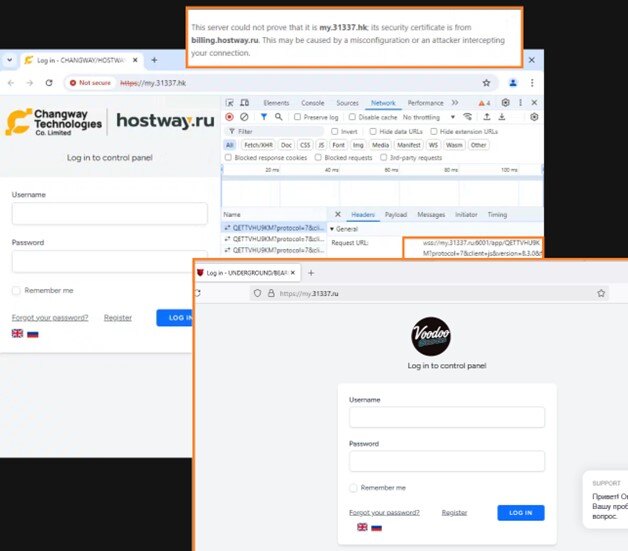
Trustwave SpiderLabs continuously tracks a range of malicious activities originating from Proton66 ASN, including vulnerability scanning, exploit attempts, and phishing campaigns leading to malware infections. In this two-part series, SpiderLabs explores the malicious traffic associated with Proton66, revealing the extent and nature of these attacks. The first part of the series focuses on mass scanning and exploit activities, highlighting a specific IP address connected to SuperBlack ransomware operators, found to distribute some of the latest critical priority exploits. The second part delves into a range of malware campaigns linked to Proton66, including compromised WordPress websites redirecting Android devices to fake Google Play stores, an XWorm campaign targeting Korean-speaking chat room users, and the WeaXor Ransomware. In November 2024, the security firm Intrinsec detailed how PROSPERO (AS200593) and Proton66 (AS198953) are connected to bulletproof services advertised on underground forums under the names UNDERGROUND and BEARHOST. Multiple malware campaigns were mentioned, with some of the IP addresses changing between networks. Interested customers could reach out via dedicated Telegram or Jabber accounts offering both Russian and English. In December 2024, a thread offering hosting services from UNDERGROUND/BEARHOST disappeared from one of the major underground forums. This, of course, confused some users, and they started to ask questions. A user named “Voodo_servers” responded to one of those inquiries, stating that the services are now offered through a private company, and customers are no longer being recruited through the forums. Intrinsec’s research had already drawn indirect connections between BEARHOST/UNDERGROUND and Hong Kong-based Chang Way Technologies Co. Limited, however, SpiderLabs’ investigation revealed another interesting piece of evidence suggesting a rebranding. While the Russian hosting control panel used by UNDERGROUND BEARHOST customers, my.31337.ru, remained unchanged, my.31337.hk page was updated to a new CHANGWAY / HOSTWAY theme. However, a websocket connection to my.31337.ru:6001 opened by the panel application script was visible in the background, indicating that the underlying infrastructure is interlaced. Interestingly, likely due to misconfiguration, a certificate from billing.hostway.ru was served by my.31337.hk at the time of research. SpiderLabs also observed an IP address shift from Proton66 ASN to Chang Way Technologies ASN in campaigns leveraging compromised WordPress pages discussed in Part 2, suggesting a relation between both providers. Starting from January 8, 2025, SpiderLabs observed an increase in mass scanning, credential brute forcing, and exploitation attempts originating from Proton66 ASN targeting organizations worldwide. Although malicious activity was seen in the past, the spike and sudden decline observed later in February 2025 were notable, and offending IP addresses were investigated. AS198953, belonging to Proton66 OOO, consists of five net blocks, which are currently listed on blocklists such as Spamhaus due to malicious activity. Net blocks 45.135.232.0/24 and 45.140.17.0/24 were particularly active in terms of mass scanning and brute force attempts. Several of the offending IP addresses were not previously seen to be involved in malicious activity or were inactive for over two years. For instance, the last activities reported in AbuseIPDB for the IP addresses 45.134.26.8 and 45.135.232.24 were noted in November and July 2021, respectively. Statistics collected between January and March indicated that technology and financial organizations were, in general, the most common target for these activities. The majority of these scanning and exploit attempts have already been blocked at the time of research, mitigating the exploitation risk for our customers. Malicious requests originating from 193.143.1.65. observed by SpiderLabs in February 2025 were particularly interesting, aiming to exploit some of the most recent critical vulnerabilities: A research document published by Forescout in March, links 193.143.1.65 with activities performed by a new ransomware operator and likely an initial access broker, dubbed “Mora_001”, seen exploiting critical authentication bypass vulnerabilities affecting Fortinet FortiOS-based devices (CVE-2024-55591 and CVE-2025-24472). The intrusion following FortiOS exploitation led to the deployment of a new ransomware strain dubbed “SuperBlack”, which closely resembles LockBit 3.0. The main differences lie in the ransom note left after encryption and the custom data exfiltration executable. SpiderLabs analyzed the sectors targeted by malicious traffic originating from the IP address 193.143.1.65, which is linked to “Mora_001”, between January and March and found that non-profit, engineering, and financial sectors were the attacker’s most preferred picks. All of our customers were protected as the scanning and exploit attempts were blocked. In the second part, we will discuss malware campaigns linked to Proton66, including compromised WordPress websites redirecting Android devices to fake Google Play stores, an XWorm campaign targeting Korean chat room users, and the WeaXor ransomware. Selected IOCs Observed (Scanning, Brute Force, and Exploitation): Selected IOCs Observed (Scanning, Brute Force, and Exploitation):Underground Hosting Services

Figure 1. Telegram accounts operating bulletproof services as BEARHOST/UNDERGROUND. Source: SpiderLabs.
Figure 2. Bearhost/Underground rebranding to Changway/Hostway. Source: SpiderLabs.Mass scanning and exploit campaigns targeting multiple sectors

Figure 3. Volume of the scanning and exploit traffic originating from Proton66 ASN. Source: SpiderLabs.
Figure 4. Scanning and exploit traffic volume originating from Proton66 net blocks (Jan. to Mar. 2025). Source: SpiderLabs.SuperBlack Ransomware Operator Takes Advantage of Newest Vulnerabilities

Figure 5. URL request observed in exploit attempts.

Figure 6. URL request observed in exploit attempts.

Figure 7. URL request observed in exploit attempts.
Figure 8. SuperBlack ransomware note. Source: Forescout Research.
Figure 9. Sectors targeted by scans, brute force, and exploit attempts from 193.143.1.65. Source: SpiderLabs
Figure 10. Selected IOCs Observed.
Figure 11. Selected IOCs Observed.
如有侵权请联系:admin#unsafe.sh