2024-3-2 04:11:51 Author: www.malwarebytes.com(查看原文) 阅读量:21 收藏
A new type of malware is being used by ransomware gangs in their attacks, and its name is PikaBot.
A relatively new trojan that emerged in early 2023, PikaBot is the apparent successor to the infamous QakBot (QBot) trojan that was shut down in August 2023. QBot was used by many ransomware gangs in the past for its versatile ability to facilitate initial access and deliver secondary payloads.
After QBot got shut down, there was a vacuum in the ransomware gang tool box—but with PikaBot, that’s beginning to change: last month we wrote about the first recorded instance of PikaBot being used by ransomware gangs, specifically Black Basta, in their attacks.
Let’s dig into how PikaBot works, how it’s distributed, how ransomware gangs use it in their attacks, and how to stop it with ThreatDown.
A closer look at PikaBot
To get a better idea of how PikaBot works, we need to first understand what a modular trojan is.
Simply put, a modular trojan is a type of malware designed to be flexible and extensible, allowing attackers to add or update its functionalities easily without needing to replace the whole malware.
The modular nature of trojans like QBot and PikaBot are what makes them so dangerous. Unlike simpler malware, PikaBot can execute arbitrary commands, download additional payloads, and inject malicious shellcode into legitimate processes running on a victim’s computer. Think of it like a backdoor that allows attackers to set up for the next stages of their attacks.
Once it’s installed onto a system, PikaBot has a whole host of ways to stay under the radar, evading detection by most conventional security tools through techniques like indirect system calls and advanced obfuscation methods.
How Pikabot is distributed
The distribution of PikaBot, like many other malicious loaders such as QBot and DarkGate, is heavily reliant on email spam campaigns. Even so, ThreatDown Intelligence researchers have seen PikaBot being delivered via malicious search ads as well (also known as “malvertising”).
PikaBot’s initial access campaigns are meticulously crafted, utilizing geolocalized spam emails that target specific countries. The emails often contain links to external SMB (Server Message Block) shares, which host malicious zip files.
SMB shares are network folders leveraging the SMB protocol—a network file sharing protocol designed for sharing files and printers across devices on a network. Attackers often use SMB shares to distribute malware. In this case, downloading and opening the hosted zip file results in PikaBot infection.
For example, consider the below phishing email containing a link to a zip file containing the PikaBot payload.

Source: ANY.RUN (Translation: I sent you some paperwork the other day. Did you get it?)
Once the recipient interacts with these emails by clicking on the link, they are taken to the SMB share hosting the malicious zip files.
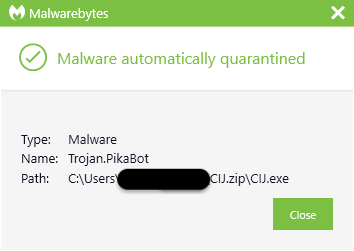
Extracting a zip and double-clicking on the executable within it will install PikaBot.

Source: ANY.RUN
How ransomware gangs use PikaBot
Ransomware gangs commonly use modular trojans like PikaBot for their attacks.
Before it was shut down, for example, Qbot allowed ransomware gangs to seamlessly integrate various attack techniques into their operations, including stealing credentials, moving laterally across networks, and ultimately deploying ransomware or other malicious payloads.
PikaBot is being used by ransomware attackers in a similar way.
Once PikaBot has established a foothold in a network, it allows attackers to engage in a wide range of follow-up activities.
For example, researchers have noted affiliates of the BlackBasta ransomware gang using PikaBot to use encrypted communications with command and control (C&C) servers. Pikabot can also assist gangs in getting detailed information about infected systems, helping them tailor their ransomware for maximum impact.
How to stop PikaBot with ThreatDown
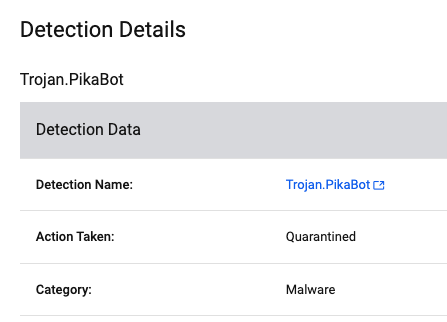
Besides preventing initial access through things such as a web content filter and phishing training, choosing an Endpoint Detection and Response (EDR) platform that automatically detects and quarantines threats like PikaBot is crucial.
However, given the constant evolution of malware, identifying dynamic threats like Pikabot boils down to two words: threat hunting.
At ThreatDown, we talk a lot about the importance of threat hunting for SMBs—and not for no good reason, either. Just consider the fact that, when an attacker breaches a network, they don’t attack right away. The median amount of time between system compromise and detection is 21 days.
By that time, it’s often too late. Data has been harvested or ransomware has been deployed.
Threat hunting helps find and remediate highly-obfuscated threats like PikaBot that can quietly lurk in the network, siphoning off confidential data and searching for credentials to access the “keys to the kingdom.”
For example, as detailed in one case study, the ThreatDown Managed Detection and Response (MDR) team employed threat hunting techniques to uncover and neutralize a sophisticated QBot attack on a reputable oil and gas company. The team’s approach involved meticulously examining Indicators of Compromise (IoCs), analyzing network traffic, and scrutinizing unusual patterns of behavior within the company’s IT infrastructure, ultimately resulting in Qbot’s discovery on the network and isolation of infected systems.

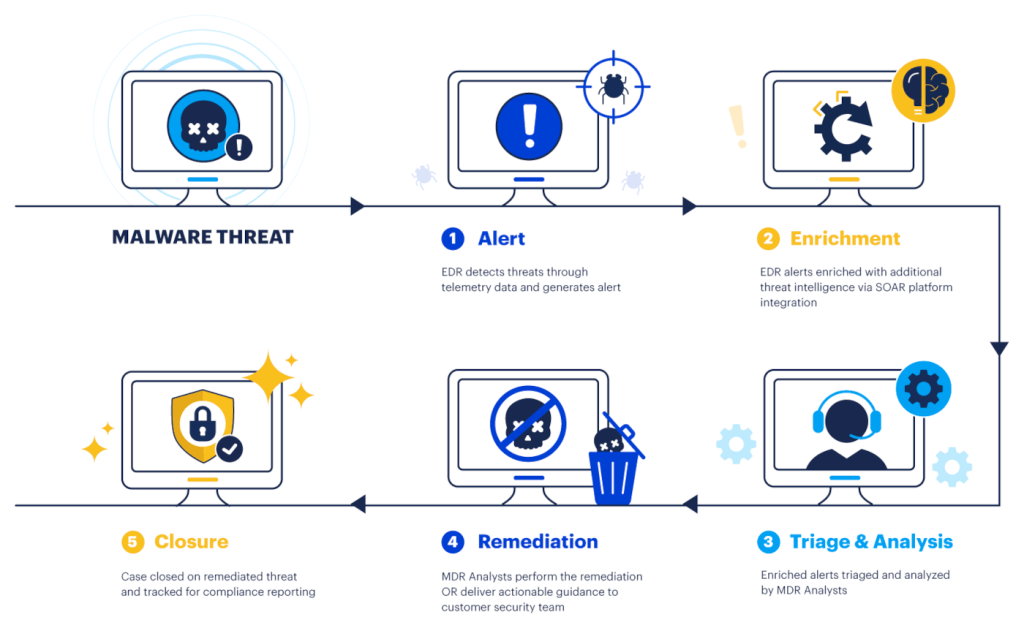
ThreatDown MDR workflow
Stop threats like PikaBot today
Want to learn more about how ThreatDown stops new threats like PikaBot? Fill out this form to speak with an expert and get a custom quote.
如有侵权请联系:admin#unsafe.sh