2023 culminated with an intensified wave of attacks on the software supply chain. Here are just a f 2024-1-31 20:0:0 Author: checkmarx.com(查看原文) 阅读量:16 收藏
2023 culminated with an intensified wave of attacks on the software supply chain. Here are just a few that our Software Supply Chain Research Team helped expose in the month of December alone:
- North Korea used public open-source and private package poisoning via the GitHub platform to infiltrate organizations and compromise their software supply chains (report)
- Attackers published malicious packages to PyPl, using various tactics, including combining obfuscation with encryption/decryption methods to hide their malicious intent, employing fileless malware to avoid detection, and leveraging the reputation of an extremely popular project (report)
- The Ledger Connect Kit suffered a significant supply chain attack resulting in the theft of over $700,000 from users’ wallets. The attack was facilitated by the takeover of a former Ledger employee’s npmjs account, which led to the release of compromised versions. This incident highlights the limitations of relying solely on Software Bill of Materials (SBOMs) to detect such attacks. (report)
We all hoped the start of a new year would bring new tidings. Unfortunately, NPM user account gdi2290, aka PatrickJS, published a troll campaign to the NPM registry by uploading a package named “everything,” which relies on every other public NPM package, resulting in millions of transitive dependencies. (report).
Jerry Gamblin, vulnerability researcher at Cisco, recently pointed out on LinkedIn that for the first time ever we have hit over 30,000 CVE’s published in a single year.
These developments, among the many others that preceded, emphasize the limited capacity of traditional security measures and the need for complementing them with advanced and dynamic approaches.
4 lessons learned in 2023
- Attackers are ingeniously stitching together diverse tactics.
- Deceptive maneuvers, exemplified by social engineering and bogus contributions, have become a staple in attackers’ arsenals.
- Abandoned digital assets are not relics
of the past; they are ticking time bombs. - The threat landscape’s relentless evolution emphasizes the importance of predictive threat hunting.
NSA's recommended practices for securing the software supply chain
December was also a month for renewed guidance from the US Government. The National Security Agency (NSA), Office of the Director of National Intelligence (ODNI), the Cybersecurity and Infrastructure Security Agency (CISA), and industry partners have released a cybersecurity technical report (CTR), “Securing the Software Supply Chain: Recommended Practices for Managing Open Source Software and Software Bill of Materials,” which builds on the “Enhancing the Security of the Software Supply Chain through Secure Software Development Practices” paper released by the Office of Management and Budget (OMB).
Even with this in-depth guidance, most customers we talk to are under the assumption that having a well-defined SBOM (Software Bill of Materials) is the only tangible approach to a software supply chain security strategy.
Checkmarx' end-to-end software supply chain security to facilitate SLSA attestation
Our vision is to bring together the idea of understanding what goes through the process, such as dependencies and software artifacts, with the development environment itself, all under the Supply-chain Levels for Software Artifacts (SLSA) framework. This first-to-market approach creates true visibility beyond what an SBOM can offer and helps get closer to providing attestation for SLSA compliance.
Preventing secrets from leaking on external tools with Secrets Detection
Secrets, such as passwords, API keys, cryptographic keys, and other confidential data, are a frequent target of a distributed supply-chain attack.
Threat actors are mining for secrets by scrapping public documentation, public repositories, and compromised private software repositories, and compromised build systems.
Each hard coded secret is now a new attack vector.
Secret Detection will help you remove hard coded passwords from your software supply chain by checking developer communication, shared tools, and components used across the supply chain.
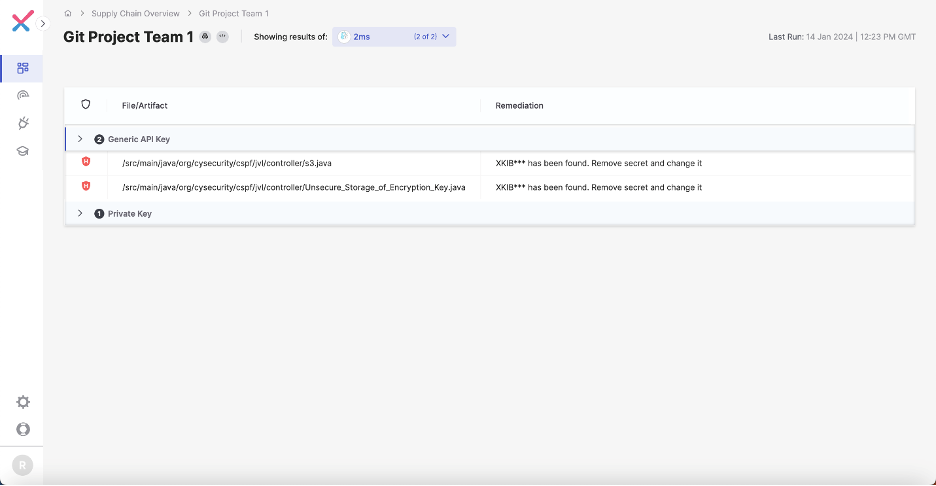
Secrets Detection integrates and expands deeper scanning capabilities of 2MS, one of the most popular open-source tools for secret detection with over 2 million downloads, directly into Checkmarx One.
Expanded capabilities include:
- Support for Confluence, Slack and Discord
- The ability to customizable rules and policies
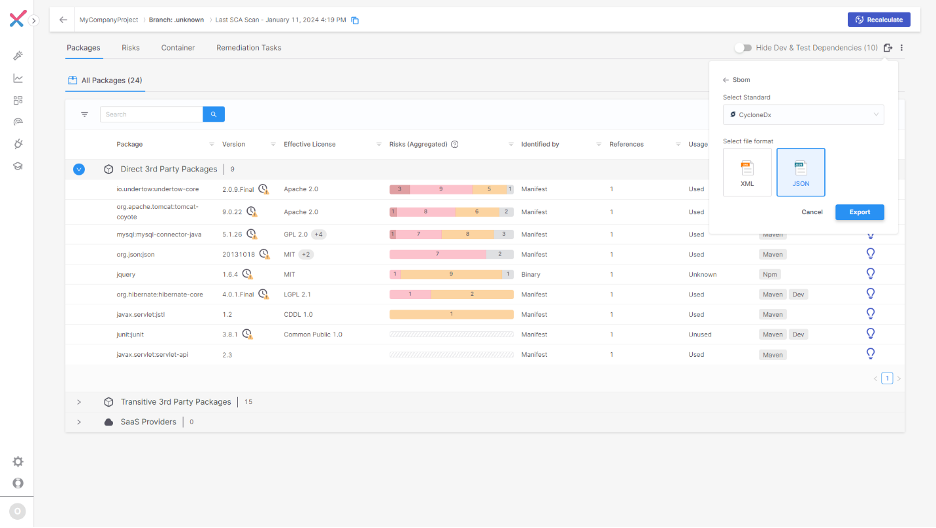
Creating a streamlined level of accountability with automated SBOM
SBOMs can be generated automatically directly from the UI, in SPDX and CycloneDX formats. This saves you time and a headache, and ensures you have an up-to-date inventory of third-party packages being used within your software supply chain.
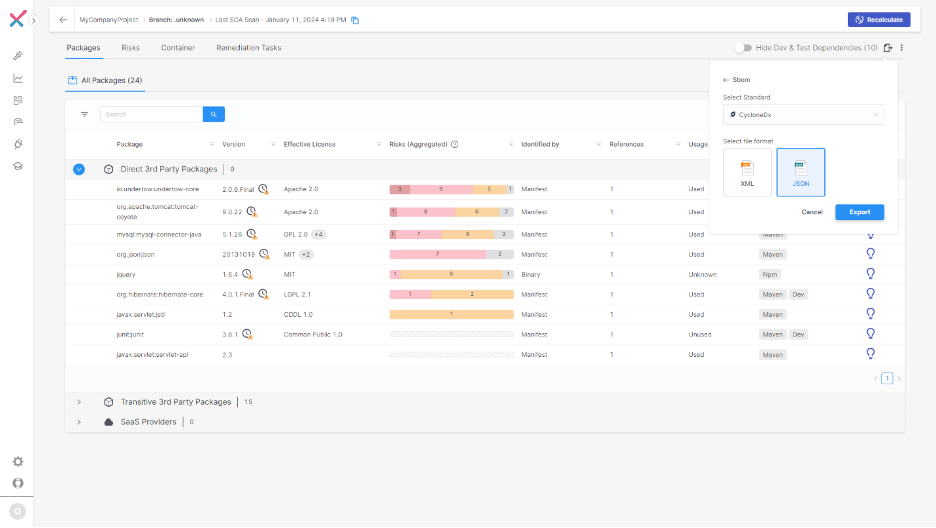
Since Checkmarx maintains a historical record of all scans performed, we can retrieve a point-in-time SBOM from previous scans or code checking events. This eliminates the need for us to build maintain and back up a catalog of SBOM files in a file share, saving time and effort while ensuring you can be compliant with historical SBOM requests.
Checkmarx supports a wide array of languages and package managers so there’s no need to implement maintain or update multiple SBOM solutions on a per project, or per language, level.
Tackling the most vulnerable internal projects first with Security Scorecard Engine
Checkmarx Scorecard enables organizations to check their own projects quickly and see the most vulnerable or at-risk projects, allowing enterprises to prioritize which to tackle first.
Scorecard leverages the format from a popular tool, the OSSF Scorecard, which assesses open-source projects for security risks through a series of automated checks.
These checks cover various parts of the software supply chain including source code, build, and dependencies, and assigns each check a score of 1-10. An auto-generated “security score” helps users as they decide the trust, risk, and security posture for their specific application.
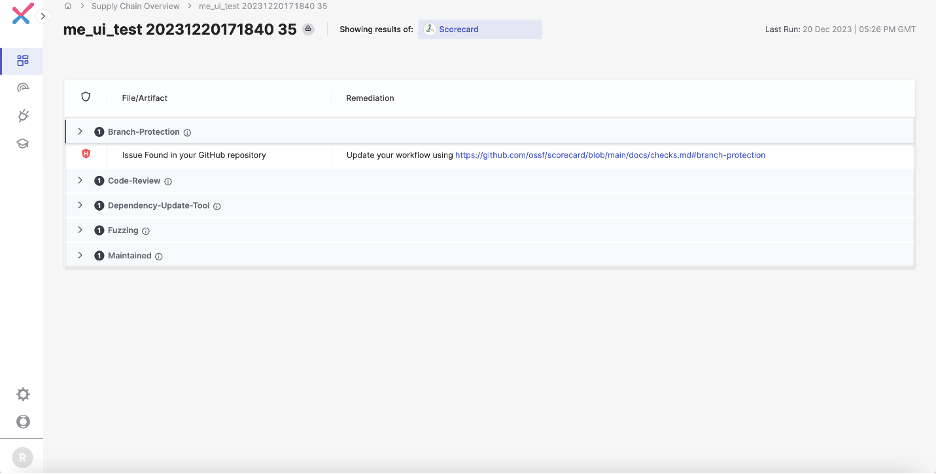
With Scorecard, users can auto-generate a security score for their own projects based on a series of checks, including:
- Binary Artifacts – Is the project free of checked-in binaries?
- Branch Protection – Does the project use branch protection?
- CI (Continuous Integration) Tests – Does the project run tests in CI, e.g., GitHub Actions, Prow?
- Code review – Does the project practice code review before code is merged?
- Dangerous workflow – Does the project avoid dangerous coding patterns?
- Vulnerabilities – Does the project have unfixed vulnerabilities?
Integrating new tools is a frictionless, one-click integration. Once you select a new tool, it gets scanned, and the results are displayed in a dedicated view within Checkmarx One.
Gaining threat intelligence and eliminating manual analysis with Malware Detection
In the SLSA framework, malicious packages are a form of dependency attack where attackers inject or contribute malicious code into open-source projects that your developers download and then build into your applications. Once downloaded, the attacker’s malicious code is running within your applications, with whatever unknown intent the package carries.
Our research team has inspected over 8 million open-source packages for all kinds of threats, finding 200,000+ malicious packages. We make that threat intelligence available to you, either in the UI, directly in developers’ IDE, or through an API-based threat intelligence feed.
Securing containerized applications throughout the supply chain
Securing your containers is a key part in preventing third parties from exploiting vulnerabilities that can lead to the impairment of your infrastructure, data leaks, and other types of attack. 87% of container images in production have critical or high-severity vulnerabilities.
The Checkmarx Container Security Solution simplifies image scanning, monitors Docker environments, and helps swiftly resolve vulnerabilities. Identify, prioritize, and address security flaws across the SDLC to preempt issues in production workloads.
- Container Image Scanning - Scan static container images to identify vulnerable code in open-source software and remediate issues before they are deployed.
- Runtime Insights Correlation - Correlate pre-production and runtime data to identify exploitable vulnerabilities in running container images, reduce noise by up to 95%, and prioritize remediation efforts.
Software supply chain security is a journey, and it is important to take steps to secure your software supply chain today; detecting supply chain attacks in code packages, securing your developer’s evolving workstations supports rapid development while reducing risk.
如有侵权请联系:admin#unsafe.sh