2024-4-22 00:38:20 Author: securityaffairs.com(查看原文) 阅读量:7 收藏
DuneQuixote campaign targets the Middle East with a complex backdoor

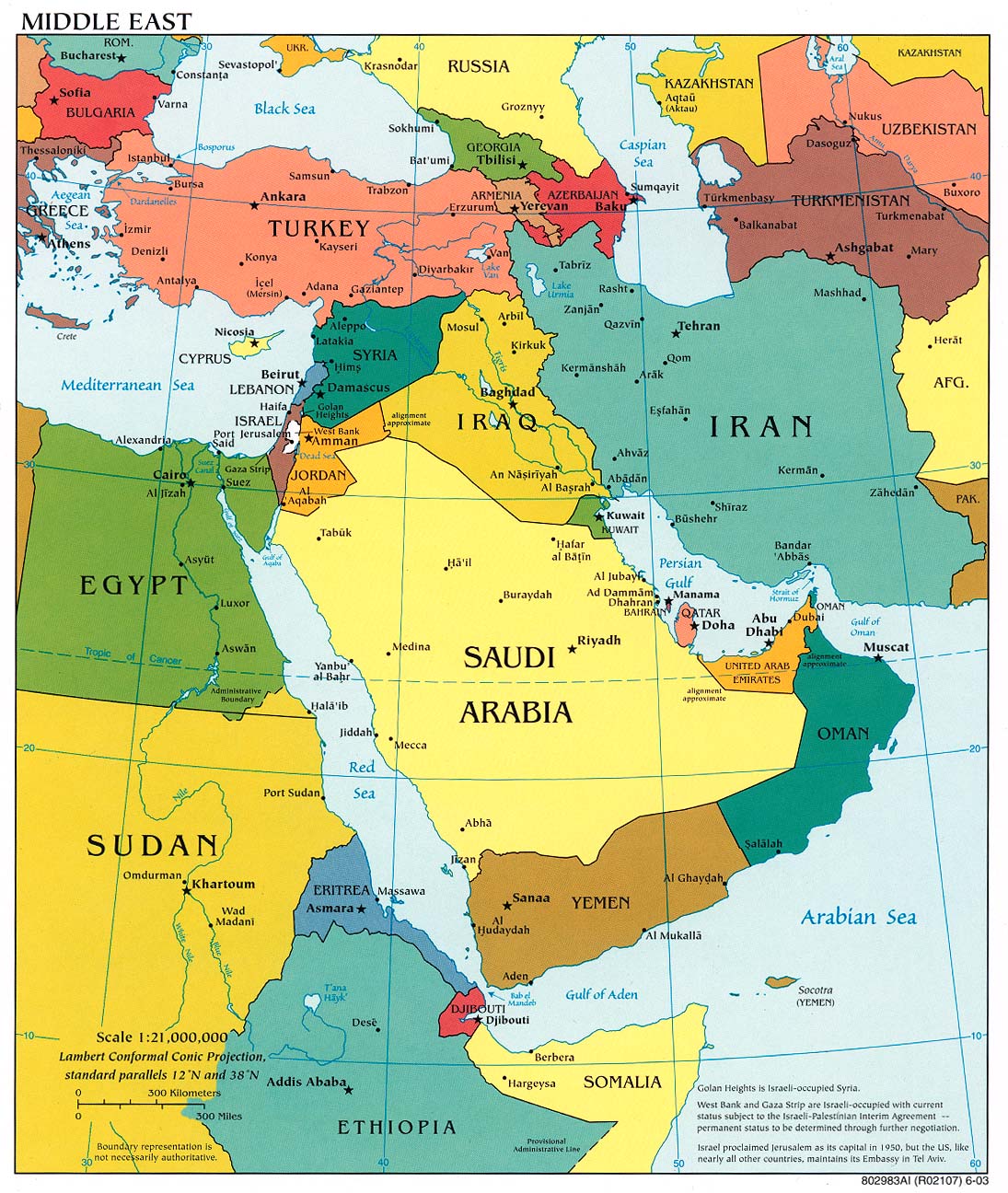
Threat actors target government entities in the Middle East with a new backdoor dubbed CR4T as part of an operation tracked as DuneQuixote.
Researchers from Kaspersky discovered the DuneQuixote campaign in February 2024, but they believe the activity may have been active since 2023.
Kaspersky discovered over 30 DuneQuixote dropper samples used in the campaign. The experts identified two versions of the dropper, regular droppers (in the form of an executable or a DLL file) and tampered installer files for a legitimate tool named “Total Commander.”
The droppers were employed to download a backdoor tracked as “CR4T”. The experts detected only two CR4T implants, but they speculate the existence of many other variants which may be completely different malware.
The threat actors behind the DuneQuixote campaign took steps to prevent collection and analysis the implants through the implementation of practical and well-designed evasion methods.
The dropper connects to an embedded command-and-control (C2), whose address is hardcoded in the malicious code and is decrypted using a unique technique to prevent its exposure to automated malware analysis tools.
“The initial dropper is a Windows x64 executable file, although there are also DLL versions of the malware sharing the same functionality. The malware is developed in C/C++ without utilizing the Standard Template Library (STL), and certain segments are coded in pure Assembler.” reads the analysis published by Kaspersky. “The dropper then proceeds to decrypt the C2 (Command and Control) address, employing a unique technique designed to prevent the exposure of the C2 to automated malware analysis systems. This method involves first retrieving the filename under which the dropper was executed, then concatenating this filename with one of the hardcoded strings from Spanish poems. Following this, the dropper calculates the MD5 hash of the concatenated string, which is then used as a key for decrypting the C2 string.”
The threat actors used strings in these functions consisting of excerpts from Spanish poems. The strings differ from one sample to another, altering the signature of each sample to avoid detection through conventional methods. Then, after executing decoy functions, the malware constructs a framework for the required API calls. This framework is filled with offsets of Windows API functions, resolved through various techniques.
The dropper calculates the MD5 hash of the combined string and uses it as the key to decode the C2 server address. Then the dropper connects with the C2 server and downloads a next-stage payload.
The researchers noticed that the payload can only be downloaded once per victim or is only accessible for a short period after a malware sample is released, for this reason, researchers were unable to obtain most of the payload implants from active C2 servers.
The Total Commander installer dropper is designed to appear like a genuine Total Commander software installer but includes additional malicious components. These alterations invalidate the official digital signature of the Total Commander installer. This version of the dropper maintains the core functionality of the initial dropper but excludes Spanish poem strings and decoy functions. Additionally, it incorporates anti-analysis measures and checks to prevent connections to C2 resources.
The experts also spotted a Golang version of the CR4T implant that shares similar capabilities with the C version. It includes a command line console for machine interaction, file download/upload functions, and command execution capabilities. Notably, the malware can create scheduled tasks using the Golang Go-ole library, which interfaces with the Windows Component Object Model (COM) for Task Scheduler service interaction.
The malware achieves persistence through the COM objects hijacking technique. The malware uses the Telegram API for C2 communications, implementing the public Golang Telegram API bindings. All the interactions are similar to the C/C++ version.
“The “DuneQuixote” campaign targets entities in the Middle East with an interesting array of tools designed for stealth and persistence. Through the deployment of memory-only implants and droppers masquerading as legitimate software, mimicking the Total Commander installer, the attackers demonstrate above average evasion capabilities and techniques.” concludes the report. “The discovery of both C/C++ and Golang versions of the CR4T implant highlights the adaptability and resourcefulness of the threat actors behind this campaign.“
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, malware)
如有侵权请联系:admin#unsafe.sh