分享github捡漏与找敏感信息的套路
分享github捡漏的一些套路声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由用户承担全部法律及连带责任,文章作者不承担任何法律及连带责任。正文主要是利 2022-11-2 15:28:11 Author: 安全狗的自我修养(查看原文) 阅读量:32 收藏
分享github捡漏的一些套路声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由用户承担全部法律及连带责任,文章作者不承担任何法律及连带责任。正文主要是利 2022-11-2 15:28:11 Author: 安全狗的自我修养(查看原文) 阅读量:32 收藏
分享github捡漏的一些套路
声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由用户承担全部法律及连带责任,文章作者不承担任何法律及连带责任。
正文
主要是利用github来发掘一些信息泄露的漏洞:
".mlab.com password"
"AWSSecretKey"
"JEKYLL_GITHUB_TOKEN"
"SF_USERNAME salesforce"
"access_key"
"access_token"
"amazonaws"
"apiSecret"
"api_key"
"api_secret"
"apidocs"
"apikey"
"app_key"
"app_secret"
"appkey"
"appkeysecret"
"application_key"
"appsecret"
"appspot"
"auth"
"auth_token"
"authorizationToken"
"aws_access"
"aws_access_key_id"
"aws_key"
"aws_secret"
"aws_token"
"bashrc password"
"bucket_password"
"client_secret"
"cloudfront"
"codecov_token"
"config"
"conn.login"
"connectionstring"
"consumer_key"
"credentials"
"database_password"
"db_password"
"db_username"
"dbpasswd"
"dbpassword"
"dbuser"
"dot-files"
"dotfiles"
"encryption_key"
"fabricApiSecret"
"fb_secret"
"firebase"
"ftp"
"gh_token"
"github_key"
"github_token"
"gitlab"
"gmail_password"
"gmail_username"
"api.googlemaps AIza"
"herokuapp"
"internal"
"irc_pass"
"key"
"keyPassword"
"ldap_password"
"ldap_username"
"login"
"mailchimp"
"mailgun"
"master_key"
"mydotfiles"
"mysql"
"node_env"
"npmrc _auth"
"oauth_token"
"pass"
"passwd"
"password"
"passwords"
"pem private"
"preprod"
"private_key"
"prod"
"pwd"
"pwds"
"rds.amazonaws.com password"
"redis_password"
"root_password"
"secret"
"secret.password"
"secret_access_key"
"secret_key"
"secret_token"
"secrets"
"secure"
"security_credentials"
"send.keys"
"send_keys"
"sendkeys"
"sf_username"
"slack_api"
"slack_token"
"sql_password"
"ssh"
"ssh2_auth_password"
"sshpass"
"staging"
"stg"
"storePassword"
"stripe"
"swagger"
"testuser"
"token"
"x-api-key"
"xoxp"
"xoxb "
HEROKU_API_KEY language:json
HEROKU_API_KEY language:shell
HOMEBREW_GITHUB_API_TOKEN language:shell
PT_TOKEN language:bash
[WFClient] Password= extension:ica
extension:avastlic "support.avast.com"
extension:bat
extension:cfg
extension:env
extension:exs
extension:ini
extension:json api.forecast.io
extension:json googleusercontent client_secret
extension:json mongolab.com
extension:pem
extension:pem private
extension:ppk
extension:ppk private
extension:properties
extension:sh
extension:sls
extension:sql
extension:sql mysql dump
extension:sql mysql dump password
extension:yaml mongolab.com
extension:zsh
filename:.bash_history
filename:.bash_profile aws
filename:.bashrc mailchimp
filename:.bashrc password
filename:.cshrc
filename:.dockercfg auth
filename:.env DB_USERNAME NOT homestead
filename:.env MAIL_HOST=smtp.gmail.com
filename:.esmtprc password
filename:.ftpconfig
filename:.git-credentials
filename:.history
filename:.htpasswd
filename:.netrc password
filename:.npmrc _auth
filename:.pgpass
filename:.remote-sync.json
filename:.s3cfg
filename:.sh_history
filename:.tugboat NOT _tugboat
filename:CCCam.cfg
filename:WebServers.xml
filename:_netrc password
filename:bash
filename:bash_history
filename:bash_profile
filename:bashrc
filename:beanstalkd.yml
filename:composer.json
filename:config
filename:config irc_pass
filename:config.json auths
filename:config.php dbpasswd
filename:configuration.php JConfig password
filename:connections
filename:connections.xml
filename:constants
filename:credentials
filename:credentials aws_access_key_id
filename:cshrc
filename:database
filename:dbeaver-data-sources.xml
filename:deploy.rake
filename:deployment-config.json
filename:dhcpd.conf
filename:dockercfg
filename:environment
filename:express.conf
filename:express.conf path:.openshift
filename:filezilla.xml
filename:filezilla.xml Pass
filename:git-credentials
filename:gitconfig
filename:global
filename:history
filename:htpasswd
filename:hub oauth_token
filename:id_dsa
filename:id_rsa
filename:id_rsa or filename:id_dsa
filename:idea14.key
filename:known_hosts
filename:logins.json
filename:makefile
filename:master.key path:config
filename:netrc
filename:npmrc
filename:pass
filename:passwd path:etc
filename:pgpass
filename:prod.exs
filename:prod.exs NOT prod.secret.exs
filename:prod.secret.exs
filename:proftpdpasswd
filename:recentservers.xml
filename:recentservers.xml Pass
filename:robomongo.json
filename:s3cfg
filename:secrets.yml password
filename:server.cfg
filename:server.cfg rcon password
filename:settings
filename:settings.py SECRET_KEY
filename:sftp-config.json
filename:sftp.json path:.vscode
filename:shadow
filename:shadow path:etc
filename:spec
filename:sshd_config
filename:tugboat
filename:ventrilo_srv.ini
filename:wp-config
filename:wp-config.php
filename:zhrc
jsforce extension:js conn.login
language:yaml -filename:travis
msg nickserv identify filename:config
path:sites databases password
private -language:java
shodan_api_key language:python分享从github寻找敏感信息的套路
声明:文章中涉及的程序(方法)可能带有攻击性,仅供安全研究与教学之用,读者将其信息做其他用途,由用户承担全部法律及连带责任,文章作者不承担任何法律及连带责任。
正文
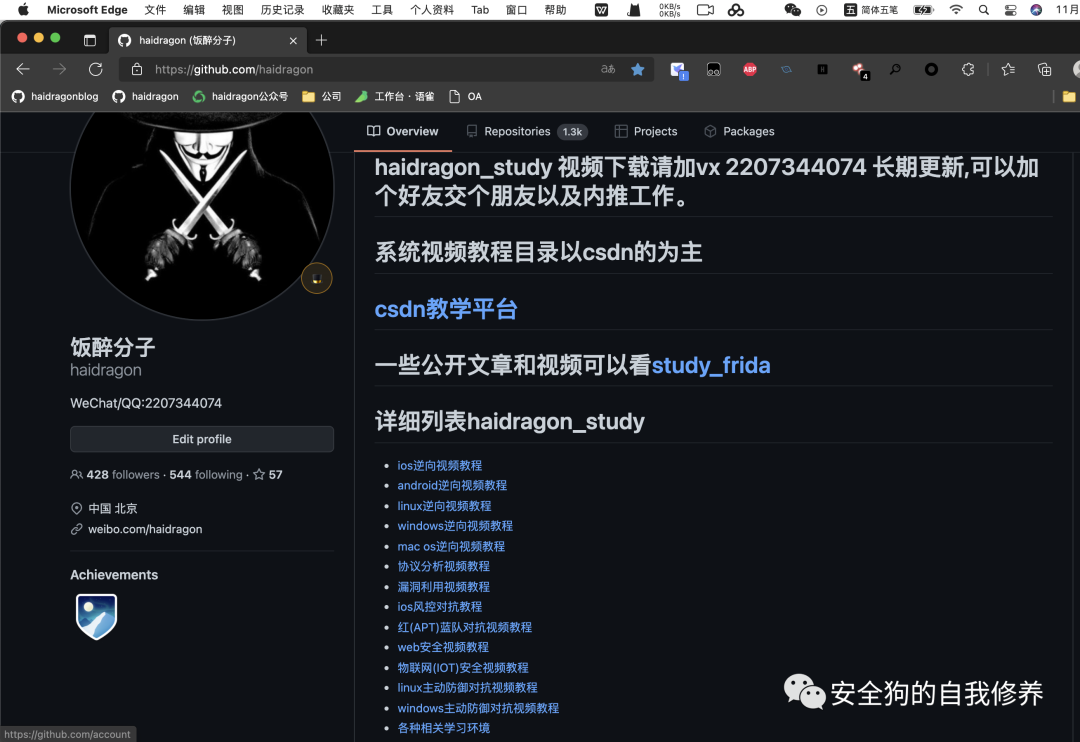
之前分享过一篇从github寻找敏感信息的套路,但是不够细致,这次分享的比较细致还有相关示例;
docker相关文件中存在的敏感信息
.docker/.dockercfg 或者 .docker/config.json中主要是包含Docker Registry Authentication相关的数据
org:company filename:.dockercfgorg:company docker AND auth AND email
user:name filename:.dockercfg
user:name filename:.dockercfg
"company.com" docker AND auth AND email
示例:
{
"https://index.docker.io/v1/": {
"email": "[email protected]",
"auth": "X3Rva2VuOjEyMzQuMThqZjg0MWZrbDQwYU90dTNrLXdCbDVuaThDM2Q0QVh0QjM2V2VqZzM4MDA2WlR5TDhUOWg5VXgrWWwzdTNVQ1hDWFZlWg"
},
"https://hub.docker.com/": {
"email": "[email protected]",
"auth": "X3Rva2VuOjEyMzQuMThqZjg0MWZrbDQwYU90dTNrLXdCbDVuaThDM2Q0QVh0QjM2V2VqZzM4MDA2WlR5TDhUOWg5VXgrWWwzdTNVQ1hDWFZlWg"
}
}
IDE中的默认文件中存在的敏感数据
很多公司的开发人员喜欢用jetbrain家的产品,但是有时候不小心会把.idea文件上传,里面很有可能包含着web服务器的凭据,这些都是比较敏感的信息
org:company filename:webservers.xmlorg:company fileTransfer AND pass
user:name filename:webservers.xml
user:name filename:webservers.xml
"company.com" fileTransfer AND pass
示例:
<?xml version="1.0" encoding="UTF-8"?>
<project version="4">
<component name="WebServers">
<option name="servers">
<webServer id="6ac7fc5c-e40f-41b3-b7fe-ed7f9b15e3c4" name="root" url="https://example.com">
<fileTransfer host="example.com" port="21" password="dff9dfdfdfdadfcfdfd8dff9dfcfdfcfdfc9dfd8dfcfdfdedffadfcbdfd9dfd9dfdddfc5dfd8dfcedf8b" username="root">
<advancedOptions>
<advancedOptions dataProtectionLevel="Private" />
</advancedOptions>
<option name="port" value="21" />
</fileTransfer>
</webServer>
</option>
</component>
</project>
其它学习教程。
文章来源: http://mp.weixin.qq.com/s?__biz=MzkwOTE5MDY5NA==&mid=2247486007&idx=2&sn=7fd9bb4ed915629c41edf08b8655259f&chksm=c13f397ef648b06808e4f5b02585e2377f55cc147c293e848b607b361e303603b62e7297332d#rd
如有侵权请联系:admin#unsafe.sh
如有侵权请联系:admin#unsafe.sh