Google has announced an important update for Chrome to help fend off a zero-day. The update fixes several issues, and readers are advised to ensure they're using the latest version of the browser.
Mitigation
If you’re using Chrome on Mac, Windows, or Linux, you need to update as soon as you possibly can. If you’re using a standard Chrome setup then updates should be applied automatically. However, this won't happen if you never close your browser, or if the update is blocked by something like a fault in an installed extension.
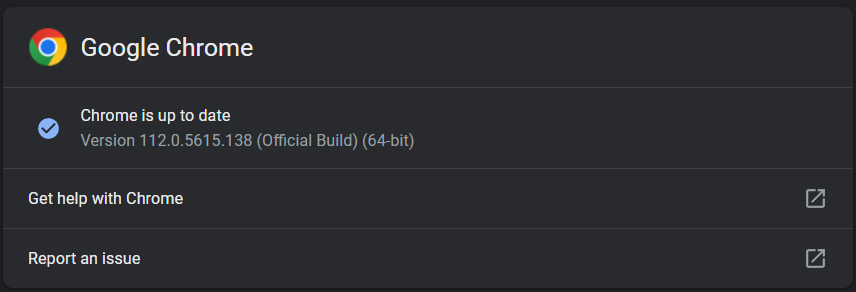
It’s always good to check, especially when something bad is floating around potentially helping to compromise devices. One easy way to do this is navigate to chrome://settings/help or clicking Settings > About Chrome.
Chrome will notify you of the version you're on and if there's an update available. Once you've downloaded the update, reload the browser and everything should be good to go. If everything has worked as it should, your version should in theory be running the latest version. At the time of writing the most recent update being offered is now 112.0.5615.138.

This will fix eight vulnerabilities, although the update is only currently available for both Mac and Windows. The Linux version is still being worked on.
Vulnerability
The exploit page for CVE-2023-2136 has few details available, as is the usual pattern followed by Google when something like this happens. Details are generally held back to give people time to patch, without offering any clues to cybercriminals about how they might exploit the vulnerability. So far, the only information we have is:
Integer overflow in Skia in Google Chrome prior to 112.0.5615.137 allowed a remote attacker who had compromised the renderer process to potentially perform a sandbox escape via a crafted HTML page. (Chromium security severity: High)
An integer overflow is a programming error that allows an attacker to manipulate a number the program uses in a way that might be harmful. If the number is used to set the length of a data buffer (an area of memory used to hold data), an integer overflow can lead to a buffer overflow, a vulnerability that allows an attacker to overloaded a buffer with more data than it's expecting, which creates a route for the attacker to manipulate the program.
Skia is a graphics library (a set of reusable code) used by Google Chrome. In this case the error allows an attacker to escape the shackles of Chrome's "sandbox", a security feature that should prevent malicious code from affecting the system that Chrome is running on.
Malwarebytes removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.