2024-12-3 16:11:23 Author: securityaffairs.com(查看原文) 阅读量:8 收藏
BootKitty Linux UEFI bootkit spotted exploiting LogoFAIL flaws
Pierluigi Paganini
December 03, 2024

The ‘Bootkitty’ Linux UEFI bootkit exploits the LogoFAIL flaws (CVE-2023-40238) to target systems using vulnerable firmware.
Cybersecurity researchers from ESET recently discovered the first UEFI bootkit designed to target Linux systems, called by its authors Bootkitty.
The bootkit allows attackers to disable the kernel’s signature verification feature and to preload two as yet unknown ELF binaries via the Linux init process.
A previously unknown UEFI application, named bootkit.efi, was uploaded to VirusTotal in November 2024.
“Our initial analysis confirmed it is a UEFI bootkit, named Bootkitty by its creators and surprisingly the first UEFI bootkit targeting Linux, specifically, a few Ubuntu versions.” reads the advisory published by ESET. “Bootkitty is signed by a self-signed certificate, thus is not capable of running on systems with UEFI Secure Boot enabled unless the attackers certificates have been installed.”
The researchers noticed the many artifacts in bootkit.efi, suggesting that the binary is likely a proof of concept that was never used in attacks in the wild.
The authors signed Bootkitty with a self-signed certificate, thus the malware cannot run on systems with UEFI Secure Boot enabled unless the attackers’ certificates have been installed.
Bootkitty bypasses UEFI Secure Boot by patching integrity verification functions in memory, allowing seamless Linux kernel booting.
Bootkitty supports a limited number of systems due to hardcoded byte patterns for function modification and fixed offsets for patching decompressed Linux kernels.
The bootkit hooks UEFI authentication functions to bypass the Secure Boot mechanism and patches GRUB boot loader functions to evade additional integrity verifications.
Researchers from firmware security firm Binarly now report that Bootkitty Linux UEFI bootkit exploits the LogoFAIL flaw CVE-2023-40238 to compromise systems running on vulnerable firmware.
This is confirmed by firmware security firm Binarly, which discovered LogoFAIL in November 2023 and warned about its potential to be used in actual attacks.
LogoFAIL is a collection of vulnerabilities in UEFI image-parsing components, an attacker can exploit them to hijack boot processes and deploy bootkits.
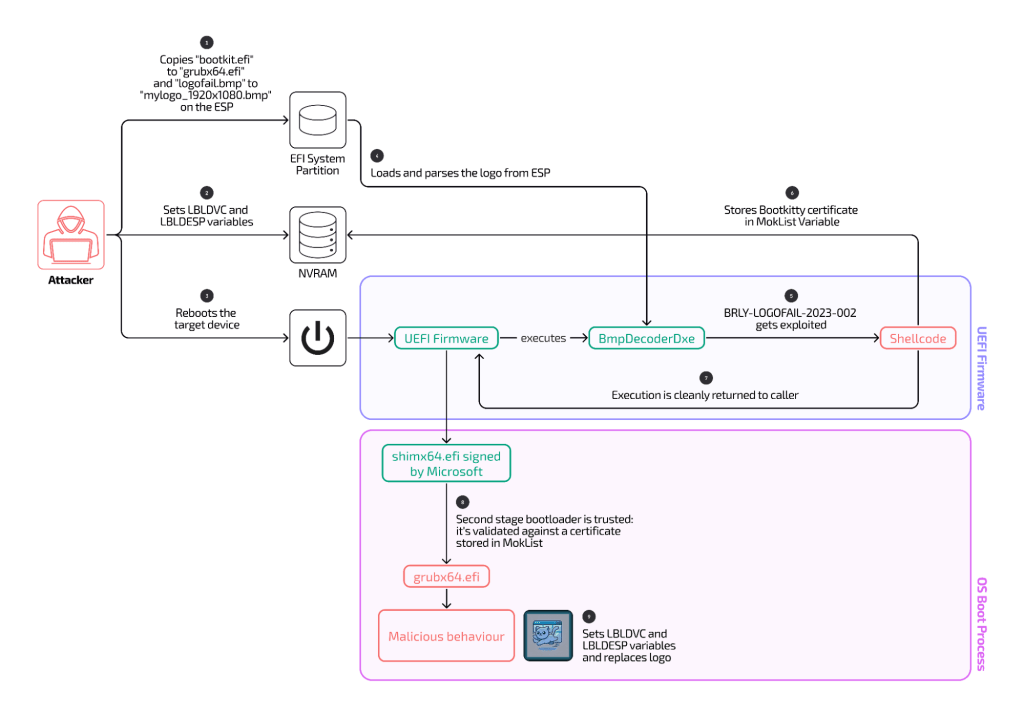
Bootkitty exploits LogoFAIL via tampered BMP files to inject shellcode, bypass Secure Boot, and target specific devices from different manufacturers, including Acer, HP, Fujitsu, and Lenovo. Despite a security patch was released, several devices are still vulnerable.
Bootkitty embeds shellcode in BMP files (‘logofail.bmp’ and ‘logofail_fake.bmp’) to bypass Secure Boot by injecting rogue certificates into the MokList variant.
“This means that the shellcode is setting the MokList variable with some rogue content (pointed by the Data variable above).” reads the report. “The variable MokList is set with a rogue certificate by the shellcode because this variable is used during the boot process (by shim) to verify the second stage bootloader, which exactly corresponds to bootkit.efi in the case of Bootkitty. “
Researchers dismissed logofail_fake.bmp as benign but flagged logofail.bmp, a 16MB file that showed some anomalies like negative dimension values (the width and the height of BMP are 0xfffffd00 (-768) and 0x0, respectively), repeated patterns, and embedded shellcode alongside certificate metadata linked to the bootkit.
Bootkitty’s shellcode exploits LogoFAIL in three stages: preparing the boot environment, exploiting the vulnerability, and deploying a malicious bootloader while replacing the boot logo.
Bootkitty restores the original instructions in the RLE8ToBlt function after executing its shellcode, attempting to erase any indicators of compromise.

Bootkitty primarily targets Lenovo devices using Insyde firmware, likely due to developer testing, but broader device support may follow. Vulnerable models include IdeaPad, Legion, and Yoga series.
“It’s been more than a year since we first sounded the alarm about LogoFAIL and yet, many affected parties remain vulnerable to one or more variants of the LogoFAIL vulnerabilities. Bootkitty serves as a stark reminder of the consequences of when these vulnerabilities are not adequately addressed or when fixes are not properly deployed to devices in the field.” concludes the report.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, LogoFAIL)
如有侵权请联系:admin#unsafe.sh